What happens when you integrate the market-leading multi-AV scanner with the most scalable, evasion-resistant automated malware analyzer available? Threat detection goodness in spades!
As evidenced by the ransomware wave, antivirus vendors struggle to close the window on new, unknown threats. Until signatures are updated, there is often a period of vulnerability when a malicious attachment will slip by the email filters, not trigger an alarm on the desktop antivirus, and lead to an infection.
The length of that window of vulnerability will vary by antivirus vendor and the sophistication and pervasiveness of the threat. This reality is the driving force for layered security — not counting on a single vendor or technology, but rather layering complementary approaches and technologies from multiple vendors.
Along those lines, VMRay Analyzer has supported for some time integration with MetaDefender. MetaDefender customers can simply add their API key into their VMRay Analyzer profile so that all samples submitted for analysis to VMRay are also run against MetaDefender.
Verifying a sample against MetaDefender will lead to one of three relevant results:
- Most or all antivirus engines detect the sample as malicious: In this case, you are probably protected already, and if an endpoint were to get infected by this sample, remediation would be readily available and the IOCs known. Dynamic behavioral analysis in VMRay Analyzer may be superfluous.
- Low antivirus detection rates of sample: If your desktop or gateway antivirus engines aren't amongst those detecting the sample, you will want the VMRay Analyzer results so that the IOCs can be used for remediation and propagated to your defenses. However, though your AV vendor may have come up short, chances are other vendors already can block and remediate the threat.
- No AV detection yet sample behaves maliciously: If no antivirus vendors detect the sample as malicious, the sample isn't on any allowlist, and yet VMRay Analyzer scores the behavior as malicious, then the IOCs generated from analysis are critical to your defense and remediation work. You can read more in our blog on VMRay's Threat Identifier score.
Of course, there is a fourth use case where the sample is not malicious, resulting in no detections and a low VTI score.
In any of these scenarios, MetaDefender provides critical information at a glance to defenders looking at analysis reports. Further, MetaDefender can be used to triage quickly and efficiently which threats require further investigation, and which can be dealt with using existing tools and signatures.
An example of how VMRay and MetaDefender work together is shown in a blog post we did earlier on Powershell ransomware. We can see in the summary that at the time of the scan in May only 5 of 43 engines identified the script as malicious:
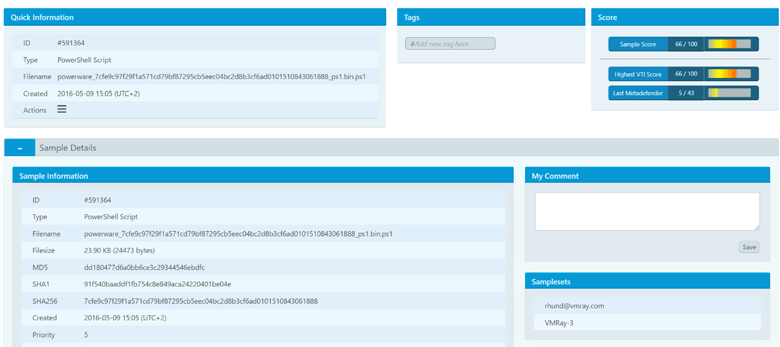
Click image to enlarge
While detections have since risen, they are, at the time of writing, still at a modest 16 out of 42.
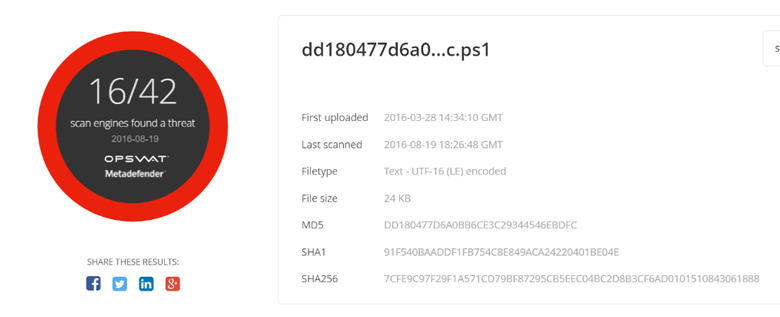
To be clear, this does not necessarily mean that the other 26 vendors would have let the script install malware on a desktop. Most vendors have behavioral engines that often block unknown files from executing if suspicious activity is detected. However, it's nevertheless an indicator that the majority of antivirus engines would not detect this file as malicious in a gateway environment such as a web or email filter.
A result such as this would precipitate action based on IOCs that can be extracted from VMRay Analyzer. In automated environments where VMRay Analyzer is integrated via the REST API with other security solutions such as TIPs like ThreatConnect or EDR tools like CarbonBlack, IOCs are machine-readable in STIX/Cybox format.
To learn more about how VMRay and OPSWAT are delivering enhanced threat visibility and detection contact us or follow us on twitter.
References
- https://www.sans.org/reading-room/whitepapers/incident/enterprise-survival-guide-ransomware-attacks-36962
- https://www.vmray.com/blog/powershellransomwarepowerware/
- https://blog.knowbe4.com/antivirus-isnt-dead-it-just-cant-keep-up
- https://www.vmray.com/blog/custom-threat-scoring-vti/
- https://www.vmray.com/wp-content/uploads/2016/07/ThreatConnect-VMRay-Feature-Brief.pdf
- https://www.vmray.com/blog/vmray-analyzer-1-10-whats-new/
Author: Chad Loeven, VMRay

Chad has been involved in enterprise security for over 20 years. Prior to VMRay he managed technology alliances at RSA. He came on board RSA via their acquisition of Silicium Security and Silicium's ECAT Endpoint Detection and Response (EDR) technology. Prior to Silicium he ran Sunbelt Software's Advanced Technology Group (ATG) (now ThreatTrack Security), bringing to market the CWSandbox malware analyzer and threat intel feeds.

