Most Security Teams Are Scanning Archives the Wrong Way
Ask most security teams how they handle incoming ZIP files and you’ll hear the same answer: “We scan them.” What they mean is that their anti-malware or EDR solution reads the archive’s header, extracts the contents, and scans for known threats. The problem is that most scanning engines trust what an archive declares about itself. Attackers have known how to exploit that assumption for years.
In early 2026, researchers published details of a technique called Zombie ZIP (tracked as CERT/CC advisory VU#976247 and CVE-2026-0866), demonstrating how a deliberately malformed ZIP archive can bypass 98% of anti-malware engines. Evasion does not require zero-day exploits or nation-state tooling. It requires only a hex editor and an understanding of how loosely most security tools parse archive metadata.
What Zombie ZIP Is
Zombie ZIP is an evasion technique that exploits a structural inconsistency in the ZIP archive format. Rather than relying on a vulnerability in a specific application or operating systems, it abuses the ZIP specification itself to create a discrepancy between the archive’s declared structure and its actual contents, allowing it to bypass scanners across platforms.
A standard ZIP archive uses a header field called the Compression Method to indicate how the stored data is encoded. A value of Method=0 specifies that the data is stored uncompressed while Method=8 indicates DEFLATE compression. A Zombie ZIP deliberately sets this field to Method=0 even though the payload remains DEFLATE-compressed. The CRC-32 checksum is calculated against uncompressed data, not the compressed bytes actually stored in the archive.
The result is an archive whose declared structure does not match its actual contents. Most security tools lack a mechanism to validate that discrepancy.
How Zombie ZIP Performs the Evasion
When a security scanner encounters a Zombie ZIP, it reads the declared compression method from the header, treats the payload as raw uncompressed bytes, and scans those bytes for known malicious signatures. Because the payload is actually DEFLATE-compressed, the scanner reads high-entropy compressed data that matches no signatures. It returns a clean verdict and passes the file through.
The attacker’s loader on the target system operates differently. It ignores the declared method field, forcibly decompresses the data stream as DEFLATE, and recovers the payload in full.
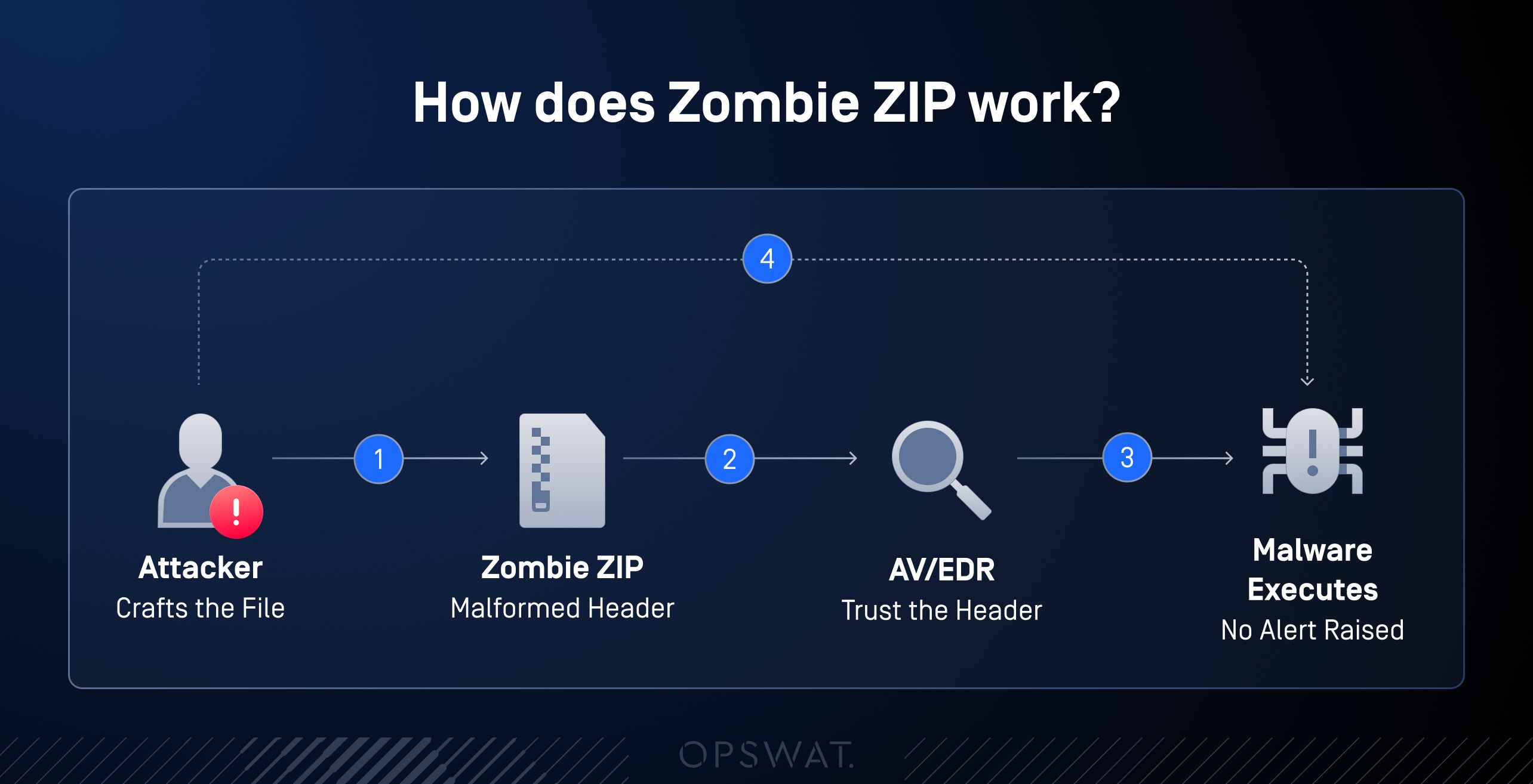
- The attacker sets the ZIP header to Method=0 (STORED) while the actual payload remains DEFLATE-compressed. The CRC-32 checksum is also deliberately mismatched.
- The AV or EDR scanner reads Method=0, treats the payload as raw bytes, encounters only compressed noise, matches no signatures, and returns a clean verdict.
- A custom attacker-controlled loader ignores the declared method, force-decompresses the DEFLATE stream and recovers the full payload for execution.
- The payload deploys on the endpoint — ransomware, RAT, or credential harvester — while every perimeter scanner reported the file as clean. No alert is raised.
Most scanning engines trust archive metadata implicitly. They process what the file declares itself to be, not what it actually contains. This assumption extends well beyond ZIP and is what attackers exploit across multiple archive formats.
Declared Format does not Equal Actual Format
Zombie ZIP is one example of a broader attack class known as format confusion. Attackers routinely:
- Rename executable files with benign extensions (.exe to .pdf, .js to .txt)
- Embed polyglot files that are simultaneously valid in two different formats
- Use obscure or legacy archive containers (RAR4, ACE, ARJ, 7z with non-standard headers) that many scanners skip entirely
- Nest archives within archives to exhaust scanner recursion limits
- Corrupt just enough metadata to make the archive unscannable, causing many tools to silently pass the file rather than block it
Each of these techniques exploits the same fundamental weakness: relying on what the file declares itself to be rather than performing deep verification of its actual structure.
What Happens When It Gets Through
CERT/CC VU#976247 formally acknowledges that the archive scanning layer has a structural blind spot already being exploited in live ransomware and RAT campaigns.
A Zombie ZIP that passes perimeter inspection can deliver a ransomware dropper, a remote access tool, or a credential harvester to an endpoint without triggering an alert. In sectors where files constantly cross trust boundaries, such as financial services processing client documents, healthcare systems receiving insurance forms, and government agencies handling contractor submissions, the exposure is continuous and invisible under conventional scanning.
How to Detect and Prevent Zombie ZIP
Detecting a malformed archive is useful, but detection alone is insufficient. The most effective response is archive reconstruction as part of a sanitization pipeline.
Instead of trusting the archive as received, the platform extracts its contents into a controlled environment, inspects every extracted file, and rebuilds a clean archive from the verified content. The output is generated from scratch with accurate, well-formed metadata.
This approach eliminates the Zombie ZIP attack vector. There is no malformed header to mislead the scanner because the header is created by the sanitization engine. Whether the original archive declared Method=0 or used DEFLATE compression is irrelevant, because reconstruction requires a successful extraction first. If the payload cannot be extracted by a standards-compliant decompressor, it is blocked, not passed.
Layered Prevention with OPSWAT MetaDefender Core™
Defeating Zombie ZIP and format confusion attacks require more than a single inspection method. MetaDefender Core applies three technologies in sequence: File Type Detection, Archive Extraction, and Deep CDR™ Technology. Each addresses a different dimension of the threat, and together they close the structural gaps that signature-based scanning cannot.
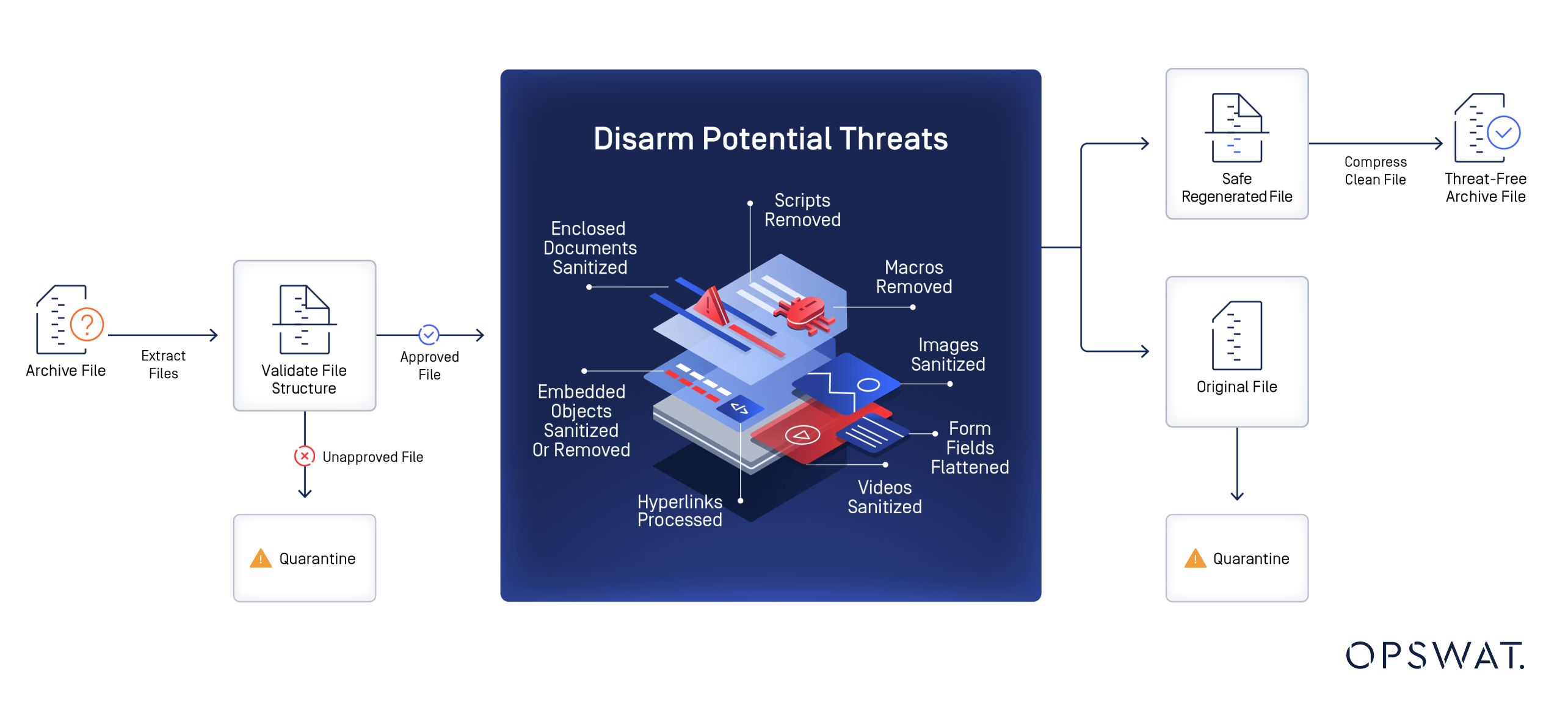
File Type Detection is the first verification step. Rather than trusting the declared file extension or header, it analyzes the actual byte structure of the file using magic byte analysis, format-aware parsing, and an AI model trained to identify spoofed or mismatched types. In a Zombie ZIP, the declared Method=0 is structurally inconsistent with the high-entropy content of the compressed payload, and that mismatch is detectable at this stage.
Archive Extraction processes the real data stream rather than relying on declared metadata. It either successfully extracts the content for per-file scanning or flags the archive as unextractable due to the CRC mismatch. A configurable policy determines whether extraction failures result in a block rather than a silent pass.
Deep CDR™ Technology sanitizes each extracted file and rebuilds the archive from the verified output. It removes potentially malicious active content, including macros, embedded scripts, and exploit code, while preserving document usability. The delivered archive is generated entirely by the sanitization engine, so there is no malformed structure to inherit from the original.
Key Takeaways
- Verify file type before you scan. Zombie ZIP exploits the assumption that declared file type equals actual file type. File Type Detection catches the structural mismatch before any signature scan runs.
- Extract before you decide. Scanning an archive without extracting its contents means scanning the container, not the payload. Archive Extraction exposes what is actually inside for per-file inspection.
- Rebuild, do not just inspect. Deep CDR™ Technology sanitizes each file and rebuilds the archive from scratch. The output contains no malformed structure because none of the original archive metadata carries over.
- Treat extraction failure as a block condition. A Zombie ZIP that cannot be extracted by a standards-compliant decompressor should be blocked and flagged, not passed silently as a corrupted file.
- Configure your platform, not just your signatures. Zombie ZIP evades signature-based scanning by design. The response is workflow configuration that enforces extraction, type verification, and sanitization at every point where files enter the environment.

