Cisco Catalyst switches sit at the heart of enterprise networks, where the management plane is both a high-value target and a single point of operational failure. During proactive research in the OPSWAT Critical Infrastructure Protection (CIP) Lab, OPSWAT Unit 515 identified four vulnerabilities affecting Cisco Catalyst 9300 Series switches. Two of these issues (CVE-2026-20114 and CVE-2026-20110) can be chained by an authenticated low-privilege Web UI user to escalate privileges and force the device into maintenance mode, creating a full denial of service condition that may require on-site intervention to restore normal operations. In line with responsible disclosure best practices, OPSWAT reported these findings to Cisco PSIRT and coordinated validation and remediation prior to public disclosure.
Advanced Security Research in the OPSWAT CIP Lab
OPSWAT Unit 515 is OPSWAT’s elite red team, responsible for safeguarding OPSWAT products and contributing to the broader security community through rigorous technical research and responsible vulnerability disclosure. Beyond internal security assurance, Unit 515 conducts advanced vulnerability research and delivers professional penetration testing services to help organizations assess real-world risk and strengthen their overall security posture.
In July 2025, within the OPSWAT Critical Infrastructure Protection (CIP) Lab, Unit 515 initiated an in-depth security research effort targeting Cisco Catalyst 9300 Series switches, selected for their widespread enterprise adoption and mission-critical role in modern network infrastructures. The work uncovered multiple weaknesses that, when chained, materially elevate operational risk and threaten infrastructure resilience.
Responsible Disclosure Timeline
July 2025: OPSWAT Unit 515 identified multiple vulnerabilities affecting Cisco Catalyst 9300 Series switches during proactive security research conducted in the OPSWAT CIP Lab.
July 2025: A comprehensive technical report, including impact analysis and proof-of-concept validation, was submitted to Cisco’s Product Security Incident Response Team (PSIRT).
July 2025: Cisco acknowledged the report and initiated coordinated validation efforts with OPSWAT to reproduce the findings and assess their severity and impact.
August 2025: Cisco confirmed the reported vulnerabilities and began developing remediation measures and fixed releases.
Advisory Release: Cisco published official security advisories, and the reported vulnerabilities were assigned multiple CVE identifiers, including CVE-2026-20110, CVE-2026-20112, CVE-2026-20113, and CVE-2026-20114, in coordination with OPSWAT Unit 515.
Cisco CVEs Discovered by Unit 515
Unit 515’s research resulted in the identification of four distinct vulnerabilities affecting Cisco Catalyst 9300 Series switches, including privilege escalation, operational denial-of-service, stored cross-site scripting (XSS), and CRLF injection. Collectively, these vulnerabilities introduce risks to administrative trust boundaries, service availability, session integrity, and system log reliability - affecting both operational continuity and security monitoring capabilities.
CVE-2026-20114 and CVE-2026-20110 are the most operationally impactful when chained. A low-privilege Web UI user can escalate access and invoke a maintenance-mode operation, resulting in full denial of service that may require physical intervention to restore.
To reduce the risk of misuse, OPSWAT does not disclose exploit scripts or sensitive technical details of the affected Cisco components. The sections that follow provide technical insight into the root causes, exploitation logic, and security impact of each vulnerability, while remediation guidance is available through Cisco’s official security advisories and fixed releases.
Privilege Escalation and Command Injection Leading to Full Denial of Service
The Cisco Catalyst WebUI implements a role-based access control model in which the Lobby Ambassador account is assigned privilege level 0, representing a highly restricted role. This account is intended solely for limited guest management tasks within the WebUI and does not permit configuration changes, CLI access, or SSH authentication under normal operating conditions.
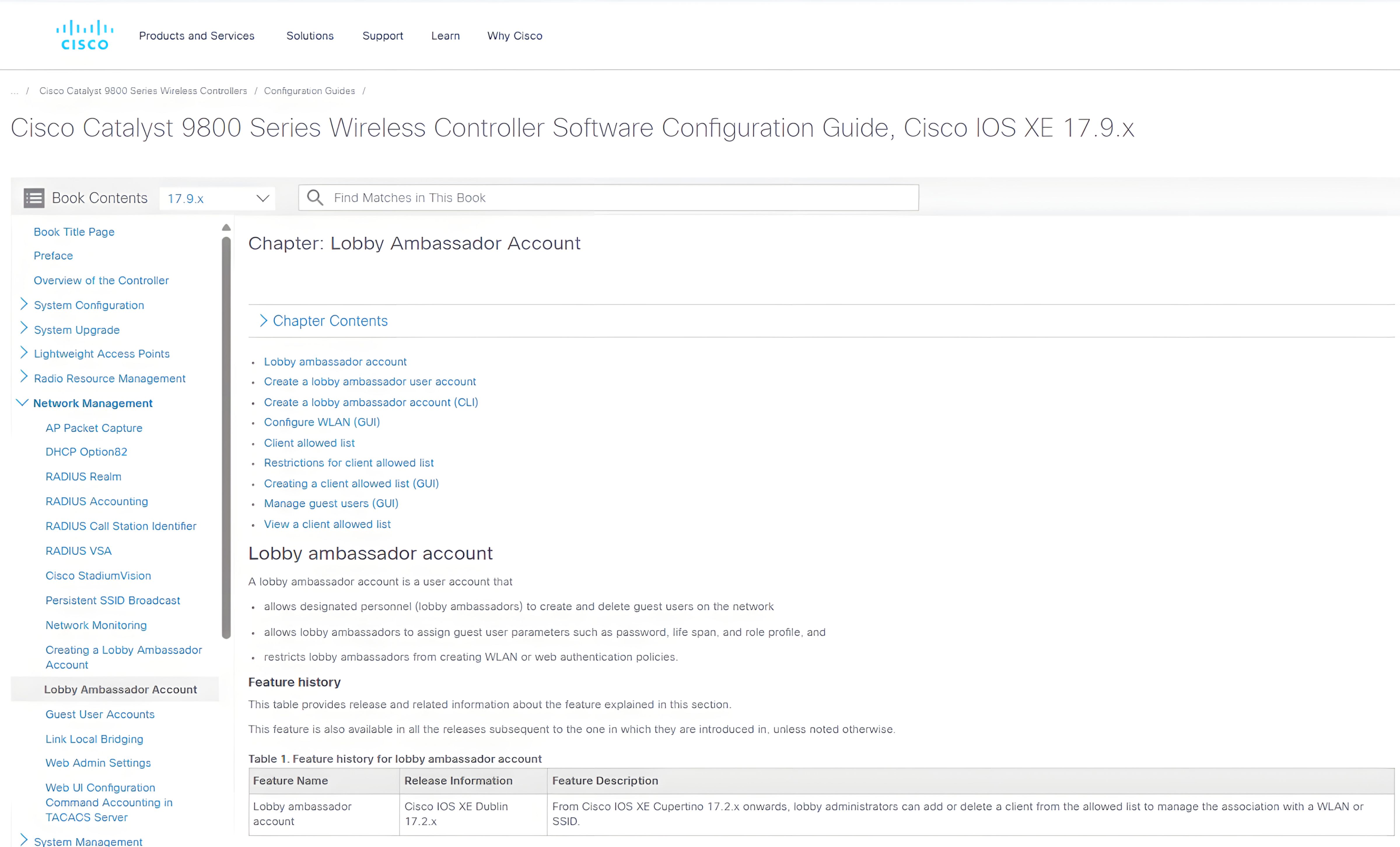
Through detailed reverse engineering and systematic analysis of internal WebUI execution workflows, Unit 515 uncovered a command injection vulnerability within functionality accessible to the restricted role. Exploiting this weakness allowed the creation of a secondary MAC-based user account with privilege level 1, effectively breaching the intended privilege boundary.
While a privilege level 1 account is not intended to perform high-privilege administrative operations, further investigation revealed insufficient command sanitization controls within the WebUI logic. These protections could be bypassed, enabling a second command injection condition to be exploited using the escalated level 1 account via WebUI.
Additionally, it was discovered that a system-level operation normally restricted to privilege level 15 administrators became reachable from the level 1 context. Specifically, the start maintenance command could be invoked, allowing the device to be forced into maintenance mode and resulting in service disruption.
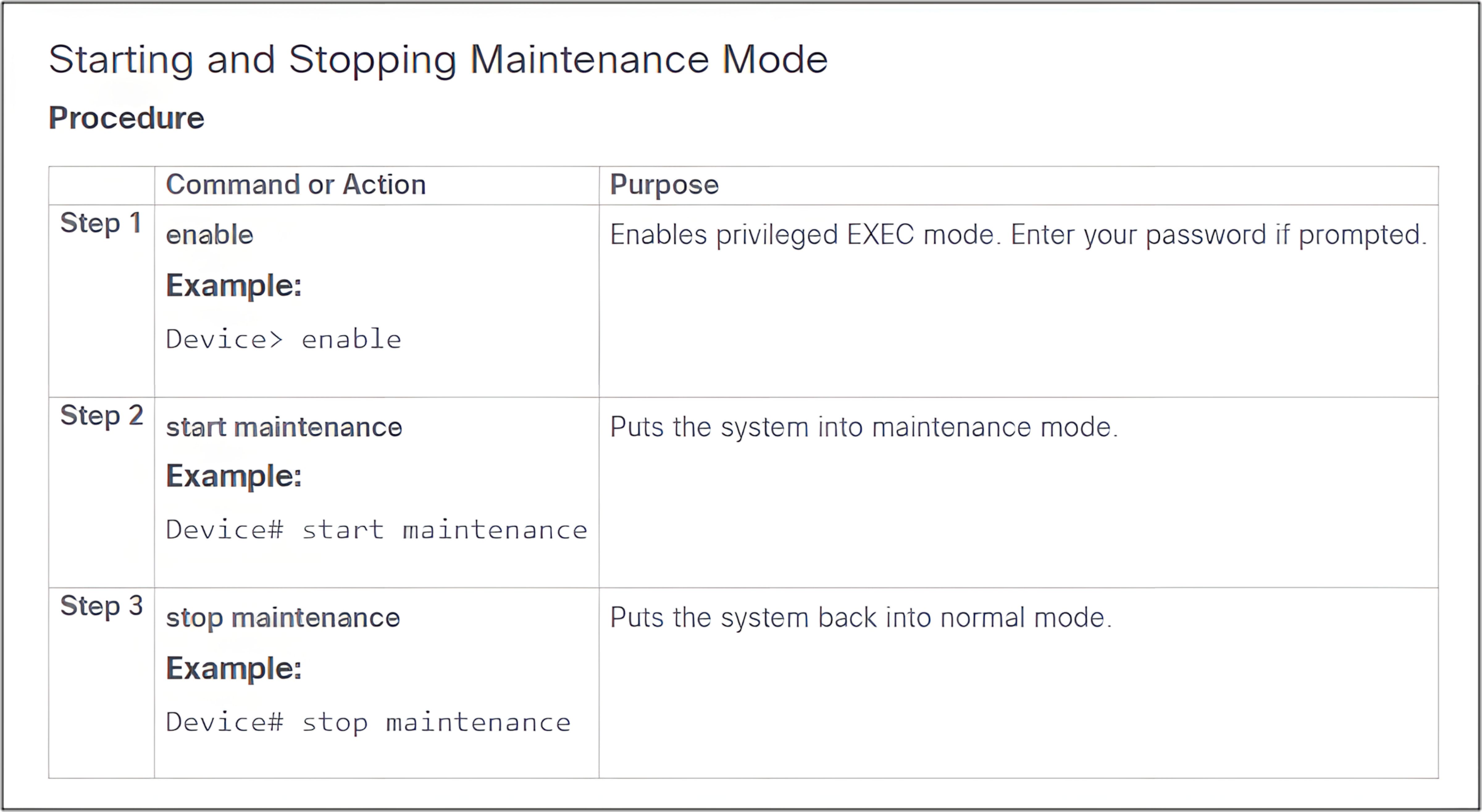
By chaining the initial privilege escalation with the subsequent command injection, the maintenance operation could be triggered - resulting in a persistent Denial-of-Service condition. In validated scenarios, restoring normal functionality required physical access to the device, significantly amplifying operational impact.
The video below illustrates the exploit chain in a controlled lab environment:
Following validation of the exploit chain, Unit 515 from OPSWAT promptly reported the findings to Cisco’s Product Security Incident Response Team (PSIRT) to support coordinated remediation and customer protection. After technical review and investigation, Cisco confirmed the reported issues and assigned two CVE identifiers to this exploit chain: CVE-2026-20114 and CVE-2026-20110.
Cross Site Scripting (CVE-2026-20112) and CRLF Injection (CVE-2026-20113)
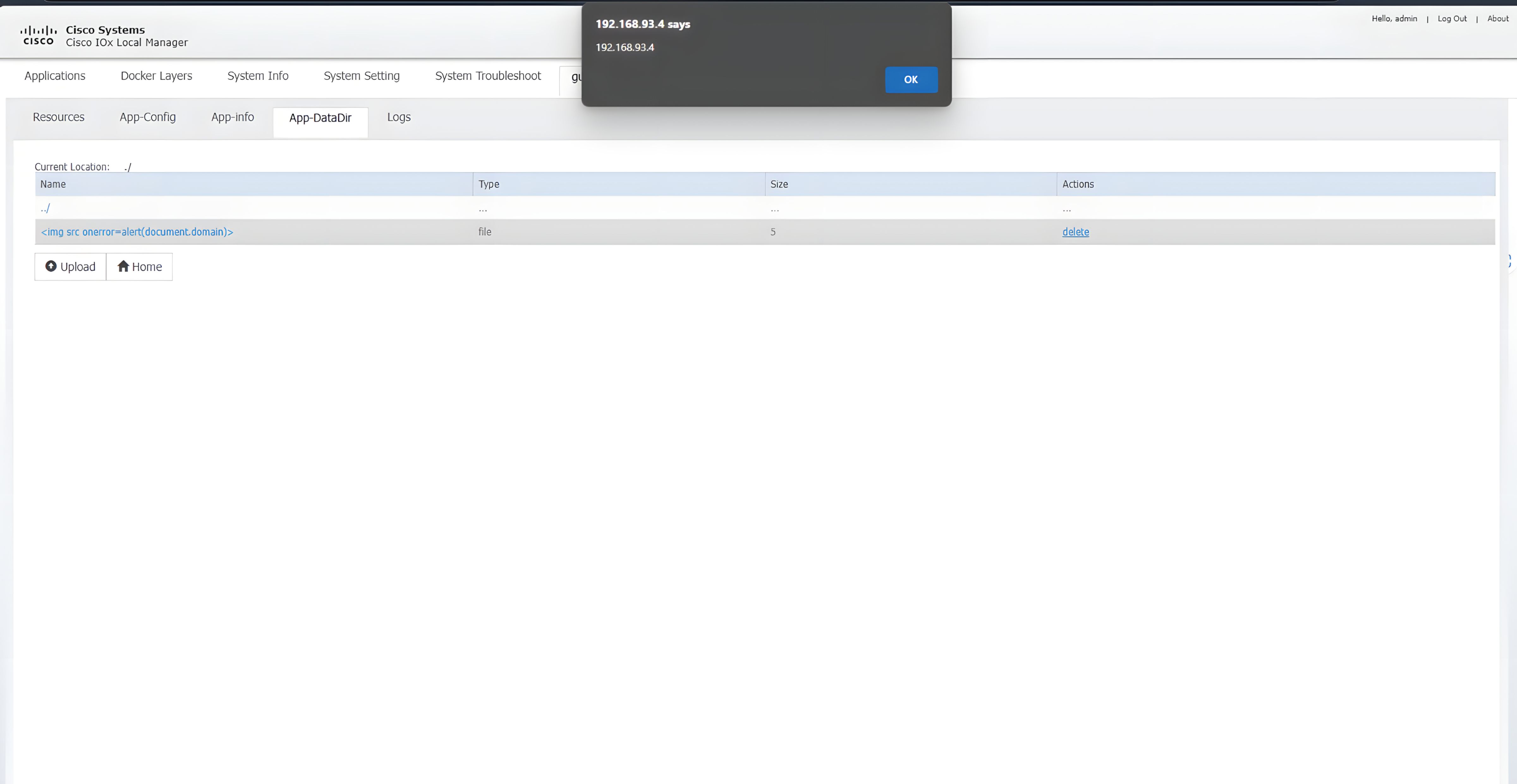
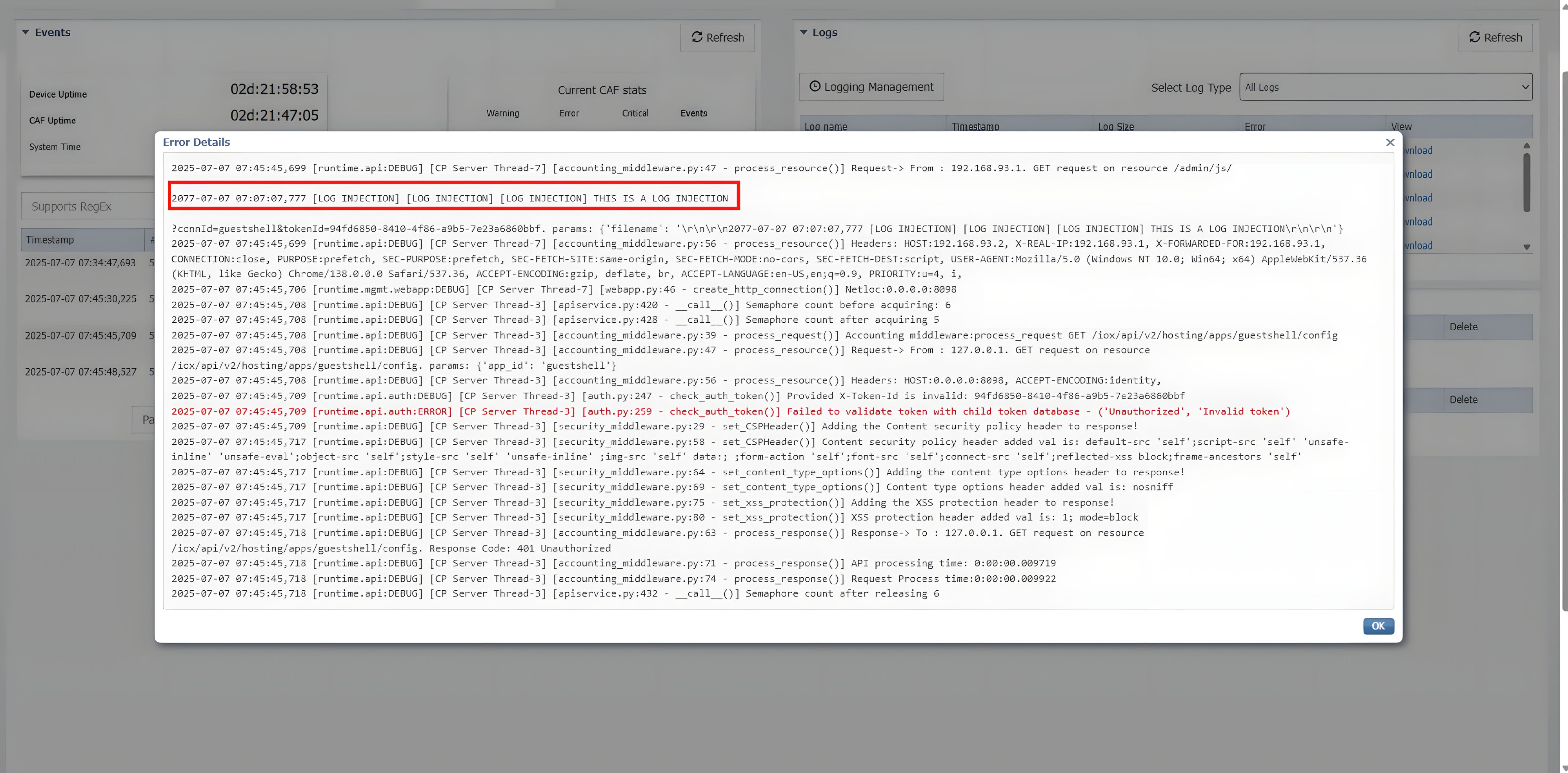
Moreover, during our analysis, Unit 515 identified two vulnerabilities within the Cisco IOS XE IOx application hosting environment: a stored Cross-Site Scripting (XSS) issue and a log injection vulnerability via CRLF manipulation. The stored XSS vulnerability stems from insufficient server-side input validation within application data handling workflows. While client-side validation mechanisms were present, they were not consistently enforced at the server level. As a result, an authenticated user could store malicious JavaScript payloads that would later execute in the context of another user’s session.
Separately, the CRLF injection vulnerability results from inadequate sanitization of user-supplied input before it is written to system logs. By injecting crafted control characters, an attacker can forge or manipulate log entries, potentially obscuring malicious activity and compromising the integrity of audit records. This weakens the reliability of logging mechanisms that are critical for monitoring, incident response, and forensic analysis.
Remediation
In late March 2026, Cisco published official security advisories addressing these vulnerabilities. Organizations operating affected Cisco Catalyst 9300 Series switches should upgrade immediately to the latest fixed releases as outlined in Cisco’s advisory. Applying these updates eliminates the underlying privilege enforcement and command handling weaknesses, preventing unauthorized escalation and abuse of operational functionality within the WebUI.
For environments where immediate patching is not feasible, interim mitigation measures should be implemented. These include restricting or disabling WebUI access from untrusted networks, enforcing strong authentication and role-based access controls for administrative interfaces, and closely monitoring for anomalous behavior such as unexpected account creation, abnormal privilege changes, or unauthorized operational commands.
Beyond patching, strengthening overall cyber resilience requires a layered defense strategy. Organizations can enhance protection of critical infrastructure environments by integrating the OPSWAT MetaDefender Platform, which provides deep content inspection, device validation, and data flow protection across network boundaries. Deploying MetaDefender alongside vendor security updates adds an additional defensive layer against exploitation attempts targeting management systems and operational technology environments.
Finally, this research underscores the importance of proactive security validation. OPSWAT Unit 515 offers advanced penetration testing services to help organizations identify privilege boundary weaknesses, insecure command handling logic, and other high-impact vulnerabilities before adversaries can exploit them. Through structured security assessments and real-world attack simulation, Unit 515 helps enterprises validate controls, strengthen resilience, and reduce exposure to complex exploit chains.
By combining timely vendor patching, strong administrative controls, layered defensive technologies, and proactive security testing, organizations can significantly reduce the risk of similar exploit paths and maintain a more resilient network security posture.
Learn more about Unit 515 and its services.

