Archive Extraction
Archive files often contain multiple layers of compressed content designed to bypass traditional security
tools. OPSWAT Archive Extraction safely unpacks archives and routes every file through deep analysis.
- Recursive Archive Extraction
- Archive Bombs Detection
- Data Corruption Prevention
OPSWAT is Trusted by
Recursive Extraction
to Configurable Depth
160+
Archive Formats
Supported
Single-Pass Extraction
Across All Engines
Archive Bomb Detection and Containment
Encrypted and Password-Protected Archive Support
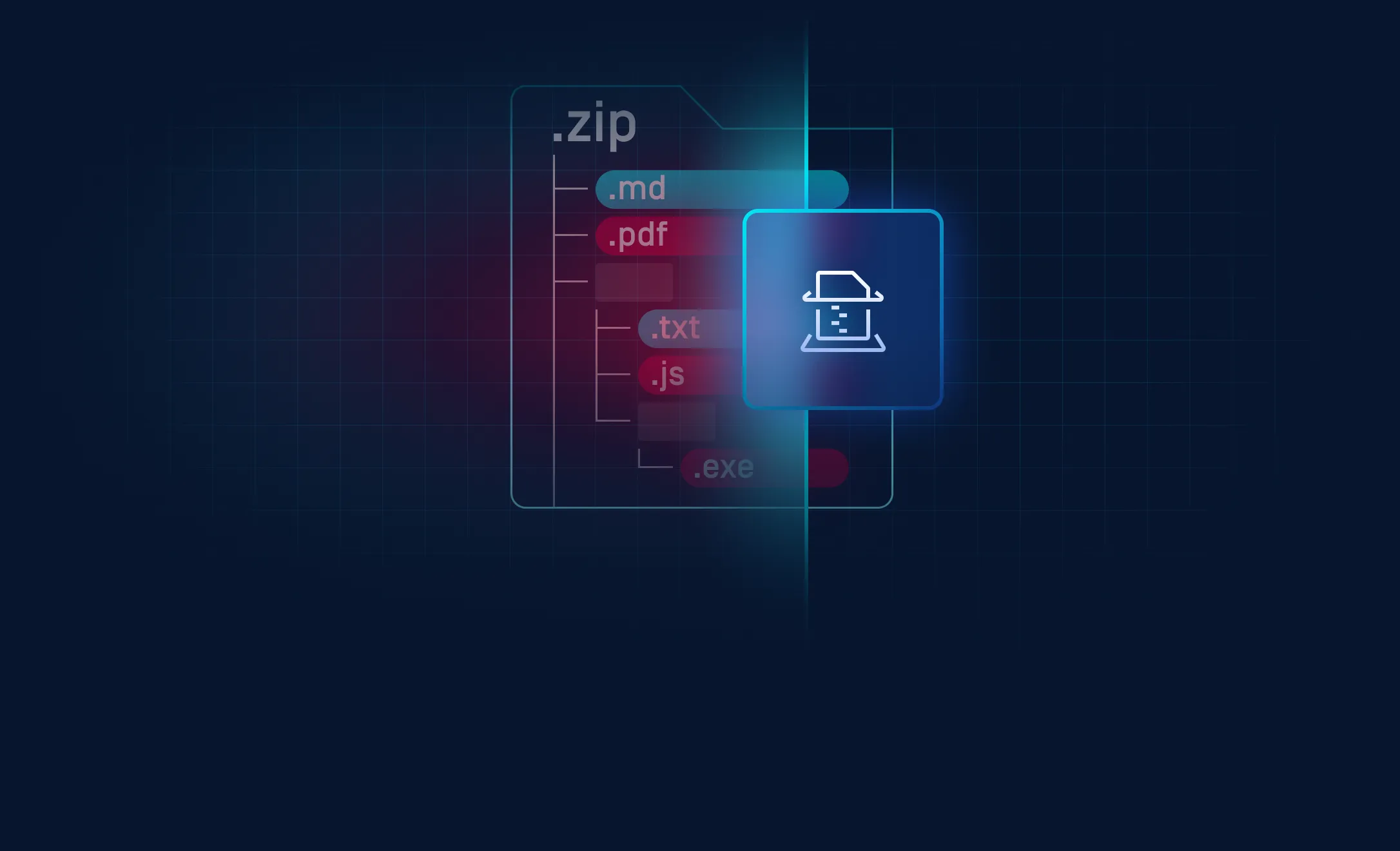
Attackers Weaponize Archive Structure
Nested layers, malformed headers, and concatenated archives defeat scanners that inspect only the surface of a
file before clearing it as safe.

Embedded Threats
Scanning an archive as a whole does not reveal what is inside it. Attackers use nested layers, concatenated ZIPs, self-extracting containers, and polyglot files to ensure parsers stop before reaching the payload. Without extraction as a prerequisite to scanning, detection engines never inspect the actual threat.
Encrypted Archives
Password-protected archives are unreadable by most security tools without the password. Active campaigns continue to deliver ransomware and infostealers this way, with the password sent through a separate channel to avoid correlation.

Malformed and Oversized Archive
Archives do not need to carry a payload to cause damage. Decompression bombs exhaust CPU, memory, and disk resources to stall or crash scanning pipelines, creating a window for other threats to pass through uninspected. Deeply nested archives produce the same result when no limits on recursion depth, file count, or extracted size are enforced.
Consistent, Scalable Archive Extraction
The Archive Extraction Engine centralizes unpacking of compressed and container file formats, ensuring every file inside is exposed and routed through deep analysis before going through other scanning engines.
Deep Unpacking, Full Visibility, Better
Inspection
The Archive Extraction Engine leverages optimized parsers to extract files, unify extraction logic, and integrate with scanning and CDR workflows.
Key Features & Benefits
Recursive Archive Extraction
Automatically extracts multiple nested layers to reveal files hidden deep inside complex archive structures that single-pass scanning never reaches. No layer of nesting becomes a safe hiding place for malicious payloads.
Single-Pass Extraction Across All Engines
Archive handling runs once per file type and the extracted output is shared across all downstream scanning engines, eliminating redundant unpacking. Faster processing and consistent results regardless of how many engines are deployed.
Configurable Extraction Limits
Administrators set explicit ceilings on recursion depth, maximum extracted file count, and total uncompressed size per workflow. Decompression bombs and oversized archives are contained before they exhaust system resources or stall scanning pipelines.
Deployment Options

On-Premises
Deploy within your existing security infrastructure for full control and customization.

Cloud
Use cloud-based processing to scale archive analysis across distributed environments.

Hybrid
Combine on-premises and cloud deployments to optimize performance and security coverage.
Resources

The difference between the Archive Extraction Engine V.S. Metascan Antivirus engines extraction
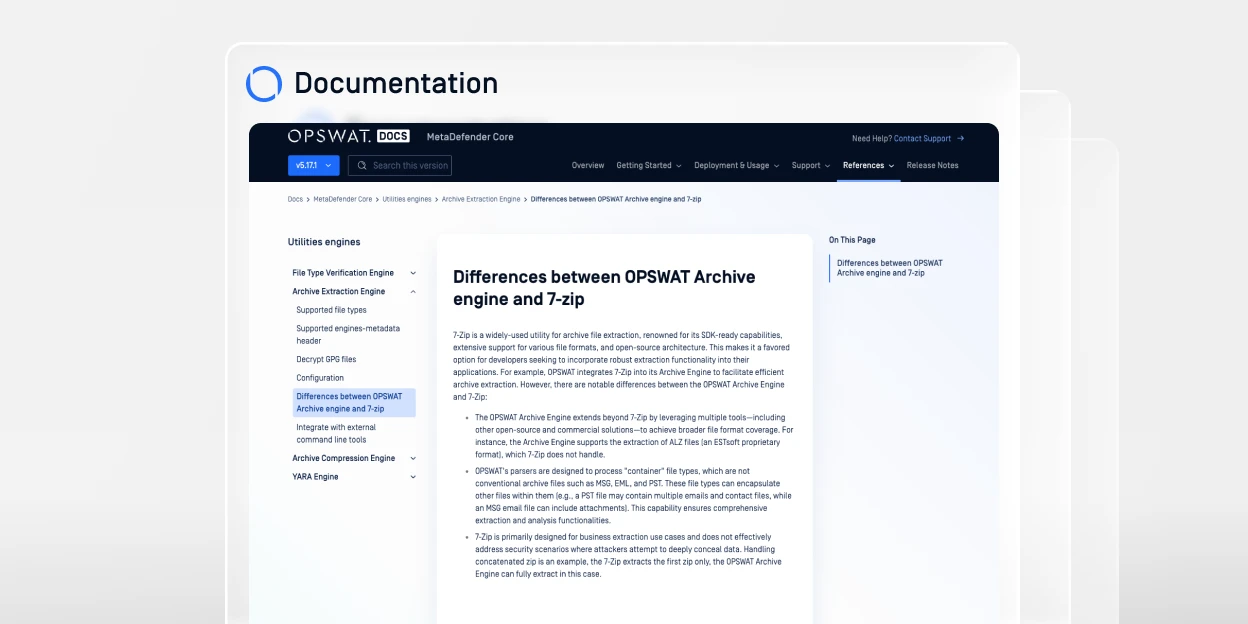
Differences between OPSWAT Archive engine and 7-zip