Introduction
This blog presents a technical analysis of CVE-2025-59718 and CVE-2025-59719, two critical authentication bypass vulnerabilities affecting multiple Fortinet products when FortiCloud Single Sign-On (SSO) is enabled.
Both vulnerabilities stem from improper verification of cryptographic signatures (CWE-347) during SAML response processing. Under specific conditions, a crafted SAML response may be accepted as valid, allowing an unauthenticated attacker to bypass FortiCloud SSO authentication.
At the time this research was conducted, public technical information was limited, and no independently verifiable proof-of-concept demonstrating real exploitation was available. OPSWAT Unit 515 performed an in-depth analysis to determine whether these vulnerabilities were practically exploitable and to assess their real-world impact.
Vulnerability Scope and Technical Impact
CVE-2025-59718 and CVE-2025-59719 affect multiple Fortinet products, including FortiOS, FortiWeb, FortiProxy, and FortiSwitchManager, when FortiCloud Single Sign-On (SSO) is used for administrative authentication.
The root cause of both vulnerabilities is an improper verification of cryptographic signatures (CWE-347) during SAML response processing. As a result, malformed or manipulated SAML responses may be processed as legitimate authentication data under specific conditions.
When FortiCloud SSO is enabled, this weakness can lead to a complete authentication bypass. A successful exploit allows an unauthenticated attacker to gain access to protected administrative interfaces without possessing valid credentials. Depending on deployment configuration and access exposure, this may ultimately result in full compromise of the affected device.
According to the advisory published by FortiGuard Labs, these vulnerabilities were identified internally. The detailed exploitation mechanics and practical attack workflows were not publicly disclosed at the time of release.
Evaluation of Public Exploitation Claims
Following disclosure, multiple public repositories and technical blog posts claimed to provide proof-of-concept exploits for CVE-2025-59718 and CVE-2025-59719. To accurately assess the real-world exploitability of these vulnerabilities, Unit 515 conducted a systematic review and hands-on validation of the publicly available materials in a controlled environment.
The reviewed materials included multiple GitHub repositories that purported to demonstrate authentication bypass via crafted SAML responses on Fortinet devices. However, during technical validation, Unit 515 determined that these implementations were non-functional.
Specifically, our analysis showed that the published PoCs:
- Do not successfully bypass FortiCloud SSO authentication
- Rely on assumptions that do not reflect actual SAML processing behavior in affected products
- Fail to produce a valid authenticated session or administrative access
As a result, none of the publicly available PoCs were capable of exploiting CVE-2025-59718 or CVE-2025-59719 in practice.
Independent Technical Validation by Unit 515
Given the critical severity assigned to CVE-2025-59718 and CVE-2025-59719, and the absence of any verified public exploitation, OPSWAT Unit 515 conducted an independent technical investigation to determine whether these vulnerabilities were practically exploitable under real-world conditions.
Testing was performed in a controlled laboratory environment using affected Fortinet devices configured with FortiCloud SSO for administrative authentication. The research focused on analyzing SAML response handling logic, signature verification behavior, and trust assumptions made during the authentication flow.
Through this investigation, Unit 515 was able to reliably reproduce the vulnerable behavior and confirm that insufficient cryptographic verification during SAML processing can, under specific conditions, be leveraged to bypass authentication controls. The resulting behavior demonstrates that the vulnerabilities are not theoretical and can be exploited in a repeatable manner when prerequisite conditions are met.
This validation confirms that CVE-2025-59718 and CVE-2025-59719 represent real authentication bypass vulnerabilities with meaningful security impact, rather than edge-case implementation flaws.
Responsible Research Statement
All testing was conducted exclusively in our isolated, non-production environments for defensive research purposes. No customer systems or external environments were affected.
Recommendation
Fortinet Mitigation
In December 2025, Fortinet released FortiGuard advisory FG-IR-25-647, addressing two FortiCloud Single Sign-On (SSO) authentication bypass vulnerabilities, CVE-2025-59718 and CVE-2025-59719. As part of the initial response, Fortinet provided updated firmware versions across affected product families and advised customers to upgrade impacted devices and review administrative access configurations involving FortiCloud SSO.
In late January 2026, Fortinet received reports from a limited number of customers describing unexpected administrative login activity that closely resembled the previously addressed issue. Importantly, several affected systems were already running the latest available firmware at the time, indicating that the observed behavior was caused by a distinct attack path rather than an incomplete patch of the original vulnerabilities.
Following further investigation, Fortinet identified an authentication bypass using an alternate path or channel (CWE-288) affecting multiple products when FortiCloud SSO authentication was enabled. This issue was assigned CVE-2026-24858 and documented under FortiGuard advisory FG-IR-26-060.
To mitigate this newly identified risk, Fortinet released additional firmware updates and implemented stricter enforcement at the FortiCloud service level. Effective from 27 January 2026, FortiCloud SSO authentication is permitted only for devices running supported, up-to-date firmware versions and maintaining an active FortiCloud subscription. Devices that do not meet these requirements are prevented from authenticating via FortiCloud SSO, effectively blocking exploitation through the affected authentication paths.
These combined measures address both the originally disclosed FortiCloud SSO bypass conditions and the later identified alternate authentication path, significantly reducing the risk of unauthorized administrative access via FortiCloud SSO.
Firewall Bypass and OPSWAT Data Diode Solution
This class of attack highlights a critical architectural risk: when a firewall is compromised or subverted, it can no longer be relied upon as a security boundary. Once this occurs, attackers may gain persistent access to trusted network segments, and every system protected solely by the firewall becomes exposed.
Firewalls remain an essential component of network security, but they are software-driven controls operating on trust assumptions. When those assumptions fail - whether through authentication abuse, logic flaws, or compromised management channels - the firewall can unintentionally facilitate attacker movement rather than prevent it. At this stage, traditional hardening and policy tuning offer limited value because the perimeter itself has been breached.
Importance of Multi-Layer Defense Beyond the Firewall
Resilient security architectures are built on the assumption of breach. Firewalls, identity services, and other software-based controls are all subject to vulnerabilities and trust failures. Once a firewall is compromised, any system relying on it as the sole enforcement point becomes critically exposed, regardless of internal hardening.
To mitigate this risk, organizations must adopt a multi-layer defense strategy that includes at least one control capable of containing a breach even after the firewall trust boundary collapses. This requires moving beyond policy-based enforcement to physical isolation.
Data Diodes as a Deterministic Security Control
A data diode enforces physically unidirectional data flow, ensuring that information can move in only one direction with no possibility of return traffic. Unlike firewalls, which depend on software policy, session handling, and trust assumptions, a data diode enforces isolation at the hardware level. The inbound path does not exist, which makes remote access, command injection, and reverse communication structurally impossible.
This approach fundamentally changes the security model. Rather than attempting to detect or block malicious activity, the data diode removes the attack path entirely. Even if upstream controls are compromised, there is no mechanism for an attacker to interact with protected systems.
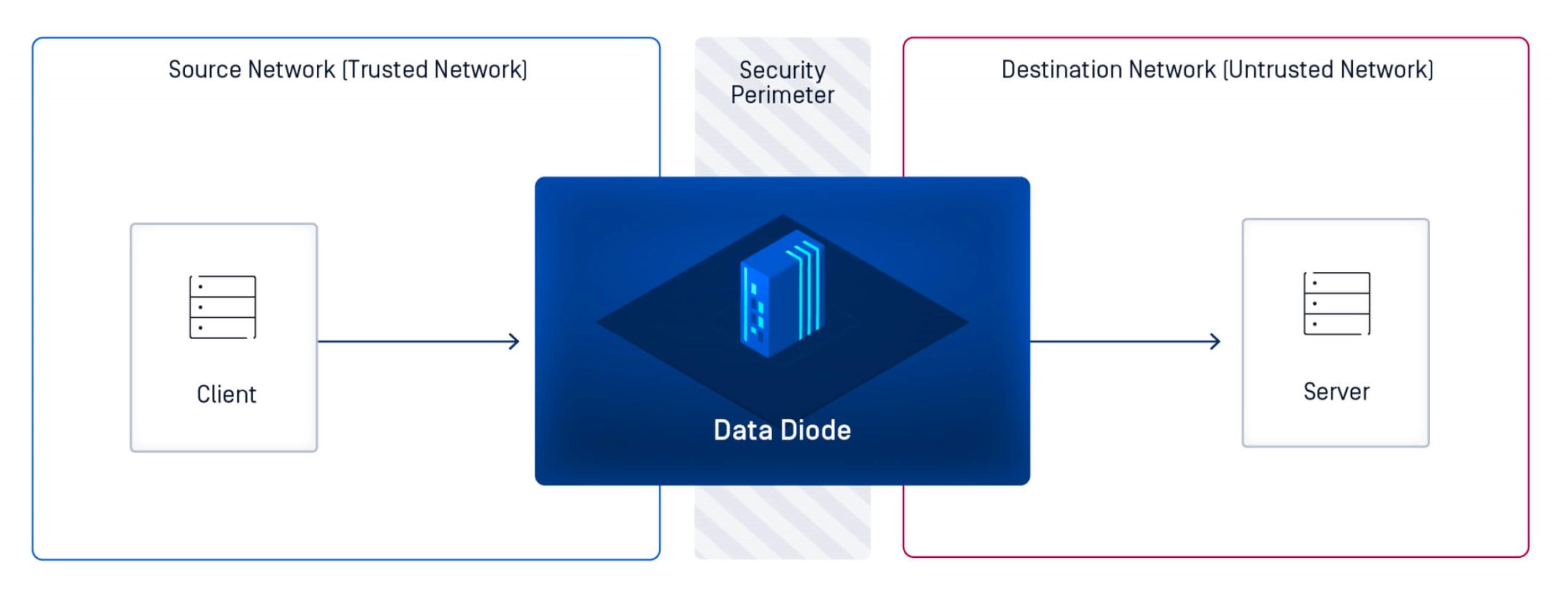
MetaDefender Optical Diode: A Comprehensive Data Diode Solution
When firewall protections are no longer sufficient to guarantee segmentation, organizations require a control that can preserve security boundaries independent of policy enforcement or bidirectional trust. The OPSWAT MetaDefender Optical Diode is engineered to meet this need, delivering the highest standards of network isolation, data integrity, and regulatory compliance for environments where failure is not an option.
Designed to defend against modern cyber threats targeting critical infrastructure and operational technology (OT) environments, MetaDefender Optical Diode provides a trusted mechanism to maintain secure communications without exposing protected networks. Rather than replacing firewalls, it complements them by enforcing physical unidirectional data flow, ensuring that critical systems remain isolated even if traditional perimeter controls are compromised.
With OPSWAT’s recent acquisition of FEND, the MetaDefender Optical Diode portfolio now supports every deployment scale and use case - from compact solutions for remote or edge facilities to high-capacity platforms for large-scale industrial environments. Whether securing a refinery, power plant, transportation hub, manufacturing site, or defense system, organizations can deploy a MetaDefender Optical Diode purpose-built for their operational requirements.
By combining physical unidirectional isolation with advanced threat prevention, MetaDefender Optical Diode enables critical networks to communicate safely - without ever being exposed to inbound risk. It provides organizations with confidence that even in high-stakes environments, essential data exchange can occur without undermining security.
MetaDefender Optical Diode is more than a cybersecurity device - it is peace of mind for environments where trust boundaries must hold, even when other controls cannot.


