In 2021, the Lazarus Group targeted security researchers with poisoned Visual Studio projects. In 2024, they planted malicious packages on PyPI using typosquatting. And in a campaign active since at least March 2025, the group shifted to spear phishing lures impersonating Edge Group, IIT Kanpur, and Airbus, targeting aerospace and defense organizations.
The delivery wrapper changes but the underlying strategy does not. Every iteration of the group's Comebacker backdoor relies on the same entry point: a file that a person opens and trusts. A recent analysis by ENKI details this latest Comebacker variant and reveals a meaningful technical evolution.
The dropper now uses a custom XOR/bit-swap algorithm instead of the RC4 or HC256 ciphers found in earlier versions. Loader stages have moved to ChaCha20 encryption. And for the first time, command-and-control traffic is encrypted with AES-128-CBC, abandoning the plaintext communications that made earlier variants easier to intercept.
Each of these changes is designed to evade signature-based detection, and each one is irrelevant if the weaponized file never reaches a user in the first place. For organizations handling classified programs, ITAR-controlled data, or mission-critical OT systems, a single compromised workstation can cascade into a supply chain incident.
This article examines how the Comebacker infection chain works, why traditional defenses struggle against it, and how prevention-first file security, applied at the email gateway, the removable media boundary, and every ingress point between, neutralizes the threat regardless of how the payload is obfuscated.
How File-Borne Attacks Bypass Perimeter Defenses
Nation-state actors like the Lazarus Group exploit email and removable media because aerospace and defense organizations rely on these channels to move files across networks. What makes Comebacker difficult to catch is what happens after delivery. The initial document appears legitimate, but once opened, it triggers a multi-stage execution chain designed to stay hidden.
Primary ingress points for Comebacker-style campaigns
Email:
Weaponized attachments disguised as supplier contracts, project updates, or invoices. ENKI identified four .docx lure documents impersonating Edge Group, IIT Kanpur, and Airbus in a campaign active since at least March 2025.
Peripheral media:
Infected USB drives or portable disks introduced into engineering or manufacturing networks during routine operations such as software updates or maintenance cycles.
A VBA macro decrypts a loader alongside a convincing decoy document using a custom XOR/bit-swap algorithm. The loader chains through multiple encrypted stages using ChaCha20. The final backdoor runs entirely in memory, leaving no artifacts on disk for endpoint tools to find.
By the time the backdoor phones home, all command-and-control traffic is encrypted with AES-128-CBC, blending in with normal HTTPS activity. Traditional perimeter tools see a user opening a document and generating encrypted web traffic, and nothing about that sequence triggers an alert.
The Lazarus Group is running parallel variants with different cryptographic implementations, ChaCha20 in one chain, HC256 in another, with identical backdoor functionality. A detection signature written for one will miss the other. This is the core problem with relying on detection alone. The attackers are specifically engineering their payloads to evade it.
Neutralizing Malware Before It Executes
So what do you do with a threat that's specifically built to evade detection? One option is to add more detection layers, more engines, more signatures, more behavioral rules. That helps, but attackers are already designing malware to evade that model. The other option is to start removing the elements that make a file dangerous. That is the operational logic behind OPSWAT’s technologies.
Every file entering the environment, whether through email or removable media, is first processed by Metascan™ Multiscanning. The file runs against 30+ anti-malware engines in parallel, combining signature-based detection with heuristics and machine learning. Where a single engine might miss a novel Comebacker variant, the probability that 30+ engines all miss it drops significantly.
But detection coverage, however broad, still depends on recognizing something malicious. Deep CDR™ Technology does not try to identify the payload. Instead, it strips the conditions that allow a payload to execute. This prevention layer removes active elements from files such as macros, scripts, embedded executables, and hidden objects. Then it rebuilds a clean, usable version of the document. This process works across 200+ file types and completes in milliseconds.
Deep CDR™ Technology in a Comebacker-style attack
Before Deep CDR™ Technology | After Deep CDR™ Technology |
|---|---|
| VBA macros trigger the loader chain | Macros stripped |
| Embedded executable drops multi-stage payload | Executable removed |
| Decoy document content (text, formatting, images) | Executable removed |
With the help of this technology, the dangerous elements are eliminated, and the usable content survives. The loader, the encryption stages, as well as the in-memory backdoor have no chance to execute. However, not every file can be sanitized. Executables, installers, and certain regulated documents must remain intact, especially in aerospace, defense, and critical infrastructure environments. For those files, a different kind of inspection is needed.
Detecting Evasive File-Based Threats That Cannot Be Sanitized
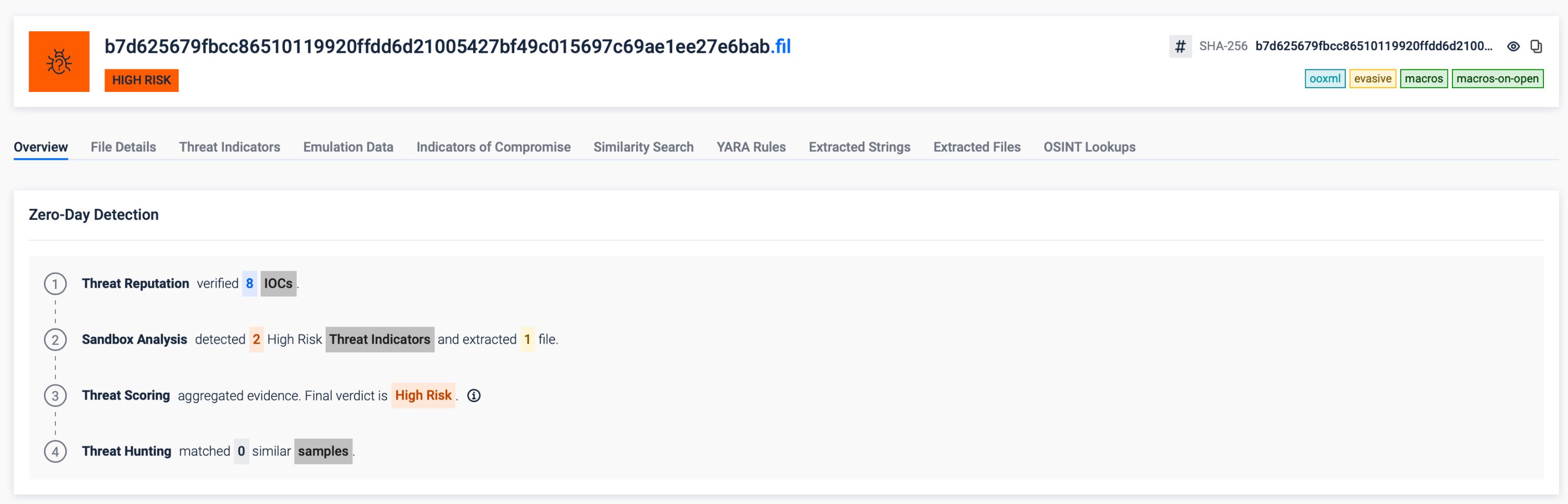
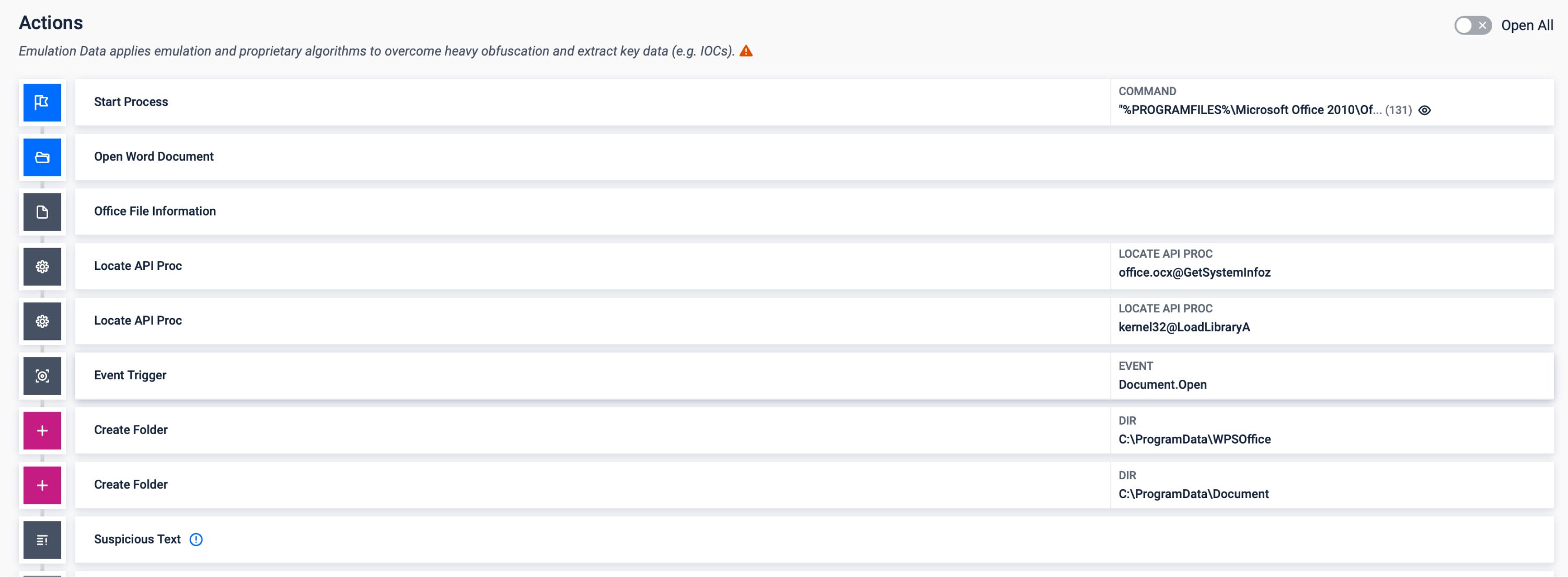
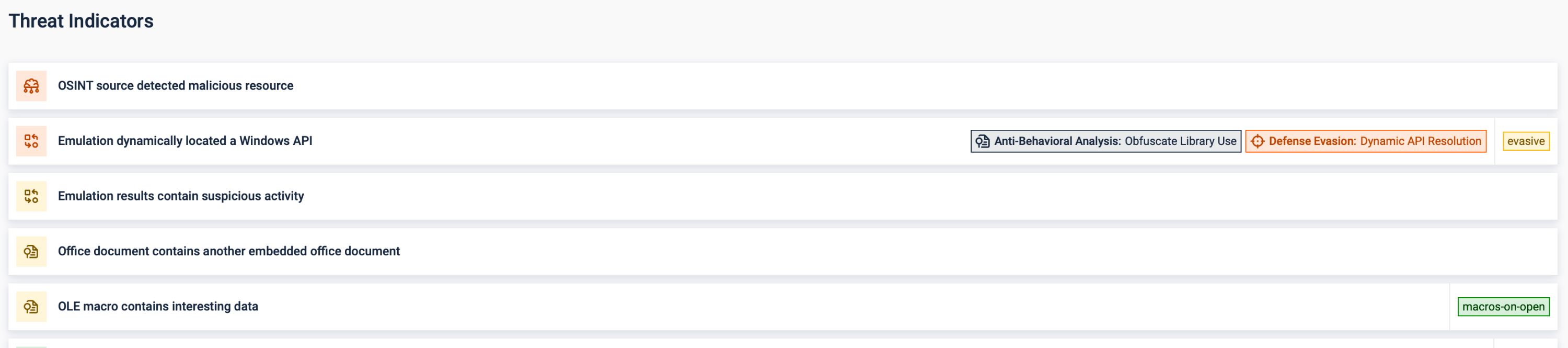
For files that must pass through intact, MetaDefender Aether's Adaptive Sandbox provides behavioral analysis through emulation-based threat detection. Instead of relying on signatures or static inspection, it observes how a file behaves during execution to expose hidden malicious activity.
ENKI's analysis shows that the Lazarus Group builds environment awareness into its malware, using delayed activation and evasion techniques designed to detect and bypass virtual machines. Rather than spinning up a full virtual machine, Adaptive Sandbox emulates execution at the instruction level, allowing analysis to occur without leaving artifacts that malware can detect.
VM-based vs emulation-based sandboxing
VM-based sandbox | Emulation-based Adaptive Sandbox |
|---|---|
| Detectable by anti-VM checks | Limited throughput in high-volume environments |
| Resource-intensive and slower verdicts | Up to 10x more efficient Verdicts in seconds |
| Resource-intensive and slower verdicts | Defeats anti-VM, anti-debug, and time-based evasion without manual tuning |
| Limited throughput in high-volume environments | Designed for high-throughput file analysis |

During analysis, Adaptive Sandbox observes runtime behaviors such as file system activity, process injection attempts, registry changes, and network communication. These are the patterns Comebacker's loader chain produces: the persistence shortcut in the Startup folder, the rundll32 execution, and the encrypted C2 beaconing.
Adaptive Sandbox also unpacks layered payloads and exposes hidden IOCs that signature-based tools never see. Results map to MITRE ATT&CK techniques and feed back into the platform as actionable threat intelligence, enabling faster decisions and more effective threat hunting.
Addressing the Pyramid of Pain with Unified Detection
Comebacker's evolution maps directly onto the Pyramid of Pain, which is the framework that ranks threat indicators by how costly they are for an attacker to change, from hashes at the bottom (trivial to rotate) to TTPs at the top (serious development effort to rewrite). The Lazarus Group has rotated the cheap indicators across every known Comebacker campaign since 2021.
Comebacker Mapped to the Pyramid of Pain
Pyramid of Pain Level | Comebacker Example |
|---|---|
| Hash Values | Distinct SHA256 hashes for each dropper and loader stage |
| IP Addresses / Domain Names | C2 domains rotated between campaigns: hiremployee[.]com, birancearea[.]com. Staging infrastructure hosted on office-theme[.]com |
| Network/Host Artifacts | AES-128-CBC encrypted C2 traffic replacing earlier plaintext communications; persistence shortcuts written to the Startup folder |
| Tools | Cipher progression from RC4 to HC256 to ChaCha20 across loader stages; custom XOR/bit-swap algorithm in the dropper |
| TTPs | Spear phishing with weaponized documents (T1566.001), reflective code loading (T1620), encrypted C2 beaconing (T1573.001), system binary proxy execution via rundll32 (T1218.011) |
The lower rows likely cost the Lazarus Group hours or days to change; rewriting loader architecture and execution patterns takes significantly more. A detection strategy focused only on the bottom rows is playing the game the group wants you to play. Every time you write a signature for one ChaCha20 key, they generate another.
From Sandbox to Unified Detection
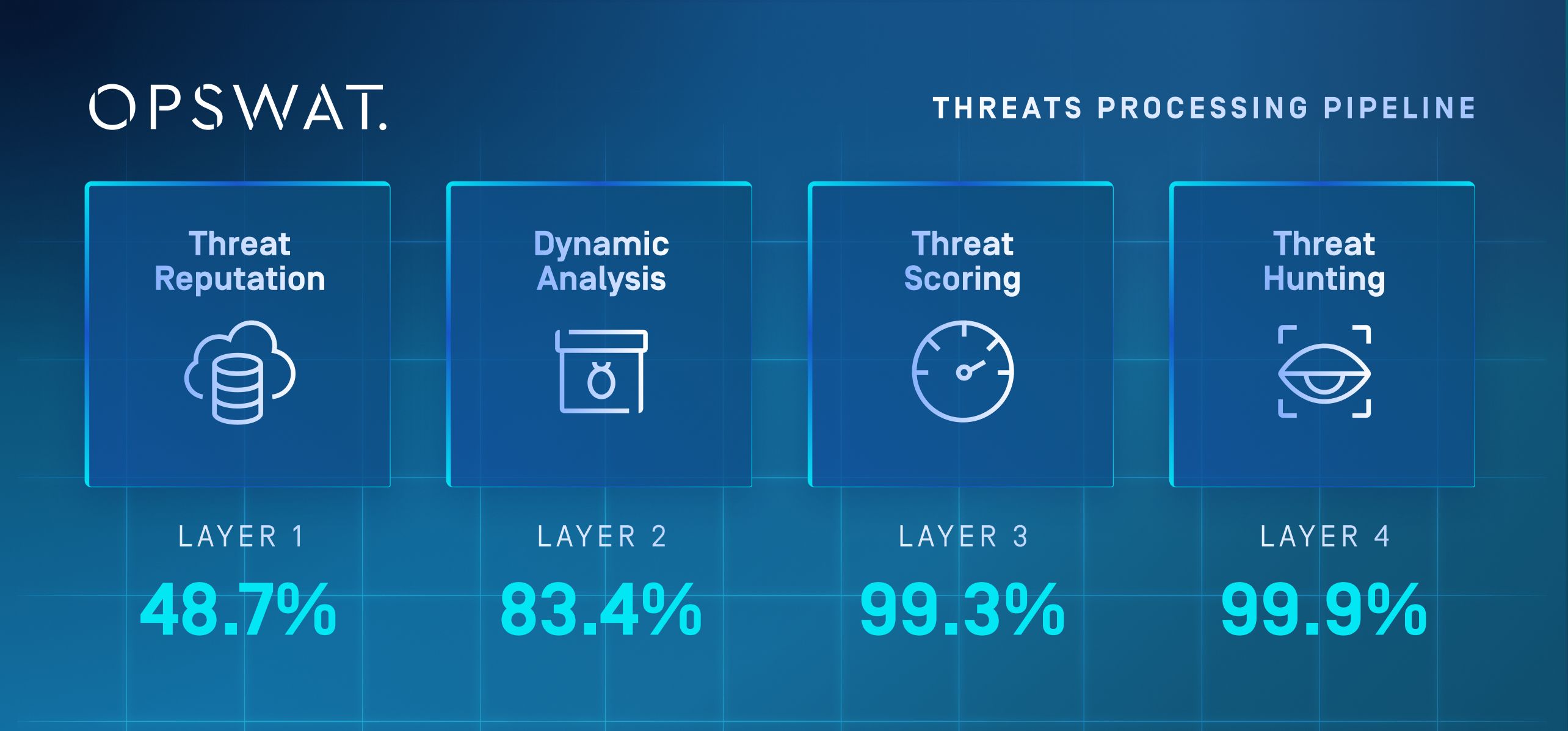
The previous section showed how Adaptive Sandbox exposes Comebacker's runtime behavior. MetaDefender Aether extends that capability into a unified pipeline that addresses the full Pyramid of Pain, processing every file through four progressively deeper layers.
Layer 1, Threat Reputation: Checks file hashes, IPs, and domains against 50 billion+ indicators. Known Comebacker infrastructure and previously seen samples are blocked immediately.
Layer 2, Dynamic Analysis: Escalates unknown samples to the Adaptive Sandbox's instruction-level emulation, exposing multi-stage loader chains, decryption routines, and rundll32 execution. Newly discovered IOCs feed back into Layer 1 automatically, strengthening detection for subsequent files.
Layer 3, Threat Scoring: Correlates behavioral signals and assigns a confidence-based risk score, weighing persistence mechanisms, process injection, and C2 activity. This is where the encrypted beaconing to Comebacker's C2 servers gets flagged, regardless of which cipher is in use.
Layer 4, Threat Hunting: Uses machine-learning similarity search across 100 million+ analyzed samples to link the 2025 variant back to the 2021 and 2024 Comebacker campaigns, even though the encryption scheme changed entirely. Forcing the Lazarus Group to abandon its loader architecture and execution model is a fundamentally different kind of pressure than chasing new file hashes.
Adding Pre-Execution Intelligence with Predictive Alin AI
Not every file needs full behavioral analysis. In high-volume environments, sending every unknown to the sandbox creates throughput pressure. OPSWAT's Predictive Alin AI addresses this as a pre-execution intelligence layer.
Predictive Alin AI uses machine learning to analyze structural and behavioral indicators of executables without detonation. Verdicts arrive in under 100 milliseconds at P99. Early testing shows 90% detection on executable files with 0.1% false positives. The engine runs online or offline with identical performance, making it deployable in the same air-gapped environments where Comebacker-style threats are most consequential.
2 Key Relevant Capabilities
- Zero-day prediction: Predictive Alin AI identifies previously unseen threats that signature-based engines miss, evaluating high-risk executable formats (PE, ELF, Mach-O, and PDF) before they run. Expanded file type coverage is on the roadmap.
- Reducing sandbox load: Files that the engine clears with high confidence proceed without sandbox analysis. The files it flags are prioritized for MetaDefender Aether's full four-layer pipeline, preserving sandbox capacity for files that genuinely need deep behavioral inspection.
Securing the Email Gateway Before Threats Reach the Inbox
Email is how Comebacker gets in. The lure documents were designed to land in an inbox and be opened. If the weaponized attachment never arrives, the infection chain never begins. MetaDefender Cloud Email Security™ integrates with Microsoft 365 and Google Workspace to scan and sanitize messages before they reach users. It operates inline with the mail flow, which means threats are stopped before delivery.
3-Layer Protection
- Attachments: Files are processed through Metascan™ Multiscanning and Deep CDR™ Technology. A Comebacker .docx with embedded VBA macros gets stripped and rebuilt before the recipient ever sees it.
- Links: URLs are analyzed and rewritten to block phishing pages and command-and-control redirections.
- Policy enforcement: Suspicious messages are automatically quarantined, sanitized, or escalated based on organizational rules.
For security teams, the impact is immediate. Fewer malicious emails reaching users means fewer alerts, fewer investigations, and less time spent on remediation. This allows teams to focus on higher-priority threats.
Protecting Removable Media and Air-Gapped Networks
USB drives and portable disks act as the bridge between external systems and control networks, making every transferred file a potential entry point. MetaDefender Kiosk™ and MetaDefender Media Firewall™ establish secure checkpoints at these boundaries.
Before any file from removable media enters a sensitive environment, it is scanned and sanitized using Metascan™ Multiscanning and Deep CDR™ Technology. This applies the same protection used at the email gateway to physical media. A weaponized document that relies on embedded macros or staged payloads is neutralized before it ever reaches the target system.
Operational environments introduce an additional challenge: media diversity. The kiosk supports 20+ media types, including USB-A, USB-C, SD cards, optical media, and legacy formats ensuring consistent enforcement even where older technologies remain in use.
Enforcement is what makes this effective. Once a file passes inspection, it receives a digital signature. OPSWAT's Media Validation Agent, installed on endpoints, blocks any removable media that lacks this signature. An unscanned USB drive simply does not work.
Centralized policies tie the process together. MetaDefender Core™ enforces quarantine rules, device restrictions, and audit logging across all media workflows, ensuring that every file crossing into an air-gapped environment is inspected, validated, and recorded. For organizations operating under NERC CIP, NIST 800-53, or ISA/IEC requirements, this level of control is essential. It provides verifiable evidence that every file entering the environment has been inspected and cleared.
Unified Prevention Across Every File Boundary
The technologies described in the previous sections, multiscanning, Deep CDR™ Technology, sandboxing, email security, and kiosk enforcement, are most effective when they operate under a single policy framework. MetaDefender Core™ provides that foundation.
The platform centralizes policies, telemetry, and enforcement across every file ingress point, from cloud email gateways to removable media checkpoints and network transfers. Instead of managing each control in isolation, security teams define file handling rules once and apply them consistently everywhere.
3 Critical Workflows enabled by MetaDefender Core
- Consistent file policies: The same scanning and sanitization rules apply regardless of how a file enters the environment.
- Automated remediation: Sandbox verdicts and reputation data trigger block, quarantine, or release decisions without manual intervention.
- Compliance and forensic readiness: IOCs and audit logs are exported to SIEM platforms for reporting and investigation.
This unified approach closes the gaps between individual controls. A sandbox verdict on a suspicious file at one boundary can immediately influence how similar files are handled across other boundaries. The operational result is faster detection, reduced analyst workload, and fewer opportunities for a weaponized file to move through uncoordinated gaps.
Ensuring that Comebacker Never Comes Back
The Lazarus Group will continue evolving its encryption schemes, loader chains, and delivery methods, but what it cannot easily change is its reliance on the file as the entry point. The MetaDefender Platform enforces prevention at every file boundary across email, removable media, and network transfers.
Multiscanning and Deep CDR™ Technology neutralize threats before execution. MetaDefender Aether's four-layer detection pipeline exposes what cannot be safely sanitized, operating across the full Pyramid of Pain and generating intelligence that strengthens defenses with every analysis.
Predictive Alin AI extends that intelligence to the perimeter, blocking predicted zero-days in milliseconds and preserving sandbox capacity for the files that need it most. MetaDefender Core ensures these controls operate under a unified policy framework.
Against Comebacker and the campaigns that will follow, the real question is not whether your defenses can detect the latest variant but whether a weaponized file can reach a user in the first place. To learn how OPSWAT can help enforce prevention across your environment, connect with an expert.

