Secure, Frictionless File Sharing
Share files and collaborate with confidence. OPSWAT solutions ensure uninhibited sharing of critical files and digital resources within your organization and with external partners, without compromising speed or performance.
File Sharing Security Risks
Access Control
Collaborating with external partners complicates permissions management, leading to risks of unauthorized access.
Policy Enforcement
Organizations struggle to implement consistent file security policies across multi-device, remote workforces.
Integration Limitations
Limited integration with existing security tools disrupts workflow automation and complicates security management.
Scaleable Security
Security solutions often fail to perform effectively at scale in cloud environments
Lack of Remediation
Without automated responses for detected malware or sensitive data, potential risks remain unaddressed.
The OPSWAT Solution
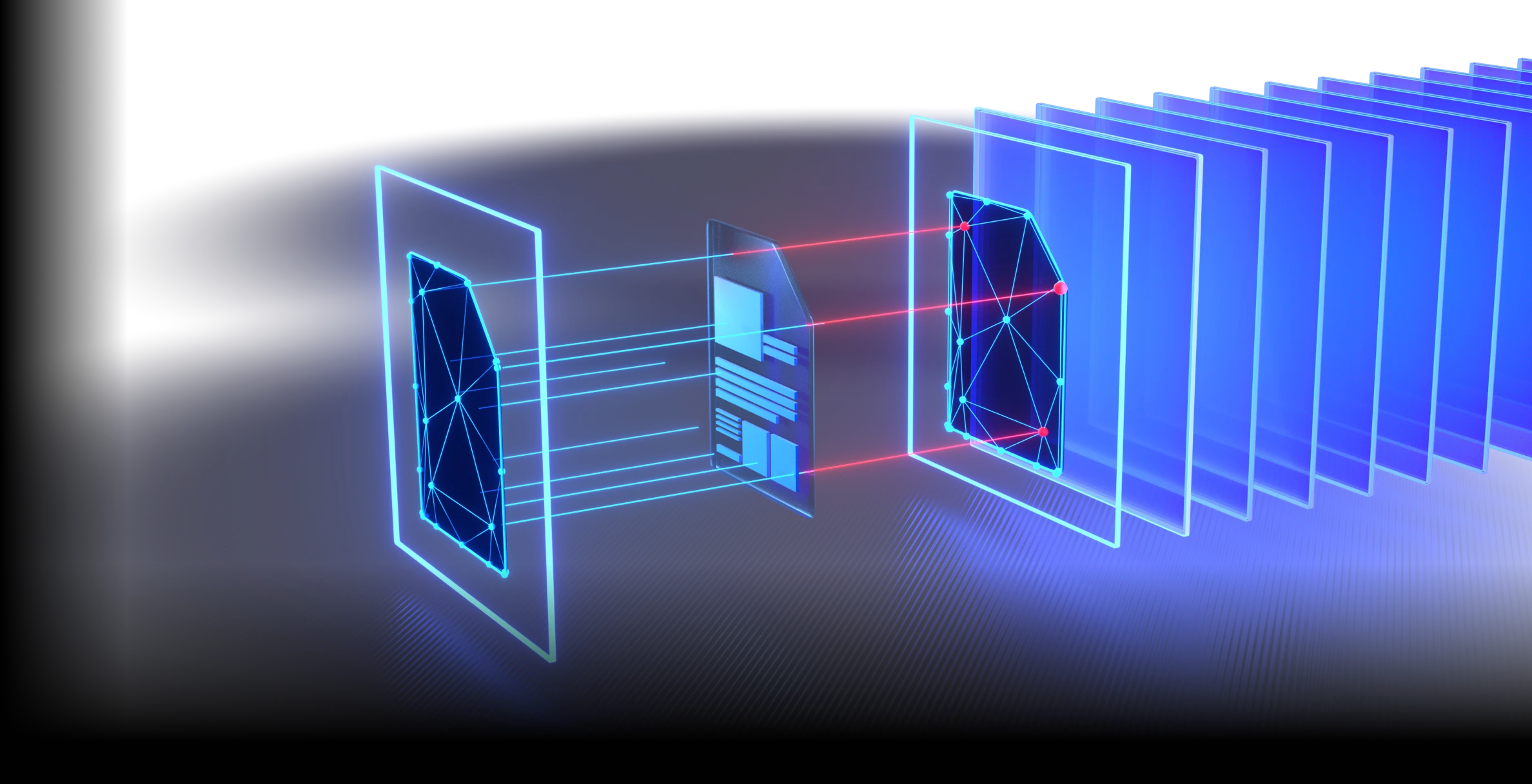
Stop Threats That Others Miss
- Supports 200+ file formats
- Recursively sanitize multi-level nested archives
- Regenerate safe and usable files
More Engines Are Better Than One
- Detect nearly 100% of malware
- Scan simultaneously with 30+ leading AV engines
Detect Evasive Malware with Advanced Emulation-Based Sandboxing
- Analyze files in a high-speed
- Anti-evasion sandbox engine extracts IOCs
- Identify zero-day threats
- Enable deep malware classification via API or local integration
Prevent Sensitive Data Loss
- Utilize AI-powered models to locate and classify unstructured text into predefined categories
- Automatically redact identified sensitive information like PII, PHI, PCI in 125+ file types
- Support for Optical Character Recognition (OCR) in images
Detect Application Vulnerabilities Before They Are Installed
- Check software for known vulnerabilities before installation
- Scan systems for known vulnerabilities when devices are at rest
- Quickly examine running applications and their libraries for vulnerabilities
Enhance Detection with Real-Time Threat Intelligence
- Correlate global IOCs, IPs, URLs, & file reputation across 50B+ artifacts
- Stop emerging threats faster
- Enrich downstream analysis
Seamless Deployments
Deploy via an extensible REST API and a native connector-enabled platform that seamlessly integrates with your existing file upload web application and security infrastructure.
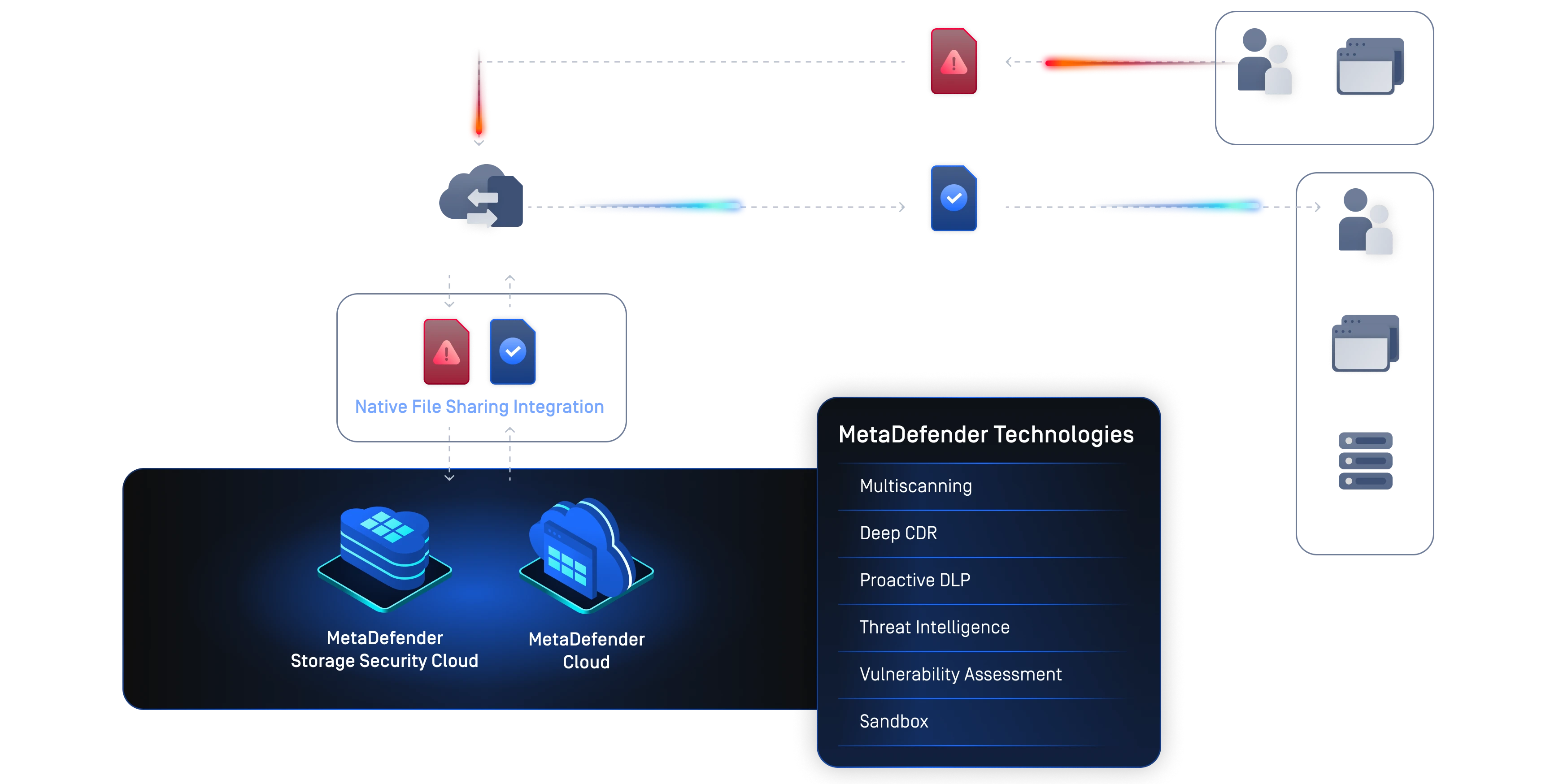



Configuring MetaDefender for Secure File Sharing
MetaDefender Workflow Engine allows security professionals to customize security policies, file processing, and administrative options to meet specific security requirements and service-level performance commitments. Organizations implementing security measures for shared assets should configure file security policies that meet the needs of each specific workflow.
Each workflow should consider the balance between security and user experience and should take into consideration the source of the file.
The following are parameters to consider when building a file sharing workflow:
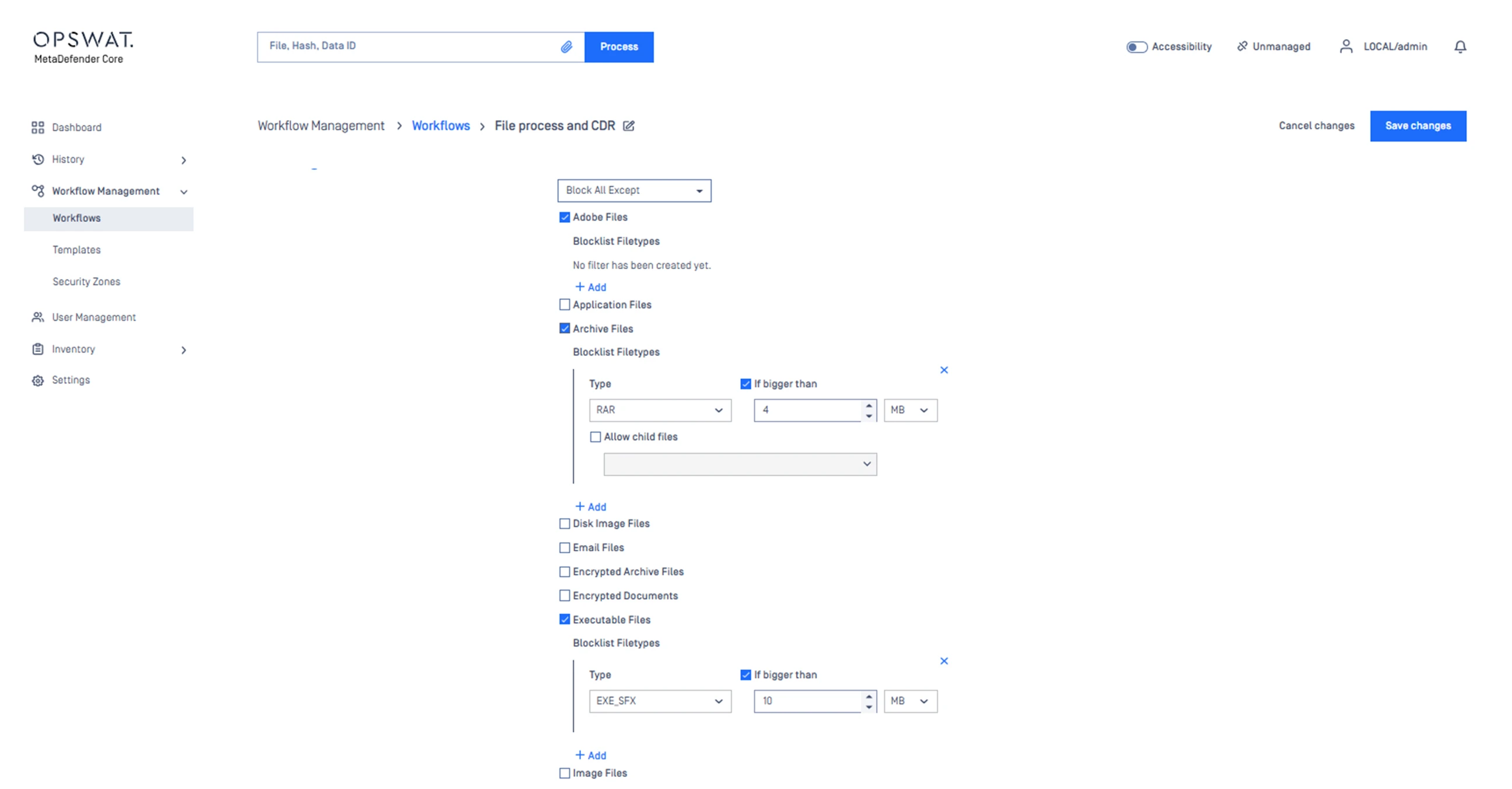
Each workflow should define the type of files accepted, including productivity, media, system, and archives, and designate the maximum file size allowed.
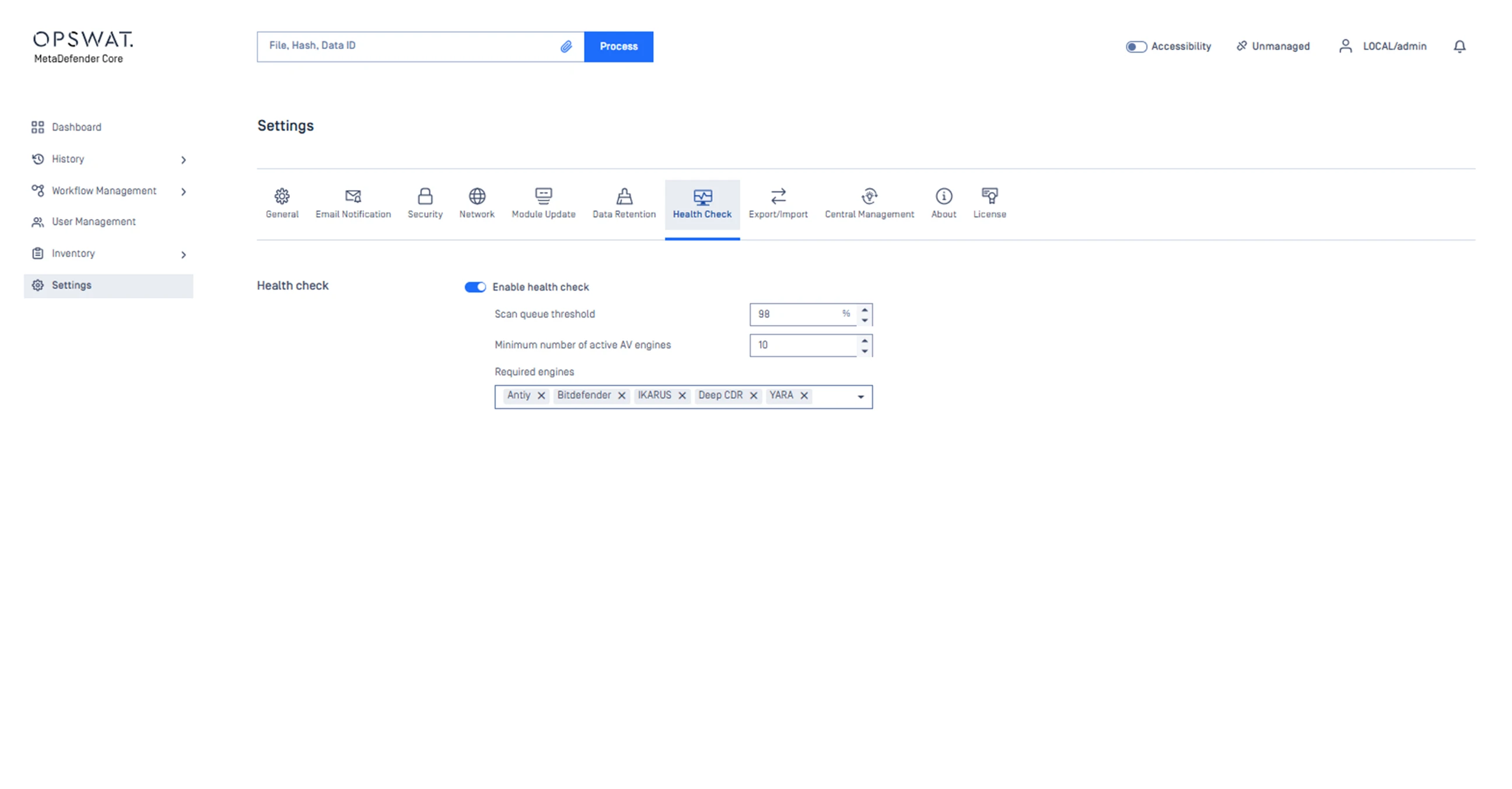
Scale to support the volume of files processed by tuning scan request queuing and defining the number of parallel threads communicating with scanning engines.
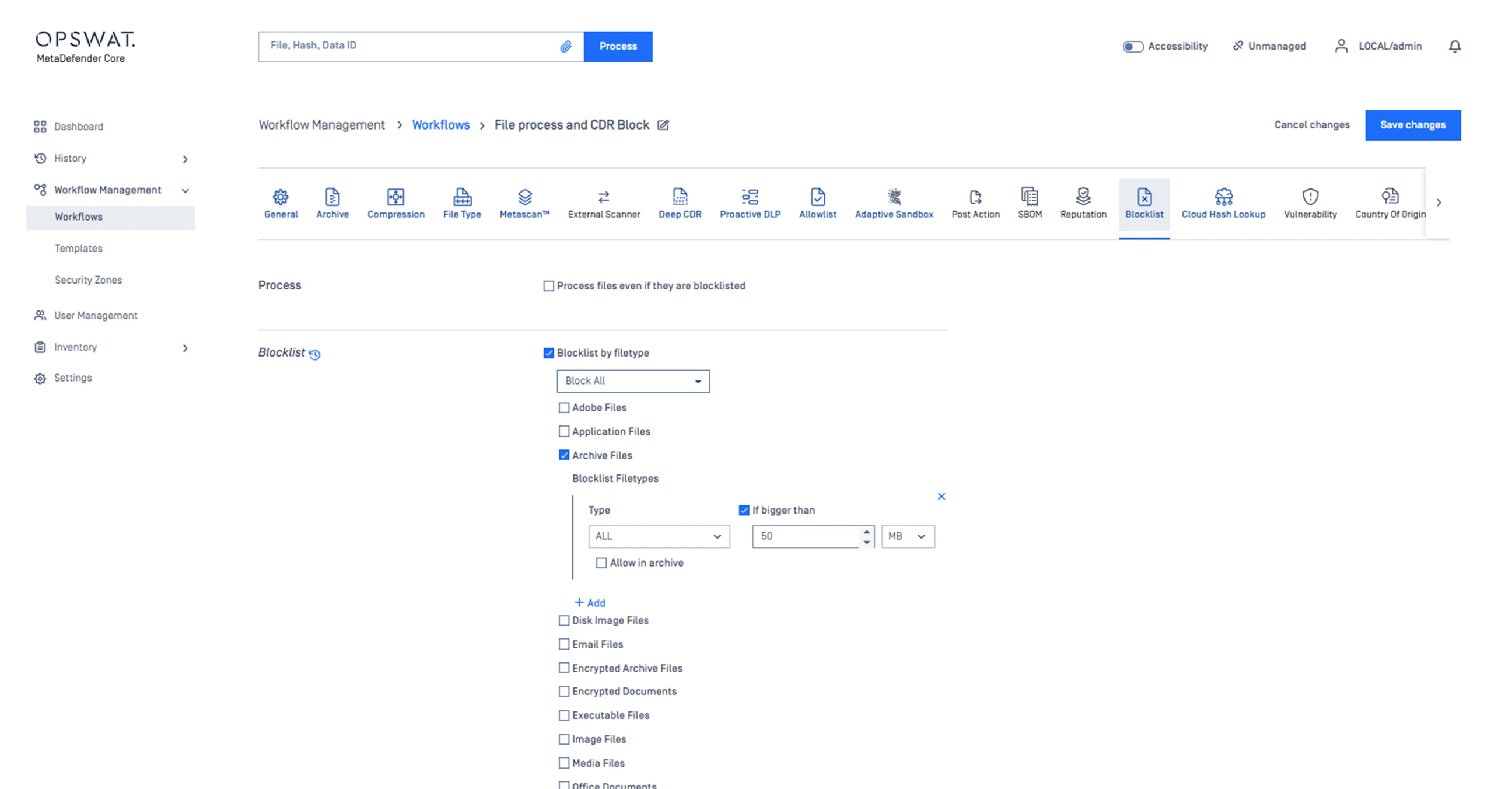
Define whether or not archive files are accepted, as well as maximum file size if allowed.
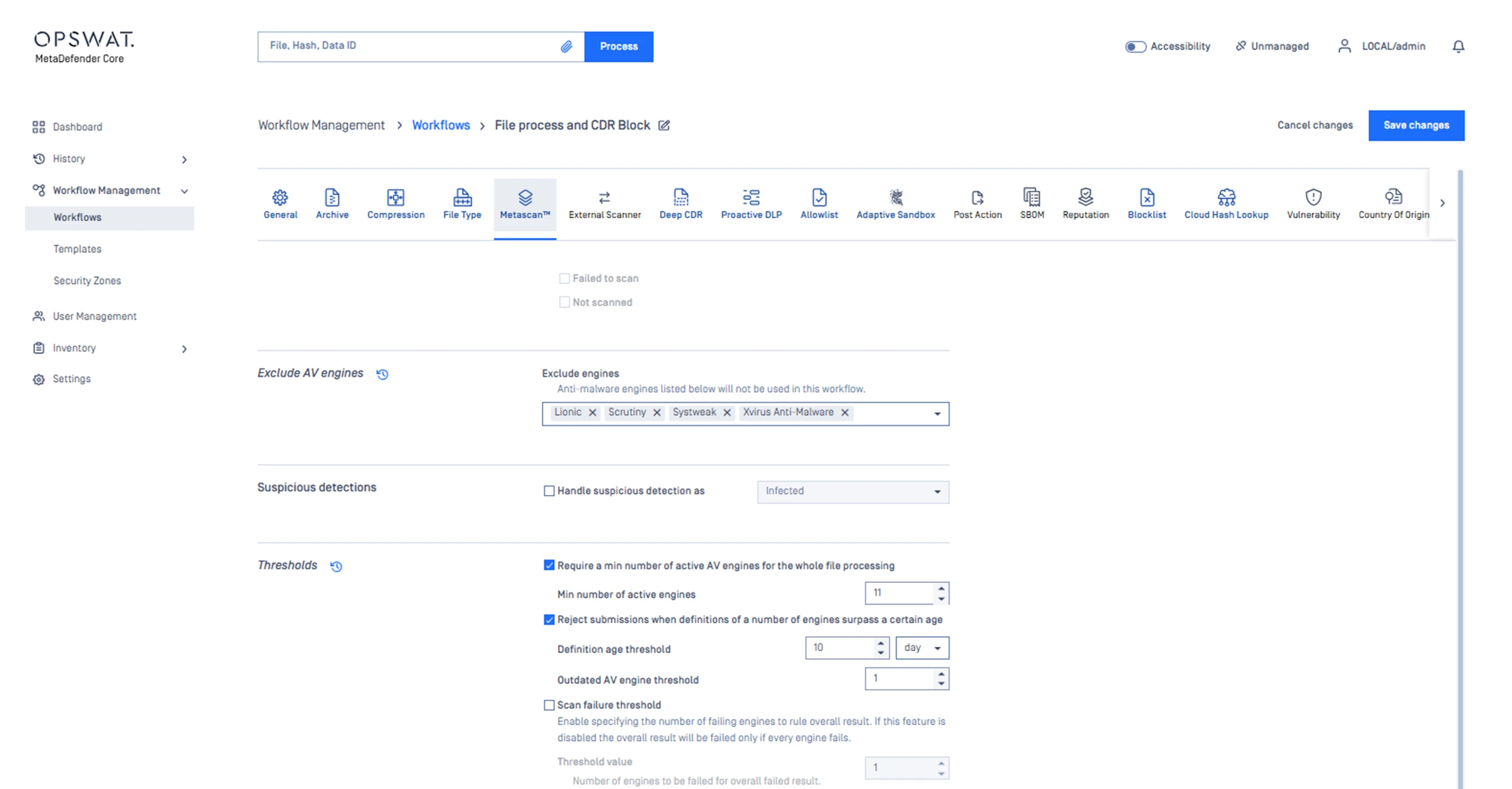
Establish a multiscanning threshold for how many engines must detect a threat before alerting as infected. A higher threshold reduces the likelihood of false positives while requiring slightly more resources.
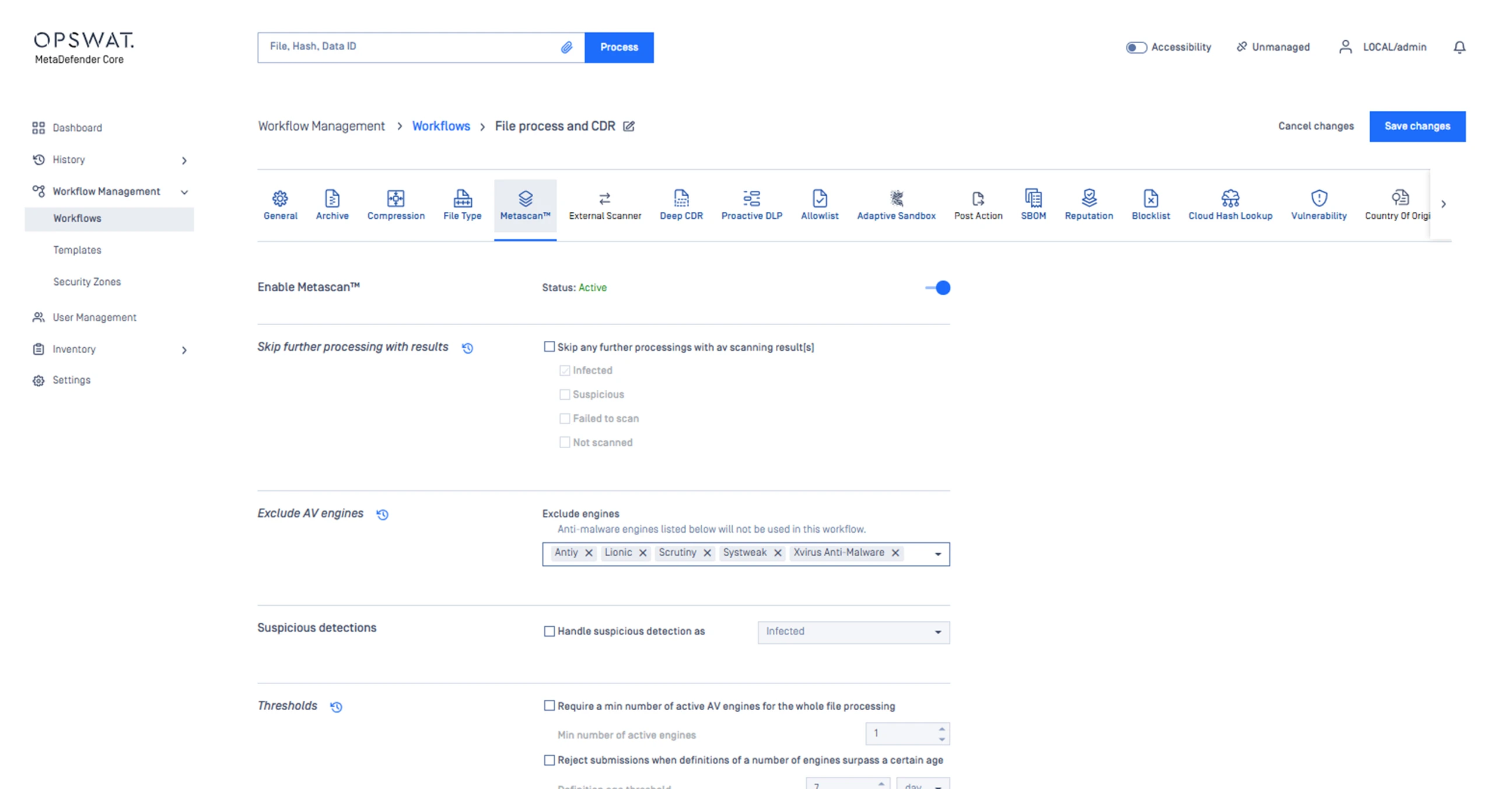
Define detection and protection workflows across Metascan Multiscanning, Deep CDR™ Technology, Proactive DLP, and Adaptive Sandbox to provide the appropriate level of security based on the source's trust level.
Our Partners
Get Started with OPSWAT Today
OPSWAT is a leader in cybersecurity solutions because we understand the risks and challenges that modern organizations face. We've developed threat intelligence capabilities that enable your team to understand threats and respond faster than ever.
Get started with our team today to discover our file security solutions.