As the Internet of Things grows, the number of malware vectors grows with it. Each internet-connected device is another possible attack gateway and provides IT administrators with even more challenges to securing their network. One entry point of malware security professionals might not be aware of is a device they use on a daily basis.
Every day workers print a variety of documents including spreadsheets, sales agreements and private user information. Printers are essential for work productivity and can be found in nearly every office environment. Users previously had to have an actual hard-wire connection to printers, but with the growth and evolution of technology users can now easily and quickly print from anywhere via Wi-Fi.
Data loss prevention for printers has traditionally been considered a physical issue. Sensitive documents printed and left on the tray can quickly make it into unauthorized hands. Manufacturers have addressed this with numerous security features — ranging from biometric authentication to PINs needed when retrieving the printed document. With the recent decrease in reliance on printers for critical business operations, one would assume the security risks would have been proportionally decreased as well. Operationally speaking, this is true — but as a network entry point, the risks are ever increasing.
Because networked printers are often configured with access to the organization's file server, email server, and active directory, the potential risk is enormous. In fact, security consultant Deral Heiland was recently quoted by The Register saying that his research team was "able to gain access to Active Directory environments by extracting useable credential data from multi-function printers 40 to 50 percent of the time." Some other proof of concept exploits are equally chilling:
- Multiple exploits possible via Jetdirect vulnerabilities (article in Spanish)
- A whole collection of MFP exploits, conveniently delivered via SlideShare
- HP vulnerability could allow hackers to literally set HP printers on fire
- Things can go kaboom when a defense contractor's 3-D printer gets hacked
On a lighter note, a recently demonstrated attack on Canon Pixma printers resulted in Doom running on the device. The vulnerability in this case was weak encryption of the firmware. Clearly, these attacks range from the terrifying to the downright humorous!
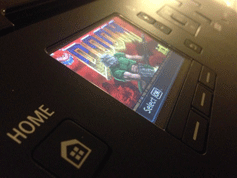
Image courtesy of The Register
But why do these attacks rarely go past the proof of concept stage? One thought is the high disparity in the printers used (both brand and model) across environments, especially compared to the relatively homogenous environments of most Windows and Mac devices. But for a targeted attack the variety of printers in the wild is not an impediment, as long as the target has a vulnerable model.
Why Attack Printers?
With numerous other attractive attack vectors available, why should you worry about your printers? There are a couple of reasons. They are some of the oldest type of devices used by organizations, tightly integrated into critical systems and don't garner the same sense of risk as other flashy IoT devices like thermostats or smoke detectors. The firmware is rarely upgraded. With websites such as Shodan making it easier to find exploitable devices, it's important for security professionals to understand what they are connecting to via Ethernet or Wi-Fi, and how they are integrated.
As we've outlined in a previous blog post, it's important that users connect to and use trusted devices whenever possible. When connecting to a printer within an organization, IT administrators typically take the correct measures to secure their users from malicious attacks. But when attempting to connect to a printer in a library, coffee shop, or another setting with relaxed security policies, OPSWAT recommends making sure all of your security applications are enabled and up-to-date. Additionally, we recommend scanning your device for malware upon completion of the printing task with multiple anti-malware engines to ensure your device was not infiltrated during the connection.
Due to the integral part printers play in daily work activities, it's not feasible for companies, administrators and home users to stop using them entirely. There will always be risks associated with any device, and with the Internet of Things becoming a larger part of our day-to-day activities we need to make sure we recognize the vulnerabilities they introduce—even if it's through the neglected printer collecting dust in the corner.

