Behavior-Centric
Threat Intelligence
A technology engine that transforms file artifacts and behavioral signals into actionable intelligence across cloud, hybrid, and air-gapped environments.
- High-Fidelity IOCs
- Similarity Correlation
- Offline Capable
OPSWAT is Trusted by
50B+
Global Threat Indicators
Sandbox-Derived
Behavioral IOCs
MISP & STIX
Exports
Threat Sharing and
Automation
ML-Based
Similarity Search
Offline Reputation Packages
SIEM & SOAR Ready
MITRE-Mapped Detection Context
Reputation Alone Is Not Enough
Enterprises handle thousands of files, emails, and data exchanges every day. Without deep inspection and policy
enforcement, sensitive information can slip through unnoticed, creating serious compliance and security risks.

Too Much Noise, Not Enough Context
Reputation-only feeds return raw indicators without behavioral insight, forcing analysts to manually pivot across tools to determine true risk.
Polymorphic Malware Evades Signatures
Recompiled variants and minor code mutations bypass hash-based detection, leaving gaps in visibility across campaigns and infrastructure.
Intelligence Silos Slow Investigations
When sandbox results, reputation data, and hunting workflows are disconnected, investigations take longer and zero-day relationships go unnoticed.
From Indicators to Intelligence
A unified threat intelligence engine that correlates global reputation with behavioral and similarity-driven analysis.
Intelligence That Correlates,
Not Just Collects
A multi-layered intelligence pipeline designed to surface relationships between indicators, behaviors, and attacker infrastructure.
Intelligence That Goes Beyond Indicators
Combine global reputation, behavioral IOCs, and similarity search to expose unknown threats, reduce investigation time, and improve detection accuracy.
Sandbox-Derived
Intelligence
Enhances reputation checks with behavioral IOCs extracted from dynamic analysis, increasing detection fidelity compared to reputation-only intelligence platforms.
Variant Detection
at Scale
Similarity search detects modified and polymorphic malware, reducing blind spots when adversaries rotate hashes or infrastructure.
Automation-Ready
Enrichment
Structured exports via REST APIs, MISP, STIX, and JSON enable rapid SIEM and SOAR integration with minimal engineering overhead.
See Intelligence Correlation in Action
Explore how behavioral IOCs, reputation scoring, and similarity search reveal hidden campaign relationships.
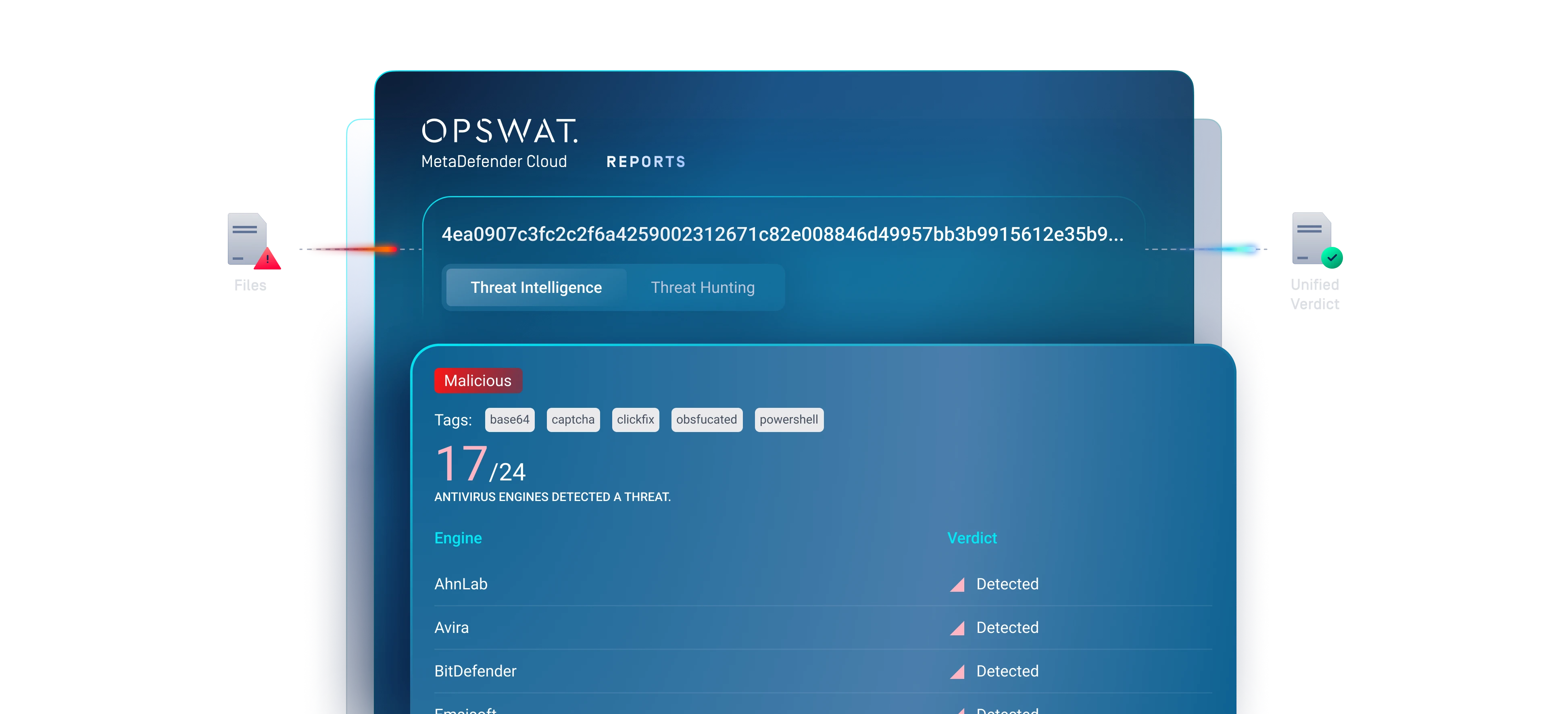
Behavioral Intelligence vs Reputation-Only Feeds
Traditional threat intelligence platforms primarily rely on known hashes, IP addresses, and domains. While useful, these indicators are easy for adversaries to rotate.
This intelligence engine correlates behavioral artifacts such as execution flow, persistence methods, configuration patterns, and infrastructure reuse. That shift moves detection higher up the attacker’s operational stack, making evasion more costly and more visible.
The result is intelligence that detects relationships across campaigns rather than isolated artifacts.

Deploy Intelligence Where Your Security Operates
Use cloud APIs, hybrid enrichment, or offline intelligence packages to deliver threat context to SIEM, SOAR, and hunting workflows.

Hybrid Deployment
Cloud correlation with local analysis. Supports enterprise SOC and TIP workflows.
Air-Gapped Support
Offline reputation packages. Intelligence continuity for regulated environments.

Cloud-Delivered Intelligence
Real-time API enrichment. Continuously updated global datasets.
Trusted by Leading Global Enterprises
OPSWAT is trusted by over 2,000 organizations worldwide to protect their critical data, assets, and networks
from device and file-borne threats.
Resources
MetaDefender Threat Intelligence

SANS Detection & Response Survey