We Protect the
World’s Critical Infrastructure
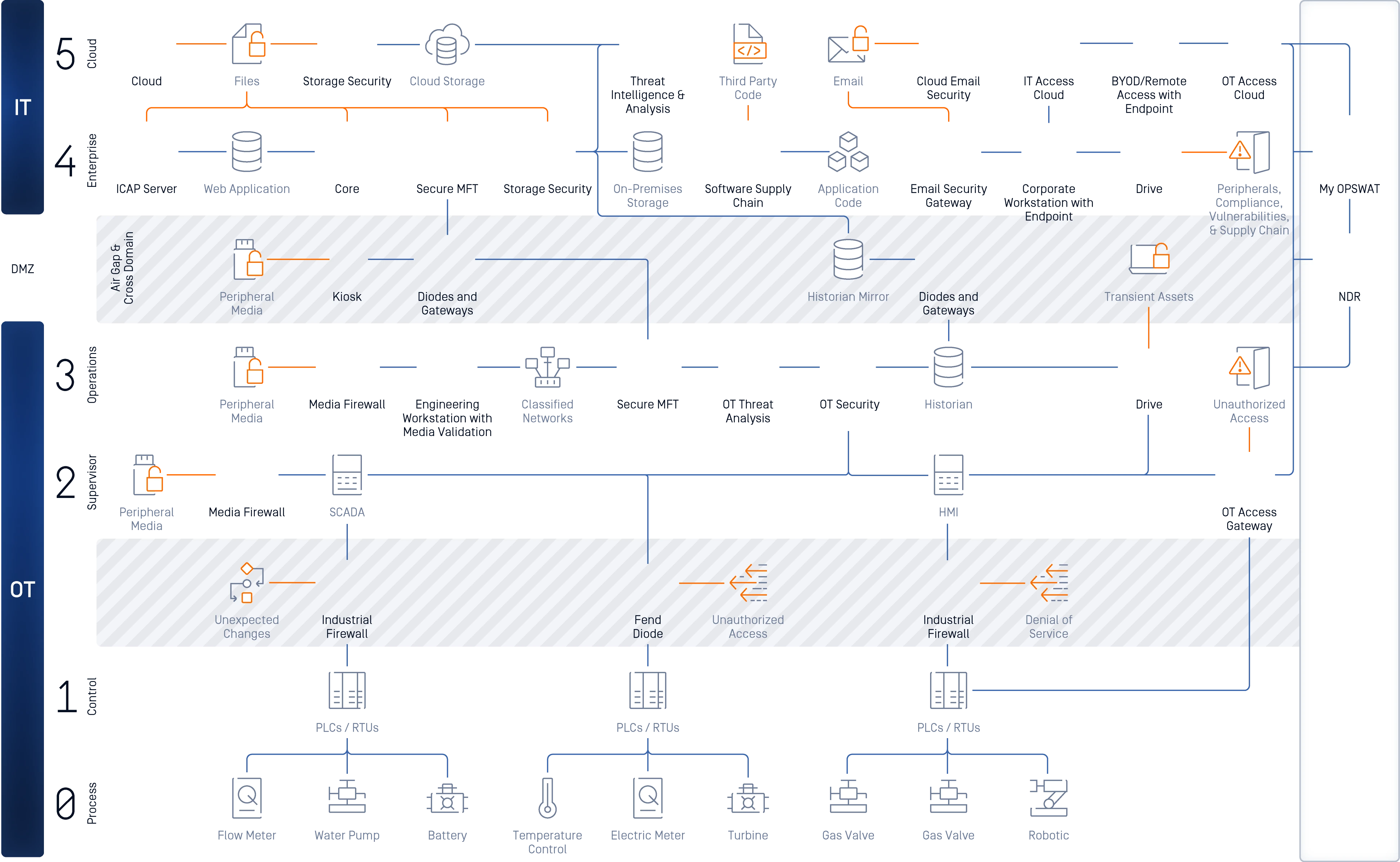
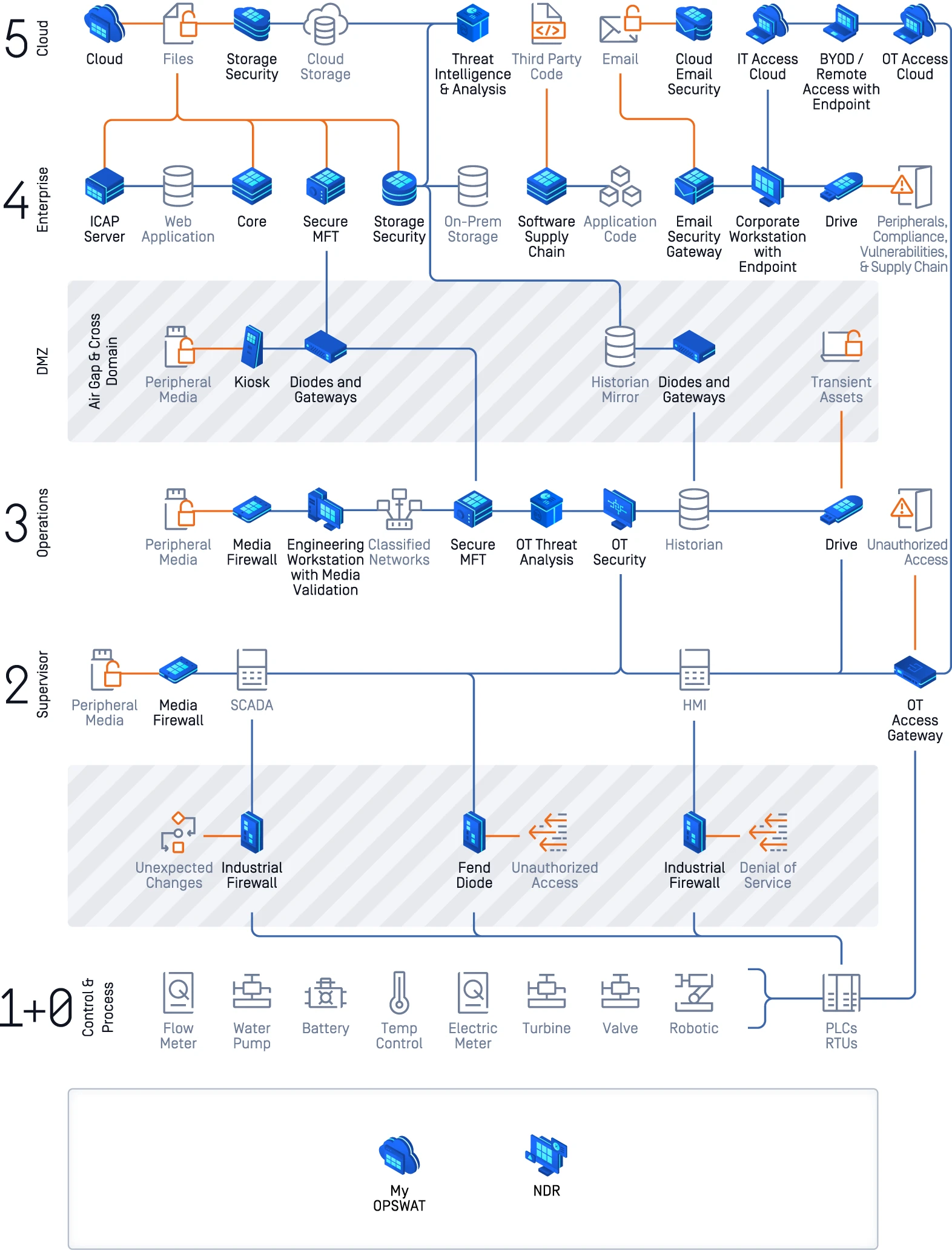
OPSWAT prevents known, unknown, and AI-generated threats from reaching the systems the world depends on. The MetaDefender Platform, OPSWAT's AI-powered cybersecurity solution, secures every file, device, and data transfer across IT, OT, and cross-domain environments.
Comprehensive AI-Powered Platform
Extensive File Security Throughout Your Organization
Integrated IT, OT Products
Wide Peripheral Media Protection
Purpose Built Machine Learning Technologies
AI and Machine Learning-Driven
Prevent AI-Borne Threats
Prevention Not Based on Detection
Training Academy for Critical Infrastructure
Practical Online Training and Certification
Regional and Virtual CIP Labs
Enterprise Training Solutions
2K+
Global Customers
20+
Years Protecting Critical Networks
275K+
Certified Professionals
Recommended Webinars
Protecting the Industries
the World Runs on
Critical infrastructure is any system the world depends on. Built to the standards of national defense and global
enterprise, OPSWAT is the firewall of data for the world's most critical networks.
Secured Perimeter and Data Workflows
for Any Organization
OPSWAT secures data flows to and from critical networks, protected by layered threat prevention, AI-powered prediction and content verification, and continuous vulnerability intelligence, all through the MetaDefender platform.

File Security
Prevent file-borne malware from reaching production systems. MetaDefender scans, sanitizes, and verifies every file before it's trusted.
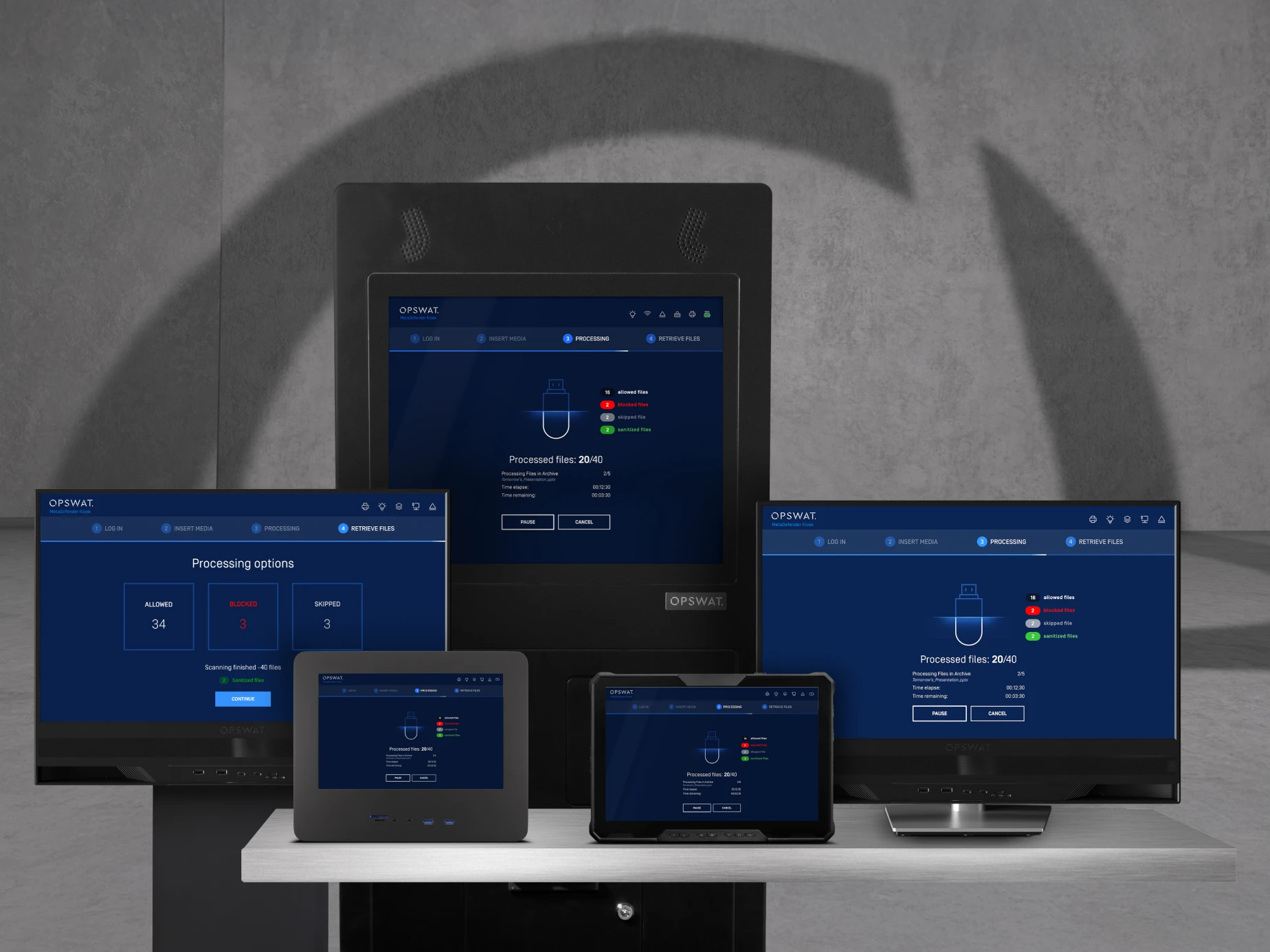
Peripheral and Removable Media Protection
Control what enters your critical environment through USB drives, portable devices, and transient assets with kiosk-based scanning and compliance enforcement at the perimeter.

Managed File Transfer
Move files securely across network boundaries with built-in threat prevention, policy enforcement, and full audit trails, without exposing sensitive environments.

Data Diode and Security Gateway Solutions
Enable hardware-enforced unidirectional data transfer between network segments. OPSWAT data diodes and security gateways protect air-gapped and segmented networks with zero risk of reverse data flow.

Storage Security
Scan and sanitize files in cloud storage, on-premises repositories, and file-sharing platforms, preventing malware and data leakage without disrupting workflows.

Email Security
Neutralize weaponized attachments and embedded threats before they reach the inbox. Deep CDR™ Technology and Metascan™ multiscanning technologies applied to every inbound message.

Access and Endpoint Security
Assess and enforce device posture before granting network access. The OESIS Framework gives security vendors and IT teams the tools to verify endpoint compliance across managed and unmanaged devices.

File Security
Prevent file-borne malware from reaching production systems. MetaDefender scans, sanitizes, and verifies every file before it's trusted.
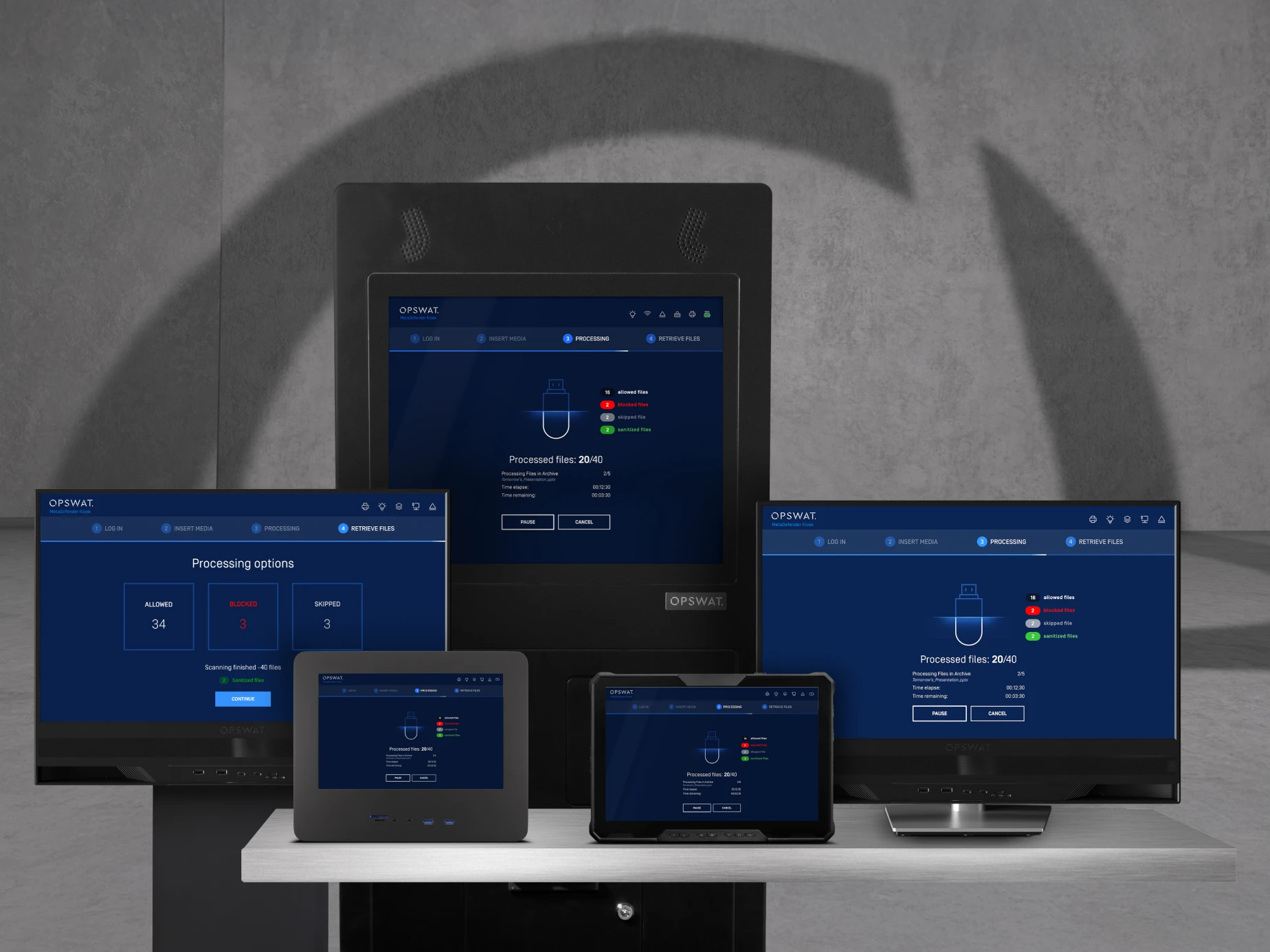
Peripheral and Removable Media Protection
Control what enters your critical environment through USB drives, portable devices, and transient assets with kiosk-based scanning and compliance enforcement at the perimeter.

Managed File Transfer
Move files securely across network boundaries with built-in threat prevention, policy enforcement, and full audit trails, without exposing sensitive environments.

Data Diode and Security Gateway Solutions
Enable hardware-enforced unidirectional data transfer between network segments. OPSWAT data diodes and security gateways protect air-gapped and segmented networks with zero risk of reverse data flow.

Storage Security
Scan and sanitize files in cloud storage, on-premises repositories, and file-sharing platforms, preventing malware and data leakage without disrupting workflows.

Email Security
Neutralize weaponized attachments and embedded threats before they reach the inbox. Deep CDR™ Technology and Metascan™ multiscanning technologies applied to every inbound message.

Access and Endpoint Security
Assess and enforce device posture before granting network access. The OESIS Framework gives security vendors and IT teams the tools to verify endpoint compliance across managed and unmanaged devices.
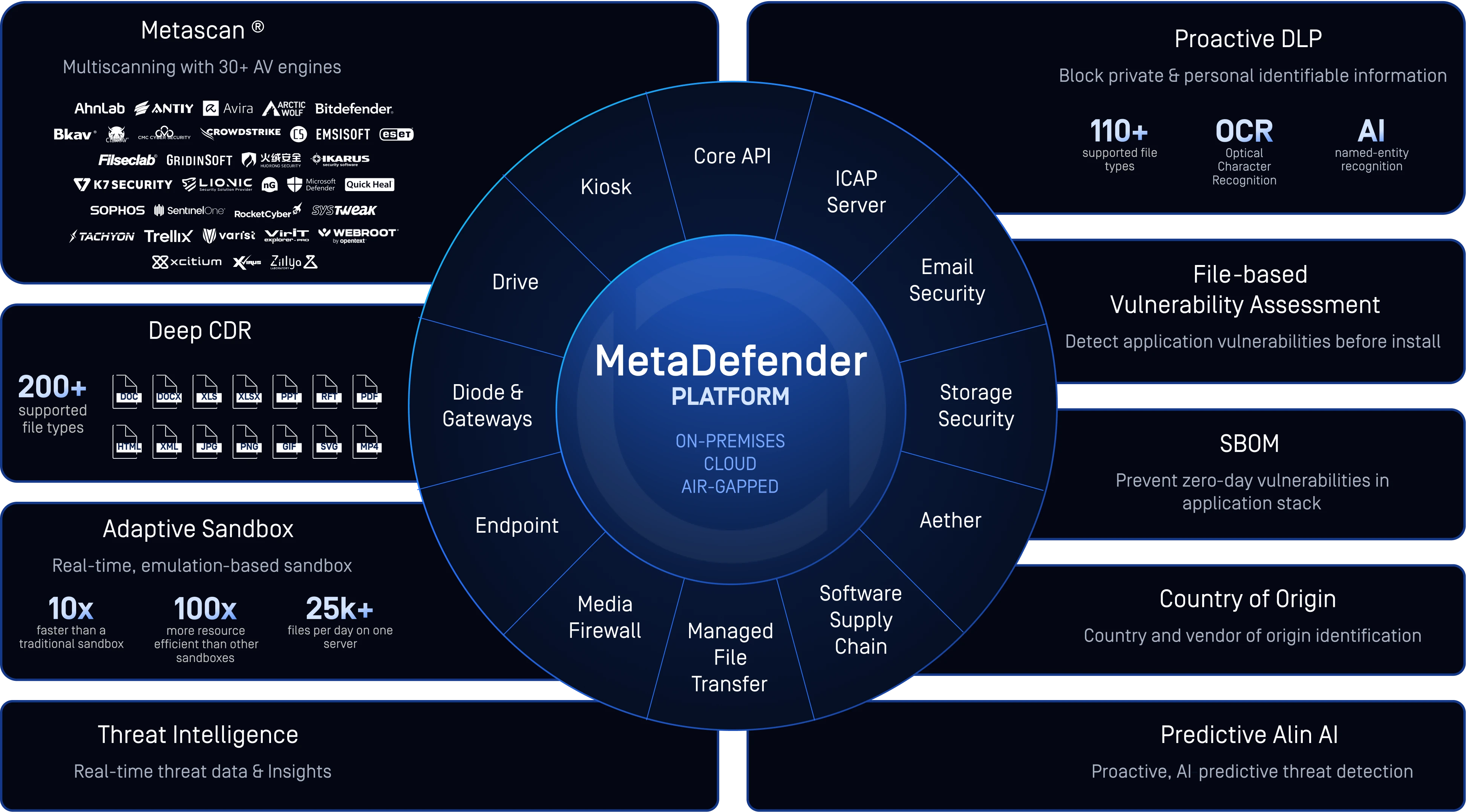
MetaDefender AI-Powered Platform
MetaDefender is OPSWAT's AI platform for critical infrastructure protection — where all data is scanned, sanitized, verified, and controlled before it moves deeper into an environment. OPSWAT delivers zero trust, prevention-first cybersecurity that secures data movement and workflows across Cloud, IT, OT, and Cross Domain environments. OPSWAT's AI is embedded natively across the platform, making threat prevention faster, more proactive, and capable of stopping AI-generated threats that legacy tools can't see.
Explore the Platform
MetaDefender Technology Stack
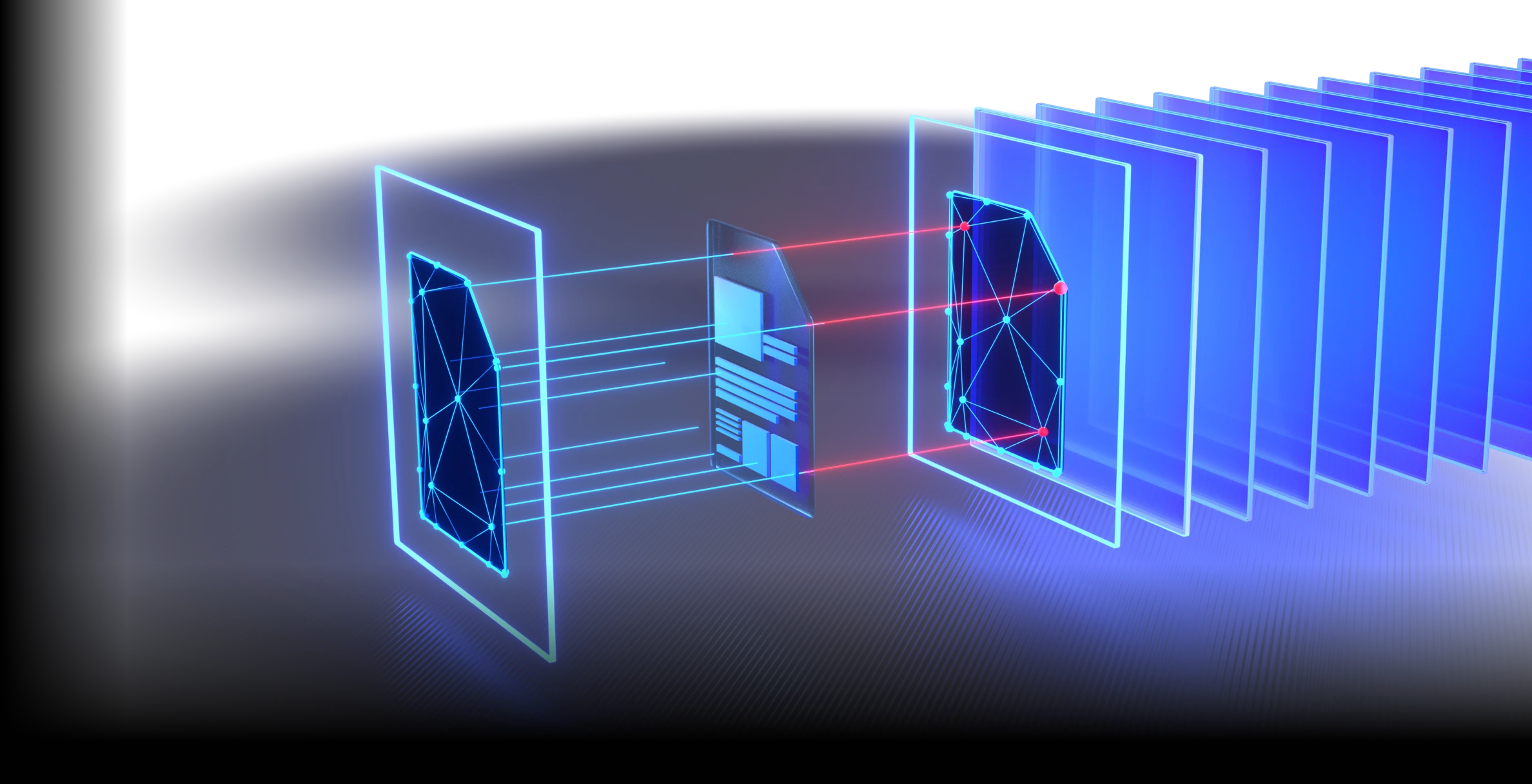
Most cybersecurity vendors are building AI to triage alerts faster, orchestrate responses, or protect AI models themselves. OPSWAT builds AI to prevent threats at the data layer — stopping malicious content before it executes, not after it is detected.
OPSWAT layers Deep CDR™ Technology, Metascan™ Multiscanning, AI-driven threat prediction, Adaptive Sandbox, and AI-powered content verification technologies to prevent, detect, and neutralize threats before they execute.
Built for Prediction,
Engineered for Speed
- Deep file structure analysis
- ML-Model trained on zero-day threats
More Engines Are Better Than One
- Detect nearly 100% of malware
- Scan simultaneously with 30+ leading AV engines
Stop Threats That Others Miss
- Supports 200+ file formats
- Recursively sanitize multi-level nested archives
- Regenerate safe and usable files
Prevent Sensitive Data Loss
- Utilize AI-powered models to locate and classify unstructured text into predefined categories
- Automatically redact identified sensitive information like PII, PHI, PCI in 125+ file types
- Support for Optical Character Recognition (OCR) in images
Detect Evasive Malware with Advanced Emulation-Based Sandboxing
- Analyze files in a high-speed
- Anti-evasion sandbox engine extracts IOCs
- Identify zero-day threats
- Enable deep malware classification via API or local integration
Enhance Detection with Real-Time Threat Intelligence
- Correlate global IOCs, IPs, URLs, & file reputation across 50B+ artifacts
- Stop emerging threats faster
- Enrich downstream analysis
Detect Application Vulnerabilities Before They Are Installed
- Check software for known vulnerabilities before installation
- Scan systems for known vulnerabilities when devices are at rest
- Quickly examine running applications and their libraries for vulnerabilities
Trust No File. Trust No Device.
Every capability is engineered natively into the MetaDefender Platform.
No bolt-ons. No separate SKUs. No acquisitions to integrate.
Built to the Standards That Govern the World's Most Regulated Industries
The MetaDefender Platform is pre-validated against the most rigorous regulatory frameworks for critical infrastructure security, including NIST 800-53, CMMC 2.0, NERC CIP, Zero Trust architecture mandates, ISO 27001, Common Criteria, SOC 2, and NEI 08-09 Rev 6 for nuclear deployments.






Deploy Quickly.
Protect Immediately.
Reduce the Burden on Operators.
OPSWAT reduces operational burden with automated workflows, unified policy management, and simplified deployment — enabling immediate protection across complex environments. AI engines operate inline and autonomously, requiring no additional integration or manual intervention to deliver value.

The Organizations That Trust OPSWAT to
Protect What Matters Most
Awards and Recognition
Intelligence From the Front Lines of Critical Infrastructure Defense

Ponemon Institute State of File Security
Essential insights IT and cybersecurity leaders need to know now.
2025 OPSWAT Threat Landscape Report
Global Cyberattack Trends Require Actionable Intelligence for Better Protection

2025 ICS/OT Cybersecurity Budget: Spending Trends, Challenges and the Future
Spending trends, challenges, and priorities shaping OT security investment.
SANS Detection & Response Survey
Uncovering the widening gaps caused by endpoint-heavy security postures, rising complexity, and inconsistent intelligence sharing.
Common Questions About OPSWAT
OPSWAT is a cybersecurity company that protects critical infrastructure by securing files, devices, and data transfers across IT, OT, and air-gapped networks. The MetaDefender Platform uses AI-driven threat prediction, Deep CDR™ Technology, Metascan™ multiscanning with 30+ anti-malware engines, and adaptive sandbox analysis technologies to prevent known, unknown, and AI-generated threats from reaching sensitive systems.
OPSWAT embeds AI natively in the MetaDefender Platform. Predictive Alin AI is a machine learning engine that predicts file-level threats before execution — with a 0.1% false positive rate and no detonation required — using models continuously retrained on zero-day threats confirmed by MetaDefender Aether.
The MetaDefender Platform is OPSWAT's unified cybersecurity system. It provides file security, email security, removable media protection, network security, cross-domain transfer, endpoint compliance, and cloud security, all managed through a single platform with centralized policy control. The MetaDefender Platform is designed for the most demanding environments, from nuclear facilities and defense networks to global financial institutions.
OPSWAT is a cybersecurity company whose mission is protecting critical infrastructure worldwide. MetaDefender is OPSWAT's AI-powered cybersecurity platform — the solution that delivers that protection. The MetaDefender Platform includes file security, email security, removable media protection, managed file transfer, data diodes, and storage security, all unified under a single management console. When organizations deploy OPSWAT, they are deploying the MetaDefender Platform and its underlying technologies.
Deep CDR™ Technology is OPSWAT's technology that sanitizes files by deconstructing them, removing all potentially malicious content, including embedded scripts, macros, and exploit code, and rebuilding clean, fully functional files. It supports 200+ file types and is the first and only CDR technology to achieve a 100% accuracy rating from SE Labs.
OPSWAT provides multiple solutions for air-gapped environments. MetaDefender Kiosk scans and sanitizes files from removable media before they enter secured networks. MetaDefender Drive verifies the security of portable devices. MetaDefender NetWall data diodes enforce hardware-level unidirectional data transfer, ensuring no data can flow back from the protected network.
OPSWAT protects organizations across energy, nuclear, government, defense, manufacturing, financial services, healthcare, transportation, and oil and gas: any sector operating critical infrastructure that requires advanced threat prevention, regulatory compliance, and protection for both IT and OT environments.
Metascan™ multiscanning is OPSWAT's technology that simultaneously analyzes files with 30+ leading anti-malware engines. By combining signatures, heuristics, and machine learning from multiple vendors in a single scan, Metascan™ detects over 99% of known malware, significantly higher than any single engine alone.
Ready to Protect Your Critical Infrastructure?
Our team is ready to show you how the MetaDefender Platform
prevents threats from reaching the systems you depend on.