CVE-2025-8088 is a path traversal vulnerability in WinRAR affecting versions prior to 7.13. Exploiting this vulnerability enables a specially crafted archive to bypass filename and path validation during archive extraction and cause attacker-controlled content to be written to specific locations on an NTFS volume. Under certain conditions, this writing capability can be leveraged for remote code execution.
Graduate fellows from the OPSWAT Cybersecurity Fellowship Program have conducted a technical analysis of CVE-2025-8088. The findings of this analysis of RAR5 and NTFS (ADS) mechanics trace the extraction workflow and ADS-handling path that lead to unsafe writes, and summarize practical mitigation and remediation guidance for cybersecurity practitioners and organizations.

Introduction to CVE-2025-8088
WinRAR is one of the most used archive utilities on Windows. It supports preserving and restoring NTFS-specific metadata, such as ADS (Alternate Data Streams). CVE-2025-8088 is present in the ADS-handling logic of specific WinRAR versions. In vulnerable versions, a malicious archive can influence the stream identifier used during extraction, with inadequate path normalization and validation in the ADS creation workflow enabling directory traversal.
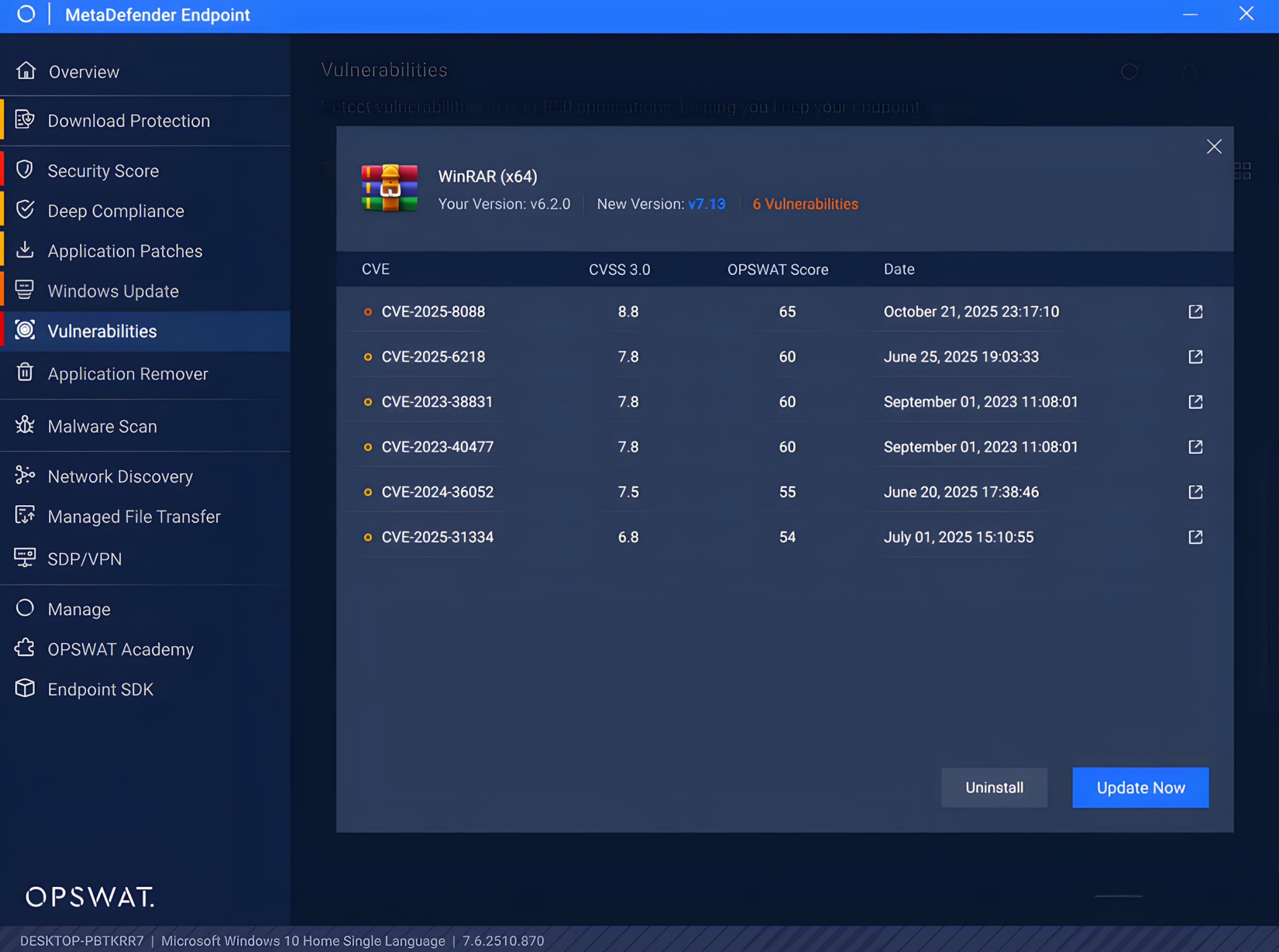
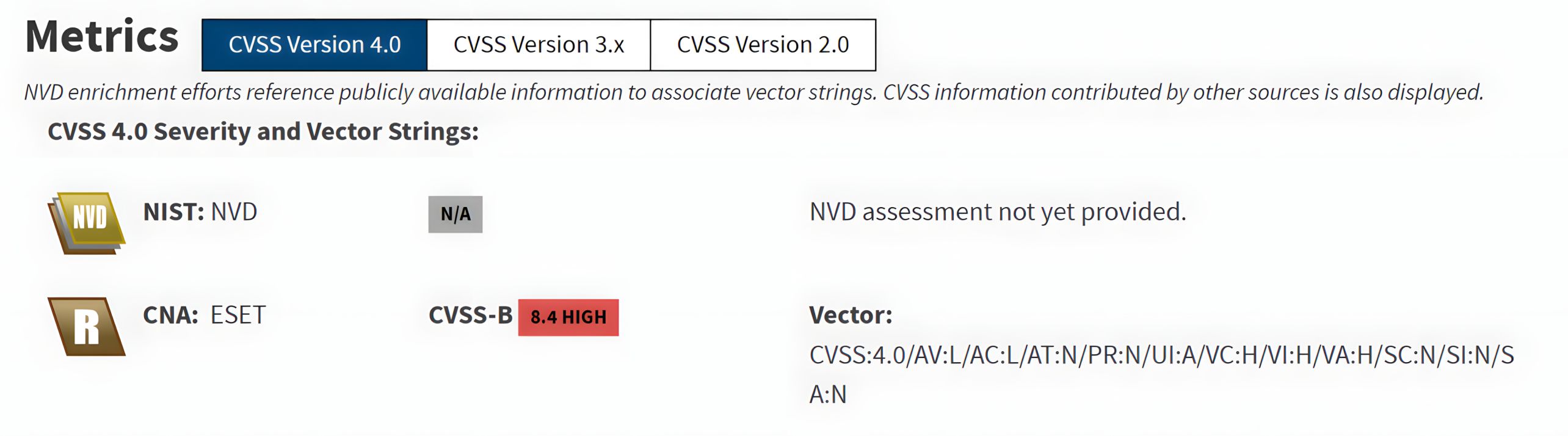
CVE-2025-8088 is assessed as a high-severity issue, with a CVSS v4.0 base score of 8.4 (High), reflecting the potential for measurable security impact if a user extracts a specially crafted archive using a vulnerable version of WinRAR.
Technical Background
NTFS Alternate Data Streams
NTFS (New Technology File System) is the default filesystem for modern versions of Windows. Compared to FAT-based filesystems, NTFS supports advanced capabilities including ACLs (access control lists), EFS encryption, compression, hard links, reparse points (junctions and symlinks), and ADS.
ADS is an NTFS feature that allows a single file or directory to contain multiple independent streams of data. The primary, user-visible content is stored in the unnamed default stream, commonly represented as ::$DATA, while additional named streams can be accessed using the syntax:
filename.ext:streamname
These named streams are not normally visible in standard Windows Explorer views, but they are fully supported by the filesystem and can be enumerated using supported tooling. For instance, dir /R can display alternate streams.
WinRAR supports extracting archive entries that include ADS syntax. When such entries exist within an archive, WinRAR writes the corresponding content into the target file’s alternate stream during extraction.
Understanding the RAR5 File Structure
The RAR5 archives are stored as a sequence of blocks. Each block starts with a header that defines the block type and size information. It may optionally include an additional metadata area and a data area consisting of payload bytes, such as compressed content.
Block = Header + (optional Extra Area) + (optional Data Area)
RAR5 uses several block types. The relevant block types in the CVE are:
- File header (type 2): Describes a file entry in the archive (name/path, attributes, timestamps, compression parameters) and is followed by the file’s payload data
- Service header (type 3): Optional supplementary headers that store additional metadata associated with the archive or a specific file entry, such as ADS
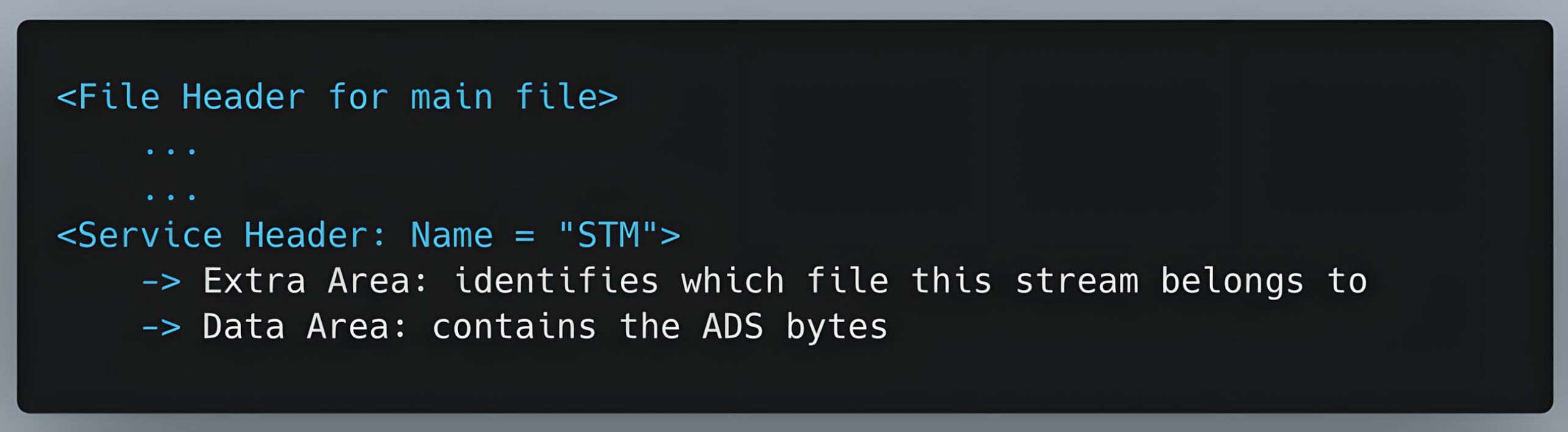
ADS in the NTFS file system are represented by a Service header (type 3), referred to as STM. The service header’s data area contains the ADS stream bytes for the base file entry.
In simplified form:
Technical analysis (CVE-2025-8088)
RAR5 Extraction Workflow
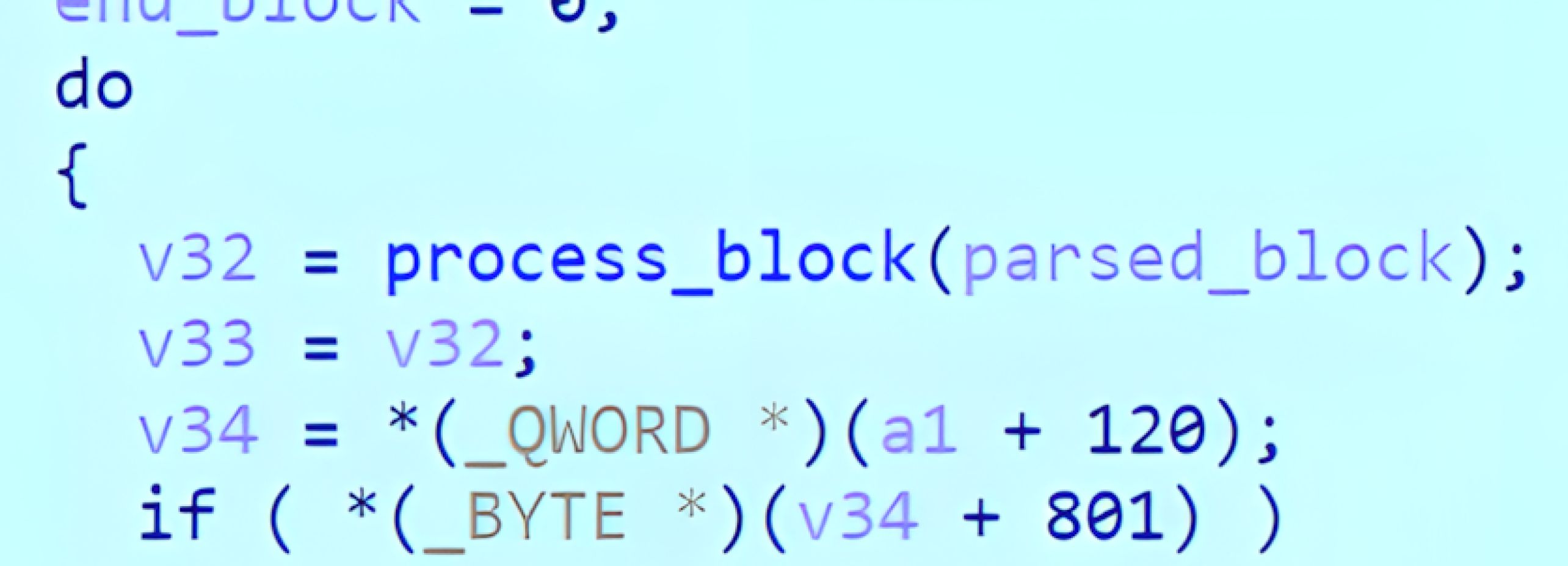
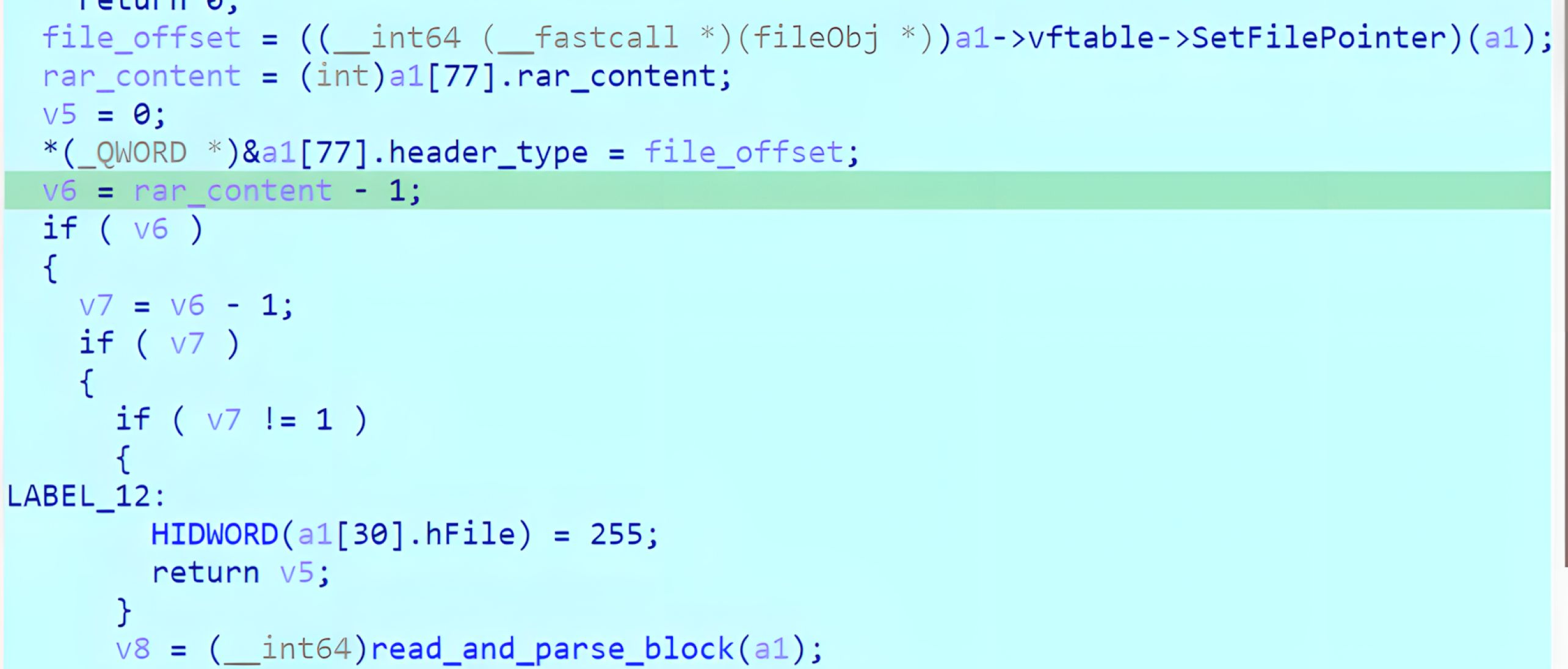
WinRAR processes RAR5 archives as a sequence of blocks. During extraction, it iterates over these blocks, parses each block header, and validates header integrity using the embedded CRC32 before continuing. After a file entry is processed, WinRAR decompresses and writes the base file content to the disk, then determines whether additional NTFS-related metadata must be applied via associated service records. When an ADS (Alternate Data Stream) record is present, such as an STM service entry, WinRAR enters the ADS-handling path, combines the base file path with the stream name to form the ADS target, and creates the stream.
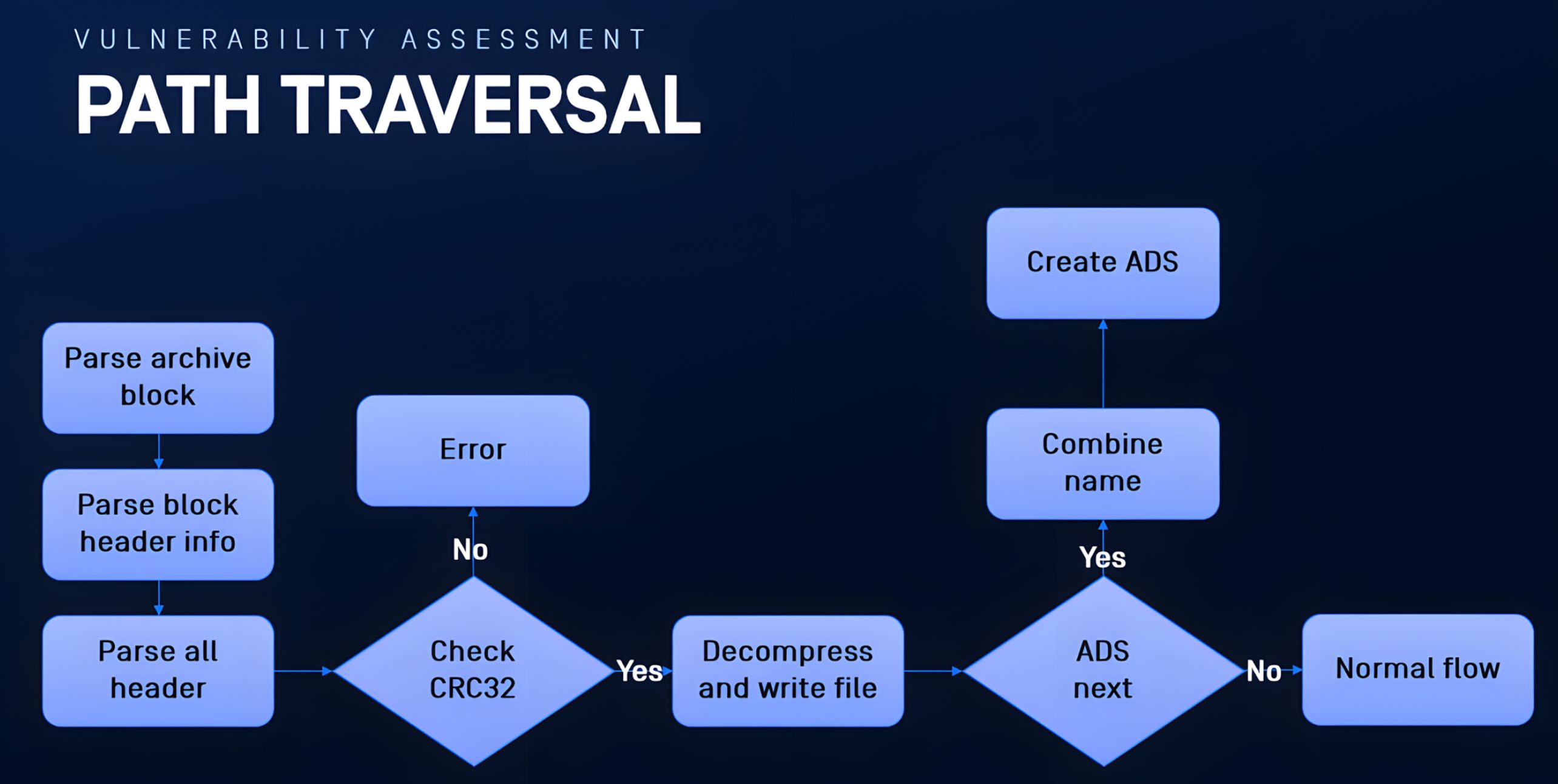
In CVE-2025-8088, the root cause is that ADS stream creation invokes the Windows API CreateFileW() using a path derived from archive-controlled metadata, making the ADS path construction/validation insufficient to prevent traversal.
Identifying the ADS (“STM”) code path
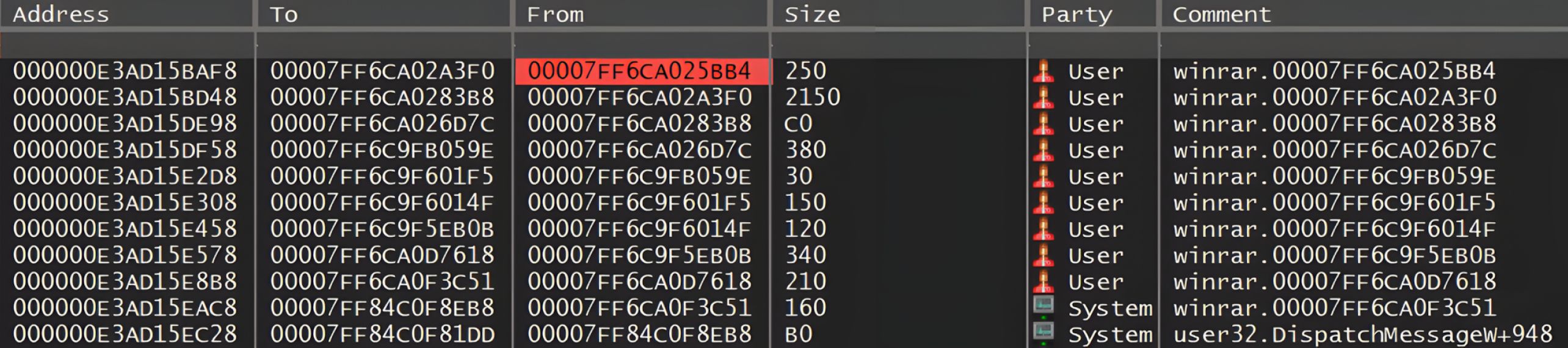
Our graduate fellows performed a combination of static and dynamic analysis in a controlled lab environment using WinRAR 7.12. They located ADS-related logic by searching for the “STM” service marker in the binary and then confirmed the extraction-side code path at runtime.
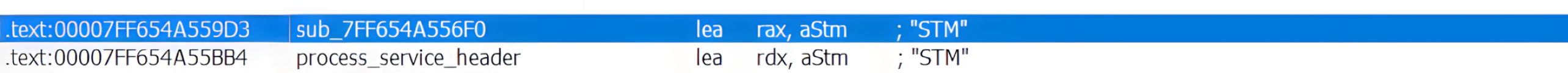
By placing a breakpoint on the “STM” reference encountered during the extraction of an archive containing ADS data, the breakpoint was consistently hit, validating that this execution path is invoked during the normal extraction workflow.
Upon hitting the breakpoint, the debugger call stack was used to reconstruct the sequence of functions invoked after the “Extract” action in the WinRAR UI, establishing a clear anchor for the downstream block-processing and ADS execution path.
Header Parsing and CRC32 Validation
WinRAR processes each RAR5 block by reading the block header, validating integrity fields, and dispatching to a block-type-specific handler. The block-processing entry point and the associated header parsing logic are shown in Figures 6-10, where WinRAR sets the file pointer to the current block offset, reads the initial header bytes, which include header type and size, and validates header integrity using CRC32 before continuing.
After successful validation, it parses additional header fields, such as flags, unpacked size, compression method, and optional checksums. Then, it processes the block body.
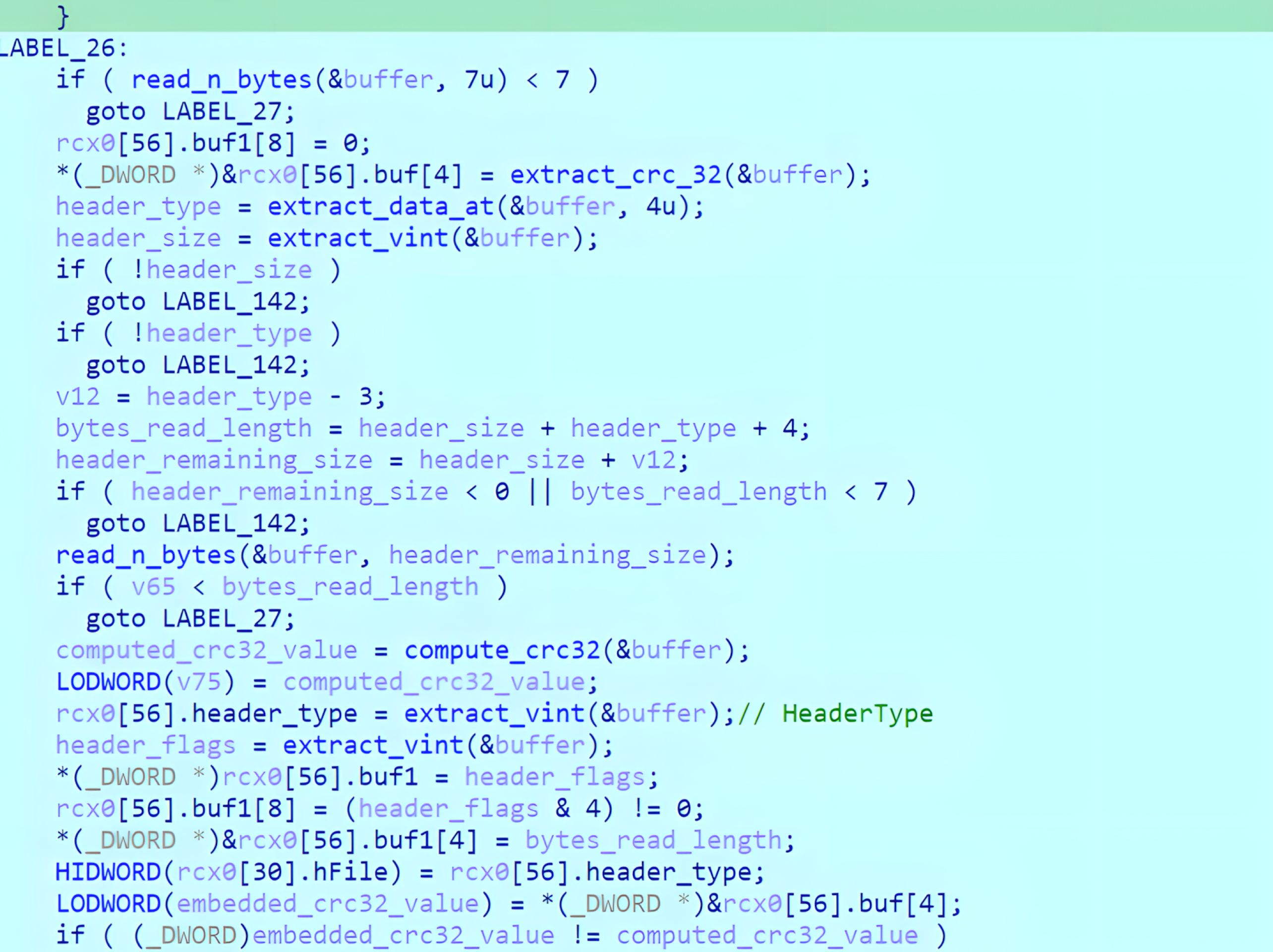
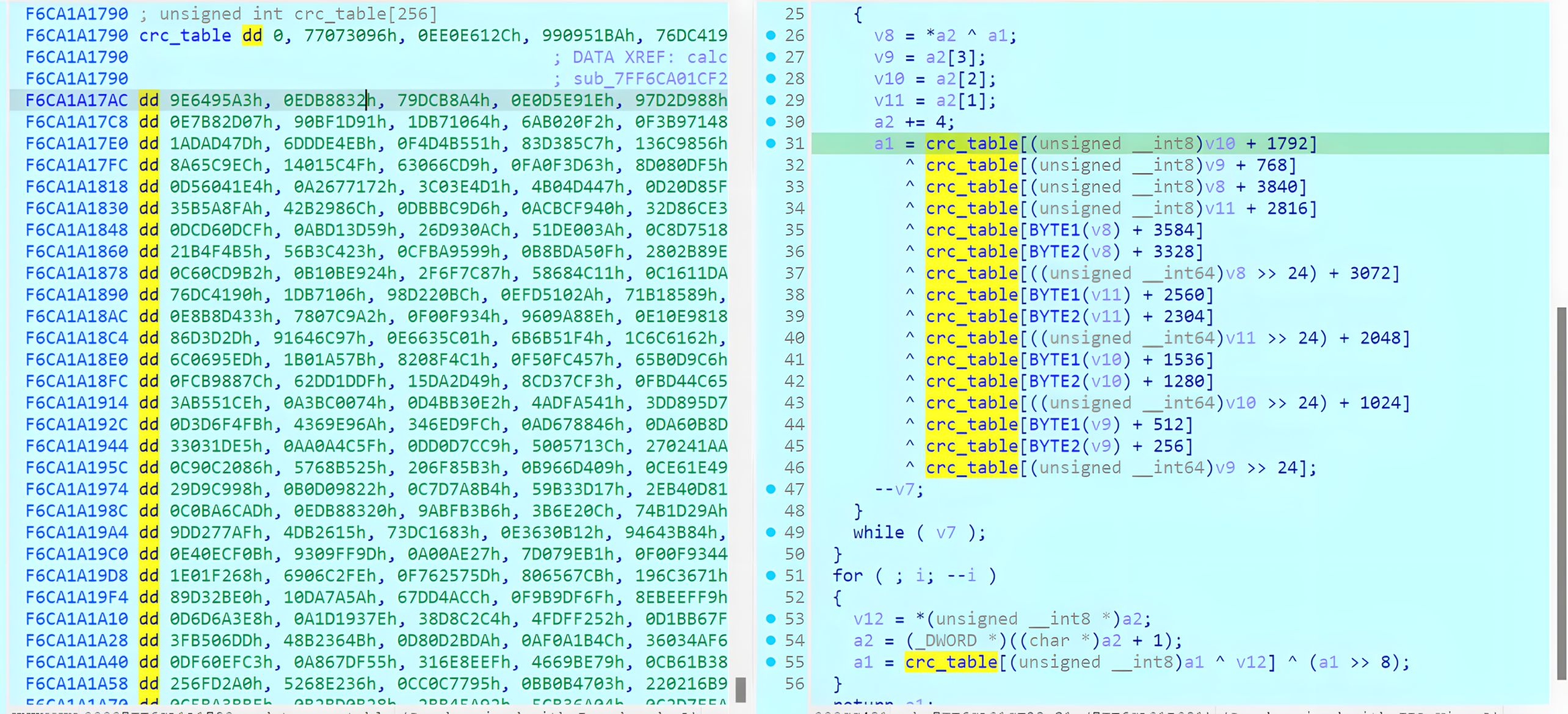
During reverse engineering, the CRC32 routine was observed to behave consistently with a standard zlib-style CRC32 implementation. Practically, this CRC32 check serves as an integrity gate. If header fields are modified, the embedded CRC32 must be updated to ensure WinRAR accepts the header and continues processing.
After validating the CRC32 header, the parser continues by extracting the remaining header information, such as the unpacked size, compression method, and other attributes.
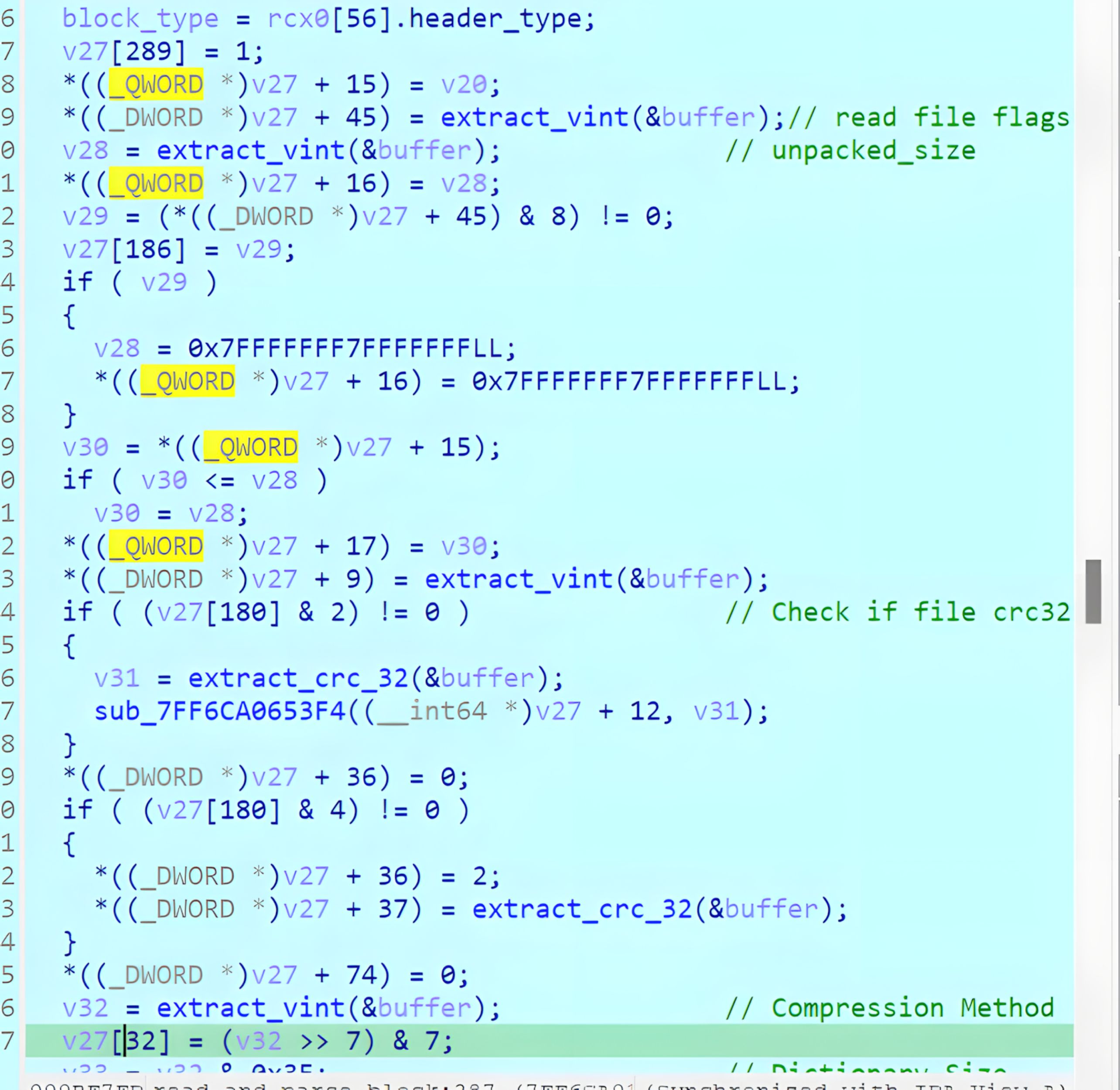
After header parsing and validation are complete, WinRAR processes the block body based on the parsed header type and flags.

In CVE-2025-8088, the header integrity validation is enforced before WinRAR dispatches to the Service block handler that processes ADS records.
ADS creation via Service block (“STM”)
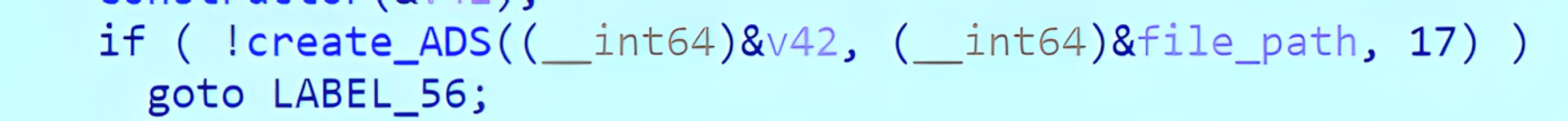
The ADS processing path is reached when WinRAR encounters a Service block. Service blocks use block type value 3. When a Service block is detected, WinRAR dispatches it to a service-header handler.
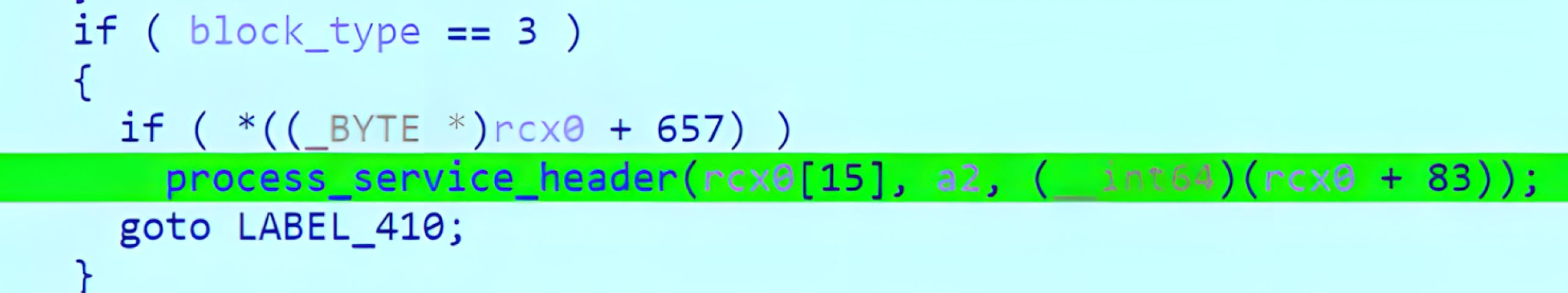
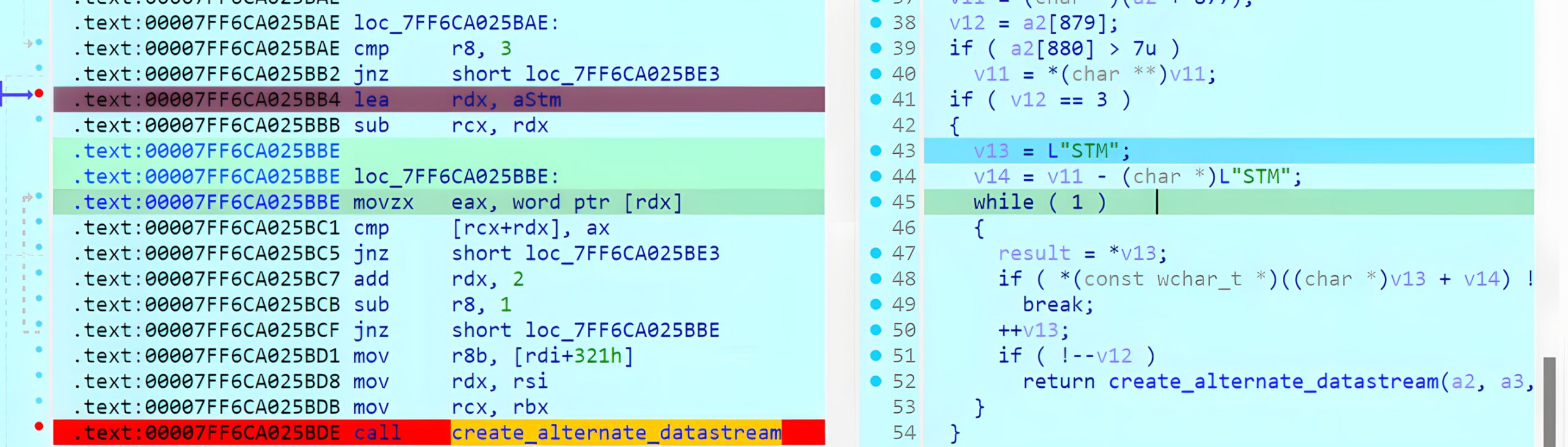
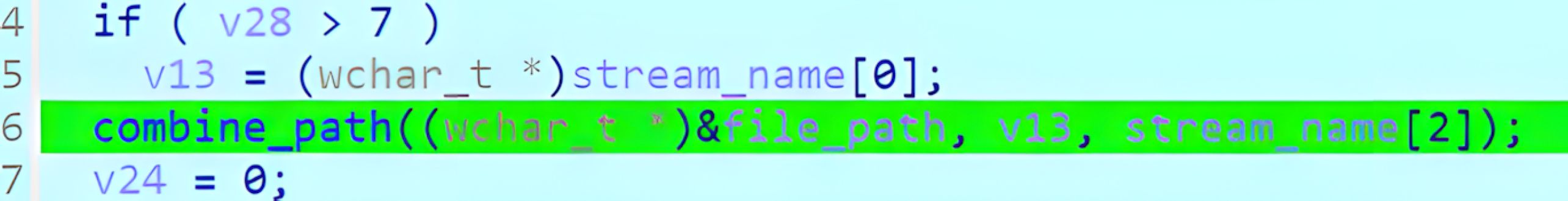
Within the service handler, WinRAR checks the service name. When the service name matches “STM”, the record is treated as an ADS payload, and the implementation transitions into an ADS creation routine.
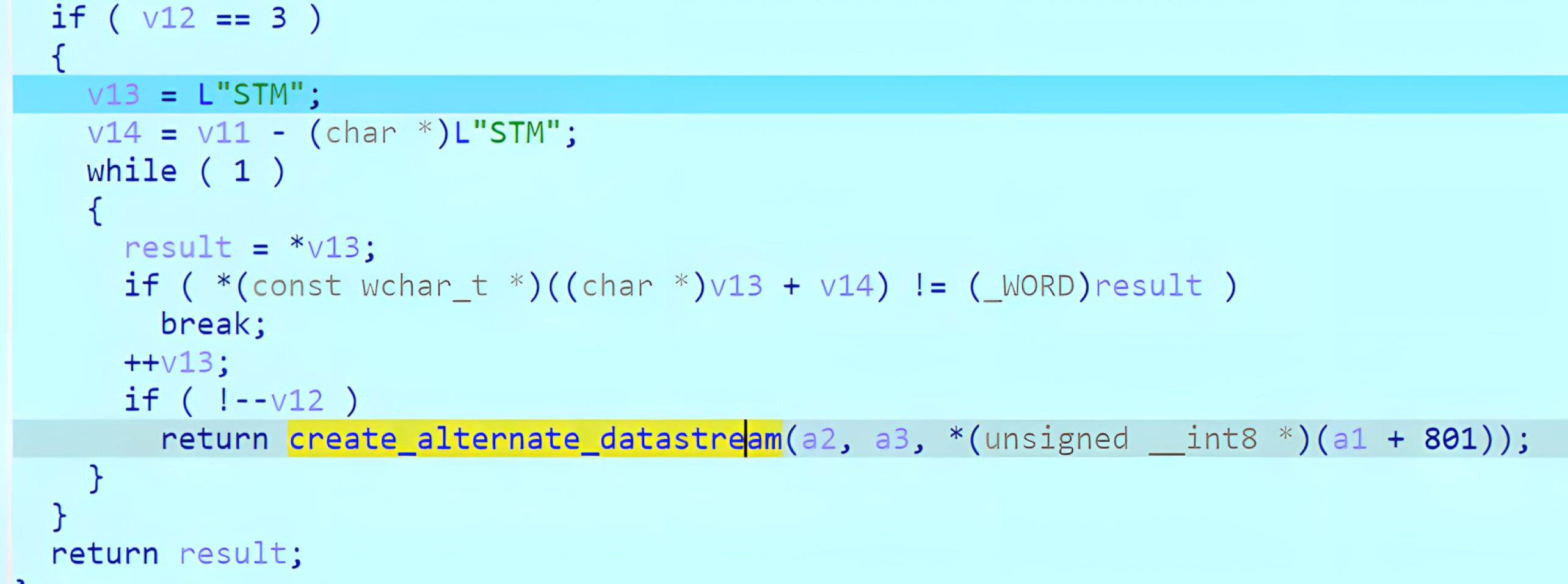
WinRAR then retrieves the stream name from the service record and combines it with the base file path to construct the final ADS target. In versions prior to 7.13, the analysis shows that the stream name is not sufficiently sanitized, allowing traversal sequences to influence the resolution of the resulting target path.
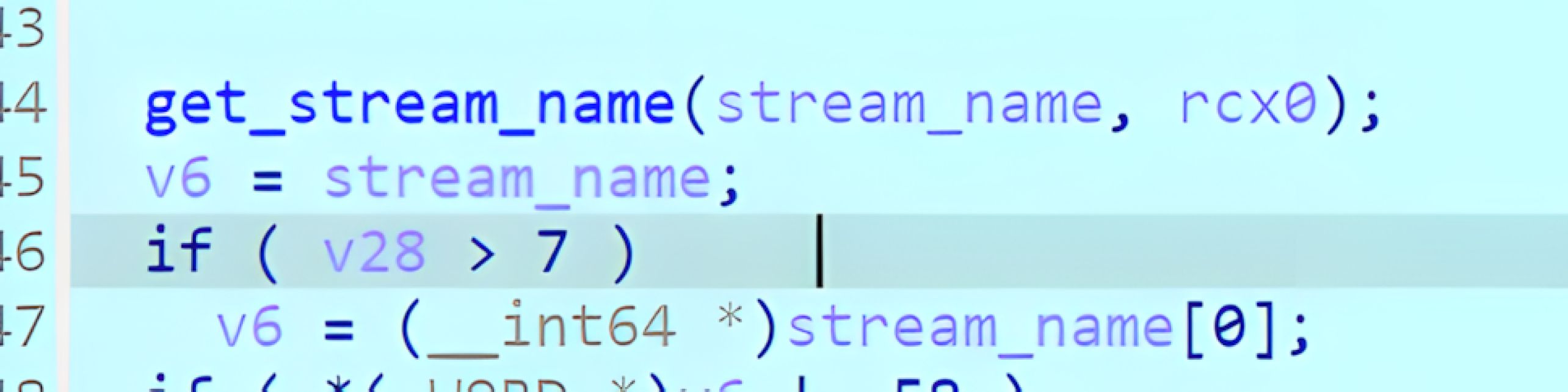
After constructing the target, WinRAR creates the stream via a helper routine that invokes the Windows CreateFileW API, and then writes the ADS bytes using WriteFile. If the resolved path is outside the user-selected extraction directory, WinRAR will create the destination stream/file and populate it with attacker-controlled content.
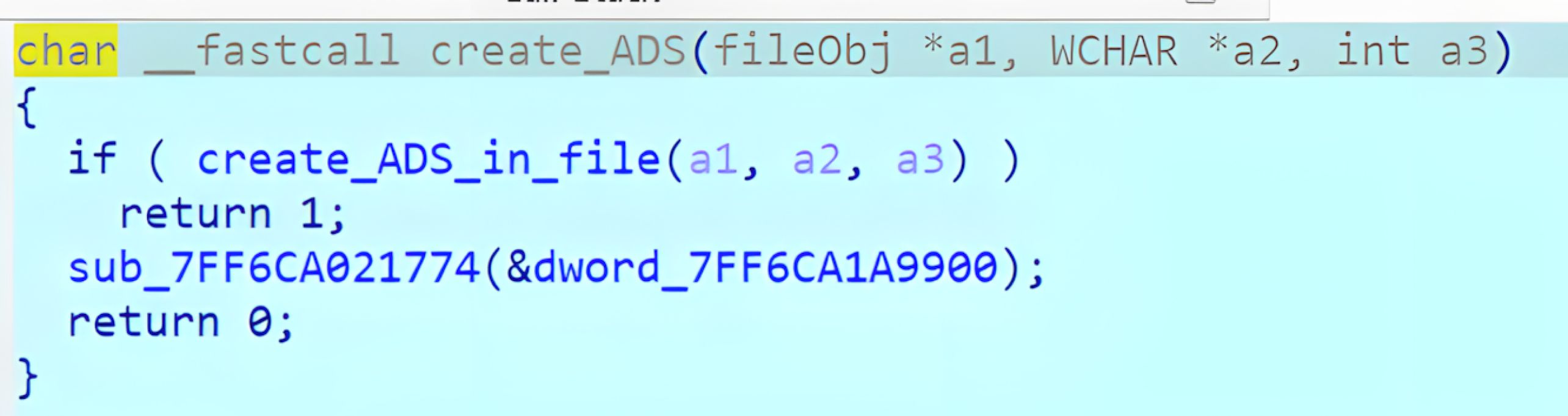
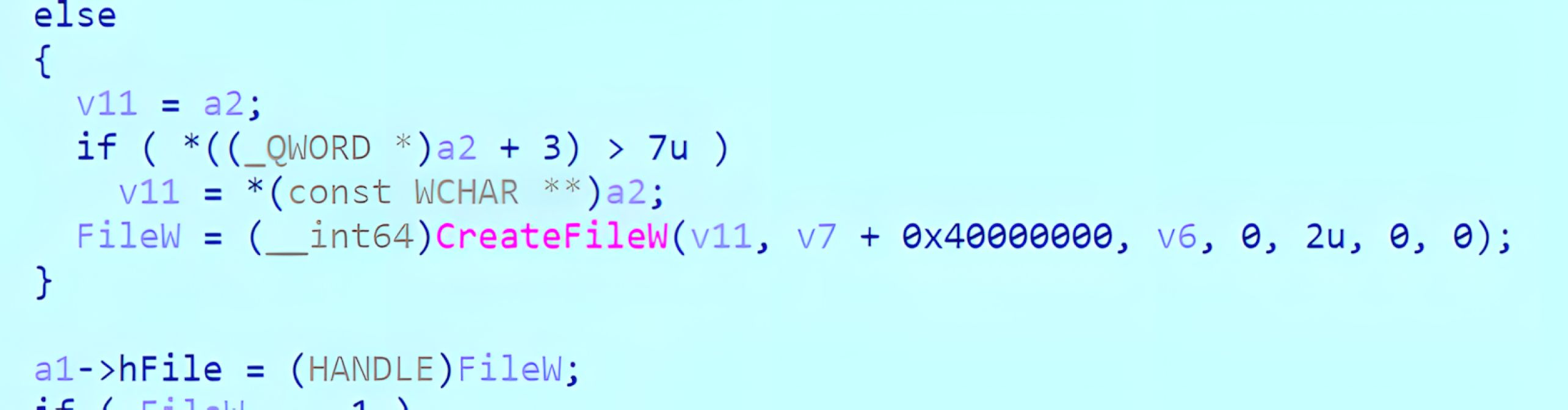
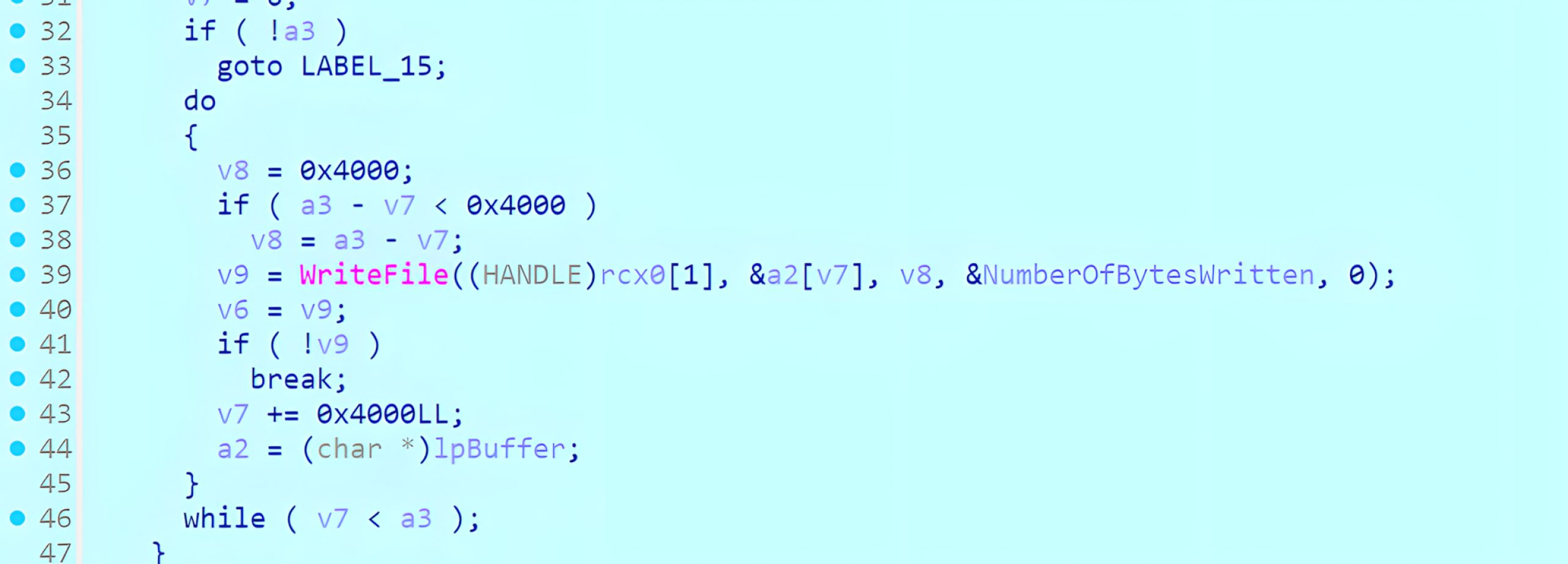
In summary, the ADS extraction workflow exposes two security-relevant conditions. First, the ADS stream name is not sufficiently sanitized, allowing traversal sequences to influence the resulting target path. Second, WinRAR creates the ADS stream by calling CreateFileW() with a path derived from archive-controlled metadata.
Together, these conditions allow a crafted archive to steer the CreateFileW() target outside the intended extraction directory and write attacker-controlled content to an attacker-influenced location. If the destination is a persistence-relevant directory (for example, the user’s Startup folder), this write primitive can enable follow-on code execution on the next logon or reboot, depending on the payload type and system configuration.
Attack Scenario
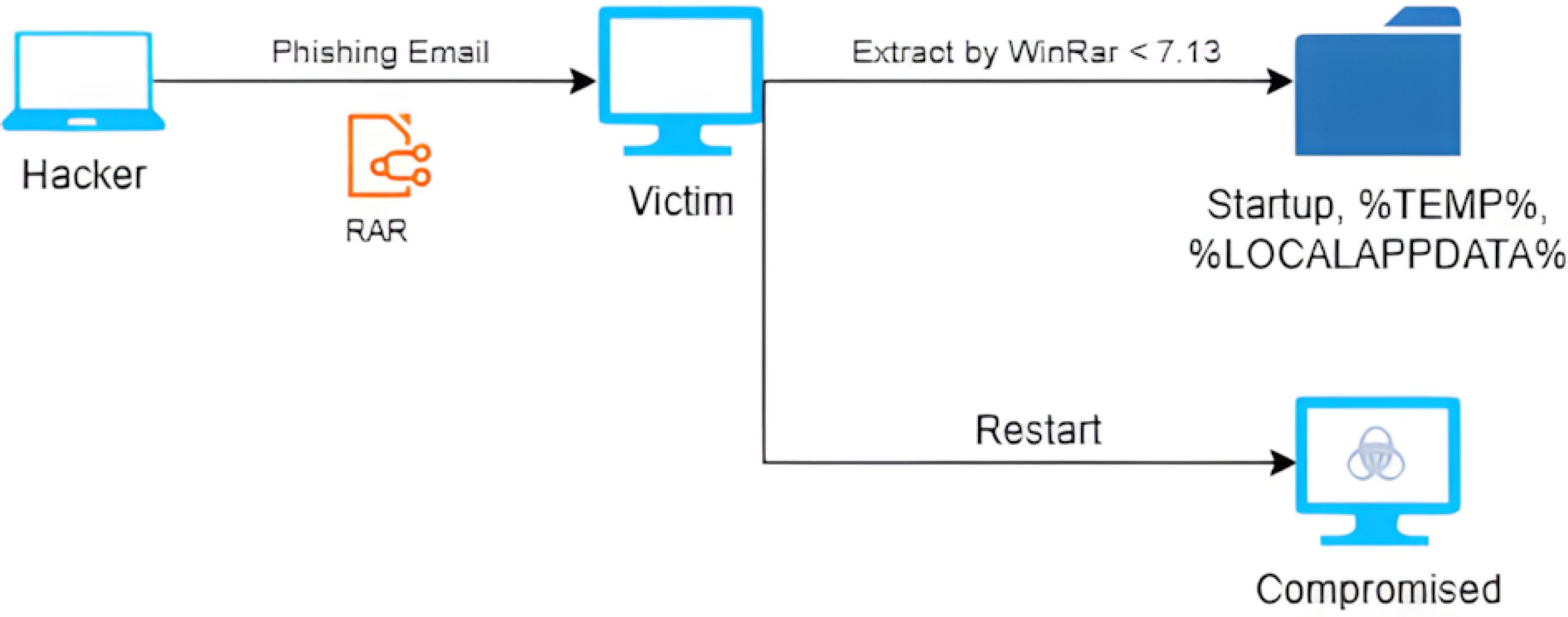
CVE-2025-8088 is practically exploitable in scenarios where an attacker induces a user to extract a crafted RAR archive using a vulnerable version of WinRAR. A typical delivery vector is social engineering, such as phishing, which leads the victim to trust a malicious archive and initiate extraction in a critical system.
The archive embeds an ADS (“STM”) service record. Its stream name is constructed to introduce traversal semantics. During extraction on NTFS, WinRAR processes the ADS record and derives the destination stream path from archive-controlled metadata. Because this ADS path construction is insufficiently constrained, the resolved target can fall outside the user-selected extraction directory, including critical locations such as the user’s startup folder.
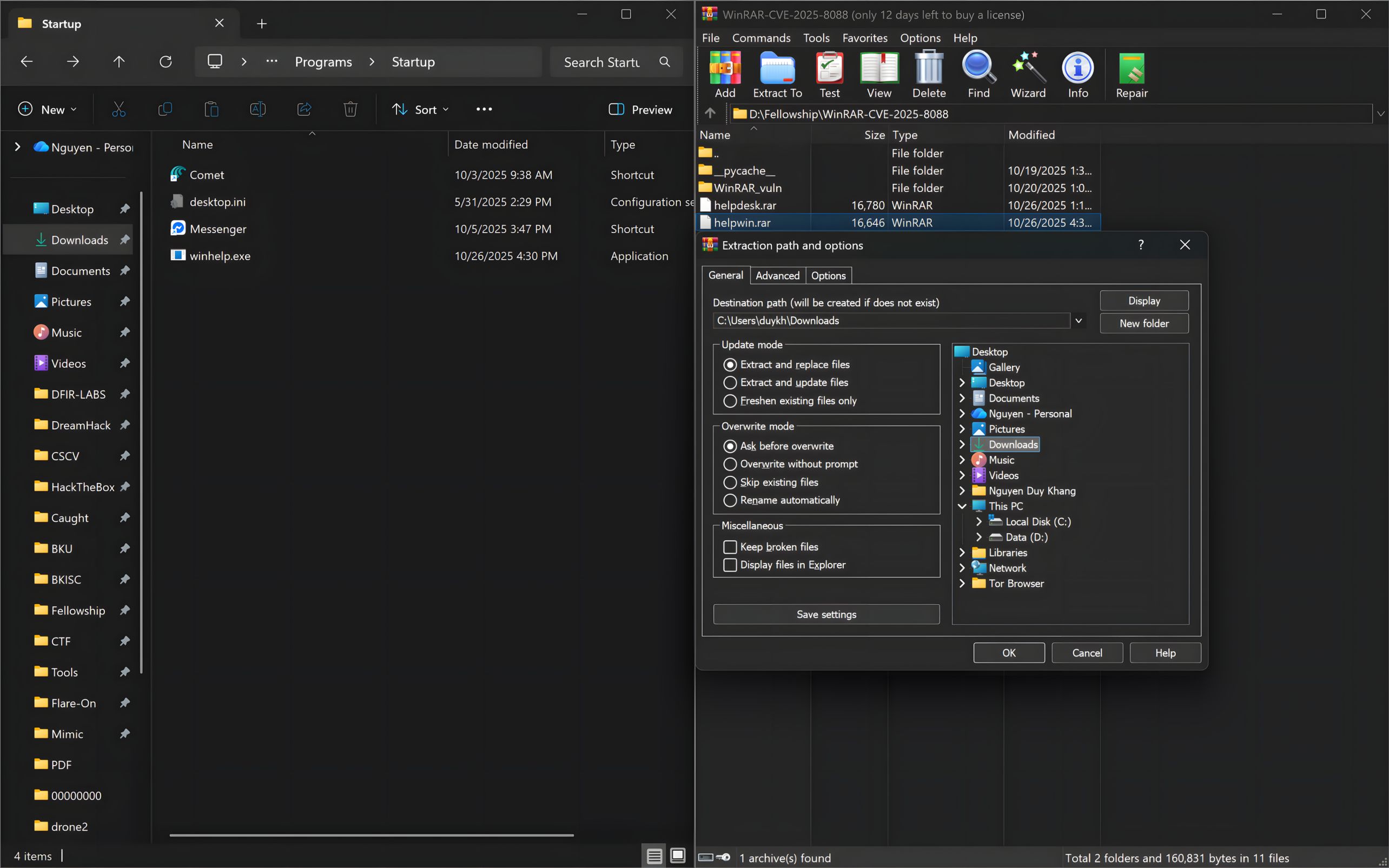
Proof Of Concept
To demonstrate CVE-2025-8088, our graduate fellows prepared a crafted RAR archive file containing an ADS (“STM”) service record with attacker-controlled fields. This archive is structured with an ADS stream name that includes traversal sequences. This structure influences the final target location during ADS handling, including the path passed to CreateFileW() when the stream is created. To ensure that WinRAR accepts the modified metadata and reaches the ADS-processing path, the relevant header CRC32 values are recomputed so the archive passes header integrity validation.
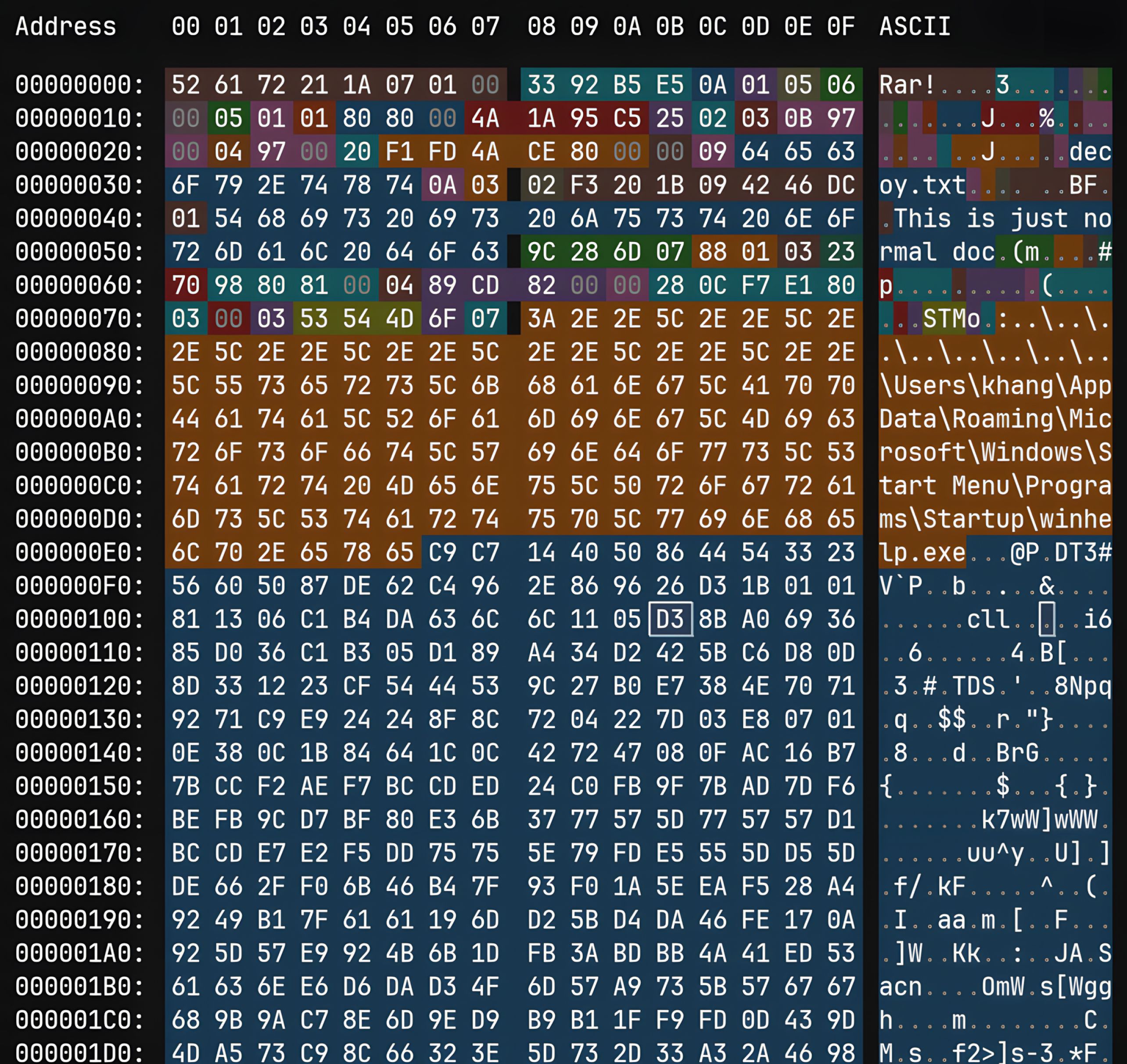
When a vulnerable WinRAR version enters the ADS-processing routine during the extraction of the crafted archive, it writes the attacker-controlled content to the pre-selected destination rather than the intended user-selected extraction directory. After extraction, payload execution is determined by its format and the execution semantics of the pre-selected destination. For instance, locations that may execute content on the next login or reboot.
Remediation
The risk of CVE-2025-8088 can be mitigated by updating WinRAR to a patched version (7.13 or later) across all managed endpoints. If a timely update is not possible, compensating controls must be considered, such as:
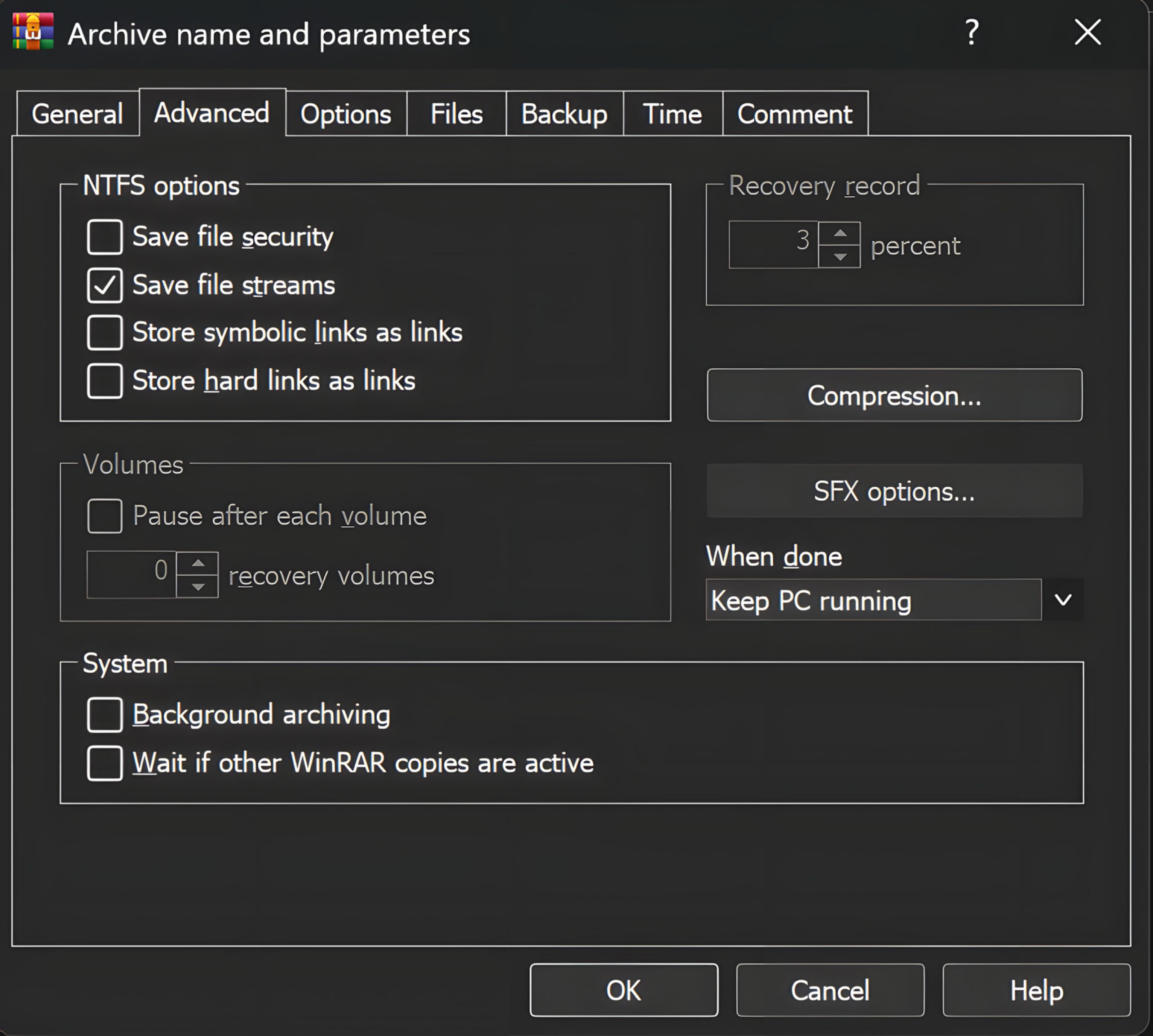
- Limiting or disabling ADS preservation in archive tooling when not required
- Restricting the extraction of untrusted archives to isolated environments
- Enforcing least-privilege operation (avoid running extraction tools elevated)
- Monitoring critical directories, such as startup locations, for unexpected writes originating from archive extraction workflows
For early advanced vulnerability detection and fast remediation, MetaDefender Endpoint™ supports urgent remediation operations by identifying devices running vulnerable WinRAR versions and highlighting required updates. Its robust vulnerability and patch management capabilities, which support more than 1100 applications, proactively identify endpoints running unpatched or out-of-date operating systems and third-party applications and deliver recommended fixes.
The Vulnerability Management feature enables administrators to quickly detect exposure, prioritize remediation, and drive upgrades to a patched release, reducing the risk of archive-based file-write attacks, such as CVE-2025-8088, and similar endpoint-based threats.