Every day, organizations generate, transfer, and receive millions of files through cloud apps, collaboration platforms, secure portals, and email. These files are often treated as routine data objects, yet they serve as ideal carriers for malware, data leaks, and denial-of-service payloads.
Traditional antivirus tools and perimeter filters are no longer enough. To stay ahead of modern file-borne threats, enterprises are moving toward multi-layered file security platforms that provide analysis, verification, and sanitization before files are used or shared.
This blog explains why a modern file security strategy matters and how MetaDefender Core uses capabilities such as Deep CDR™ Technology (Content Disarm and Reconstruction), File Type Verification, Metascan™ Multiscanning, Proactive DLP™ (Data Loss Prevention), and Adaptive Sandbox to reduce file risk at every entry point.
Files Are the Most Overlooked Threat Vector in Your Infrastructure
While most security investments focus on endpoints, identity systems, and network firewalls, files remain one of the most under-protected surfaces in the digital environment assets for most organizations.
Every day, files move through enterprise infrastructure. They are uploaded via web forms, shared through collaboration tools, synced to object storage, or attached to emails. Each one can carry zero-day malware, embedded scripts, or policy violations that bypass traditional tools.
MetaDefender Core is a modern file security platform that enables organizations to inspect, sanitize, and verify every file before it is stored, shared, or executed. This reduces file-based risk while preserving the speed and flexibility of business operations.
Common File-Based Attack Methods and Why Antivirus Alone is Not Enough
Denial-of-Service via File Uploads
Attackers use oversized files or mass file uploads to overwhelm storage or computing resources. These attacks often pass through upload forms and APIs undetected, particularly when archives are used to disguise payload size.
MetaDefender Core helps prevent file–based denial-of-service attacks by:
- Enforcing limits on file size and quantity.
- Controlling archive extraction behavior to prevent decompression overload.
- Verifying file types to reject high-risk or misidentified formats.
Archive-Based Attacks and Concatenated Archives
Some attackers create archive files that contain multiple nested layers or concatenated streams. These files may appear small but can expand dramatically during decompression. Concatenated archives may confuse standard extractors and allow malicious files to bypass scanning.
MetaDefender Core protects against archive-based exploits by:
- Analyzing archive depth and structure prior to decompression.
- Setting limits on total extracted size and file count.
- Detecting anomalies in concatenated archives or malformed headers.
Why Archive Files are the #1 Choice for Cyberattacks
Malware Embedded in Common File Formats
Threat actors often embed malware in familiar file formats such as Word documents, Excel spreadsheets, or PDFs. These files may contain scripts, macros, or hidden executables that are obfuscated to avoid detection. Many of these threats evade single-engine antivirus solutions.
MetaDefender Core provides stronger protection against embedded malware through:
- Metascan™ Multiscanning using over 30 leading anti-malware engines.
- Deep CDR™ Technology (Content Disarm and Reconstruction) to remove active content like macros and scripts.
- Behavioral inspection via Adaptive Sandbox for evasive threats.
File Replacement Exploits
In asynchronous or delayed processing environments, attackers may upload a clean file to pass validation, then replace it with a malicious version before it is stored or executed. This race condition can lead to files being trusted when they should not be.
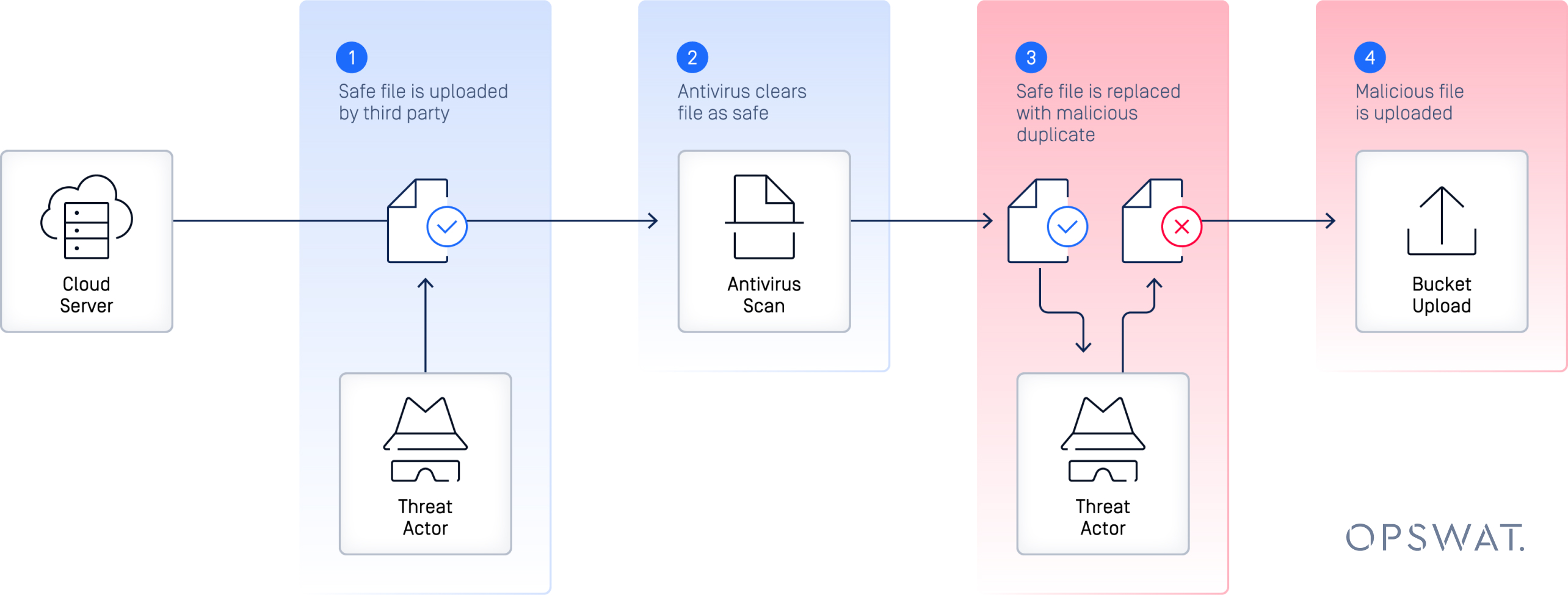
MetaDefender Core addresses this risk by:
- Scanning and sanitizing files before storage or further handling.
- Using immutable workflows that prevent mid-process changes.
- Performing final validation before files are used or delivered.
Malicious or Sensitive Files from Trusted Sources
Even files from trusted users, partners, or internal systems may contain malware or sensitive data that should not be shared. Without consistent scanning, these files can introduce risk unintentionally.
MetaDefender Core enforces zero-trust file policies by:
- Verifying the true file format, regardless of file extension.
- Scanning for PII, PHI, or other regulated data using Proactive DLP™.
- Applying consistent controls across upload portals, email systems, and storage platforms.
Advanced Technologies That Power MetaDefender Core

Building a Multi-Layered File Security Strategy
Files are used in phishing, malware delivery, lateral movement, and data exfiltration. Despite this, most enterprise systems treat files as trustworthy by default once they pass an antivirus scan.
A zero-trust file security strategy treats every file as potentially harmful until proven otherwise. That requires multi-layered tools that can inspect, sanitize, and validate every file, regardless of its source, format, or intended use.
MetaDefender Core supports this strategy by combining detection and prevention. It helps organizations neutralize threats at the point of file entry, across email, storage, web uploads, and more.
Closing Thoughts
Files are now one of the most common attack vectors in enterprise environments. Relying on antivirus detection alone leaves critical gaps that attackers are eager to exploit. Modern file security requires layered inspection, active content removal, and policy enforcement.
MetaDefender Core provides the platform technologies needed to close these gaps. With Deep CDR™ Technology, Metascan Multiscanning, Adaptive Sandbox, and Proactive DLP, organizations gain visibility and protection across every file workflow.
To reduce risk and operate with confidence, enterprises must secure every file before it is opened, shared, or stored.

