Cyber security firm FireEye published a warning last week about the spread of FormBook malware. FormBook steals data, tracks keystrokes, and copies form submissions (hence the "FormBook" name), and it also can receive and execute various commands from the attacker's server. FormBook spreads largely via malicious Word, Excel, PDF, and archive files.
According to FireEye's research, which the company acknowledges is not comprehensive, FormBook malware campaigns have mostly targeted aerospace, defense, and manufacturing firms in the U.S., and companies across various industries in South Korea.
However, the span of the attacks is not limited to these countries and industries — a large number of countries and a wide variety of industries have been targeted.
Phishing Emails and Malicious PDFs
The attacks via Word, Excel, and PDF files — which we at OPSWAT often refer to as "productivity" files — are mostly concentrated in the U.S., while the majority of the attacks in South Korea use archive files that contain malicious payloads.
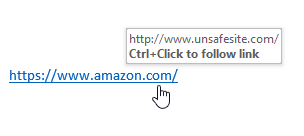
FireEye obtained screenshots of some of the phishing emails and malicious PDFs the attackers have used. With phishing emails purporting to be from shipping companies, attackers trick users into opening a PDF and then clicking a hyperlink within that PDF.
FormBook Characteristics

Although attacks like these often leverage zero-day vulnerabilities, this is not the case with FormBook. The malware does not exploit any unknown vulnerabilities. Instead, it is able to inject itself into processes and install function hooks via known issues.
In fact, the party selling FormBook claims in their advertising materials that the malware works "perfectly on all versions of [W]indows." They list all Windows operating systems from XP to 10, and all Windows Server operating systems from 2003/R2 to 2012/R2.
FormBook is highly persistent and is resistant to both detection and removal.
FormBook changes its installed file name, path, registry key, and file extension randomly. It performs a number of checks for malware analysis, and it "reads Windows' ntdll.dll module from disk into memory, and calls its exported functions directly, rendering user-mode hooking and API monitoring mechanisms ineffective" (per FireEye).
Once FormBook is on a system, it logs keystrokes, grabs internet forms, copies passwords, and can even take screenshots. It can also perform a variety of other tasks if directed by the command and control server, including a system reboot or shutdown, downloading and executing files, and launching commands using ShellExecute.
Malware-as-a-Service
The creator or owner of the malware sells it to attackers as a service. The unknown person behind FormBook has been advertising its capabilities on numerous hacking forums for over a year. Their pricing structure is advertised to be:
- $29 per week
- $59 per month
- $99 per three-month period
- $299 "Pro" (pay period is unclear, or may be one-time fee)
Analysis
Though FormBook has some capabilities that make it unique, the techniques by which it spreads are the same tried-and-true methods — phishing emails, malicious attachments, etc. — that any self-styled "hacker" can execute without too much technical knowledge.
Especially in the age of malware-as-a-service, it is easier than ever for even unskilled cyber criminals to wreak havoc — and for malware creators to make a profit. Criminals will continue to develop and propagate malware at ever-increasing rates; it's relatively easy compared to other criminal activities, and the financial incentives for cyber attackers are strong.
For these outbreaks, user error is partially to blame, since FormBook could not install without a user opening a malicious file.
However, user error is the one factor in cyber security that never goes away. No matter how well an organization's users are trained, a targeted phishing email can and likely will fool someone.
Organizations need stronger solutions to plug up the holes in their security. Eliminating potential threats in emails and documents is a strong place to start.