In October 2025, the ASD (Australian Signals Directorate) released CI Fortify, a set of recommendations designed to strengthen the cyber resilience of critical infrastructure environments.
The guidance arrives at a time when operators of critical services are facing a difficult reality; connectivity can no longer be assumed to be trustworthy during major cyber incidents.
ASD’s guidance makes the strategic context clear (cyber.gov.au): "Australian CI is, and will continue to be, an attractive target for state-sponsored cyber actors. Australia has joined multi-country advisories warning of the threat of state-sponsored actors targeting CI as highlighted in the recent Salt Typhoon advisory.”
The ASIO (Australian Security Intelligence Organisation) Annual Threat Assessment 2025 has assessed espionage and foreign interference are already at extreme levels and are anticipated to intensify[1]."
Against this backdrop, CI Fortify outlines two critical resilience capabilities for infrastructure operators:
- The ability to isolate vital OT and supporting systems from surrounding networks for up to three months while maintaining essential services.
- The ability to rapidly rebuild those systems from trusted sources when the integrity of the environment is uncertain.
For operational technology environments, this is more than cybersecurity guidance—it is a fundamental resilience design principle.
Designed for Isolation: A Mindset That Predates Modern OT Security
Long before industrial cybersecurity became a widely discussed discipline, many operational environments already operated under constraints that forced resilience by design.
In early telecommunications networks of the 1990s and early 2000s, systems were built with the expectation that connectivity could fail. Architects assumed limited external dependency, and recovery processes relied on known-good offline backups and controlled system rebuilds.
This mindset aligns closely with what CI Fortify is now advocating for critical infrastructure environments.
The key operational questions are straightforward:
- If connectivity between OT systems and external networks had to be severed immediately, could the critical service still operate safely at a minimum operating state?
- If trust in the environment was compromised, could vital systems be rebuilt quickly and confidently without improvisation?
These are engineering questions—but they have strategic implications for the entire organisation.
Why OT Isolation Readiness Matters Beyond Security Teams
Although CI Fortify originates from a cybersecurity authority, its implications extend far beyond security operations.
Isolation affects:
- Operational continuity
- Vendor access and remote maintenance models
- Cross-domain automation and integrations
- Incident response processes
- Governance and regulatory reporting
In many industrial environments, isolating OT networks can disrupt business processes that have gradually evolved around connectivity and automation. As a result, resilience planning must include clear operational ownership, documented manual processes, and defined authority structures.
For CISOs, engineering leaders, and critical infrastructure operators, resilience is no longer measured only in defensive controls. It is measured in clarity and preparedness:
- What systems remain operational under isolation
- What services degrade or fail
- Which tasks must be performed manually
- How quickly trust can be restored through system rebuilds
Organisations that can answer these questions confidently are far better positioned to manage large-scale cyber disruptions. A Practical Starting Point: One-Page Resilience Control Map
The objective is simple; produce a one-page control map and gaps list that can be used for planning, investment decisions, and audit conversations.
- Define the minimum operating state for each critical service - Start by identifying each critical service and defining the minimum acceptable operating state that must be maintained to preserve safety and essential functionality.
- Identify vital OT and enabling systems - For each critical service, identify which systems are truly vital (not all systems will be vital) to maintaining that minimum operating state. Assign a clear owner to each identified system to ensure accountability during incident response and recovery
- Map isolation points and dependencies - Determine where isolation can be enacted, then map any dependencies that will result in a failure when isolation occurs. e.g. Reliance on NTP time sources for clock synchronization means millisecond level drift can destabilize HA clusters and trigger failovers.
- Establish thresholds and authority - Define the triggers for partial isolation and full isolation, and name who has authority to act. Equally important is identifying who has authority to initiate those actions, typically defined through a threshold-authority matrix.
- Plan for manual operations during isolation - Isolation inevitably disrupts automated workflows. Map the manual operations that will need to occur to the owner. No shortcuts. Contact any vendors for potential workarounds and help.
- Define the minimum outbound telemetry - Even during isolation, operators must avoid losing visibility. Define the minimum outbound data required for safe operations like safety monitoring telemetry, security alerts and logging and historian replication data. This ensures operational teams maintain situational awareness.
- Validate rebuild readiness - Ensure no backups are unavailable or untrustworthy. Offline known good and tested backups of firmware, configuration and processes for vital systems are essential and must not contain malware that may have caused the outage in the first place.
- Document the one-page artefact - Summarize all the above on one page to be used in an emergency. Include: Critical services and minimum operating state - Vital systems and owners - Isolation points and dependencies - Thresholds and decision authority - Manual operations plan - Minimum outbound data requirements - Rebuild readiness status and gaps
CI Fortify and the MetaDefender™ Platform
Over the past two decades, many industries have dramatically improved efficiency through digital transformation and increasing connectivity. CI Fortify is a reminder that true resilience requires the ability to operate with less connectivity – not more. The organisations that take this seriously tend to reduce operational surprises during incidents and create clearer alignment between cyber governance and engineering execution.
The pressure test is simple, under isolation, can the business sustain critical services safely. Under low trust, can it rebuild vital systems at pace.
OPSWAT's MetaDefender platform provides purpose-built capabilities that directly address these two core resilience requirements—isolation readiness and trusted rebuild.
MetaDefender Industrial Firewall strengthens an organisation's ability to enact and sustain network isolation by enforcing strong segmentation between IT and OT networks at the most critical layers. Designed specifically for ICS, OT, and SCADA environments, MetaDefender Industrial Firewall operates across Purdue Model Layers 2 through 3.5, protecting the assets closest to physical processes.
Its Firewall Learning Mode helps to monitor and learn normal network traffic, automatically generating security policies that reflect legitimate operational behaviour—making it possible to define and enforce precise isolation boundaries without disrupting production. Protocol-Specific Deep Packet Inspection provides granular visibility and control over industrial protocols including Modbus, EtherNet/IP, S7Comm, DNP3, OPC-UA, BACnet, PROFINET, and many others, enabling operators to block anomalous traffic, zero-day threats, and DoS/DDoS attacks at the protocol level. When isolation is enacted, this level of control ensures that only authorised, essential communications persist.
The ruggedized hardware is built for harsh industrial environments with extreme temperatures, and it integrates natively with MetaDefender OT Security to provide combined intrusion detection and prevention with continuous asset visibility—maintaining situational awareness even when external connectivity is severed. Support for IPsec and OpenVPN in recent releases also enables secure, encrypted communication across segmented or isolated OT networks when controlled vendor access or multi-site coordination is required during recovery.
MetaDefender Storage Security directly supports the second CI Fortify imperative: the ability to rebuild vital systems from trusted sources. Before any backup, firmware image, configuration file, or software update is used to restore a compromised environment, organisations must have confidence that those recovery assets are free from the very malware that may have caused the incident.
MetaDefender Storage Security addresses this by scanning stored files using multiple anti-malware engines simultaneously with Metascan™ Multiscanning technology, applying Deep CDR™ Technology to neutralize hidden threats in over 200 file types, and performing file-based vulnerability assessments—all within on-premises, hybrid, or cloud storage environments.
It integrates with a wide range of storage platforms including SMB/NFS-compatible NAS, NetApp, Dell EMC, Amazon S3, and Microsoft Azure, meaning organisations can secure their backup repositories regardless of infrastructure. Periodic and real-time scanning capabilities ensure that backup integrity is continuously validated, not just checked at the point of initial storage. This means that when the decision is made to rebuild under low-trust conditions, operators can proceed with verified, known-good recovery assets rather than introducing additional risk into an already compromised environment.
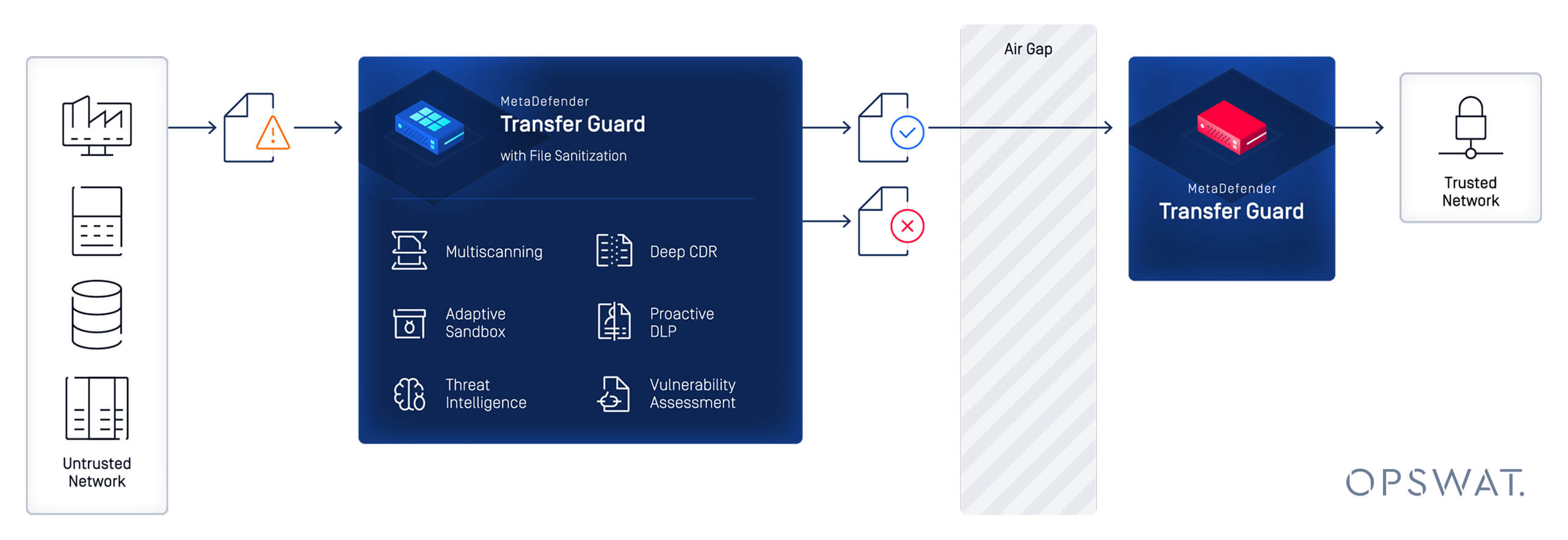
MetaDefender Managed File Transfer (MFT) and MetaDefender Diode X (Previously Transfer Guard) further extend these capabilities by providing secure, policy-controlled mechanisms for moving files across trust boundaries—a critical requirement both during normal operations and during incident recovery.
MetaDefender MFT enables secure file exchange between internal teams, external contractors, and across segmented security zones, with every file subjected to Deep CDR™ Technology, Multiscanning, and Proactive DLP™ technologies before it is admitted into a protected environment.
MetaDefender Diode X adds hardware-enforced unidirectional data transfer using optical diode technology, ensuring that no routable connection exists back into the protected zone—an essential capability for maintaining isolation while still allowing safety-critical telemetry, patches, or operational data to flow securely in one direction.
Together, these solutions provide a layered, practical foundation for CI Fortify alignment: enforcing segmentation, controlling data flows across trust boundaries, protecting critical systems from file-borne and network-borne threats, and ensuring that backup and recovery workflows are built on verified, trustworthy assets.
For critical infrastructure operators navigating evolving cyber threats and resilience requirements, building an isolation-ready OT architecture is no longer optional—it is foundational.
Learn how OPSWAT solutions can help strengthen OT resilience and support CI Fortify principles—connect with an expert today.