Enterprises increasingly rely on cloud infrastructure to power their operations and store vital data. But with the immense opportunities the cloud offers come with equally significant challenges, especially when securing digital assets. Enterprise cloud security is now a top priority for IT leaders and C-suite executives, demanding a deep understanding and strategic implementation.
We'll explore enterprise cloud security, best practices gathered from CISA and NIST, the importance of a proactive security posture, and the inevitable challenges and rewards of embracing the cloud. With over 20 years of experience securing critical infrastructure and cloud computing, we offer advice to equip your organization with the knowledge and tools it needs to navigate the cloud safely and efficiently.
What is enterprise cloud security?
Enterprise cloud security is the policies, measures, controls, and technologies that large-scale businesses use to safeguard their cloud-hosted data, applications, and infrastructure. As the trend of migrating operations and sensitive data to the cloud grows, addressing the distinctive security challenges makes cloud security important.
Organizations need to be able to monitor, track, apply, and enforce their security and privacy policies on their cloud workloads, based on business requirements, in a consistent, repeatable, and automated way.
NIST SPECIAL PUBLICATION 1800-19B
Here are the key aspects:

Understanding the Threat Landscape
Central to this concept is protecting enterprise-scale cloud setups from a myriad of internal and external threats. Security teams must defend against unauthorized data access and various cyber threats, such as file upload attacks.

Scale and Complexity
Unlike the cloud security provisions tailored for individuals or small businesses, enterprises deal with vastness and complexity. Large organization may employ containers and microservices. While microservices enhance functionality by supporting a single application with many independent services, they also bring operational challenges involving controlling access for large numbers of employees, securing extensive datasets, and complying with diverse regulatory jurisdictions.

Navigating the Shared Responsibility Model
Cloud service providers, including AWS, Google Cloud, and Microsoft Azure, advocate the shared responsibility model. While the providers ensure the security of the cloud's foundation, clients must ensure the security of what they host within that cloud. Enterprises must discern the division of these responsibilities.

Embracing Multi-Cloud and Hybrid Cloud Strategies
Presently, many enterprises diversify their cloud strategies, using a combination of private, public, and hybrid cloud setups. The challenge lies not only in securing each environment but also in supporting uniform enterprise security standards.

Commitment to Continuous Monitoring and Evolution
Securing the cloud isn't a "set it and forget it" task. With the ever-changing landscape of cloud technologies and emerging cyber threats, there's a perpetual need for monitoring and refining the enterprise cloud security approach.
Recognizing the Imperative of Compliance
Adhering to stringent regulatory standards, such as Europe's GDPR or the U.S.'s HIPAA, is non-negotiable for many enterprises. Therefore, they must equip their cloud security strategies with tools and methods to ensure consistent compliance.
The Shared Responsibility Model: Security and Compliance
Security and Compliance in cloud computing is a collaborative effort between the cloud service provider (CSP) and the customer to secure the cloud environment. While the cloud provider ensures the infrastructure's security management, the customer handles safeguarding their data, applications, and configurations within that infrastructure.
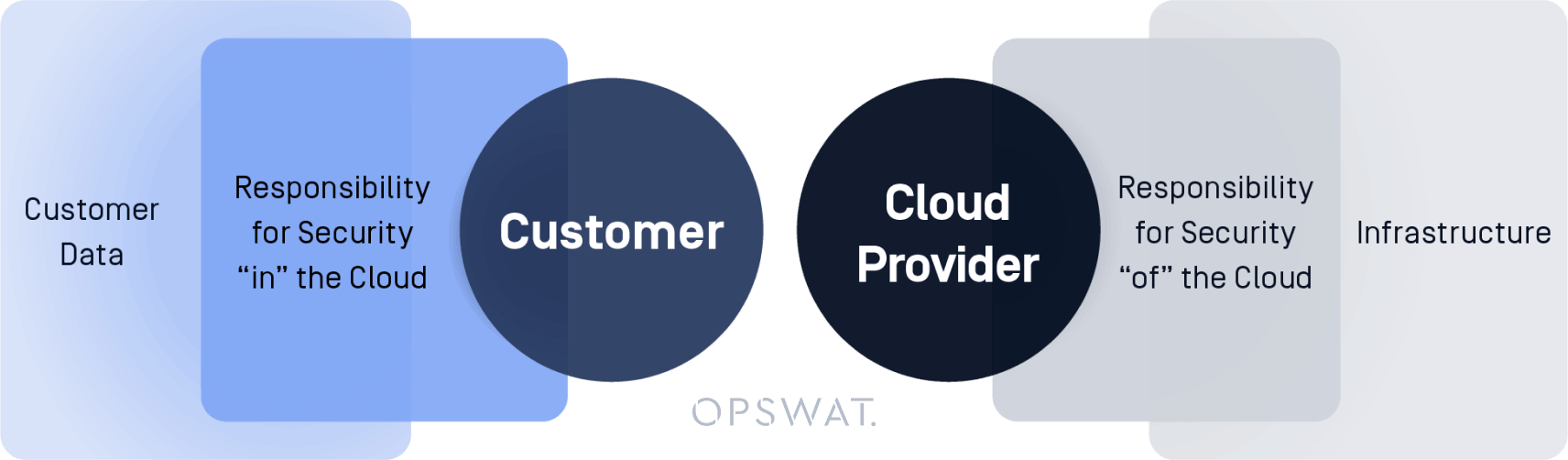
This joint model alleviates the customer's operational responsibilities, as the cloud provider manages everything from the host operating system and virtualization layers to the physical security of the facilities.
Conversely, customers oversee the guest operating system, its updates, security patches, certain application software, and the configuration of the provided security firewall. The onus on customers will vary based on the services they opt for, their integration into their IT setup, and the relevant legal and regulatory standards. This model offers flexibility, allowing the user to have control over deployment.
This split in responsibility describes the distinction between the Security "of" the Cloud (provider's responsibility) and Security "in" the Cloud (customer's responsibility).
How do public cloud providers fit in?
Major public cloud providers, such as Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP), have strongly advocated this model. Here's a simplistic breakdown:
Cloud Provider's Responsibility: "Security of the Cloud"
- Ensure physical security of data centers.
- Maintain infrastructure and cloud resources against threats.
- Provide built-in security features and tools for customers.
Why is the shared responsibility model crucial?
The shared responsibility model offers flexibility, allowing organizations to tailor their security measures based on their specific needs while building on the foundational security provided by the cloud service provider.
Additionally, there's an element of cost efficiency; by dividing tasks, businesses can optimize their security investments, zeroing in exclusively on their areas of concern. Businesses achieve an enhanced security posture when they recognize their delineated responsibilities, empowering them to secure their cloud storage environments comprehensively, from the infrastructure right up to the data.
Key Takeaways for Businesses
To bolster your cloud security, it's crucial to stay informed. This means regularly reviewing your CSP's shared responsibility guidelines, which often come with detailed documentation and best practices.
Furthermore, investing in training is indispensable, ensuring your IT and security teams are well-versed in their roles concerning the protection of your cloud assets. It's also beneficial to use cloud-native tools; the majority of public cloud providers present native tools designed to aid in your security endeavors, so make sure to familiarize yourself with these resources. Lastly, conduct regular audits of your cloud environment to guarantee compliance with the shared responsibility model.
Top 5 Enterprise Cloud Security Challenges

Enterprise cloud security brings about distinct challenges. These are the top five:

1. Visibility and Control
Transitioning to cloud services often surpasses the capacity of traditional monitoring tools. Shadow IT, meaning cloud services used without IT's knowledge, complicates visibility. This can result in unsanctioned applications, unmonitored data movements, and possible compliance breaches.

2. Data Security and Privacy
Cloud storage of sensitive data prompts fears of breaches or exposure. The challenge lies in encrypting data in transit and at rest across various services. Storing data in foreign data centers also presents residency and sovereignty issues.

3. Identity and Access Management
In the cloud, managing user identities and permissions intensifies. Companies need to ensure consistent user access policies across different cloud services, safeguard credentials with mechanisms like MFA, and prevent unauthorized access.
4. Compliance and Governance
Ensuring compliance with different regulations becomes intricate when data resides across various cloud platforms. While providers might be compliant, enterprises must also ensure their cloud usage aligns with regulations like GDPR or HIPAA.

5. Threat Protection and Response
Cloud settings face unique threats, such as malware and misconfigured storage. Addressing these necessitates specialized tools and knowledge, especially with the advent of Infrastructure as Code, which demands vulnerability-free infrastructure definitions. OPSWAT MetaDefender Storage Security detects threats and secures data storage.
Overcoming these challenges entails utilizing appropriate security tools, revising security policies, continuous training, and nurturing a security-focused organizational culture.
Key Features of a Robust Enterprise Cloud Security Solution
Enterprise cloud security is vital for safe business operations within the cloud. Essential features include:
| Identity and Access Management (IAM) | Allows only authorized access to cloud resources and cloud assets, with features like multi-factor authentication and single sign-on. |
| Data Encryption | Secures sensitive data at rest and during transfer, with advanced options like client-side encryption and key management. |
| Intrusion Detection and Prevention Systems (IDPS) | Real-time threat monitoring and blocking by analyzing suspicious traffic patterns, enhancing your security posture. |
| Endpoint and Cloud Network Security | Safeguards devices connecting to cloud environments and uses tools such as firewalls and VPNs to defend the cloud infrastructure. |
| Security Information and Event Management (SIEM) | Centralizes real-time, potential security threats and alert analysis for a stronger security posture management. |
| Compliance Management | Ensures adherence to regulations like GDPR and HIPAA, with auditing tools. |
| Micro segmentation | Segments cloud networks for enhanced security, preventing broad intrusions. |
| Backup and Disaster Recovery | Regular data backups with swift restoration capabilities. |
| Zero Trust Architecture | Assumes no user/device is inherently trustworthy, demanding continuous verification. |
| Application and Container Security | Ensures safety of cloud applications and their container deployments. |
| Visibility, Reporting, and DDoS Protection | Provides a clear security overview, reports potential threats, and mitigates DDoS attack effects. |
| Secure API Gateways and DevOps Integration | Safeguards APIs and integrates devops for continuous protection. |
The right combination of these features varies by enterprise needs, size, and industry. A layered security approach offers robust defense against multiple threats.
Must-Have Enterprise Security Technologies
Enterprise cloud security management begins with detecting and preventing threats moving between clouds and corporate networks. Scanning files uploaded to your cloud data storage with multiple-antivirus engines prevents malware and data breaches. The ability to scan files moving between hybrid cloud environments, on-premises data storage, and cloud environments is also key.

Identifying solutions that can be easily implemented into existing architectures and complex networks is also important. ICAP servers are a plug-and-play solution to protect your cloud-hosted applications and network against malicious content. An ICAP implementation makes it simple to connect private corporate cloud networks to data loss prevention (DLP), content disarm and reconstruction (CDR), and antivirus scanning technologies.
Monitor and report on the encryption status of endpoint devices, with cloud access control technologies. Security teams can streamline the user access and sign-in process with endpoint security products. Periodic reviews and reports on an endpoint's security profile and allowing external applications to access the security data through OAuth API, browser cookies, and client certificates ensures a thorough security check before granting access to vital cloud or local network resources.
Understanding Enterprise Cloud Security Architecture
Enterprise cloud security architecture focuses on designing secure patterns for cloud workloads. It bridges business needs with technology by designing controls for Infrastructure-as-a-Service (IaaS), Platform-as-a-Service (PaaS), and Software-as-a-Service (SaaS) models. The overarching aim? To find and mitigate security flaws, especially in interconnected systems before deployment and during cloud management.
As businesses undertake their cloud migration journey, there's an increasing need to understand the nuances of enterprise cloud solutions. Given the spate of data breaches and cloud security failures in recent times, adopting a robust cloud security architecture has never been more critical. But how can organizations ensure they're on the right path?
Cloud Deployment
Cloud deployment isn't just about leveraging cloud computing services. It's about guiding organizations on how to smoothly transition to, integrate, maintain, and operate these services. When executed correctly, cloud deployment becomes the bedrock of data security in private cloud environments and beyond. Furthermore, with an apt enterprise cloud strategy, businesses can safeguard their cloud assets, ensuring that sensitive data remains uncompromised.
Adaptable Solutions
Cloud solutions aren't about choosing a one-size-fits-all approach. Instead, they emphasize a flexible and broadly applicable architecture. This enables businesses to identify cloud capabilities and opt for vendor-agnostic solutions, ensuring that their cloud technology remains relevant, irrespective of the shifting tech landscape.
Conclusion
Implementing a cloud security solution is vital for business continuity, trust, and profitability. As businesses expand in the cloud, protecting their assets is crucial. Understanding challenges and using the right tools and strategies strengthens defenses against cyber threats. With a proactive security approach, businesses can embrace the cloud's benefits while reducing risks.
Enterprise Cloud Security FAQs
What is Enterprise Cloud Security?
Enterprise cloud security is the policies, measures, controls, and technologies that large-scale businesses use to safeguard their cloud-hosted data, applications, and infrastructure.
How is enterprise-level cloud security different from small business or individual cloud security?
What does the Shared Responsibility Model mean in cloud security?
What are cloud access security brokers?
What are the differences between public and private clouds?
Public cloud and private cloud differ mainly in ownership, cost, security, customization, and scalability. Third-party services like AWS, GCP, and Azure provide the public cloud, which multiple users share. It is cost-effective for varying workloads and offers vast scalability but limited customization. Private clouds are exclusive to one organization. They can be on or off-premises. Private clouds provide enhanced security, more customization, and control but might demand higher upfront costs. Many enterprises blend a hybrid approach to get the best of each cloud solution.