2015 may just go down in history as the year of the hack.
2015 was filled with 365 days of headlines covering everything from the OPM breach, to Anonymous' latest shenanigans, to mobile vulnerabilities. The breadth and depth of these breaches were both alarming and eye-opening. We saw how an average teenager with basic computer skills can bring down telecom giants and how CCaaS (cyber-crime as a service) has quickly become a booming business. Governments breached other governments and federal agencies had their weaknesses exposed in serious ways. Even gamers and kids weren't safe in 2015.
At Reason Core Security, we believe that it's important to study the past in order to prepare for the future. That's why we decided to take a look at some of the vulnerabilities that made a majority of these hacks possible in order to understand how to avoid them in 2016. We also believe that to be truly secure, you need to use a multi-layered approach. Keep reading to learn our recipe for real security!
Flash
Flash, oh, Flash! Millions scorned you, your creator and champion, Adobe, tried in earnest to save you, but in the end you were just too insecure for your own good. Adobe's Flash was the standard for delivering rich web content for years. Used in gaming, on websites and in video display, for a large chunk of the existence of the internet, Flash was everywhere - on your browser, on top 100 Alexa-ranked websites, and in those dancing e-cards grandma always sent you.
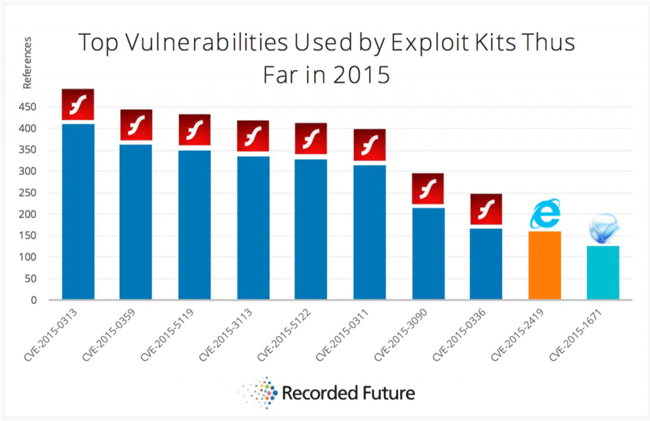
Vulnerabilities used by exploit kits in 2015
True, Flash was in every corner of the web, but it contained critical flaws that made it a hacker's playground and was a huge resource hog, draining battery life faster than you can say "iPhone 7". In the last few years, it seemed that there was a newly discovered Flash threat every week, and sometimes there were many more than that. The July data dump of Hacking Team's database, creators of surveillance software used by governments, brought to light three previously undiscovered zero-day vulnerabilities which hackers gleefully tested as soon as they had the chance, all within just a few days of each other. Then there were the countless times Flash was used in malvertising exploits, delivering malware via infected ads to millions of unsuspecting visitors to Yahoo, Forbes, The Huffington Post, and The LA Times.
In December 2015, after Facebook, FireFox and Chrome all banned Flash, Adobe took the hint (although at an agonizingly slow pace) and announced that they were discontinuing Flash. It will be replaced with Adobe Animate, which uses aspects of Flash and the newer, much more secure HTML5, which is largely viewed as its successor.
Now that Flash has been discontinued, will 2016 be more secure? We'll have to stick around to see, won't we?
Java
Let's talk about Java. No, not the place, not the drink and no, not Javascript. We are talking about Java, the programming language used to create multimedia content, that was estimated to be involved in 50 percent of cyber-attacks within the last few years. To be clear, it's not actually the language itself that isn't secure, it's the browser plugin that accompanies Java that seems to have more holes than Swiss cheese, which allow cyber criminals to swipe PII like passwords and credit card information.
Java, purchased by Oracle in 2010, has had its ups and downs. In April 2015, Oracle disclosed that newly discovered vulnerabilities left millions of users at risk and unless they patched the program ASAP, there was a remote possibility for hackers to access highly PII. In July, the Advanced Persistent Threat group or APT28, attacked members of NATO and a U.S. defense organization in a zero-day Java exploit known as Pawn Storm.
In late 2015, Oracle came under fire from the FTC as the new versions didn't actually get rid of the buggy older versions if users had more than one version installed. Yes, the new, more secure version was as safe as apple pie, but the older, non-secure versions were still at large on 850 million PCs, putting them all at risk. Oracle was ordered to inform users of the issues and to help them uninstall buggy versions.
Experts have long advised users to disable Java. Unless your business has custom apps built using the platform, chances are you don't really need it, so it's better to just get rid of it.
Angler Exploit Kit
Exploit kits help cyber criminals take advantage of vulnerabilities that are already on computers or devices (and with the rise of IoT, your coffee maker and Barbie Doll too, but more about that later). So, how does this relate to those previously mentioned Flash and Java vulnerabilities? Exploit kits make them easy to find and, well, exploitable. They work like this - you search for something, like that nifty internet-connected coffee maker on your search engine of choice and rather than reaching IoTcoffeemakersRus.com, you get redirected by hackers to a website hosting an exploit kit. That kit scans your computer for vulnerabilities and then essentially "drops" the malware in those holes.
The Angler Exploit Kit, an especially down and dirty tool, has been partially responsible for over 40 percent of attacks in the first part of 2015. A good deal of its popularity comes from the fact that it's easy to use and doesn't take much technical know-how. It's a favorite among Dark Web forums where it is sold as CCaaS (Cyber Crime as a Service). To learn more about CCaaS, you can read one of our recent posts covering the topic. The cyber criminal doesn't have to do very much, aside from some minor configuration changes to implement the mayhem. As simple as it is to set up, it's quite advanced in its evasion methods. It changes IP addresses and host names and its components change from victim to victim.
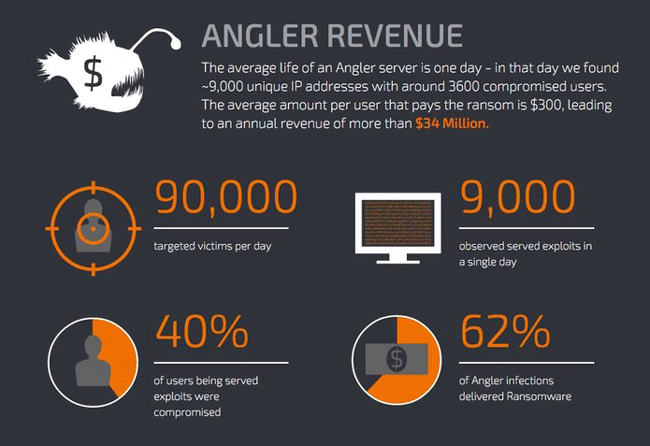
Statistics on Angler Exploit Kit
Angler was a key element in many of 2015's most damaging banking Trojans like Dridex and Vawtrak and is a perennial favorite for ransomware distributors, used in TeslaCrypt and Cryptowall which netted $30 million before it was taken down in mid-2015.
SQL Injection
In November, British Telecom giant Talktalk got hacked by a bunch of teenage boys using SQL Injections. SQL Injections work by entering malicious code into a form on a web site, then the form spits back information that it wasn't supposed to divulge. SQL Injection attacks have been around for longer than some of the Talktalk hackers have been alive and its dangers have been known for just as long.
SQL Injection attacks have been used against the World Health Organization, The Wall Street Journal and numerous federal agencies' websites. This attack method routinely makes it to the top spot on OWASP's Top Ten Vulnerabilities list. SQL injection vulnerabilities put millions of WordPress and Joomla websites in jeopardy in just this past year alone. It's a fan favorite among hackers as it's easy, clean to pull off and it's effective, too. SQL Injection vulnerabilities were a key element in the recent VTech hack, putting 6.3 million kid's information at risk.
So what does all of this mean for you?
Well, in short, it means that real security isn't as simple as some people might hope it to be. To really keep your devices and networks safe, you need to use more than one method and put in some elbow grease. In order to achieve this, at Reason Core Security we recommend a multi-layered approach to security, making sure all your bases are covered.
"Multi-layered" means assessing all the different parts of your home network and applying individual tactics where they are needed, rather than relying on one piece of software that may (or more likely, may not) keep you fully protected. Contrary to what a lot of non-techies believe, antivirus is an imperative aspect of security but should also be used in combination with some other really important, and often overlooked ingredients in the creamy multi-layered security cake. To set up an effective, multi-layered security approach, you should do the following:
- Update and patch all software and operating systems as soon as an update or patch is released. Those older versions of software are a key starting place for hackers.
- Backup your files. Let's say that you do get angled by Angler or another ransomware tactic. The day you decided to play it safe and backup your data will go down as your finest "I told you so" moment ever.
- Use a strong antivirus software, something with multiple methods for detection, that doesn't only rely on updating signature databases and has a long-standing good reputation and releases regular updates. Antivirus software is good for finding known threats, so it's effective when it comes to legacy viruses and Trojans. That being said, you will still need to keep up with more current threats, and for that you need anti-malware software.
- Use a solid anti-malware software like Reason Core Security to detect zero-day attacks and malware samples that are still in the wild. Anti-malware uses fewer resources than antivirus and takes far less time to update and detect threats and finds threats that antivirus software can't. Use it together with your antivirus software for a double-whammy against vulnerabilities.
Let's take the lessons from 2015 seriously and learn from them to make 2016 the year of "real security".

About the Author
This post was written by Batya Steinherz, a Web Content Manager at Reason Core Security. She is in charge of developing engaging content, blog management and social media marketing for Reason Core Security. Reason Core Security's Anti-malware applications are OPSWAT Silver Certified.
Interested in writing for OPSWAT? Submit your products for certification, and contact OPSWAT for details and requirements.