Product Overview
OPSWAT MetaDefender Core protects organizations’ web applications, endpoints, and other data sources from advanced cybersecurity threats.
MetaDefender Core leverages proprietary technologies—including Deep Content Disarm and Reconstruction (Deep CDR™ Technology), Multiscanning, File-Based Vulnerability Assessment, Data Loss Prevention, and Threat Intelligence—to provide comprehensive protection for your networks and infrastructure against increasingly sophisticated malware.
Release Highlights
Central Hub Version 1.1.0
- For archive processing, extracted child files are shared among MetaDefender Core instances for optimized productivity and boosted performance.
- MetaDefender Core instances now share authentication sessions using Redis caching server.
- MetaDefender Core Central Hub now supports batch processing.
Docker Containerization Enhancements
- Supports MetaDefender Core upgrade with zero down time on containerization environment Kubernetes (blue/green and rolling strategies)
- Supports MetaDefender Core upgrade with data retention
- Log rotate service built in Docker base image
- Supports proxy configuration for Docker run
- Supports new option to enable "allowCrossIPSessions" when starting MetaDefender Core on container environment
Windows 11 Support
For Microsoft Windows deployments, MetaDefender Core supports the following operating systems:
- Windows 10, 11
- Windows Server 2012, 2012 R2, 2016, 2019, 2022
New Configuration: Reject File Submissions Based on Engine Availability
Allow MetaDefender Core to only accept file processing submissions when certain specific engines are available.
To find this setting go to Workflow Rule -> General tab.

New Configuration: Add an Exception to Process Unsupported File Types for Sanitization
When “Block unsupported file types” is enabled, configure an exception list to allow specific unsupported file types. By doing so, those file types configured in the exception list will not be blocked.
To find this setting go to Workflow Rule -> Deep CDR™ Technology tab.

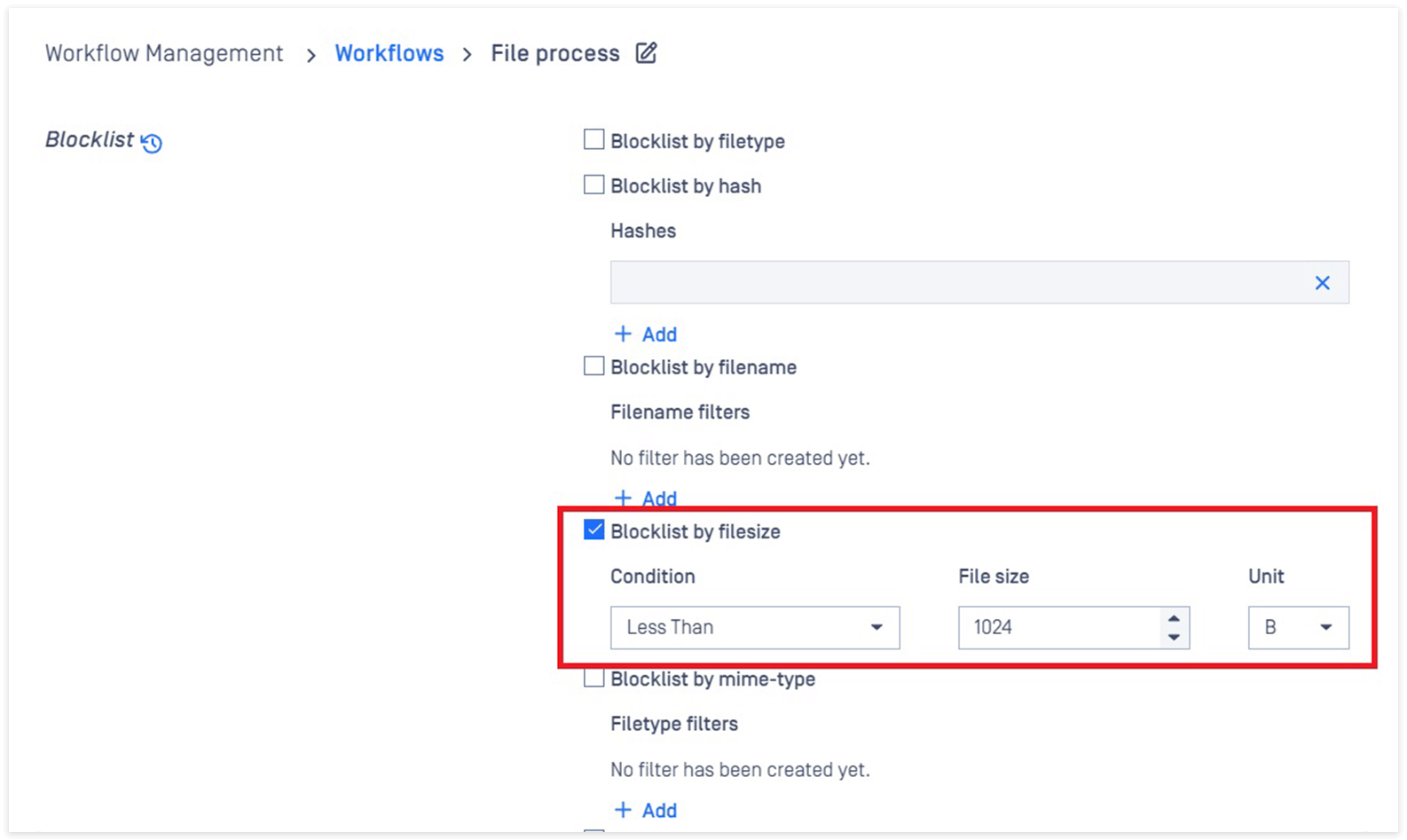
New Configuration: Set File Size Conditional Limits for Blocklisting File Processing
Configure MetaDefender Core to block file processing for file sizes greater than or less than a specified file size.
To find this setting go to: Workflow Rule -> Blocklist and Allowlist tab.
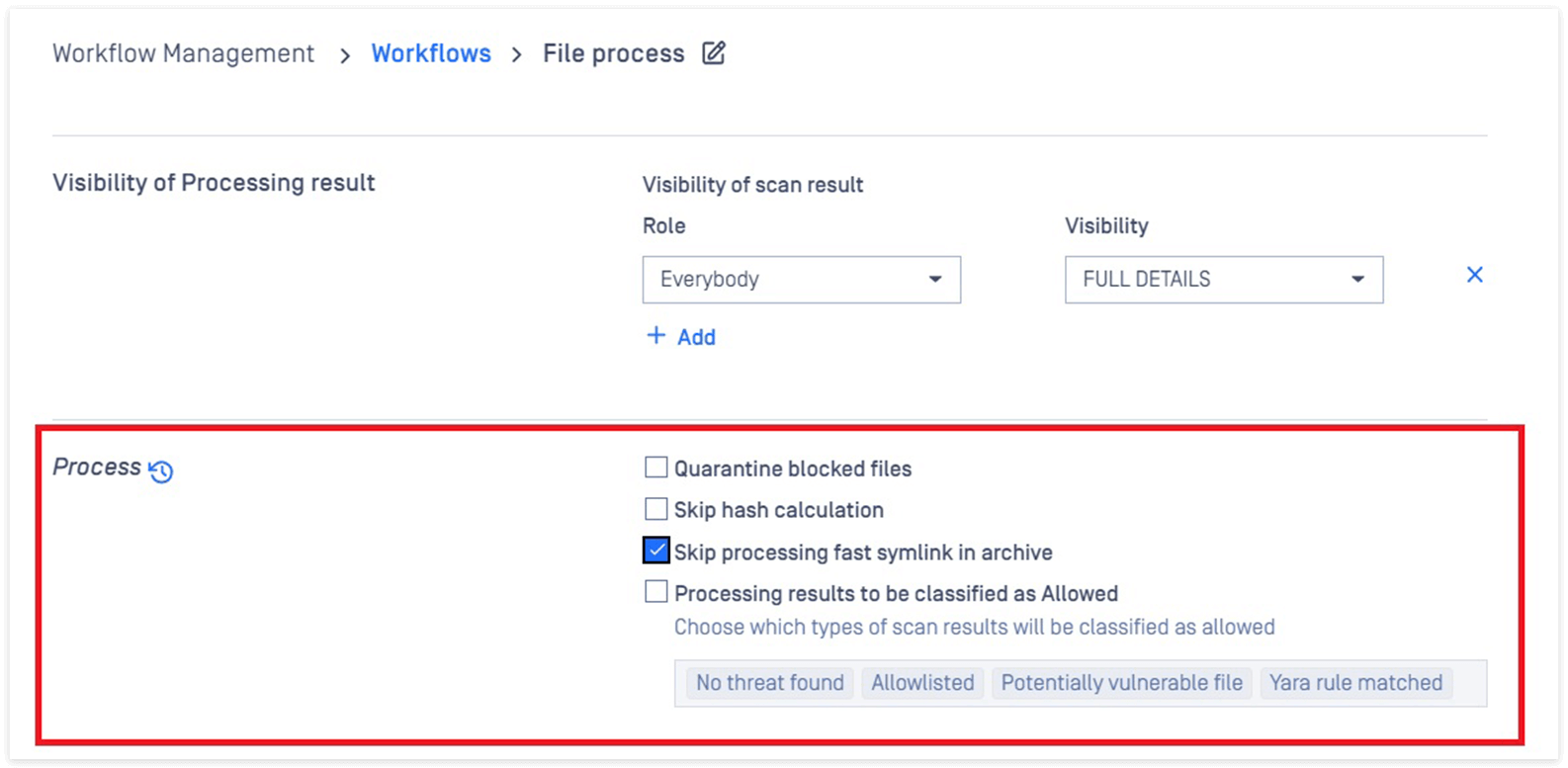
New Configuration: Skip Processing Fast Symlink in Archive Files
By default, MetaDefender Core will try to process any files, including fast symlink in archives. Administrators now can skip fast symlink process by selecting this option in the workflow rule.
To find this setting go to: Workflow Rule -> General tab.
UI Enhancements
- Enhance and remediate UI accessibility support and compliance
- Display backup license status
- Add sanitized label as an indicator in the processing history
- Support “search by name" for workflows
- Add result for vulnerability assessment when "skip hash calculation" setting is enabled
- Add descriptive tooltip for "Fallback file type detection to current extension if needed" setting
- Change setting name "Blocklist unsupported file types" to "Block unsupported file types"
Enhancement: Import Full Configuration Package (.zip) with the Ignition File
Better automation support by importing full configuration package (.zip) via the ignition file.
Example:
eula=true [config] import=settings.zip import_password=123 ....
Details: Ignition file.
Enhancement: Webhook Callback Retry Mechanism
Enhanced webhook retry mechanism for resending callback result in case of timeout or not receiving a webhook server’s response.
Define timeout threshold via new transfertimeout key (by default, 30000 ms) with PUT - Webhook set configuration
New CLI Tool: Clean Up Database Created by No-Longer-Used MetaDefender Core Instance in Shared DB Mode
Clean all scan data from MetaDefender Core instance(s) that you no longer use, applicable in the shared DB mode.
Tool located at:
- Windows: C:\Program Files\OPSWAT\MetaDefender Core\ometascan-db-cleaner.exe
- Linux: /usr/sbin/ometascan-db-cleaner
Details: Database Cleanup Tool in Shared DB Mode
New CLI Tool: Check Remote PostgreSQL User Compliance
Database system admins can quickly determine if a remote PostgreSQL database has sufficient user privileges as described in PostgreSQL User Privilege Requirements to work properly with MetaDefender Core application.
Details: Remote PostgreSQL User Privileges Checking Tool
Other Enhancements and Updates:
Security enhancements
- Upgrade third-party libraries (gperftool, libxml2) for vulnerability risk
- Add support for digest verification in FIPS enabled environment while installing MetaDefender Core
Logging enhancements
- Prevent misleading (and unharmful) error messages in PostgreSQL logs
- Add batch ID and data ID information in NGINX access logs
- Remove misleading warning messages in MetaDefender Core logs while updating engines via folder
Performance enhancements
- Improve hash lookup performance
For more information, please visit opswat.com/products/metadefender/core or contact our critical infrastructure cybersecurity experts for assistance.
Release Details
Product: MetaDefender Core
Release Date: 4 January 2022
Release Notes: 5.4.0
Download Link on OPSWAT Portal: Download

