Remote Access Dilemma
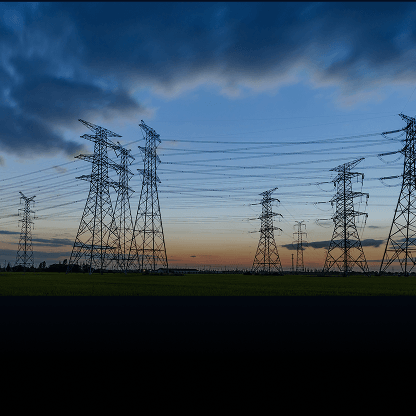
A global leader in consumer goods manufacturing was facing growing complexity across its remote operations. Their global operations rely heavily on tightly integrated production systems, including ICS (industrial control systems) and other OT infrastructure.
With over 70 production sites and hundreds of internal engineers, contractors, and OEM partners needing OT access, the company’s existing infrastructure was showing signs of strain.
Key Challenges:
- Scalability Limitations
- Traditional VPNs couldn’t support the growing user base
- Manual user provisioning led to delays and administrative overhead
- Insufficient Security Controls
- No real-time enforcement to prevent unauthorized actions
- Inadequate auditing of third-party access
- Operational Complexity
- Inconsistent access management across regions
- Role-based permissions were difficult to enforce
- Fragmented integration with the company’s cloud-hosted SIEM
Securing OT Access Without Sacrificing Agility

To support its growing operational complexity and cybersecurity demands, the company implemented MetaDefender OT Access across more than 70 globally distributed facilities. The platform delivered a unified, scalable, and secure way to manage remote access for over 900 users, ranging from internal engineers to OEM vendors and contractors.
Unified and Flexible Deployment
- A single secure solution for all third-party and internal remote access, eliminating the need for multiple tools or dedicated VPNs.
- Rapid deployment across all sites—each instance fully operational in under a day, with no firewall reconfiguration required.
- Flexibility to deploy via dedicated AWS instance, on-premises 1U appliance, or VMware ESXi virtual appliance, tailored to each site's needs.
- Uses a fully encrypted, outbound-only TLS tunnel, blocking pre-authentication attacks common in traditional VPN setups.
Granular Security and Session Control
- Role- and protocol-based access is enforced at the session level, allowing fine-tuned permissions aligned to user responsibilities and activity.
- Built-in support for native OT protocols ensures policy enforcement down to command-level granularity within systems like Modbus, OPC UA, and S7.
- DPI (Deep Packet Inspection) monitors session traffic in real time, with the ability to instantly block unauthorized or out-of-policy behavior.
- Continuous monitoring and over-the-shoulder live viewing enable live supervision of RDP sessions for compliance and operational assurance.
Seamless Enterprise Integration
- Integrated with Microsoft Active Directory and SSO platforms (Azure AD, Okta) for unified identity management and secure password sharing.
- Two-factor authentication and device posture checks via MetaDefender Endpoint ensure only compliant devices gain access.
- Connected to SPLUNK for real-time analytics and MetaDefender Managed File Transfer (MFT) for secure file exchange without bypassing access controls.
- All session activity is recorded and logged to syslog, including RDP recordings, supporting audit trails and regulatory compliance.
By aligning with both IT and OT requirements, MetaDefender OT Access became a core pillar of the company’s remote access and cybersecurity strategy.
Outcome: Control at Scale—Without Compromise
With MetaDefender OT Access our client was able to centralize and secure remote access across its entire operational footprint—while maintaining uptime, auditability, and regulatory compliance.
- Over 900 users are now governed through centralized policy enforcement, with role- and protocol-specific permissions tailored to their operational needs.
- Real-time DPI and session logging provide full visibility into user actions at the command level, allowing for proactive threat detection and granular accountability.
- Integration with the company’s SIEM not only simplifies audit readiness but enhances threat hunting by correlating access events with broader network telemetry.
- Operational resilience was maintained throughout the deployment, thanks to the platform’s non-intrusive, software-based implementation model.
MetaDefender OT Access’s ability to provide granular control over remote access while maintaining operational efficiency has been game-changing for our global operations. We now have complete visibility into who's accessing what, when, why, and how—all while supporting our teams and OEM partners with the secure access they need to keep our production lines running smoothly.
Chief Information Security Officer
Building Tomorrow's Manufacturing Security Today
The successful deployment of MetaDefender OT Access has not only solved immediate access management pain points but has also laid a secure foundation for the company’s next phase of digital transformation. With a scalable platform in place, the team can now onboard more partners, expand operations confidently, and maintain rigorous compliance standards globally.
Ready to Transform Your OT Access Strategy?
Whether you're managing five facilities or fifty, remote access doesn’t have to be a security risk—or a technical headache. Discover how MetaDefender OT Access can secure your critical infrastructure while empowering your teams to work efficiently from anywhere in the world.