Research conducted by OPSWAT, provider of solutions to secure and manage IT infrastructure, found that over 80% of IT security professionals cite their biggest fear as infected or compromised devices accessing their data or assets. 42% were also concerned about devices not being encrypted when accessing their data or assets, and a further 35% that the devices had riskware or greyware installed.
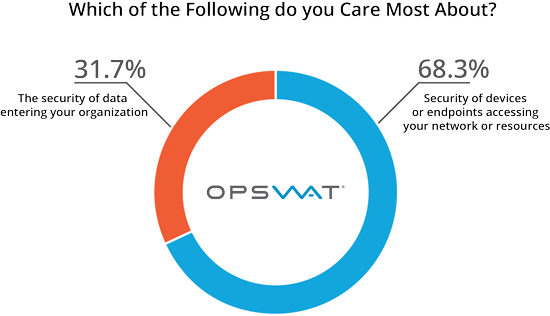
The need to have all devices secure was echoed, with 68% of respondents saying that the security of devices or endpoints accessing their networks and resources was more important to them than the security of data entering their organization. 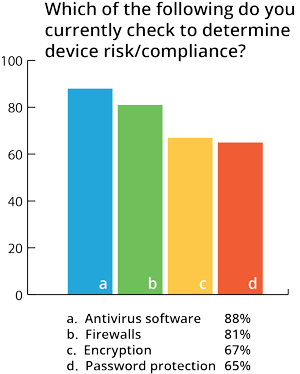 Despite 35% of respondents being concerned over greyware accessing their data, only 13% currently check for greyware when determining risk and compliance. Antivirus software (88%) and firewalls (81%) continue to be the leading defenses within organizations. Encryption (67%) and password protection (65%) are also popular amongst IT security professionals.
Despite 35% of respondents being concerned over greyware accessing their data, only 13% currently check for greyware when determining risk and compliance. Antivirus software (88%) and firewalls (81%) continue to be the leading defenses within organizations. Encryption (67%) and password protection (65%) are also popular amongst IT security professionals.
The survey also showed that the popularity of multi-scanning is on the rise, with 72% of respondents using multi-scanning software within their organization. Of that 72%, three-quarters said they use multi-scanning for email security and to scan endpoints and processes, and over half using it to scan uploads to their server.
"With over 390,000 new threats emerging daily, anti-malware engines need to detect new threats continuously, and will inevitably address different threats at different times. By using only one or two antivirus engines, companies are exposing themselves to malware threats, since no antivirus engine can be accurate 100% of the time. However, by using multiple anti-malware engines, companies can benefit from several detection algorithms and heuristics to significantly increase malware detection rates, as well as their protection against new threats. With multi-scanning, only one engine needs to detect the threat in order for a company to be protected" said Benny Czarny, CEO at OPSWAT.
The survey was conducted amongst over 100 IT professionals across the RSA Conference, Infosecurity Europe and Black Hat.
If you are interested in seeing more from our survey, please take a look at the additional survey results highlighted below:
1. Has your company experienced a malware breach in the past 12 months?
- Yes - 22.4%
- No - 77.6%
2. How does your organization use multi-scanning? (select all that apply)
- Email security for incoming and outgoing files - 77.8%
- It is built into my own application - 17.3%
- Scan endpoints and processes - 77.8%
- Scan uploads to a server - 58.0%
- Scan binaries before software release to check for false positives and/or malicious code - 35.8%
- Other - 6.2%
3. Do you know which NAC or SSL VPN solution your organization uses?
- Yes - I know which VPN we use - 36.6%
- No - I'm not sure - 63.4%
4. What is your biggest problem with your NAC or SSL VPN solution?
- Not able to check for security or compliance issues. For instance, I have no way to determine which devices are encrypted - 18.7%
- New software applications are not always detected by the current solution - 17.3%
- I am unable to check unmanaged devices to ensure that they are not infected - 40.0%
- If a user cannot connect, remediation requires time/money that my department doesn't have - 24.0%