Why Secure Data Flow is a Cybersecurity Priority for Pharma
Pharmaceutical companies are prime targets of cybercriminals because they hold valuable intellectual property, sensitive personal data, and operate complex IT and production systems that can’t easily be taken offline. High-profile incidents, such as the 2023 ransomware attack on Sun Pharmaceutical Industries where more than 17 terabytes of data were reportedly stolen, show how breaches of corporate IT can quickly escalate into significant operational disruption, regulatory exposure, and business risk.
As discussed at the World Economic Forum’s C-suite panel on scaling AI, pharma organizations face growing pressure to modernize and scale digital operations while complying with complex global regulations. Achieving this requires standardized processes, strong data governance, and assured data integrity built directly into the system architecture and operations. Without these foundations, “it’s garbage in, garbage out” — as noted by Amin Nasser, President and CEO of Saudi Aramco, during the panel discussion.
Where Reliable Data Transfer Became a Security Risk
Reliable OT-to-IT data transfer meant a security risk for this pharmaceutical company, as well. Validated manufacturing and laboratory data had to be replicated without allowing any IT system to initiate connections back into production. Batch records, test results, and LIMS exports had to move from the OT zone into corporate QA and analytics, but traditional transfer methods weakened isolation and increased cyber exposure in high-security environments.
4 Key Security and Operational Challenges
Data integrity risks from intermittent transfer failures and synchronization issues
Security exposure caused by temporary connections that weakened OT isolation
Operational friction between security, manufacturing, and QA teams when transfers failed or required manual intervention
Audit pressure due to incomplete or unreliable transfer records supporting regulated processes
What Security Teams Needed to Move Forward Safely
The company needed a safer way to move critical manufacturing and laboratory data out of production environments without putting those environments at risk. Leadership set out to remove the constant tension between data availability and strict OT isolation by defining 5 key requirements.
5 Security Requirements
- No return path into production, so corporate IT systems could never initiate network connections back into validated OT environments
- Assured, lossless data delivery, ensuring batch records, historian data, and LIMS outputs arrived intact and in sequence
- Support for required data replies, including acknowledgements and sequence control, without breaking isolation
- No changes to validated systems or workflows, preserving existing manufacturing and QA operations
- Audit-ready traceability, with reliable records for internal reviews and external inspections
Previous approaches made it hard to maintain security, reliability, and compliance at the same time. A purpose-built approach to IT–OT data transfer solved this by supporting all three without exception.
From Air Gapping and Manual Transfers to Assured Data Flow
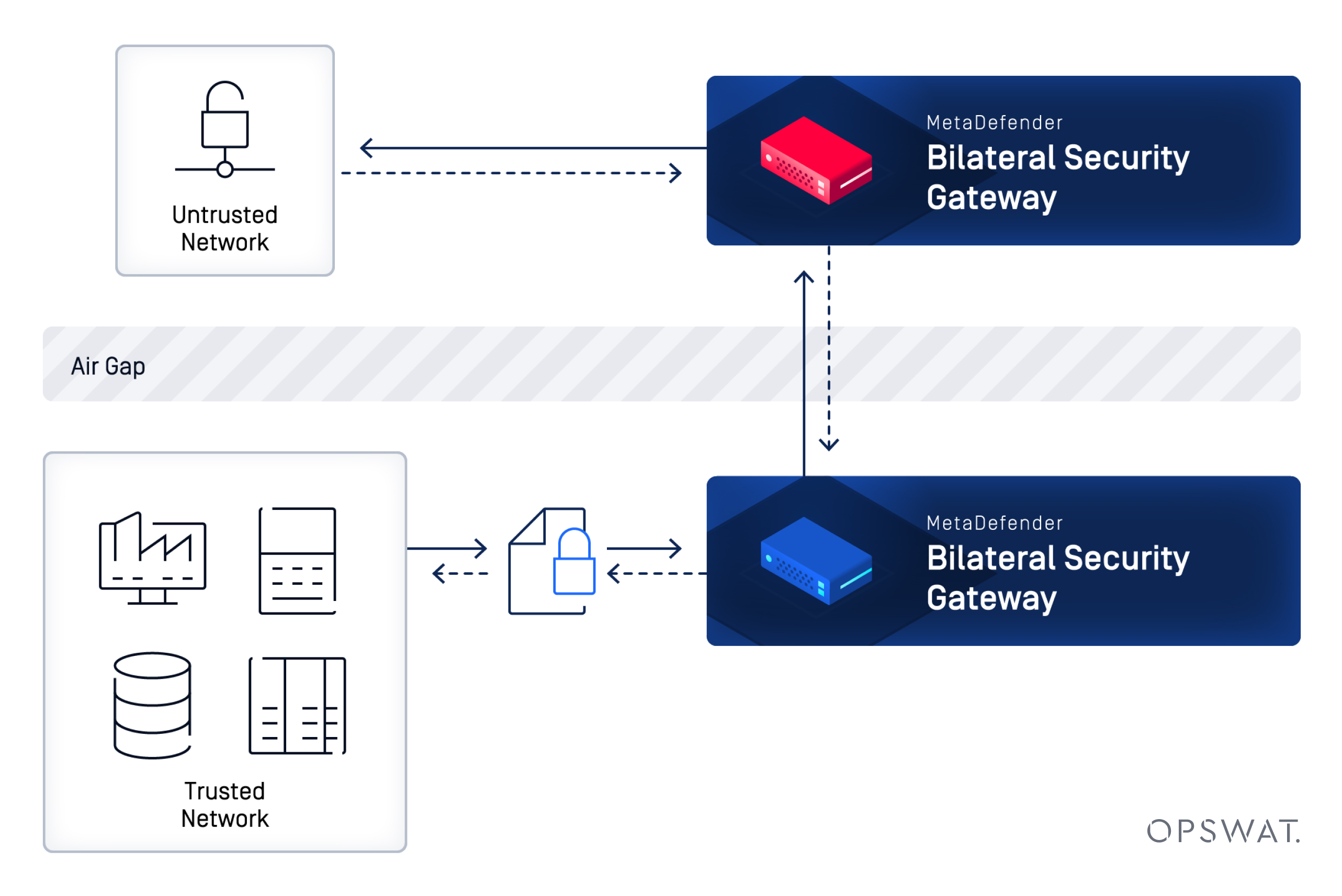
Reliable, lossless data transfer became the new baseline, without reopening risk into production. By deploying MetaDefender Bilateral Security Gateway™ (BSG), the company established a secure, resilient way to move validated manufacturing and laboratory data from OT environments into corporate systems.
The new solution enabled the organization to strictly enforce one-way OT-to-IT data flows, while still supporting the acknowledgements, sequence control, and database replies required by industrial historians and SQL-based systems. This allowed data to arrive intact and in order, without creating a network return path into production or requiring changes to validated applications.
Security and Operational Outcomes
- Lossless OT-to-IT data replication: batch records, historian data, and production logs reached QA and analytics systems without synchronization issues
- Secure handling of required data replies: SQL databases and industrial historians synchronized correctly without introducing a return path
- Strict OT isolation: validated production systems stayed segmented from corporate IT and external networks
- No disruption to validated environments: no changes required to existing applications or manufacturing workflows
Secure isolation and reliable data delivery were no longer competing priorities. MetaDefender Bilateral Security Gateway removed the need for fragile configurations and security exceptions and established a data transfer model where availability, integrity, and isolation were enforced directly by the system architecture.
Extending Secure Data Flow Across the Enterprise
The company can now extend this same isolation-first model to additional parts of the business without introducing new risks. By applying assured data delivery and strict separation beyond core manufacturing, leadership sees a clear path to safely supporting R&D collaboration, advanced analytics, and consistent data movement across global sites.
Next Areas for Secure Adoption
- Expanding secure data exchange into R&D environments where research and laboratory teams share data with corporate systems without exposing sensitive or regulated assets
- Supporting advanced analytics and reporting initiatives by safely feeding production and quality data into centralized analytics platforms
- Standardizing secure data movement across sites using a consistent, policy-driven approach that scales with global operations
Secure isolation and reliable data delivery were no longer competing priorities. MetaDefender Bilateral Security Gateway removed the need for fragile configurations and security exceptions and established a data transfer model where availability, integrity, and isolation were enforced directly by the system architecture.
When Security and Availability Finally Align
With MetaDefender Bilateral Security Gateway, the organization now operates with lossless data flow, strict production isolation, and confidence that security controls are enforced consistently and without exception. For CISOs and security leaders facing similar challenges, this approach shows that reliable data access can be achieved without weakening cybersecurity controls.
Ready to secure your OT-to-IT data transfer without compromise? Talk to an OPSWAT expert to learn how MetaDefender Bilateral Security Gateway can support your environment.