Electric utilities operate highly distributed, safety-critical control environments, and systems such as SCADA, EMS, protection relays, and substations must run continuously without disruption. Many of those cyber assets only communicate with legacy protocols, and most of the equipment was designed long before the emergence of modern cyberthreats, making the necessary upgrades needed to keep up feel impossible.
Despite the limitations, utilities in the modern world are expected to offer centralized monitoring, provide real-time operational visibility, and inevitably, share data with corporate IT, SOCs, and regulators. This creates a persistent tension between operational isolation and organizational visibility.
In the utility sector, a cyber incident is not limited to just data loss or downtime. The more severe risks include loss of grid reliability, causing further cascading outages and resulting in safety hazards to workers and the public. On top of everything, regulatory violations under NERC CIP can result in hefty penalties in financial and legal liabilities.
Many modern organizations choose firewalls and VPNs to provide foundational controls, but relying on these security solutions exposes the utilities to a critical vulnerability: They are bidirectional by design. Firewalls must allow return traffic by common communication use cases and can often be misconfigured or exploited. Even tightly configured firewalls depend on software correctness by skilled admins and require ongoing rule maintenance to ensure policies remain in effect while precise changes are permitted.
From a high-impact BES perspective, as required to address within the CIP standards, this means inbound risk never fully goes away — it's only being managed at best — assuming you have a strong team of experts and operators. The presence of any inbound electronic pathway becomes the core risk that compliance teams must defend complex configurations during audits such as providing evidence to meet the requirements in CIP-005-8 Table R1 for securing the electronic security perimeter (ESP) and CIP-007-7 Table R1 for system hardening. If a monitoring, IT, or vendor network is compromised, attackers will exploit allowed return paths to pivot back into OT environments and inject commands, malware, or malformed traffic to create irreversible damage.
This is why NERC CIP emphasizes minimizing and strictly controlling inbound access - not just detecting misuse. A data diode enforces one-way data transfer at the hardware level. Information can move out of a protected OT environment, but cannot return, regardless of software state, configuration, or compromise. This approach transforms the security model from “inbound traffic is blocked by rules” to “inbound traffic is physically impossible”.
With a data diode in place, utilities can continue to fulfill the essential business reporting needs such like export SCADA or EMS telemetry, replicate historians, and send logs and alerts to SOC platforms, all without introducing an inbound attack path into the BES Cyber System environment.
As shown in the diagram below, visibility is preserved while exposure is kept out.
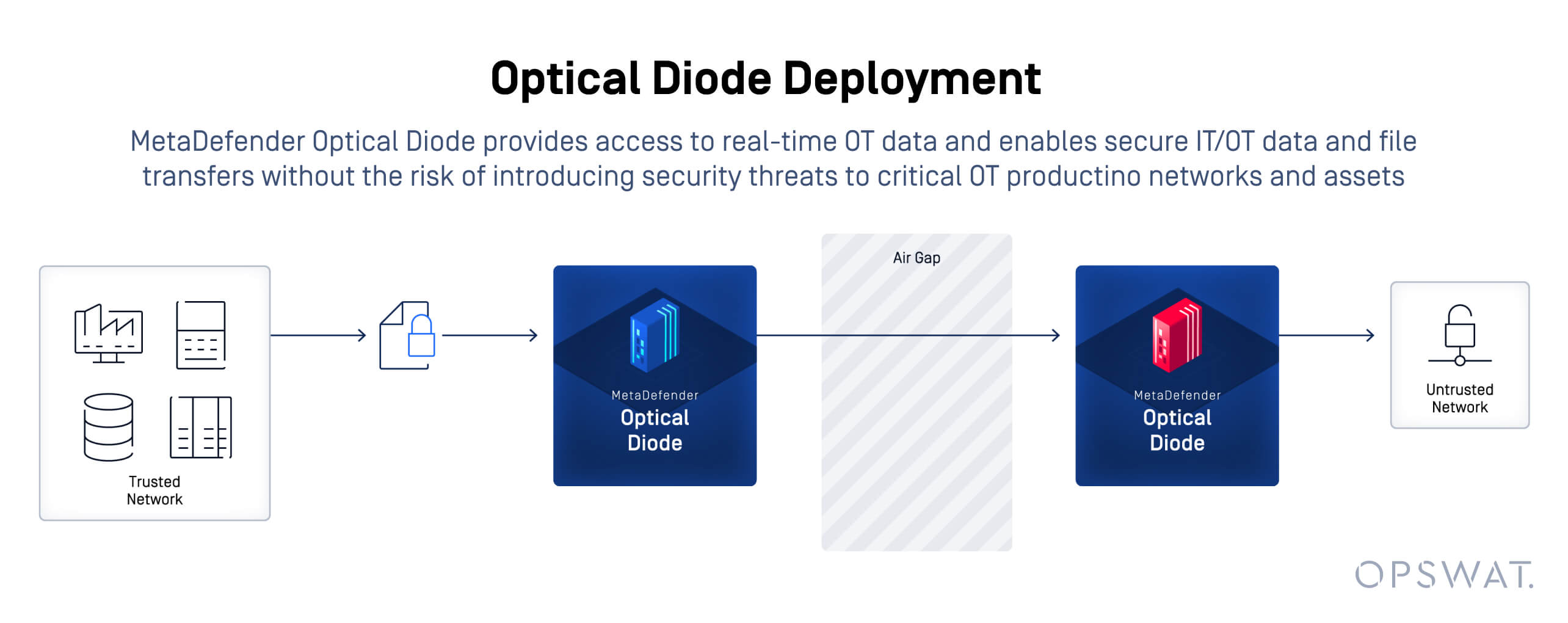
Architecturally, the change is simple but decisive: software trust boundaries are replaced with physical enforcement. Auditors don’t have to “trust the rules,” they can trust the architecture and the law of physics.
The actual fast pass is that within Standards CIP-002 through CIP-013: Using a unidirectional gateway/data diode can exempt a utility from several compliance requirements (such as 21 out of 26 rules in some NRC contexts). Using data diode helps avoid requirements of documentation to satisfy CIP-010-5 Table R1 for Configuration Change Management and Monitoring as there are no firewall configuration changes needed. Diode also fits the requirements in CIP-011-4 Table R1 for Information Protection, as only designated information can be transferred in full auditable trail while other information cannot be passed through the one-way communication by policy.
This fast pass enables compliance and audit readiness to better document explainable control aligned with NERC CIP intent, effectively reduce scope for inbound access justification and provide strong evidence of due diligence in high-impact environments. As the top goal of the utility, operational continuity ensures that no impact on control system availability, no changes to legacy OT protocols, and predictable, stable data flows are achieved.
For utilities evaluating one-way security architectures, solutions like MetaDefender Optical Diode are designed specifically for regulatory-driven, high-assurance environments where inbound risk is unacceptable. Whether driven by NERC CIP compliance, operational risk reduction, or long-term resilience, hardware-enforced unidirectional data flow remains one of the most defensible security decisions a utility can make.
Learn more about how MetaDefender Optical Diode can help you achieve NERC CIP compliance.