The New Year is in full swing here at OPSWAT. The Gears team has been working really hard, and our latest Gears release includes several exciting new features as well as important performance improvements and bug fixes.
- AppRemover beta release
- Customizable text for the remediation page
- Allowlist and blocklist disk encryption by vendor and version
- New API using browser cookies
- New Gears integration partner: Portnox
In addition to features and fixes, we've made another change. Our release names are now public, starting with this one: Minnesota.
If you're more of a numbers person, you should read our new knowledge base article that describes what our Gears client version numbers mean.
AppRemover Beta Release
Back in 2008, OPSWAT released a utility called AppRemover. It was designed to be a lightweight and powerful tool for thoroughly uninstalling security applications like antivirus and anti-spyware. Nearly 7 years later, AppRemover has been downloaded over 4 million times and is still one of OPSWAT's most popular products.
In 2014, AppRemover was rebuilt using OESIS V4 Removal Module, and because Gears uses OESIS V4 we decided to build AppRemover right into Gears for Windows. Adding similar functionality for Mac users is planned for mid-2015
Enabling AppRemover
Windows users downloading Gears without creating an account will automatically see AppRemover. For Gears customers with Gears Cloud accounts, further action may be necessary to enable AppRemover during the beta period. If you don't see it in your Gears client, but you'd like to, simply follow these steps:
If you don't have Gears client customized already (default):
- Download this zip file
- Log in to OPSWATGears.com
- Go to Configure > Account Settings
- Under Device Settings, click the UPLOAD button
- Select the zip file you downloaded in step 1
- Click Save

Example of edited XML
If you have Gears client customized already:
- Log in to OPSWATGears.com
- Go to Configure > Account Settings
- Under Device Settings, click the link "Download current branding package"
- Extract the .zip file that is downloaded
- Open GearsApp_brand.xml in your favorite text editor
- Find this tag (or your modified version of it): <translation var="Show-Malware" text="hide-feature" optional="true" />
- Between that tag and the next section, insert: <translation var="Show-AppRemover" text="" optional="true" />
- Save the XML and re-zip the package with any name you prefer
- Back on OPSWATGears.com, click the UPLOAD button and upload your updated .zip file
- Click Save
Using Gears AppRemover
In addition to removing antivirus and anti-spyware applications, AppRemover will uninstall potentially unwanted applications like peer-to-peer file sharing clients, and toolbars. The total number of supported applications for removal is currently around 400. By the time Gears AppRemover is out of beta in a few weeks, it will support more application types and well over 1000 applications!
AppRemover in Gears functions just like the standalone version of AppRemover. Once you open the program, it scans your installed applications and displays those that are available for removal. Select the applications you wish to remove, and then follow the onscreen instructions and AppRemover handles the rest.
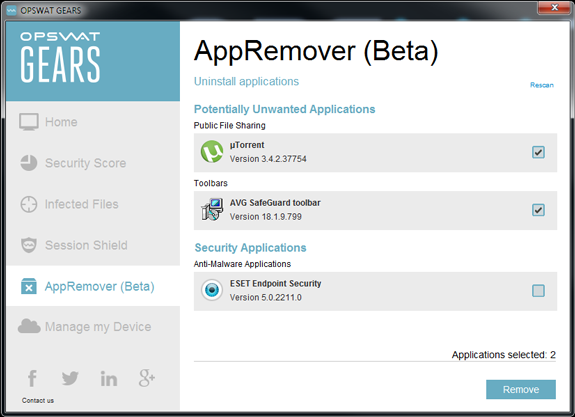
Select unwanted applications to be removed
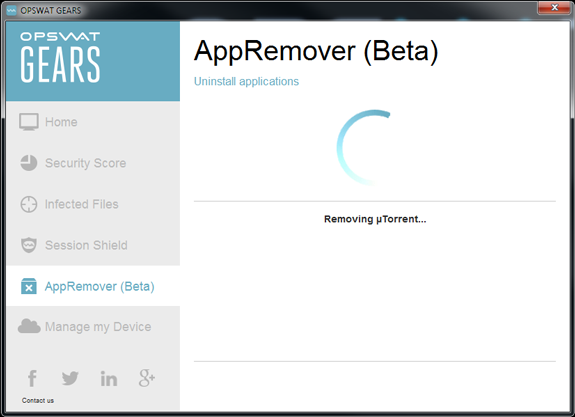
Sit back and let AppRemover do the work
Customizable Text for Remediation Page
Last December we added the ability for Gears customers to personalize remediation pages. This included the ability to customize page title, images, colors, etc. but it lacked one really important feature: customizable text. We've now added this ability and we think the remediation page is pretty cool.
To customize the text on your remediation page:
- Log in to OPSWATGears.com
- Go to Configure > Rebranding
- Click on the text you want to change
- Make your edits
- Click save
That's it! This new feature supports formatting, hyperlinks and even non-Latin alphabets.

Edit text right in the browser, then click save

The remediation page updates immediately with the changes
We also made a few other enhancements to the remediation page customization:
- Add 'center' alignment option for logo
- Link the minimize/maximize arrow color to the Category header color
Allowlist and Blocklist Disk Encryption by Vendor and Version
While Gears already has unmatched support for detecting disk encryption state, we've taken things one step further by providing our users with the ability to specify exactly which encryption vendors, products and versions they approve to consider a device compliant.

This advanced encryption policy is implemented the same way as our advanced antivirus policy feature that was introduced last November. If you haven't looked at the advanced antivirus selection feature, now is a good time to review both.
To use this new feature:
- Log in to OPSWATGears.com
- Go to Configure > Device Policy > Encryption >
- Check the box for: "Report if no encryption application is installed"
- Click on the button for "Advanced"
- Select "Require a specific encryption product"
This will enable the feature, and then to configure it simply move products from the right side to the left, and click save.
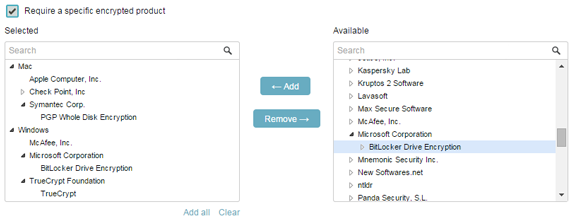
Simple yet powerful controls
The device compliance checking will only be as strict as your selections. So if you select 'TrueCrypt Foundation: TrueCrypt' without selecting a version, then all versions of TrueCrypt will be allowed. If you then add 'TrueCrypt: 5.x', then only the 5.x version of TrueCrypt would be considered compliant.
New API Using Browser Cookies: "NAC for SaaS"
Gears offers incredible benefits when paired with a secure access solution. Historically those solutions have been NAC, IPsec VPN, SSL-VPN, DNS/DHCP servers, and even managed switches. Now with organizations of all sizes embracing SaaS or cloud-hosted technologies to increase productivity and mobility, it's critically important that more focus be paid in endpoint security compliance.
Technologies exist to help IT departments manage their attack surface while transitioning to the cloud, but most (if not all) fall short with regard to endpoint posture and security policy compliance. We recognized this gap and started developing a new API for Gears that would allow for various services to get endpoint compliance information directly from Gears and gate access to SaaS products accordingly.
The new API, our browser cookie API, allows web applications to query a unique identifier for the device, see which account it is managed by, and check if it meets that account's compliance policy. The unique identifier is queried directly from the cookie, whereas the account and compliance checks can be fetched from the cookie or from our REST APIs (by using the unique identifier).
Using Gears to control access to software is nothing new — as long as that software was locally installed on the endpoint. The unique functionality provided with the browser cookie API is that purely hosted software can now be integrated as well — no browser plugin, ActiveX or Java needed.
Go to our developer portal for detailed documentation of this API.
New Gears Integration Partner: Portnox
The team at Portnox makes some cool products. Their NAC is software-only and easy to deploy. No network infrastructure changes needed, like port mirroring or network taps. For an agentless solution, it even has some impressive policies. For organizations using Portnox who are looking for more detailed endpoint policies, Gears integrations are now simple and easy to setup.
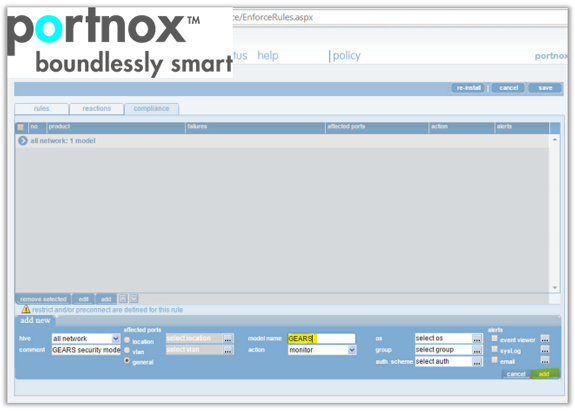
Portnox policy creation for Gears integration
The integration is as simple as configuring a Portnox policy to check certain aspects of the Windows and Mac computers in question. An easy to follow Portnox integration guide is now available on our website.
Other Changes
Cloud updates
- Event log time filters now properly enforced
- Rename Advanced Threats to Infections
- Various bug fixes and UI enhancements
Client updates
- OS X 10.6 is no longer supported
- New look for installers on Windows and Mac
- Malware scanning license usage is more efficient
- Reporting status for 3rd party patch management status is fixed (Windows)
- Fixed an issue causing high CPU usage in WmiPrvSE (Windows

