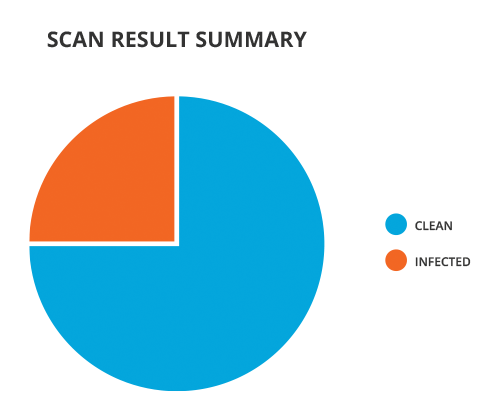
Certain sites have a reputation for being safe from malware. CNET's Download.com is such a site; most people assume files hosted on that site are malware free. We decided to do a quick test of that assumption using the top 20 downloads for each of the four most popular operating systems: Windows, OSX (Mac), iOS (iPhone, iPad), and Android. We scanned each download package against 35+ anti-malware engines to see what kind of results we would get. The results showed that 25% of our sample of downloads were flagged as suspicious by at least one anti-malware engine. For both Windows and Android, 8 out of the 20 scanned files were flagged as potentially harmful, whereas for OSX and iOS, only 3 out of 20 and 1 out of 20 files were flagged, respectively.
| Category | Clean | Suspicious |
| Windows | 12 | 8 |
| OSX | 17 | 3 |
| iOS | 19 | 1 |
| Android | 12 | 8 |
No file was flagged by a majority of the engines, but half of the flagged files were identified as suspicious by five or more engines. A little over a third of the flagged files were selected by only one anti-malware engine. This inconsistent detection indicates that no single anti-malware engine can offer comprehensive protection from threats.
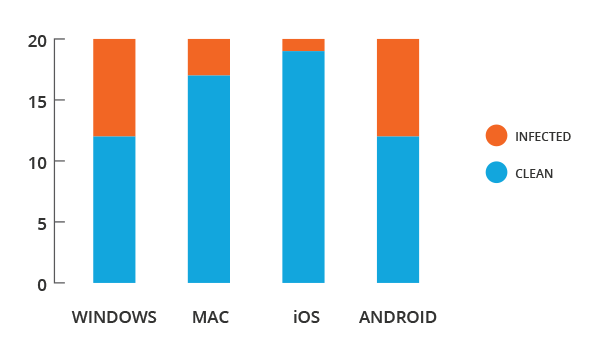
Scan Results by Operating System
We found that adware was the most common form of malware detected in this set of files. The general consensus among the security community is that adware is not as harmful as other types of malware, but it is certainly not innocuous. George Prichici, Metascan® Online's product manager, urges people to be wary when downloading applications, even from a notable source like CNET. Recent malware scams like Gunpoder show even trusted sites can pass along malware. Gunpoder was hidden behind an advertisement module and embedded code within a popular game engine, which then allowed it to fool antivirus engines by masquerading as a piece of adware. Given that standalone AV engines are inconsistent when scanning for known malware, complex threats like Gunpoder have a higher likelihood of being detected by using multiple scanning engines. You can view statistics on top malware threats, and how well standalone scanning engines were at detecting them on Metascan Online's Stats Page.
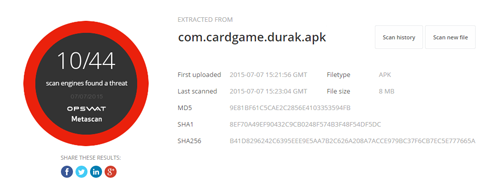
Click to View Gunpoder Scan Details from Metascan Online
Malware can exist everywhere, even at trusted sites. Yet people need to download files. The key is to take extra steps to reduce the risk that a file is malicious. Having files scanned by the 44 engines on Metascan Online is one such extra step. If you install the Chrome extension for Metascan Online, you can have newly downloaded files automatically submitted to Metascan Online and see the results on a new tab in Chrome (though note that it will not quarantine the file or in any other way prevent you from using it). You can also look at the specific name of the threat and conduct the corresponding research for it, though often the threat name is proprietary to the vendor, and there is no freely obtainable information about it. If you can wait to use the file, resubmit it to Metascan Online on subsequent days to see if there is an increase in the number of flags (i.e. is it possible there is new malware only starting to get detected by all of the anti-malware vendors). Ultimately there is no foolproof way to know if a file you are downloading is free of malware, but you can make a more informed assessment by using Metascan Online. As the Russian proverb goes, trust but verify.

File quarantine can help you identify the source of a threat by performing an analysis of the file as well as removing the risk of losing valuable data from improperly classifying a clean file. In this way, quarantine helps you take a deeper look at files from a site, such as the ones mentioned above from Download.com, and verify if they are safe to use. If you are interested in learning more about file quarantine, you can read our white paper, Three Considerations for File Quarantine Configuration. The white paper covers the three main aspects to consider when configuring and maintaining a file quarantine, and the security benefits of implementing a quarantine within your security architecture.

