Mining | Customer Stories
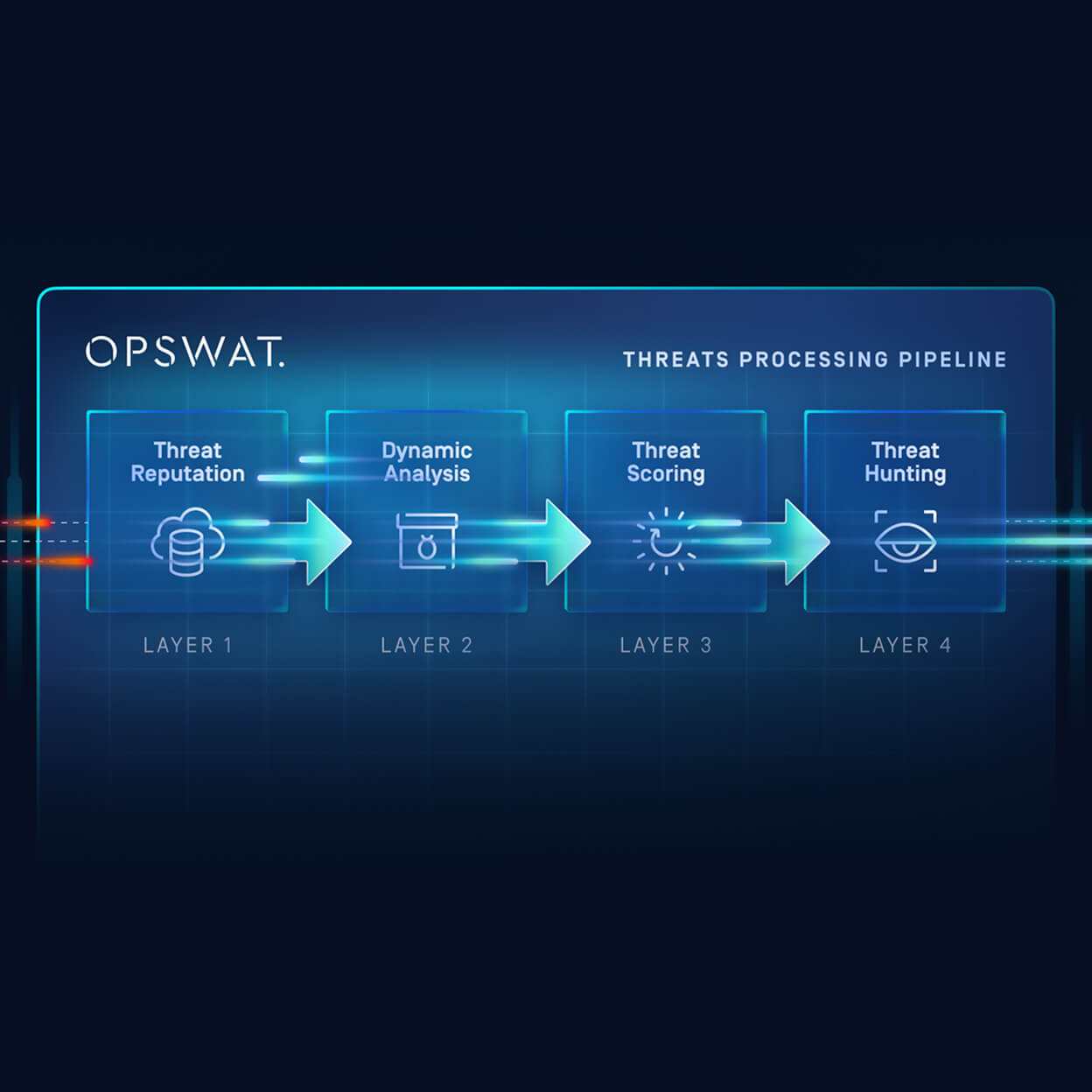
Sending Logs, Alerts, and Telemetry Through a Data Diode
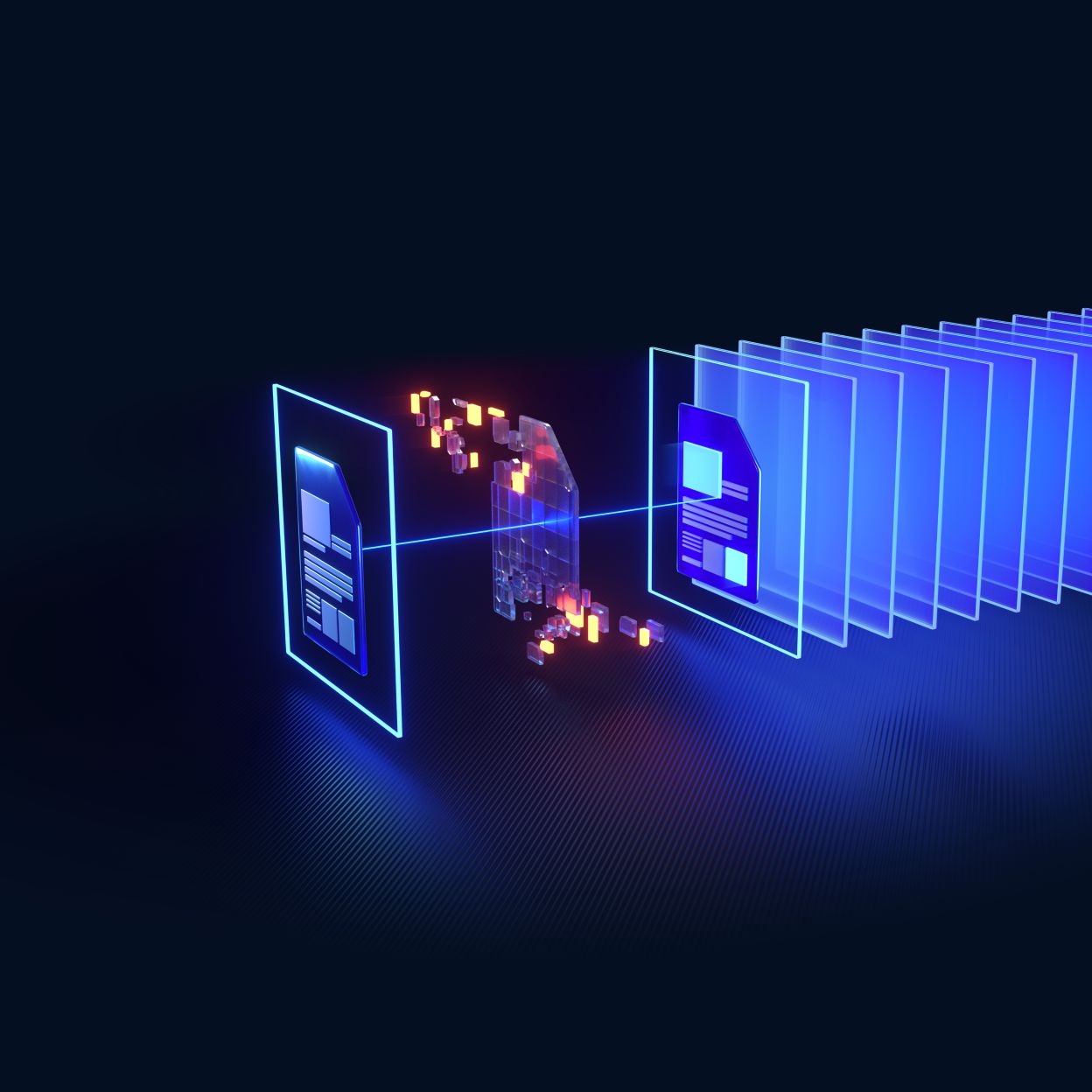
File-based threats remain one of the most persistent and evasive risks to enterprises, from zero-day exploits in documents to APTs hidden in seemingly safe files. As organizations work to secure every file entering their environment, Content Disarm and Reconstruction (CDR) has become a critical layer of defense.