Proactive DLP™
Detect, redact, and anonymize sensitive data across 125+ file types, aiding compliance and enforcing data handling policies.
- Sensitive Data Protection
- Breach and Insider Threat Prevention
- Regulatory Compliance Support
OPSWAT is Trusted by
125+ File Type Coverage
AI-Driven
NSFW & Inappropriate Content Detection
HIPAA-Aligned
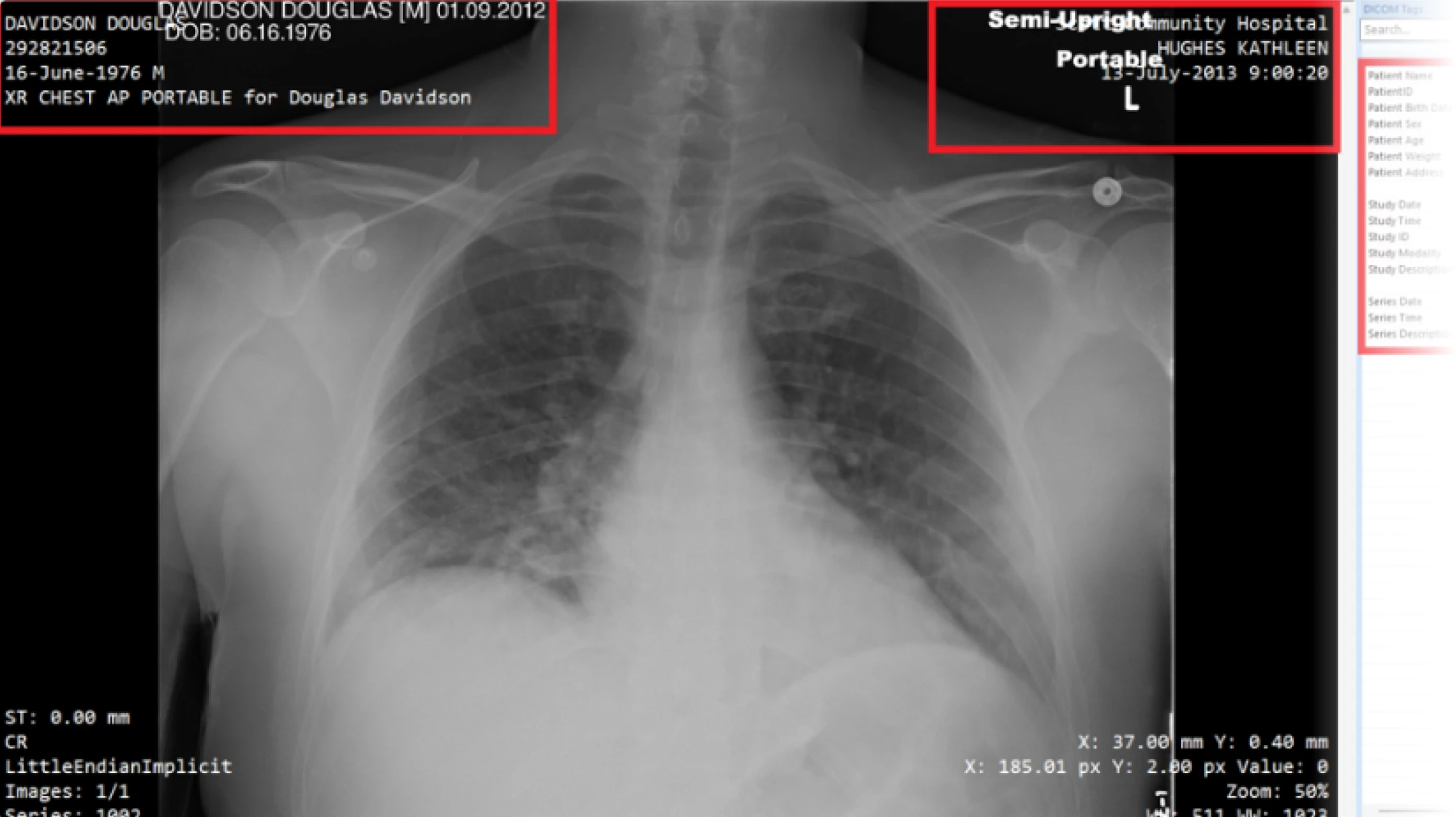
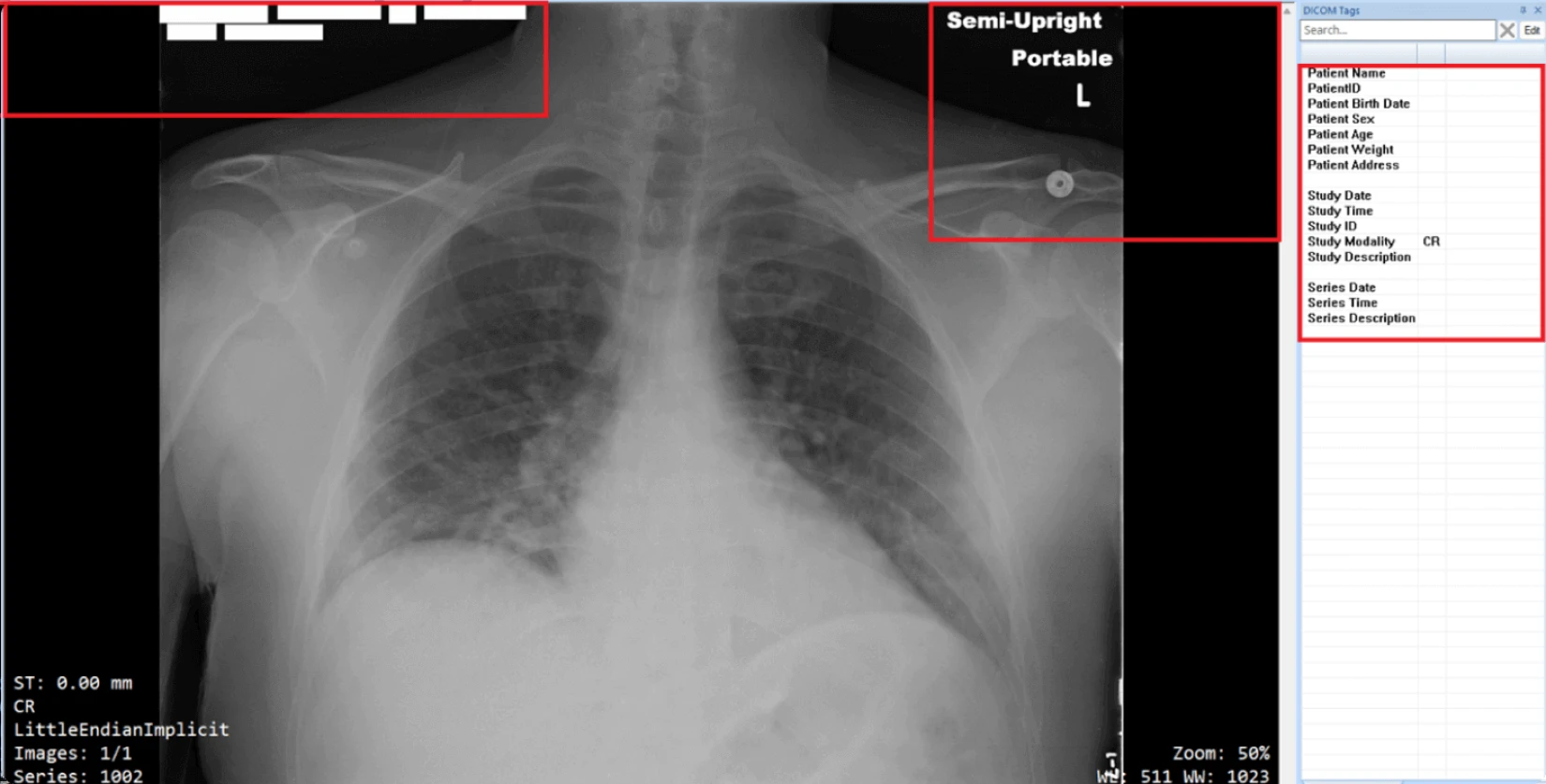
DICOM Anonymization
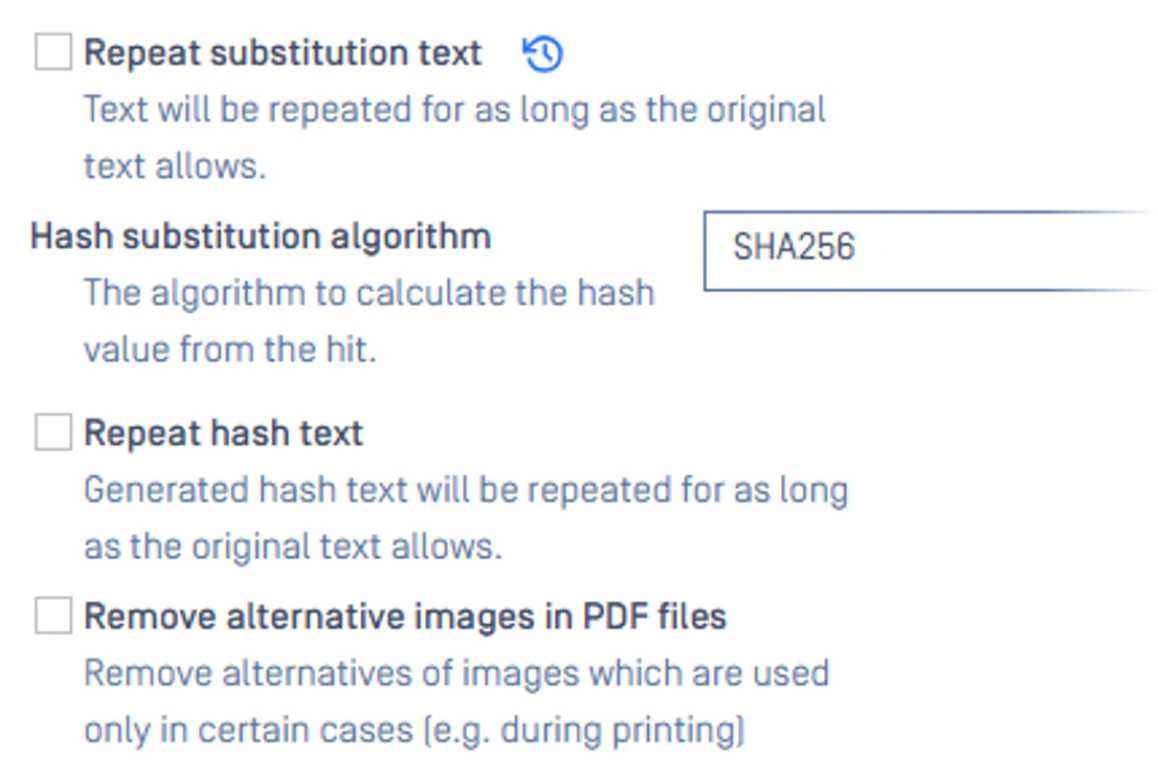
One-Way Hashing
for Sensitive Data Anonymization
Structured & Unstructured Data Detection
Metadata Removal
Hidden Data. Unseen Risk.
Enterprises handle thousands of files, emails, and data exchanges every day. Without deep inspection and policy enforcement, sensitive information can slip through unnoticed, creating serious compliance and security risks.

Hidden Sensitive Data in Complex Files
Sensitive or regulated information often resides in documents, images, or archives that pass through networks unchecked. Traditional scanners could miss these embedded risks, leading to unintentional exposure.

Lack of Policy Control
Manual or inconsistent data handling policies makes it difficult to enforce corporate and regulatory policies. Organizations risk non-compliance with frameworks such as GDPR, HIPAA or PCI DSS, leaving sensitive information exposed.
Insider Threats
Most data leaks stem from accidental sharing, misconfigured access, or other insider threats, including intentional misuse of data. Without automated detection and anonymization, employees can expose confidential information regardless of intent.
Sensitive Data Protection
Proactive DLP detects, redacts, and anonymizes sensitive data through deep inspection and automated policy enforcement, aiding compliance and control across every data exchange.
How It Works
Proactive DLP analyzes your files, detecting, classifying, and securing sensitive data before it leaves your organization or reaches external users.
Block. Redact. Anonymize.
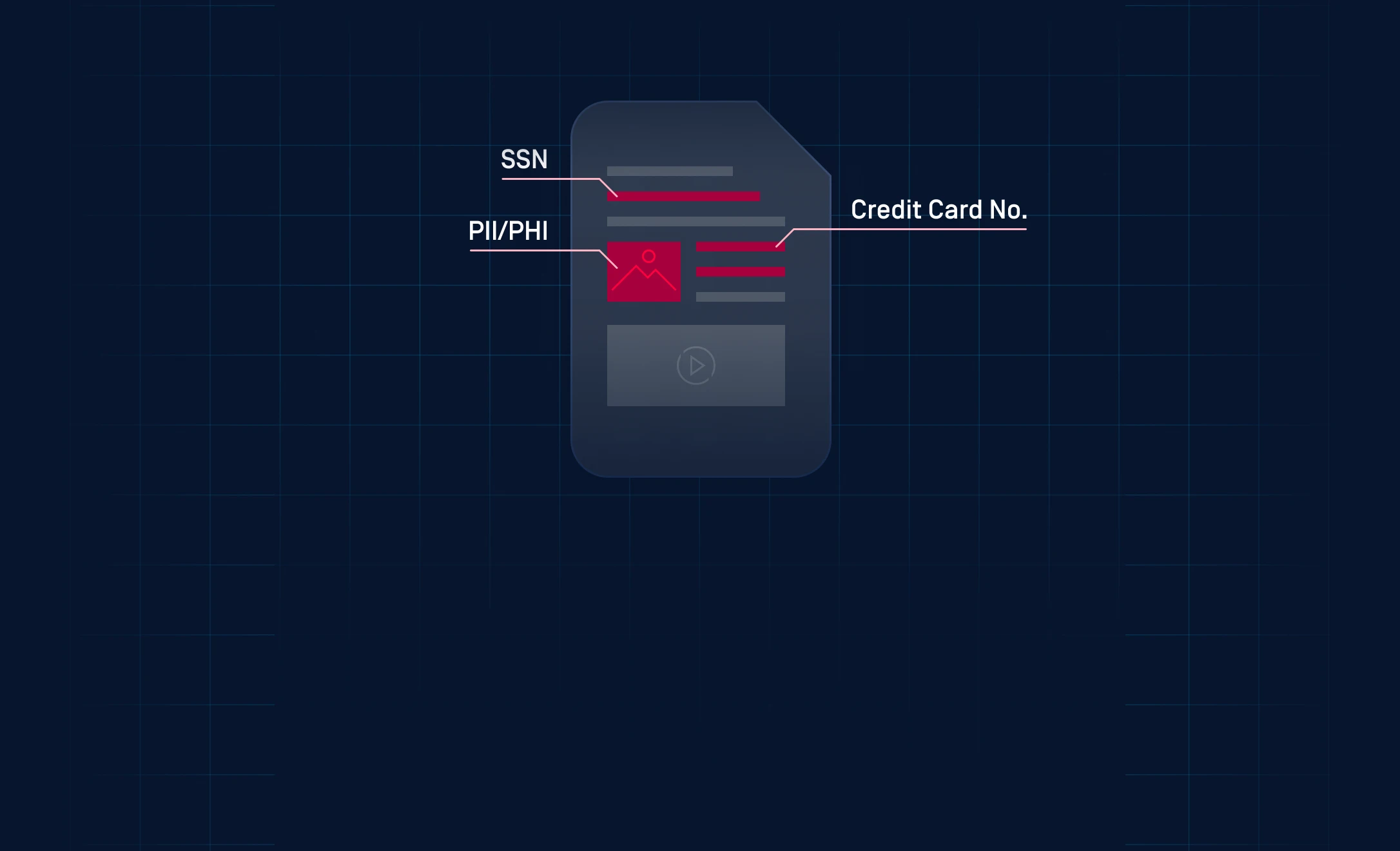
AI-Powered Sensitive Data Detection
Using OCR and NER to identify PII, PHI, credentials, financial data, secrets, and inappropriate content across 125+ file types, including text, images, and embedded documents, with high detection accuracy.
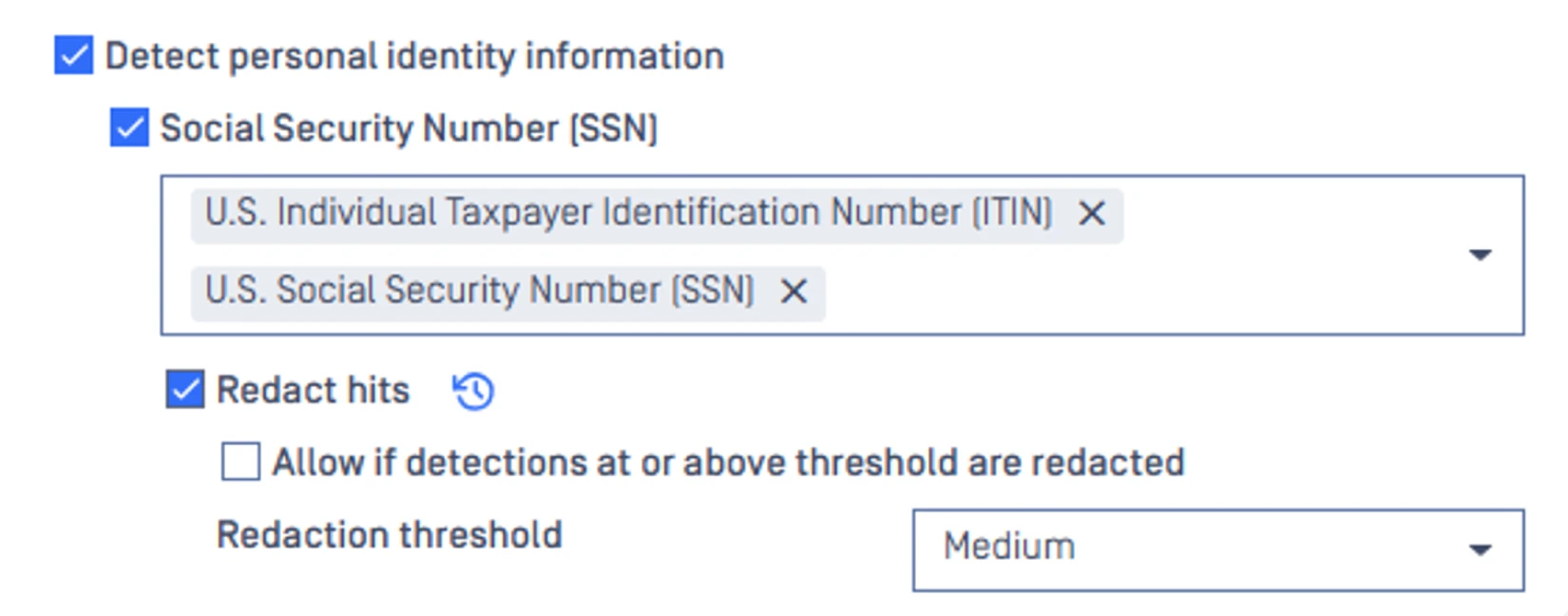
Content-Based Policy Enforcement
Automatically enforces content-based policies by blocking or allowing files based on sensitivity, applying redaction, substitution, metadata removal, tagging, or watermarking to support safe and compliant data sharing.
Regulatory Compliance Alignment
Detects and blocks regulated data types, including PII, PHI, and financial information, with customizable policies that help organizations align with PCI-DSS, HIPAA, and GDPR requirements.
Integration with Multi-Layered
Security Ecosystem
Works with OPSWAT technologies like Metascan™ Multiscanning, Deep CDR™ Technology, and Adaptive Sandbox to deliver comprehensive, defense-in-depth protection against data breaches and advanced cyber threats.
See How Proactive DLP Protects Your Data
Understand how Proactive DLP safeguards your file exchanges, detecting risks and preventing data loss before it happens.
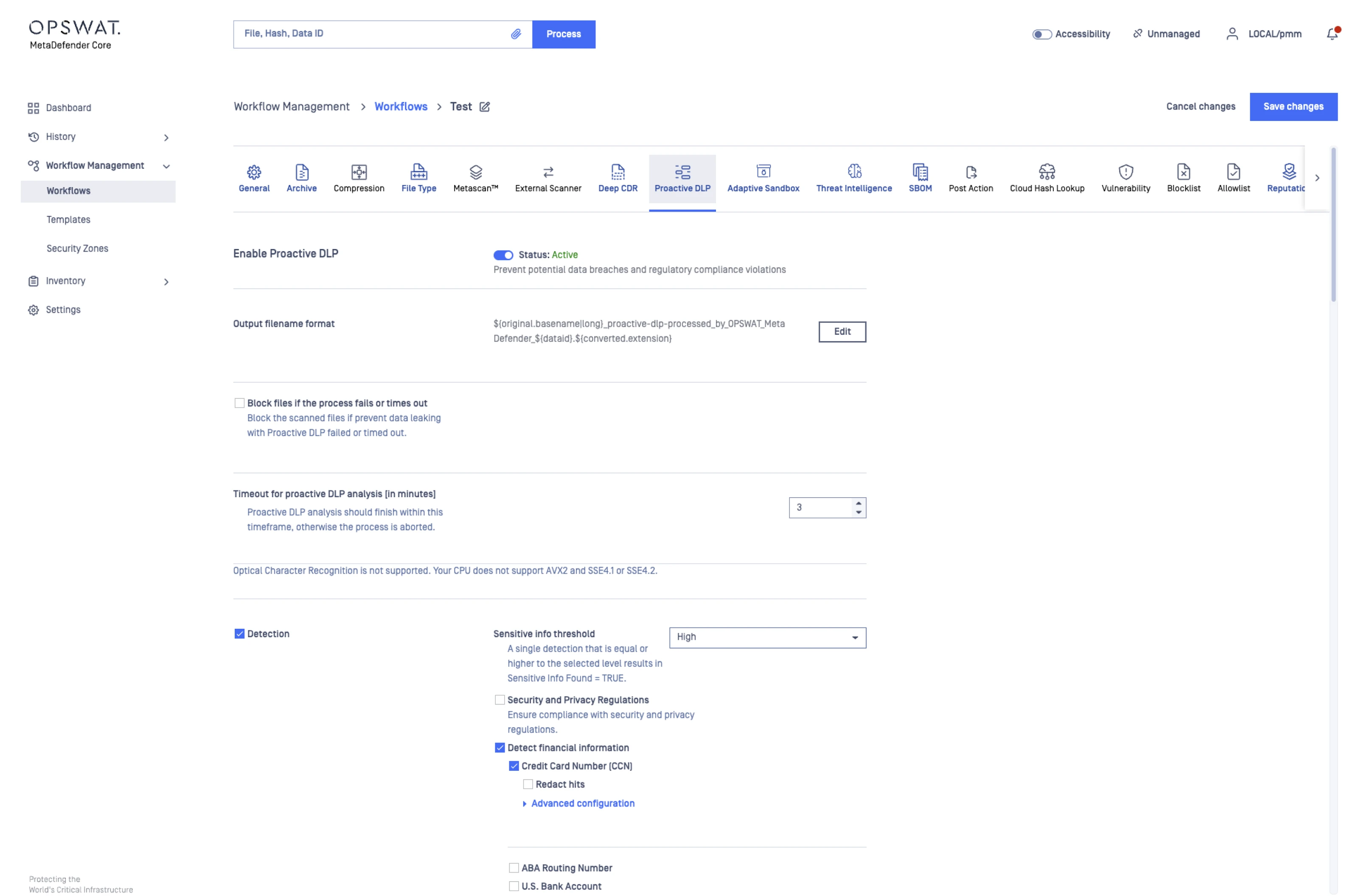
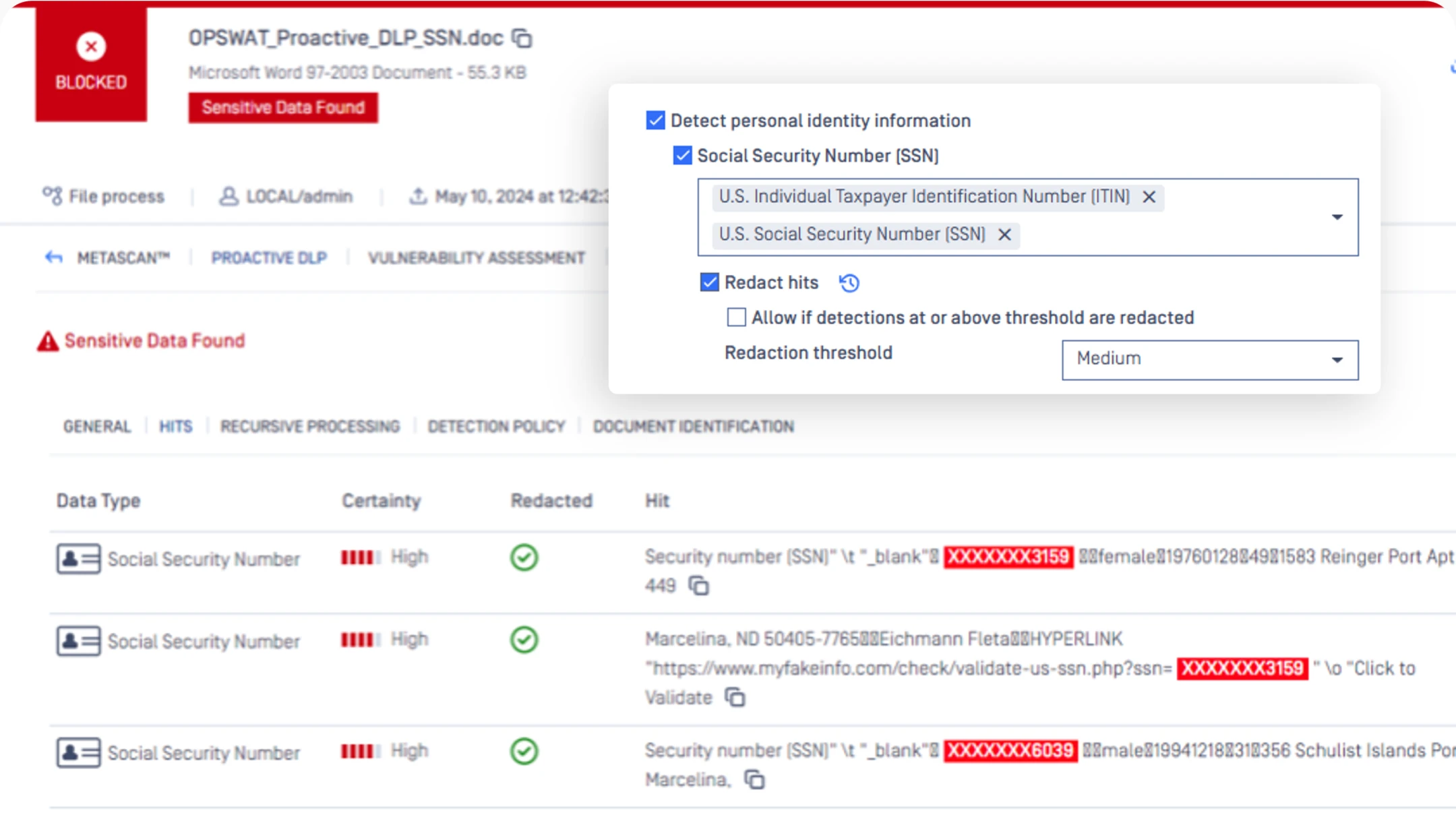
Enables AI-powered data protection to detect and safeguard sensitive data across various file types.
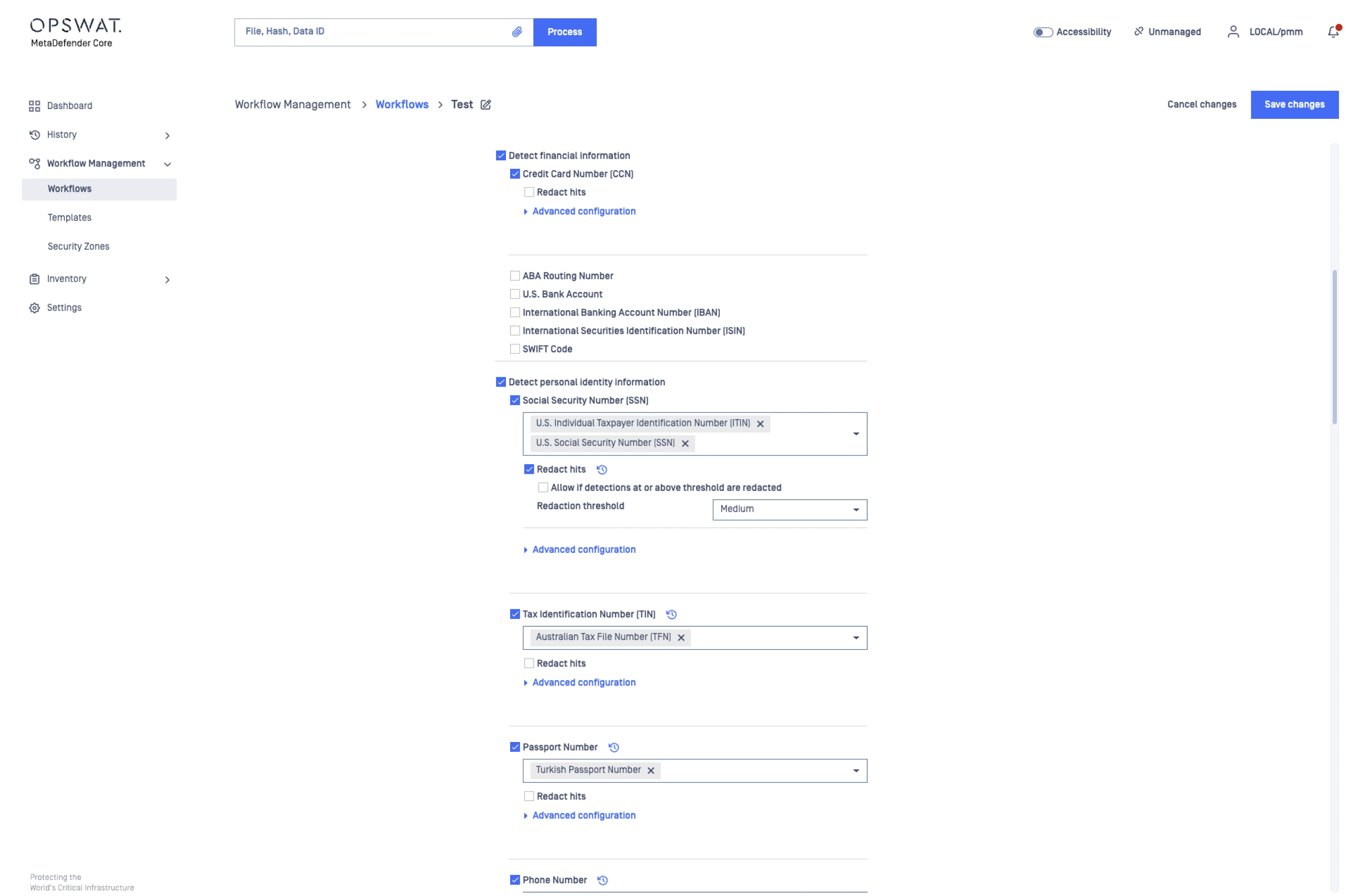
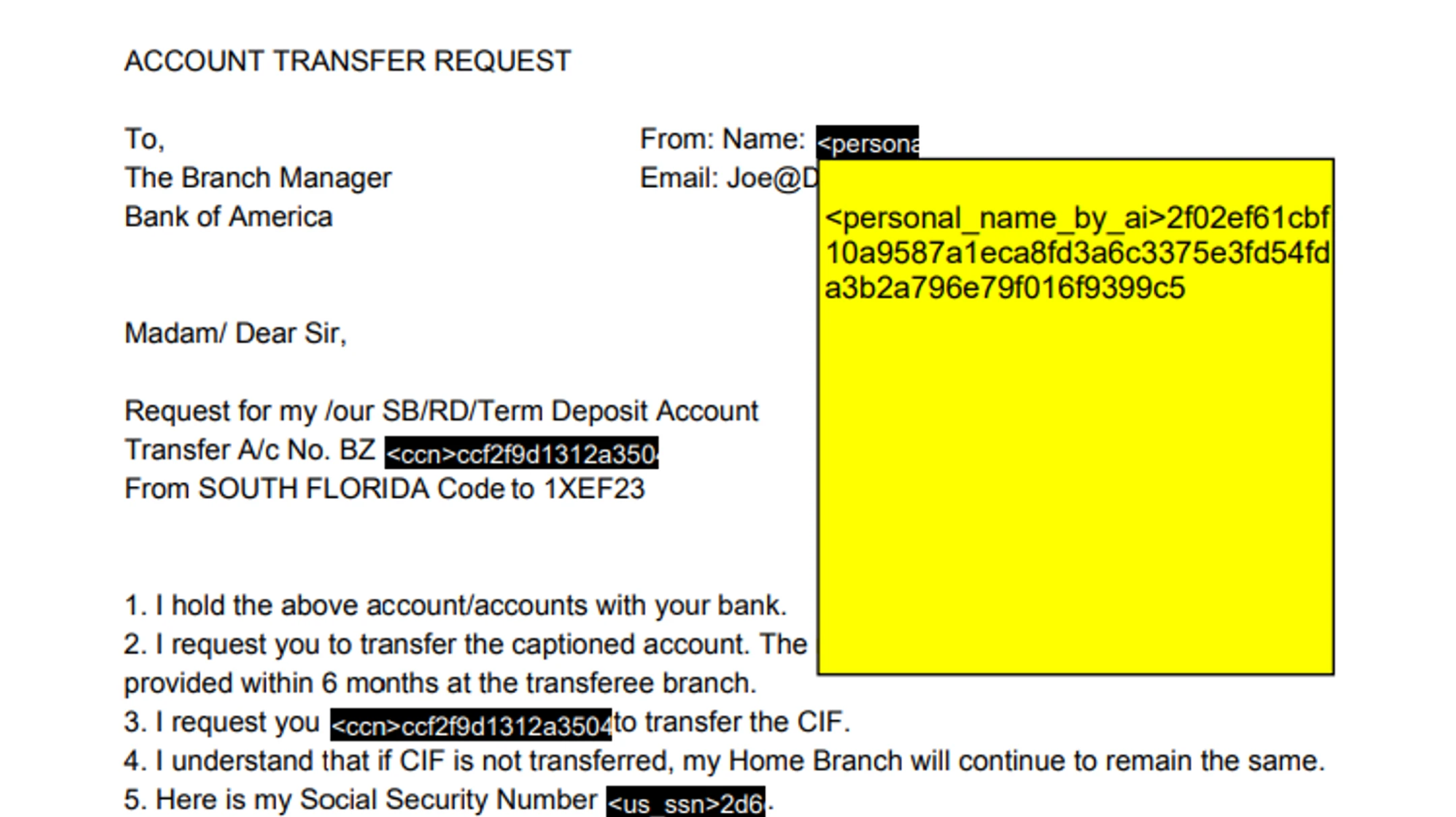
Easily redact sensitive data including financial info, personal identity, network and device info, secrets, regex, and metadata.
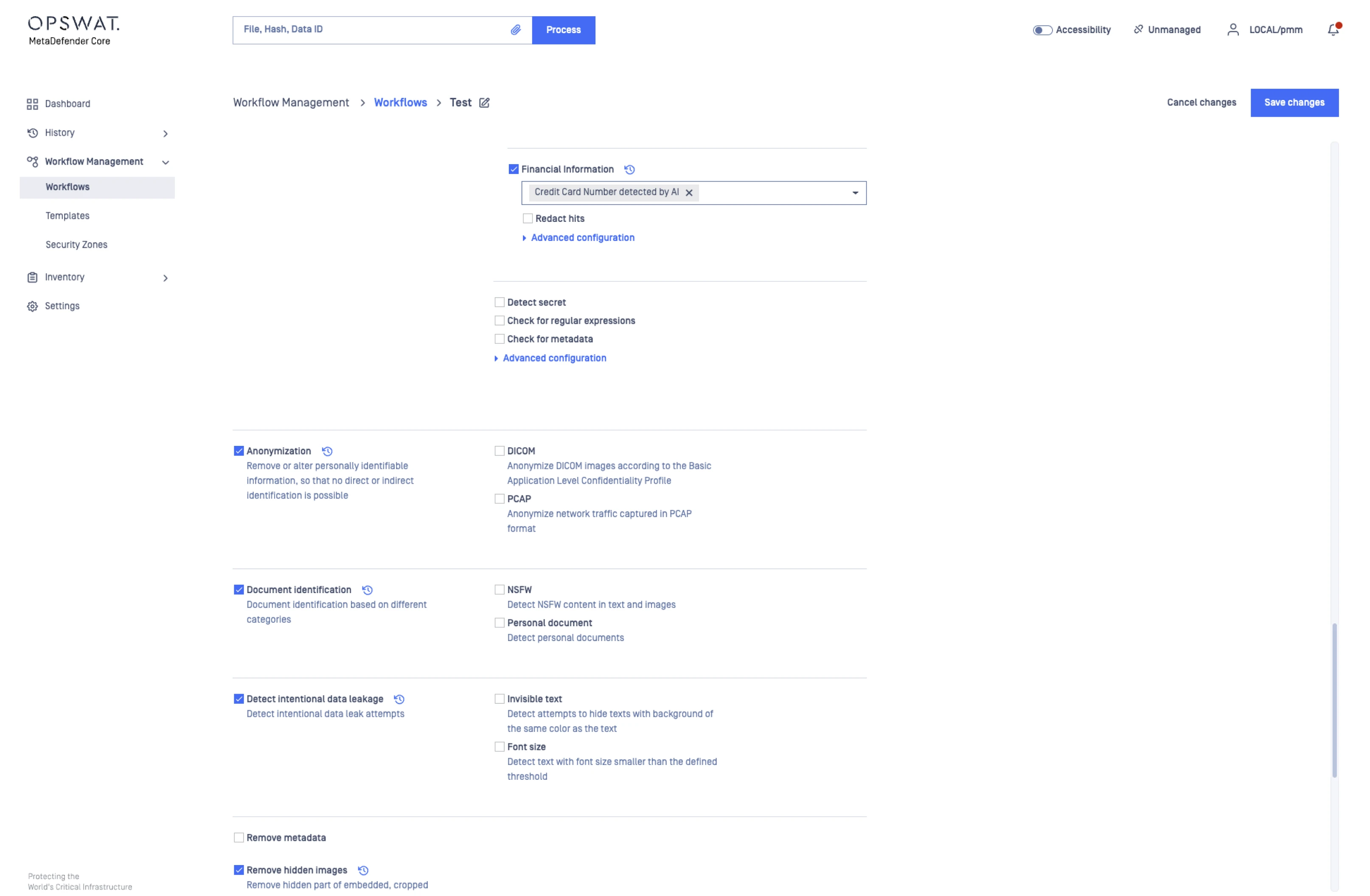
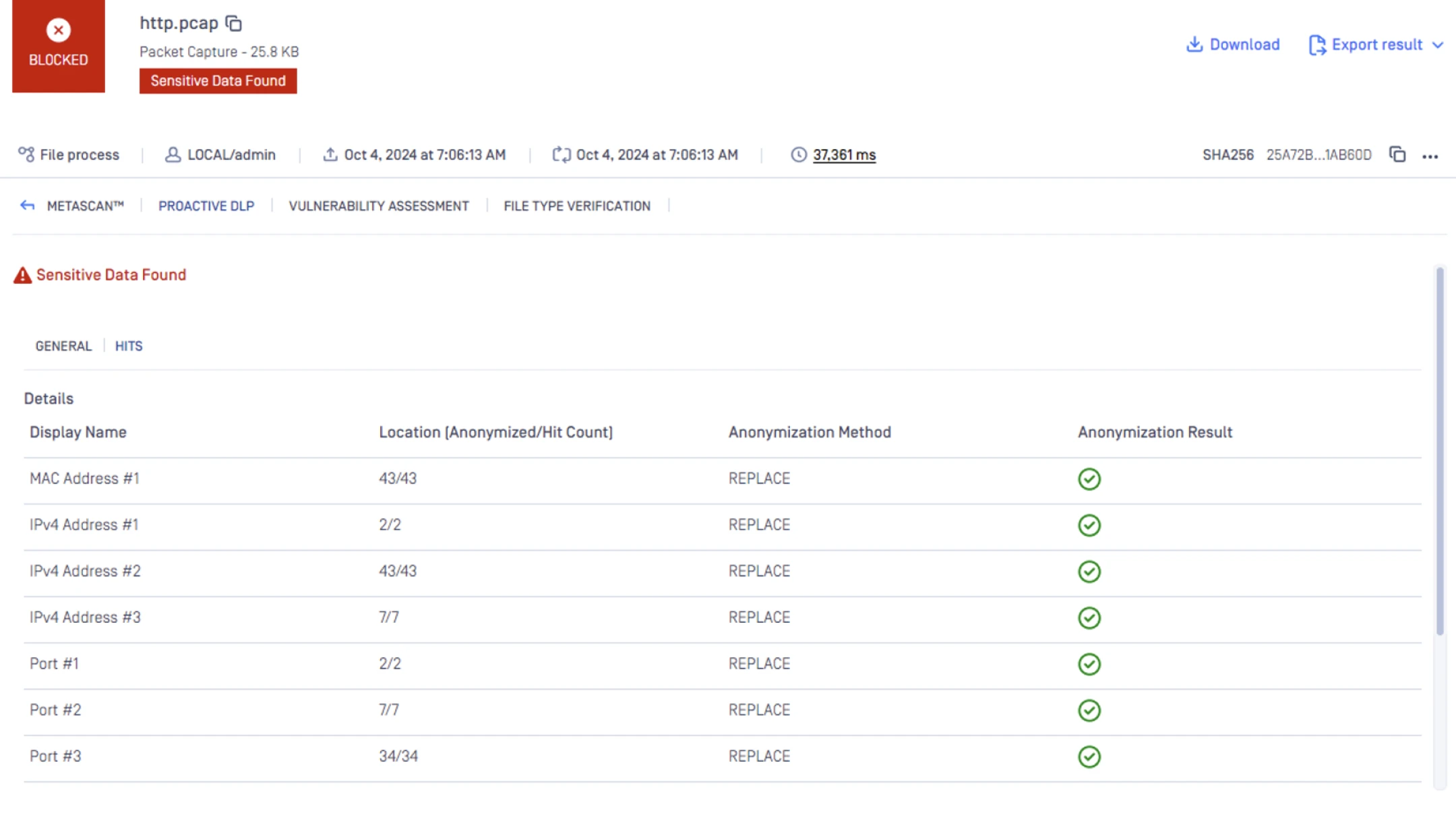
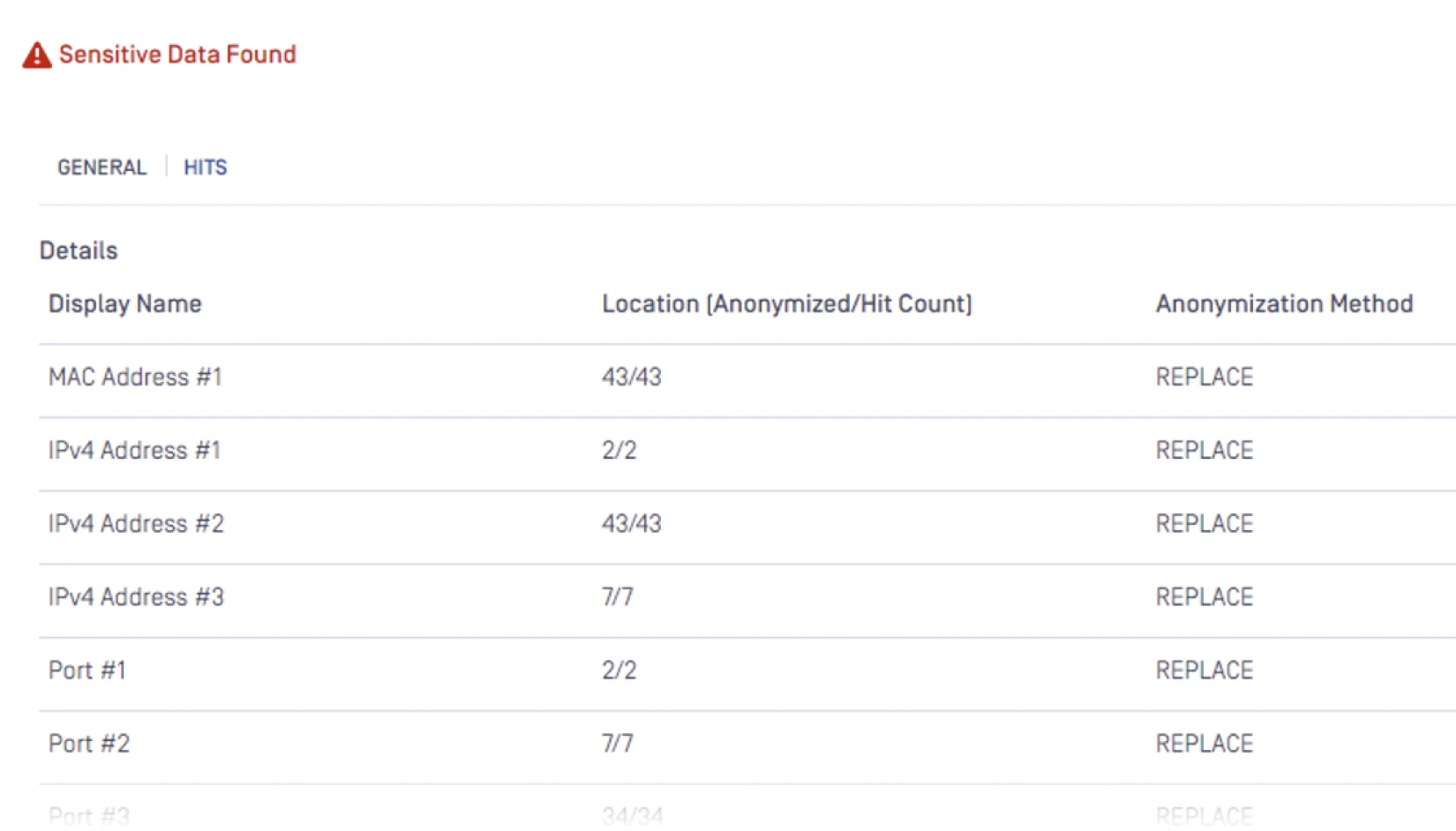
Support anonymization across diverse file types such as DICOM and PCAP files to prevent intentional or accidental data leaks.
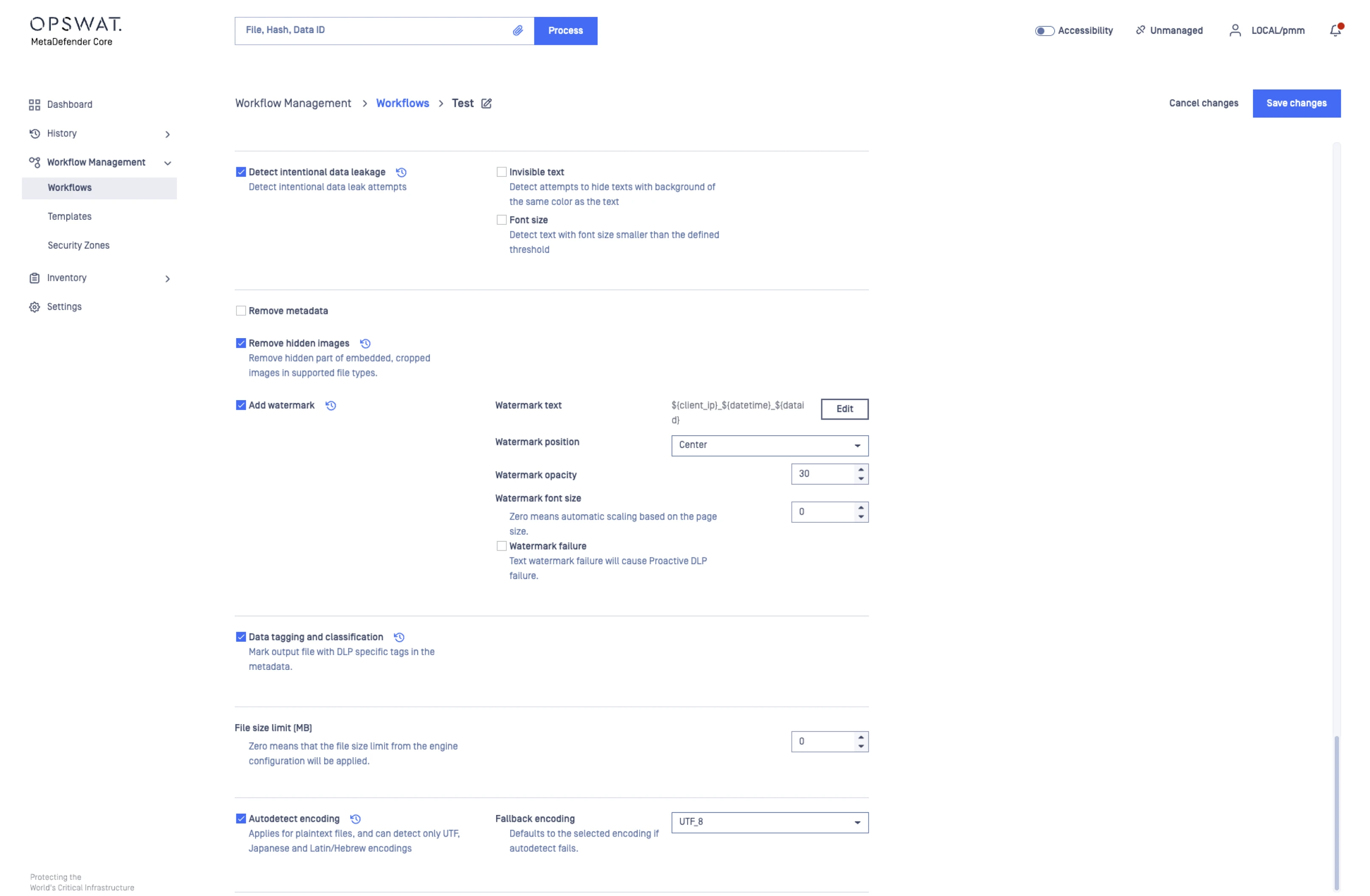
Applies tagging and classification to output files, removes embedded or cropped images, and automatically detects varied encodings.
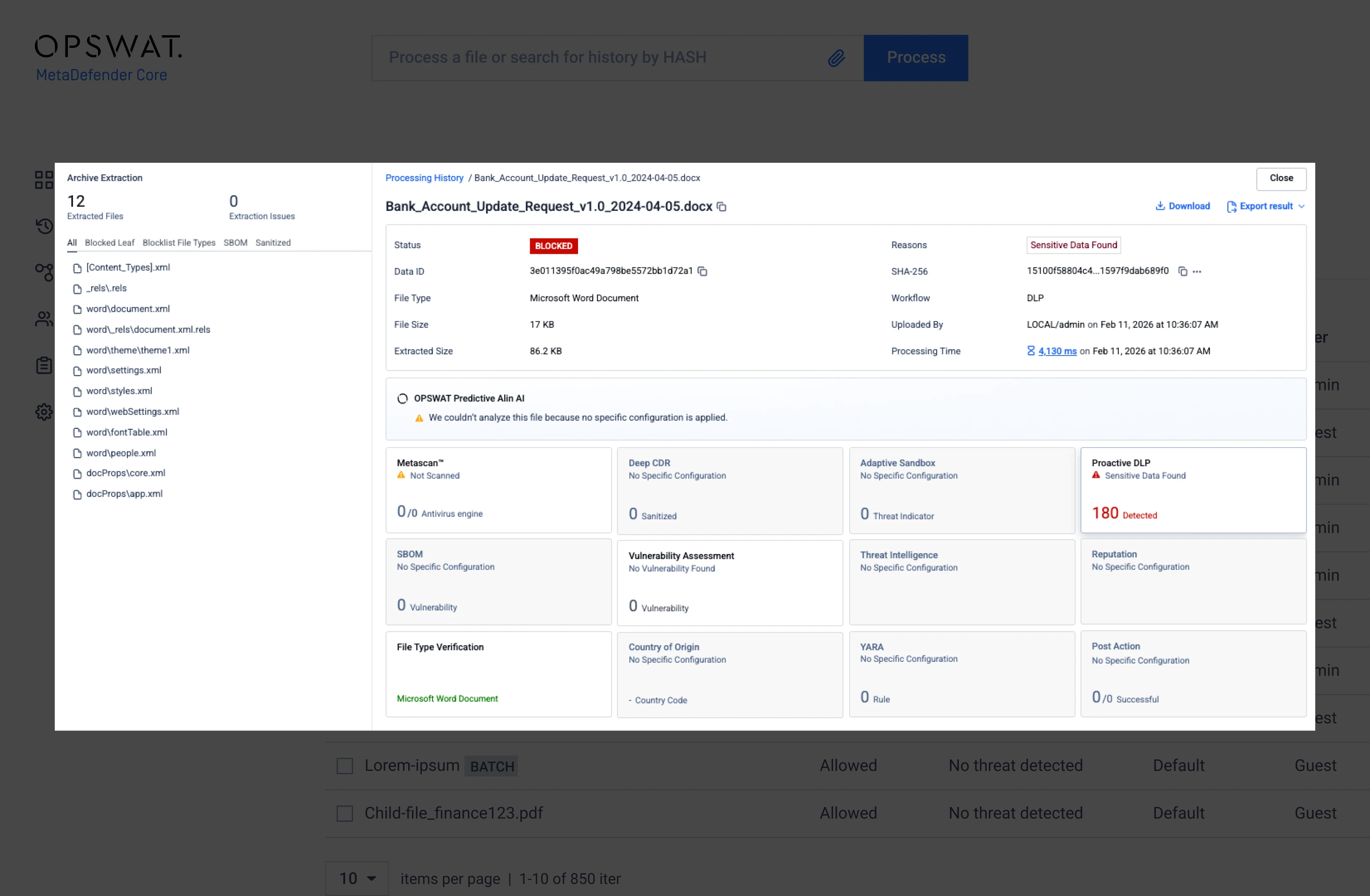
Automatically identifies and categorizes sensitive data, assigning clear verdicts such as Infected or Suspicious for faster response.
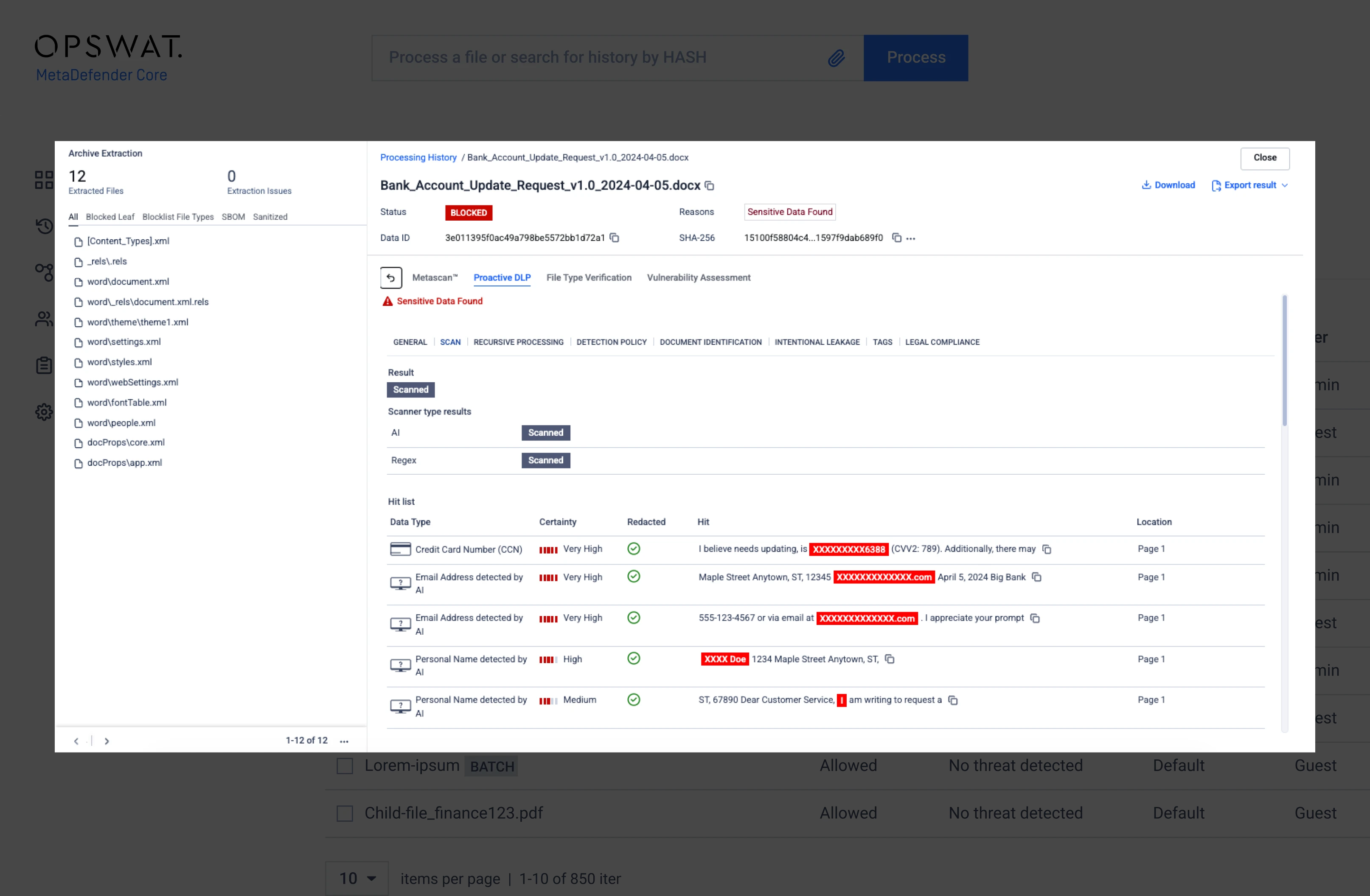
Delivers AI-powered scan results that evaluate predefined sensitive data types and assign certainty levels to identify highly critical information.
Comprehensive Protection
for Every Sensitive Data Type
Proactive DLP identifies, classifies, redacts, and anonymizes sensitive information across structured and unstructured content, preventing leaks and supporting compliance at scale.
PI (Personal Information)
Personal Information includes names, addresses, contact details, and other identifiers frequently shared in everyday business workflows. Because this data is often scattered across documents and communications, it becomes a common point of accidental exposure. Proactive DLP scans files in real time to flag PI, applying redaction or anonymization to ensure that non-regulated but sensitive personal data cannot be leaked internally or externally.
PII (Personally Identifiable Information)
PII includes Social Security numbers, passport and driver’s license details, birthdates, and other identity-specific data that attackers can exploit for fraud or impersonation. Its high sensitivity makes it a top target during breaches. Proactive DLP detects PII patterns across 125+ file types, redacts or masks the information, and enforces policies that prevent employees from sharing regulated data, supporting GDPR, NIST, PCI-DSS, and other compliance frameworks.
PHI (Protected Health Information)
PHI covers medical records, lab reports, insurance details, DICOM files, and any health-related identifiers regulated under HIPAA. Because PHI is highly valuable for identity fraud and medical billing scams, exposure can lead to severe financial and legal penalties. Proactive DLP identifies PHI across text and images, anonymizes sensitive fields, and ensures healthcare organizations maintain HIPAA-aligned data handling across internal systems and external data exchanges.
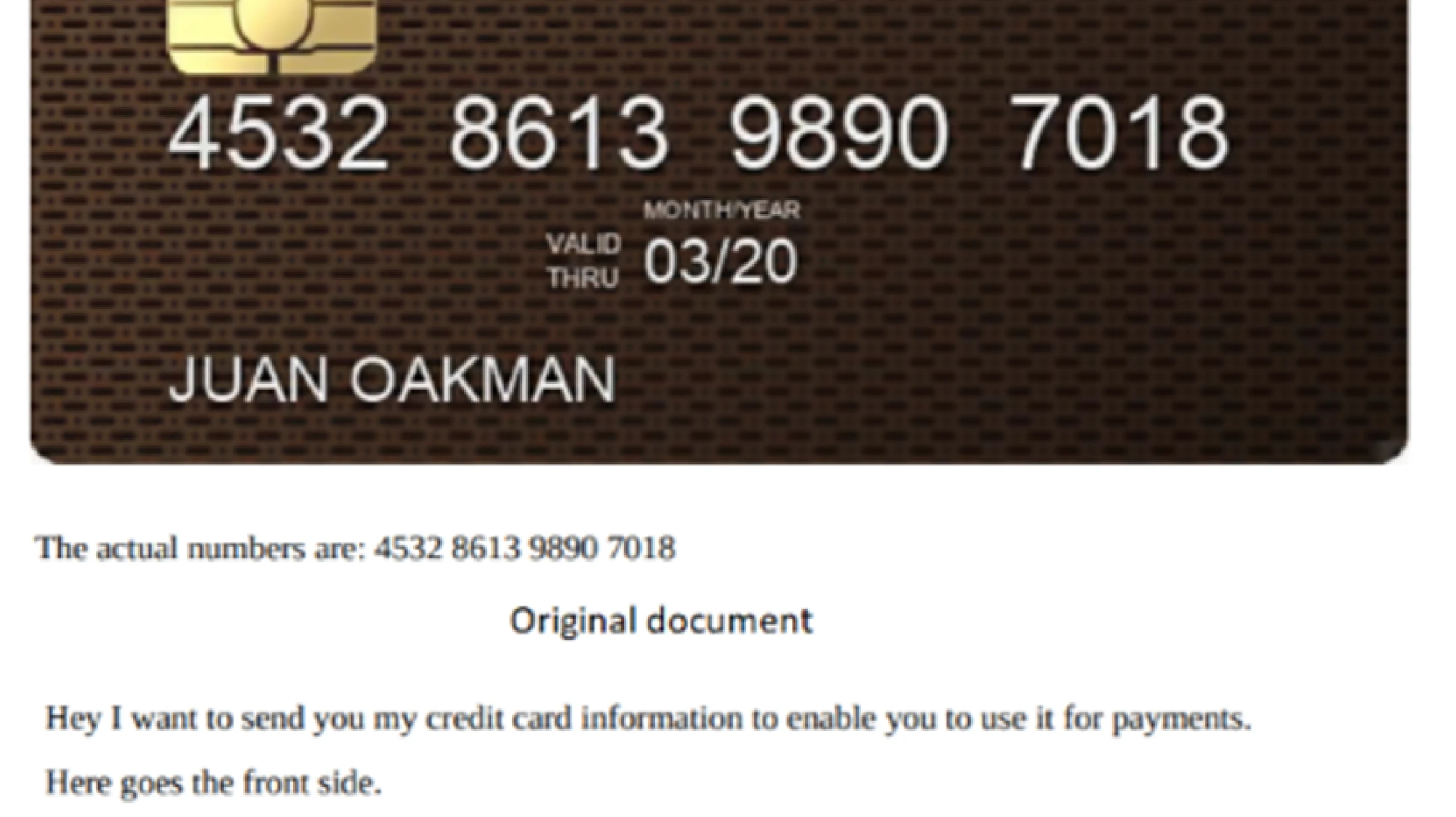
Financial Data
Financial data includes credit card numbers, bank account details, transaction records, payroll information, and tax documents. These assets are frequently targeted for fraud, insider abuse, and exploitation. Proactive DLP scans documents, spreadsheets, PDFs, and images for financial markers using pattern and AI-based detection. It can redact sensitive values, enforce PCI-aligned policies, and block unauthorized sharing, protecting organizations from financial loss and compliance risks.
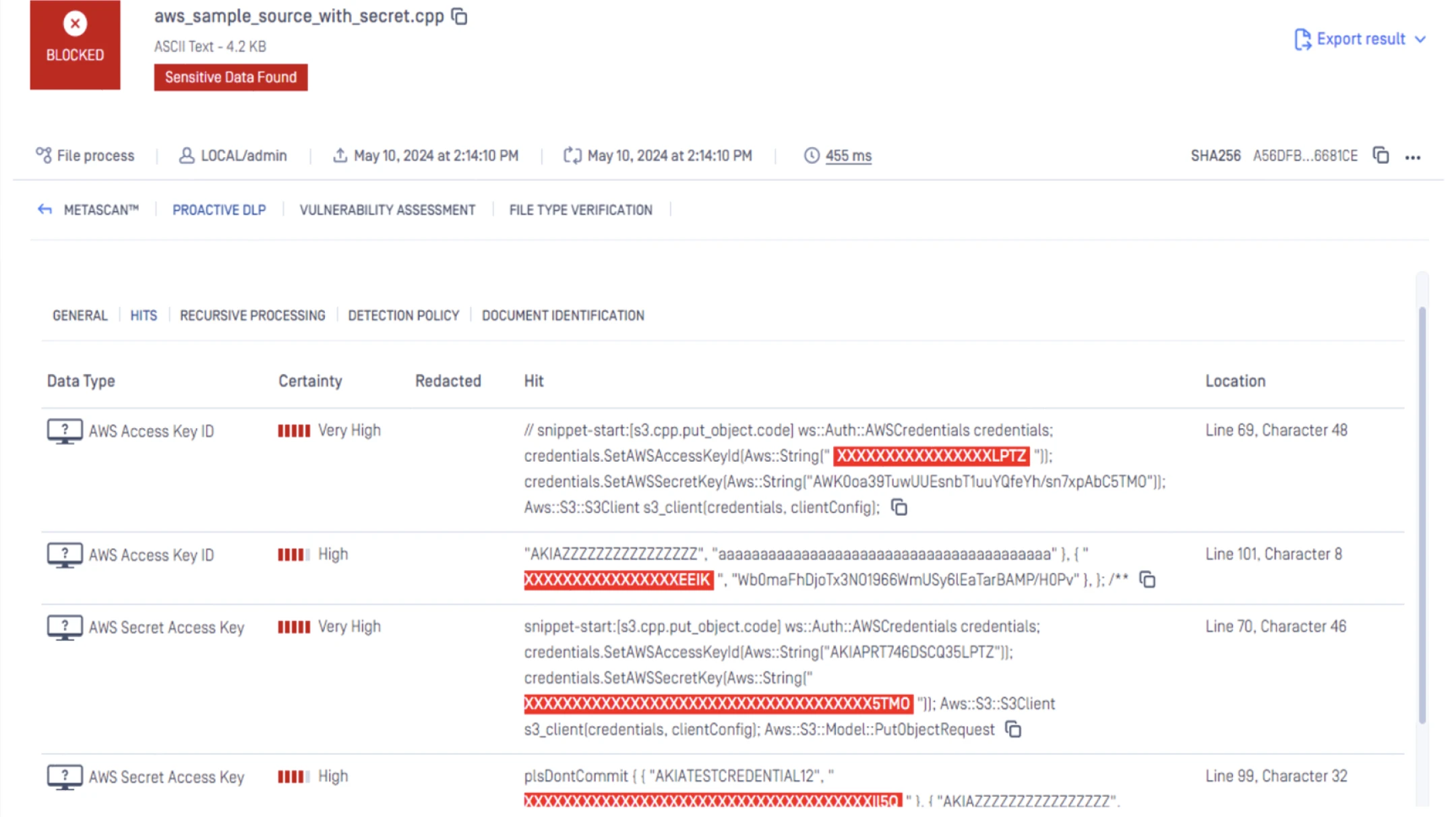
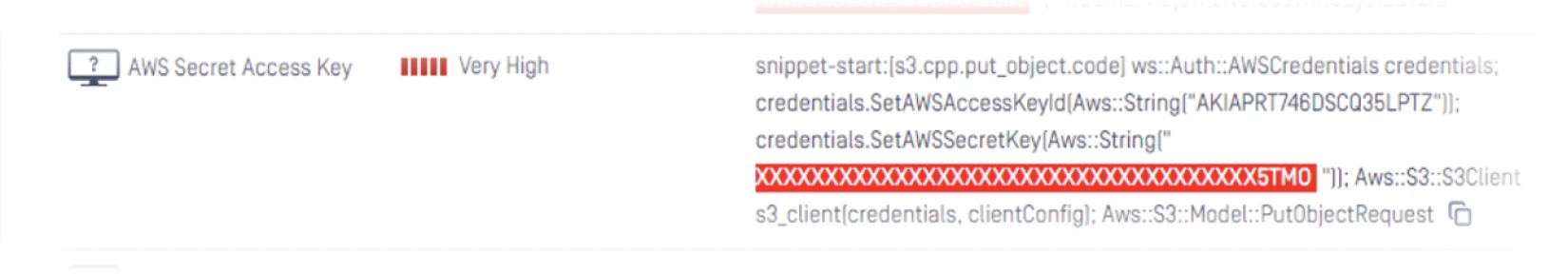
Secrets (Credentials & Keys)
Secrets include API keys, passwords, authentication tokens, private keys, and configuration strings commonly embedded in code files, documents, and emails. When leaked, these can provide direct system access to attackers. Proactive DLP detects secrets using advanced pattern matching and machine learning, automatically redacting or blocking files that contain exposed credentials, helping prevent unauthorized access, privilege escalation, and supply chain compromise.
- MetaDefender Platform
- MetaDefender Platform
- MetaDefender Platform
- MetaDefender Platform
- MetaDefender Platform
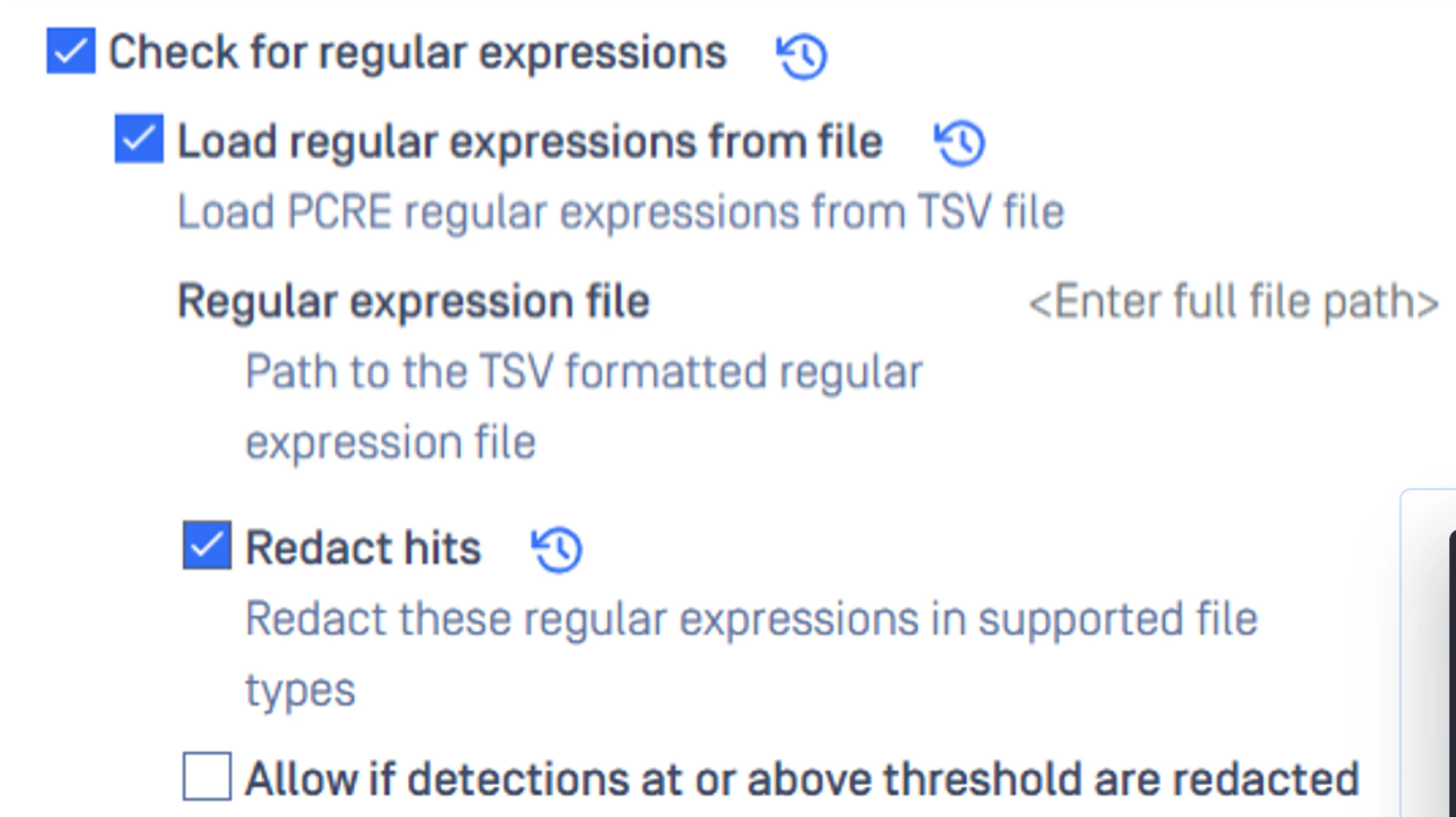
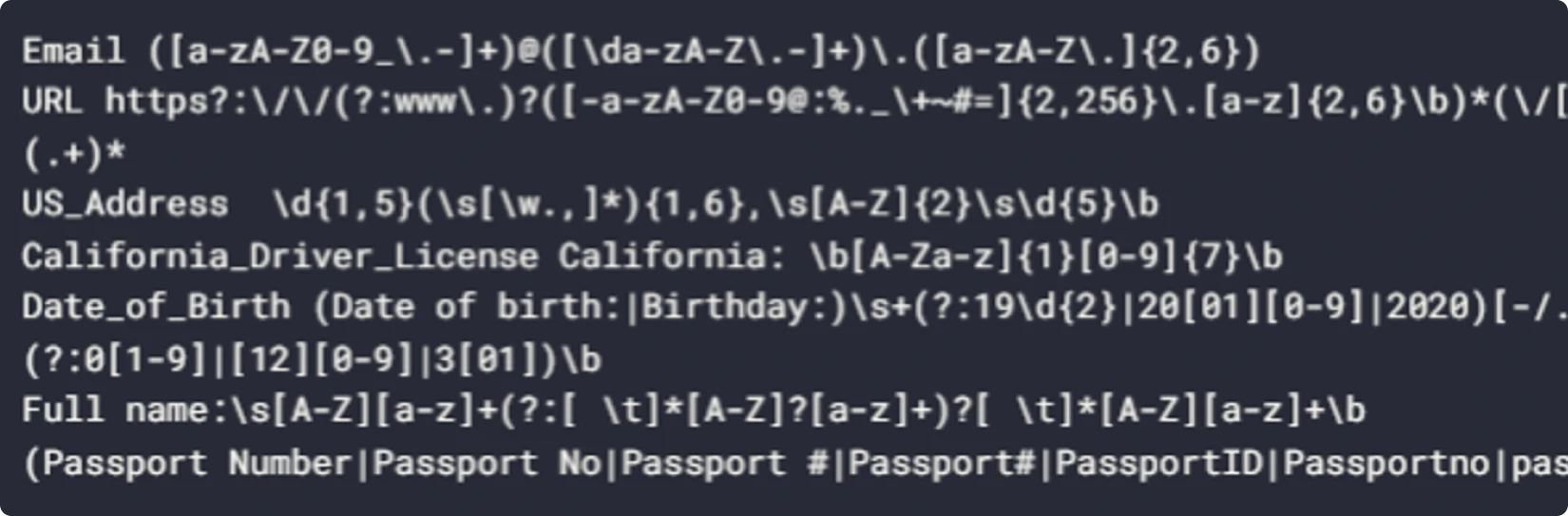
RegEx-Based Pattern Matches
RegEx-based detection covers any custom sensitive pattern, such as customer IDs, internal project codes, contract numbers, proprietary identifiers, or industry-specific formats. These values often leak unintentionally through shared documents or reports. Proactive DLP enforces granular pattern rules, applying redaction or blocking based on organizational policies. This flexibility allows enterprises to secure unique business data that traditional DLP solutions often overlook.
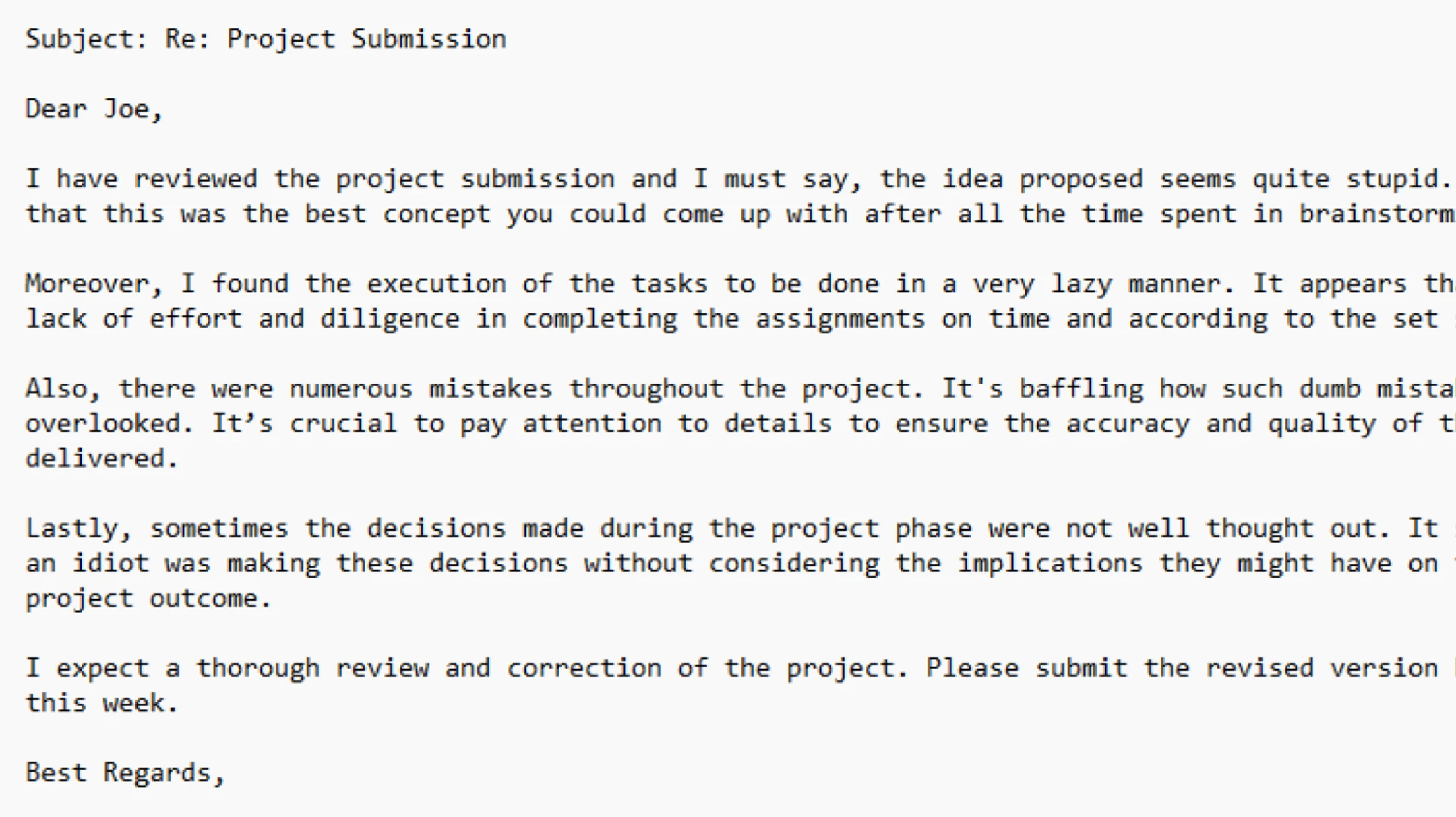
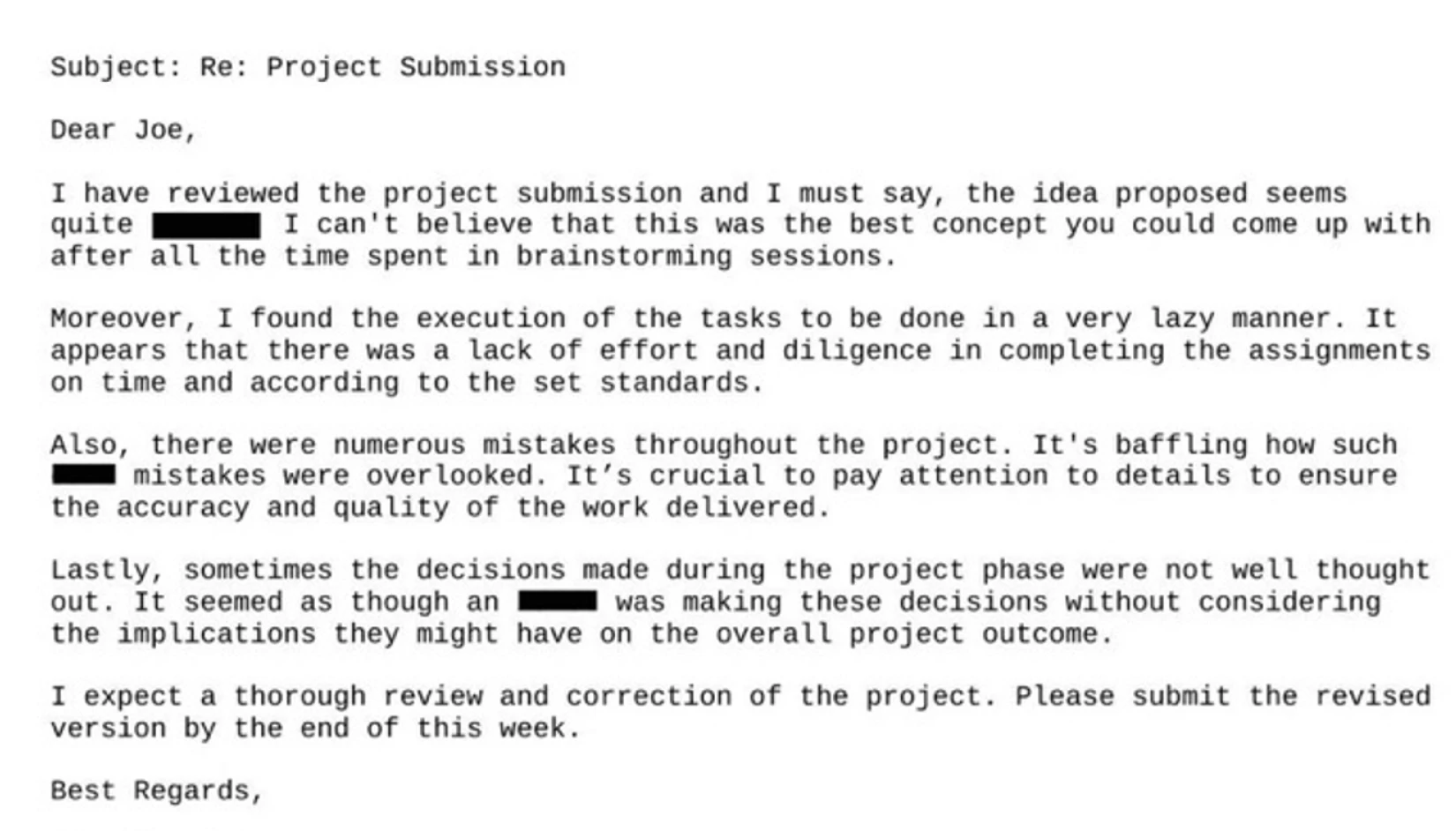
NSFW Content & Images
NSFW content includes inappropriate, offensive, sexual, or harmful imagery and text that can contribute to hostile workplace environments or legal liability. Such content may appear deliberately, accidentally, or embedded within user-uploaded files. Proactive DLP uses AI-based vision and language models to detect NSFW content across photos, screenshots, documents, and archives, flagging or blocking materials to maintain compliance, corporate standards, and professional integrity.
Network & Device Information
Network and device identifiers (such as IP addresses, MAC addresses, hostnames, system logs, and PCAP captures) can reveal infrastructure layouts or internal configurations. Exposure of these details enables reconnaissance and targeted attacks. Proactive DLP identifies network metadata and device information across structured logs and complex file types, including PCAP and CSV files, then redacts or anonymizes sensitive values to prevent external leakage of operational insights.
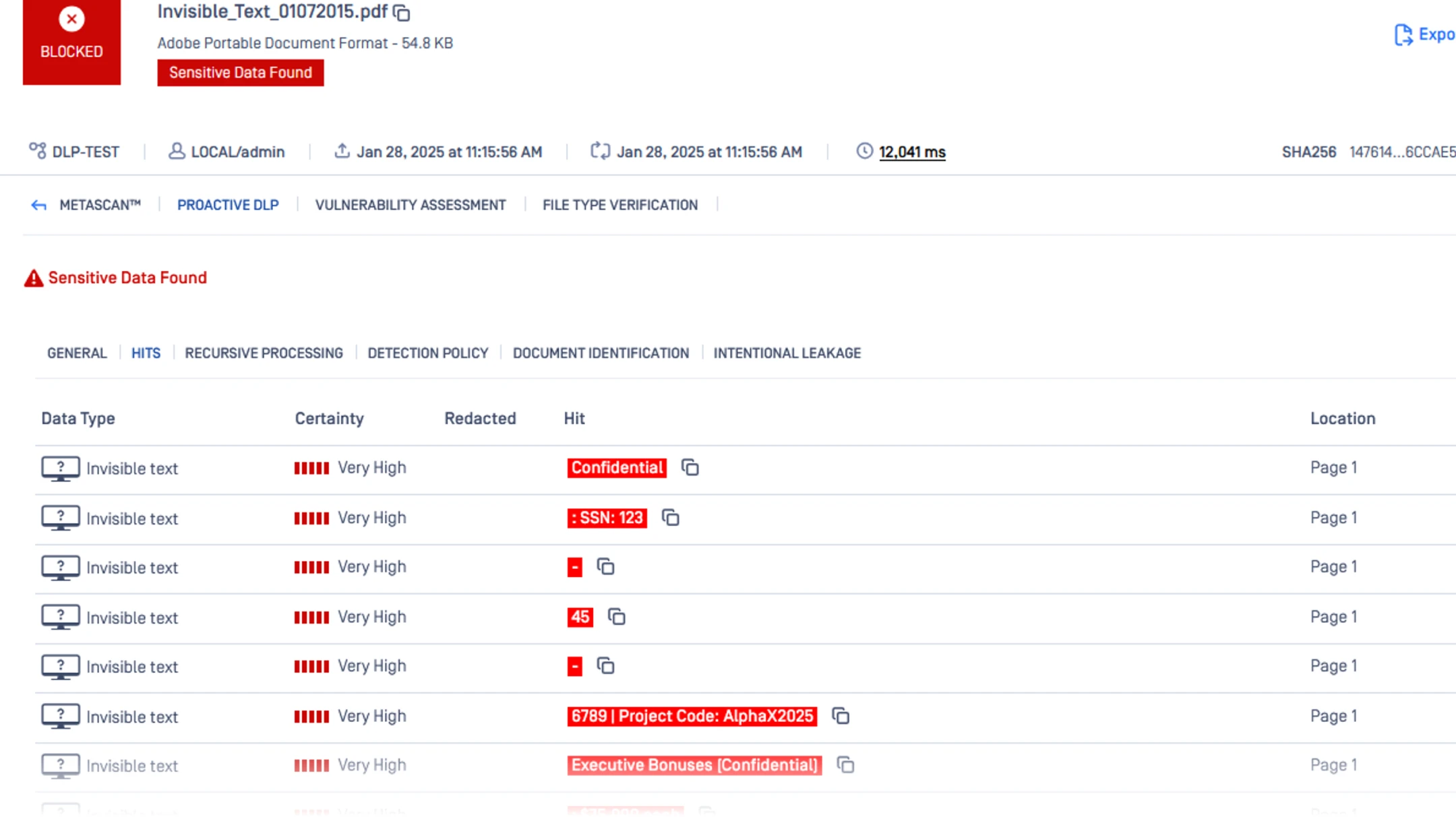
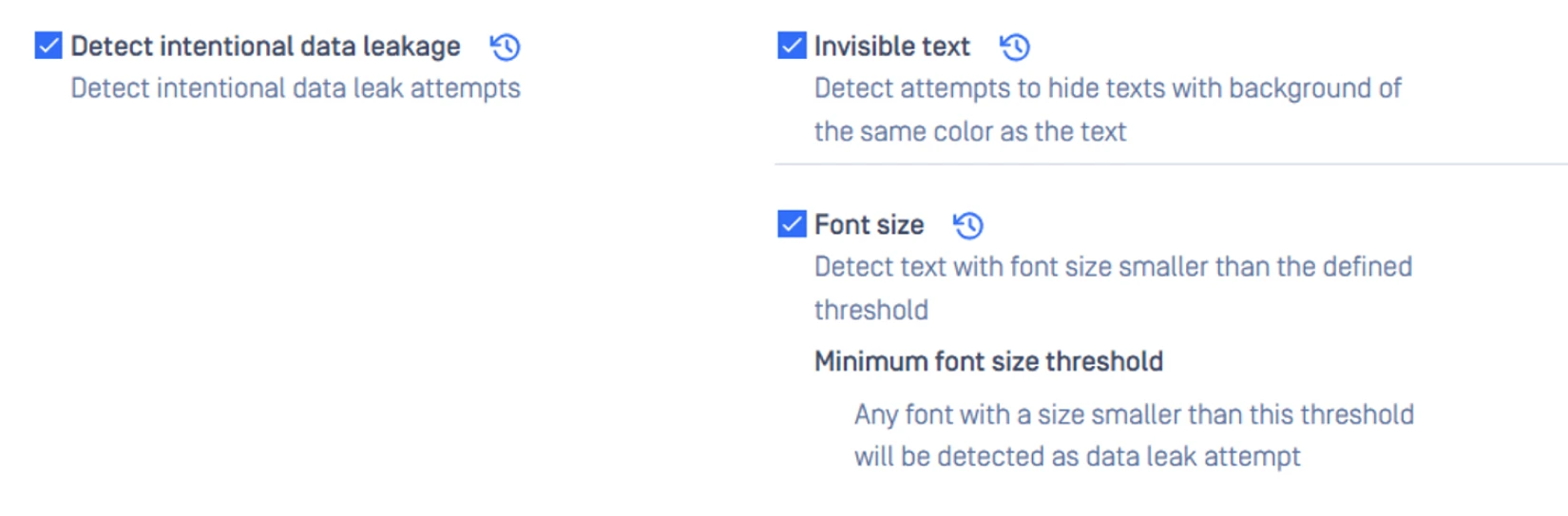
Intentional Data Leak Indicators
Intentional data leaks may involve deliberate sharing of confidential files, exfiltration attempts using disguised content, or manipulation of documents to bypass security controls. These high-risk scenarios can cause severe damage if not intercepted. Proactive DLP analyzes behavior, file content, and policy violations to identify suspicious patterns, enforce automated redaction or blocking, and stop malicious or policy-breaking file transfers before data leaves the organization
- MetaDefender Platform
- MetaDefender Platform
- MetaDefender Platform
- MetaDefender Platform
Deploy Anywhere, Integrate Everywhere

On-Premises
Maintain complete control over policies, engines, and performance within your own environment.

Air-Gapped
Enforce DLP policies securely in fully isolated environments without external network exposure.

Cloud
Deliver scalable protection with continuous availability and minimal operational overhead.