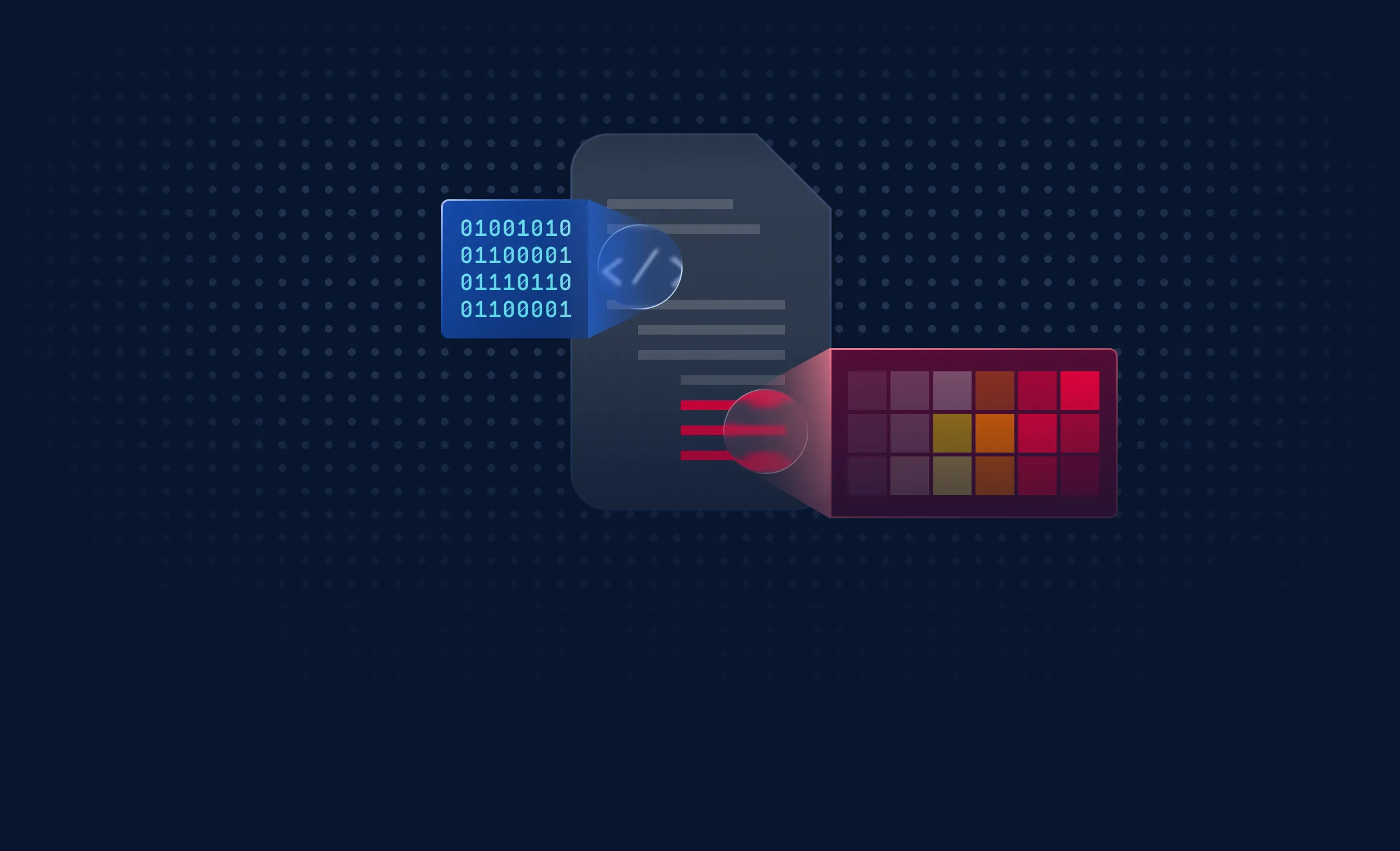
Predictive Alin AI is trained on curated, privacy-safe enterprise datasets that reflect real file movement patterns rather than consumer telemetry.
- The engine analyzes structural file attributes, entropy patterns, and semantic indicators to predict malicious intent.
- Each sandbox-confirmed zero-day strengthens the model, creating a continuous feedback loop that improves predictive accuracy over time.
- This approach enables organizations to stop malicious files before execution while maintaining low false positives and minimal performance impact.