One of the ways that we illustrate the value of multi-scanning is to show how viruses take different lengths of time to go from unrecognized by any antivirus engine to being recognized by most. High profile viruses will quickly be added to antivirus signature databases soon after they are discovered, but lower profile threats that don't have much media coverage or aren't as widespread may take much longer.
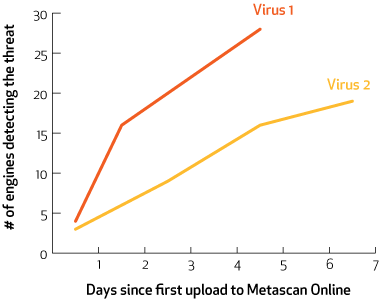
The spread of the detection of the two threats described below illustrates the variability in how quickly new virus outbreaks are added to different antivirus engine databases.
Virus 1 was first submitted to Metascan Online (a free online virus scanner) on April 4th, when it was detected by 4 different antivirus engines. By the next day, it was detected by 16 different antivirus engines and by April 8th it was detected by 28 different antivirus engines. Over the four day period this was a difference of 24 engines detecting the threat.
Virus 2 was first uploaded to Metascan Online on April 6th, when it was detected by 3 different antivirus engines, but it was added to antivirus definition databases much more slowly than Virus 1, and was still only recognized by 9 engines two days later. The detection rate rose to 16 by April 10th and 19 by April 12th. This is only a 16 engine increase over 6 days.
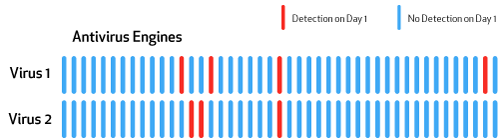
Another important thing to note about these two outbreaks is that only one antivirus engine detected both on the first day each file upload was scanned, again illustrating the value of multi-scanning as a way to significantly improve detection of early virus outbreaks.
The lesson to be learned from this data is that one cannot depend on all antivirus engine providers to immediately add virus definitions to their databases soon after another engine has identified a virus. By using a multi-scanning product, an organization can improve their odds of detecting new outbreaks before damage can be done to their systems.

