MetaDefender Technology Stack
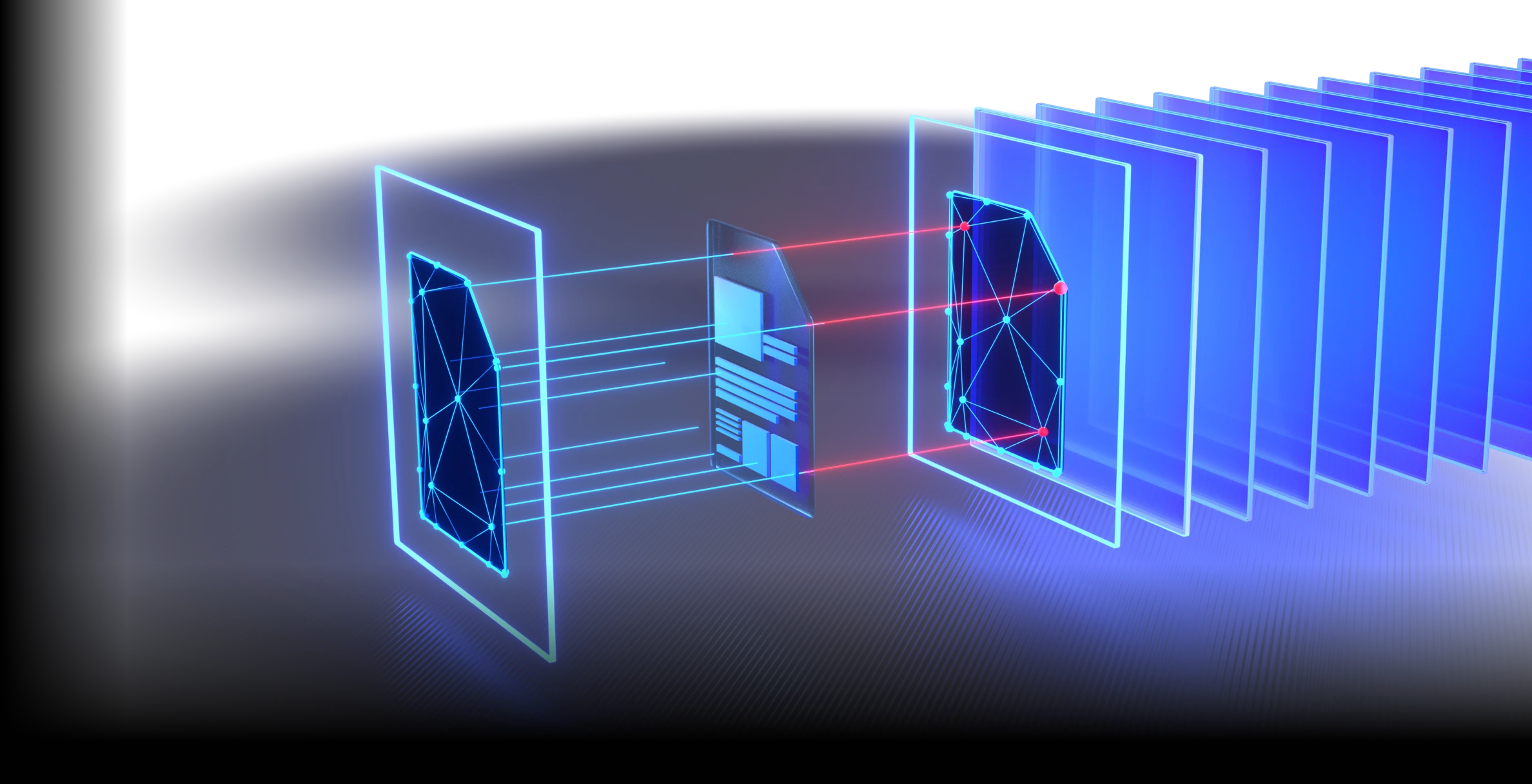
The MetaDefender Technology Stack powers the entire MetaDefender Platform with AI-driven technologies designed to work in
concert. Whether protecting email, cloud, storage, peripheral media, managed file transfer, or any data channel, these
technologies create multiple layers of defense that adapt to evolving threats in real time across all your use cases.
- Universal Platform Foundation
- Cross Channel Protection
- Continuous Threat Intelligence
OPSWAT's First AI Predictive Engine
for Zero-Day Detection Without Execution
100% Protection
Verified by SE Labs Deep CDR™ Technology Test

All-In-One
Technology Stack with AI-powered Capabilities
>99.2%
Malware Detection
#1 Market Leader
Multiscanning & Deep CDR™ Technology
20x Faster
AI-powered Zero-Day Detection
Technology Explorer
Filter by capability, technology and feature.
Comprehensive Threat Prevention,
Detection and Compliance
OPSWAT layers Deep CDR™ Technology, Metascan™ Multiscanning, AI-driven threat prediction, and Adaptive Sandbox to prevent, detect,
and neutralize threats before they execute.
Built for Prediction,
Engineered for Speed
- Deep file structure analysis
- ML-Model trained on zero-day threats
More Engines Are Better Than One
- Detect nearly 100% of malware
- Scan simultaneously with 30+ leading AV engines
Stop Threats That Others Miss
- Supports 200+ file formats
- Recursively sanitize multi-level nested archives
- Regenerate safe and usable files
True File Type Detection for Security-Critical Workflows
- AI-Enhanced
- Detects spoofed file types in milliseconds
- Inline enforcement without performance loss
Prevent Sensitive Data Loss
- Utilize AI-powered models to locate and classify unstructured text into predefined categories
- Automatically redact identified sensitive information like PII, PHI, PCI in 125+ file types
- Support for Optical Character Recognition (OCR) in images
Detect Evasive Malware with Advanced Emulation-Based Sandboxing
- Analyze files in a high-speed
- Anti-evasion sandbox engine extracts IOCs
- Identify zero-day threats
- Enable deep malware classification via API or local integration
Enhance Detection with Real-Time Threat Intelligence
- Correlate global IOCs, IPs, URLs, & file reputation across 50B+ artifacts
- Stop emerging threats faster
- Enrich downstream analysis
Secure Your Software Supply Chain
- Manage risks associated with open-source software (OSS), 3rd party components and dependencies
- Ensure codebase transparency, security, and compliance
Detect Application Vulnerabilities Before They Are Installed
- Check software for known vulnerabilities before installation
- Scan systems for known vulnerabilities when devices are at rest
- Quickly examine running applications and their libraries for vulnerabilities
Enable Instant Detection of a File’s Geographic Source
- Detect the geographic source of uploaded files, including PE, MSI, and SFX (self-extracting archives)
- Automatically analyze digital fingerprints and metadata to identify restricted locations and vendors
Recursively Extract and Analyze Deeply Nested Archive Files
- Recursive extraction to configurable depth
- Single-pass extraction across all engines
- Archive bomb detection and containment
- Encrypted and password-protected archive support
Research Center
Discover in-depth analyses and insights, including our Zero-day Detection live view, to better understand the effectiveness of various cybersecurity strategies.