Title
Create new category
Edit page index title
Edit category
Edit link
Repositories
Firstly after navigating to the Reports page you will see the Repositories that were scanned.
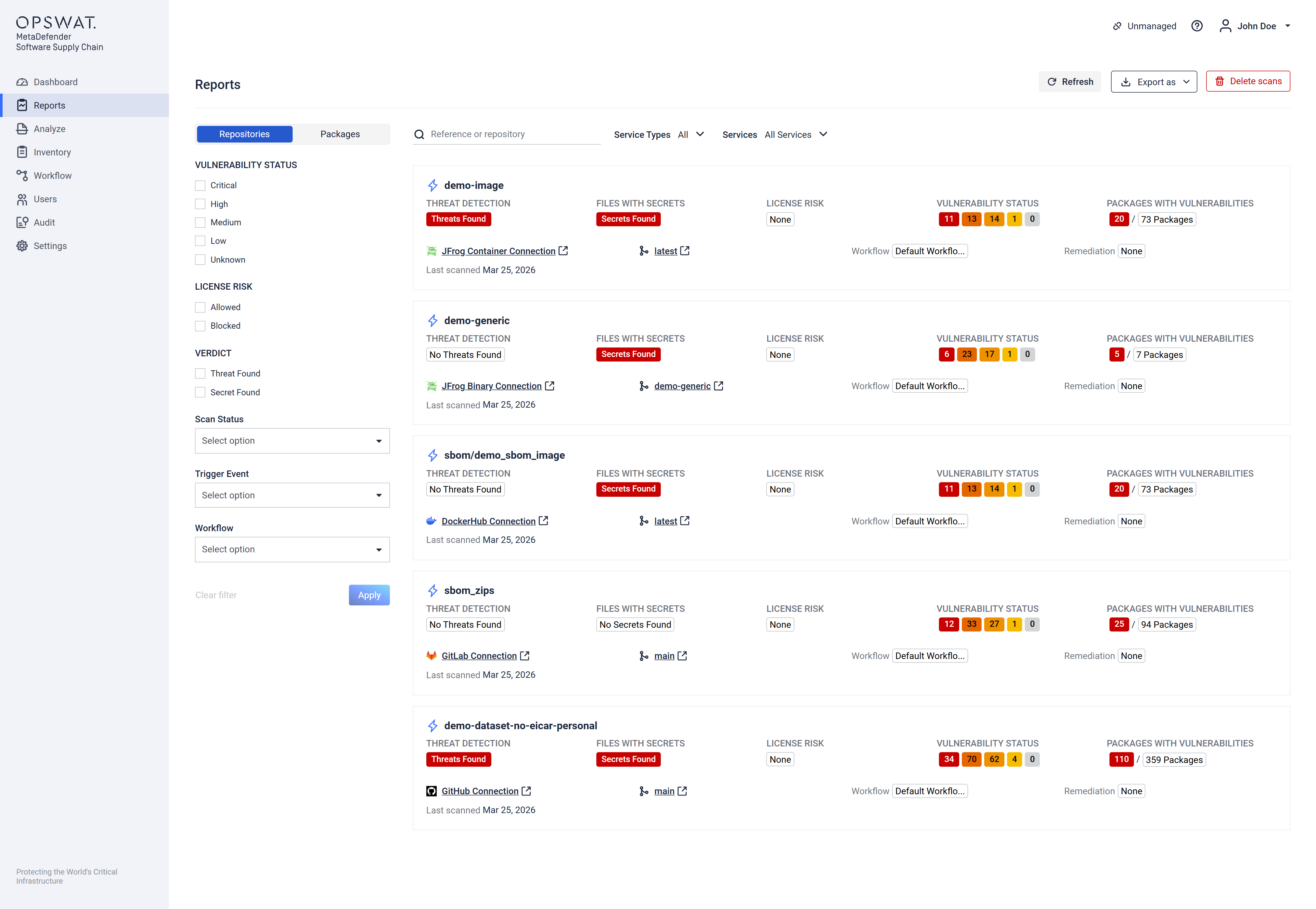
Here are some actions that are available for you:
You can filter by Vulnerability Status, License Risk, Verdict, Scan Status, Trigger Event and Workflow, all from the left side filters.
Filtering is also possible by using the top section right above the cards, which contains:
- Search, that lets the user search for references that were scanned or repository names.
- Service Type, that lets the user filter by the service type which in this case can be Source Code, Container or Binary
- Services, that lest the user filter by all the services that we have integrated.
Creating a PDF export for all scans or a CSV export for all CVEs.
Click on a report in order to see more details and you will be redirected to the Repository page
The Repository page will show all the branches that have been scanned from the selected repository.
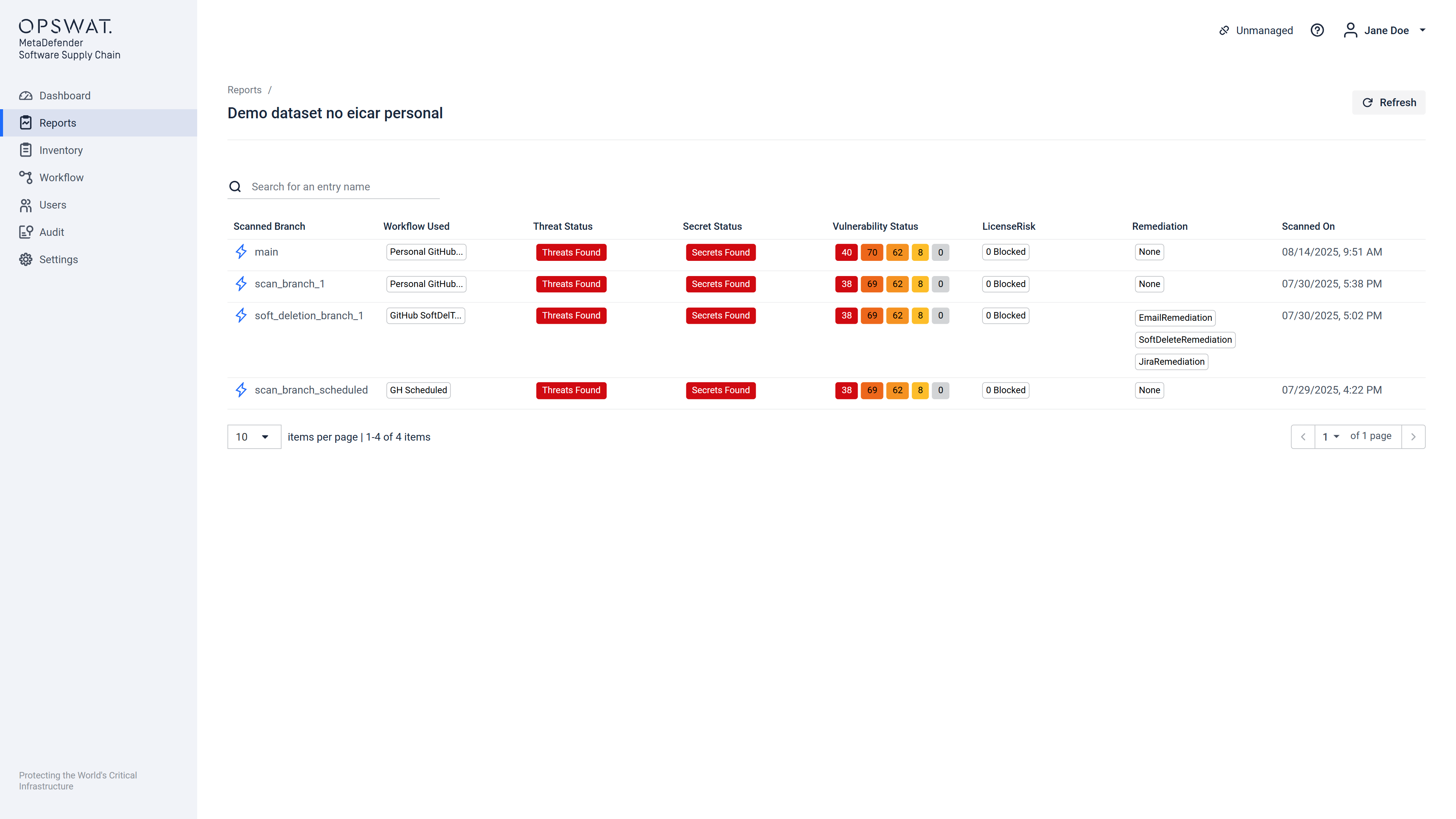
After Clicking on a branch or tag you will be directed to a page where you can see more detailed view of the vulnerabilities and issues.
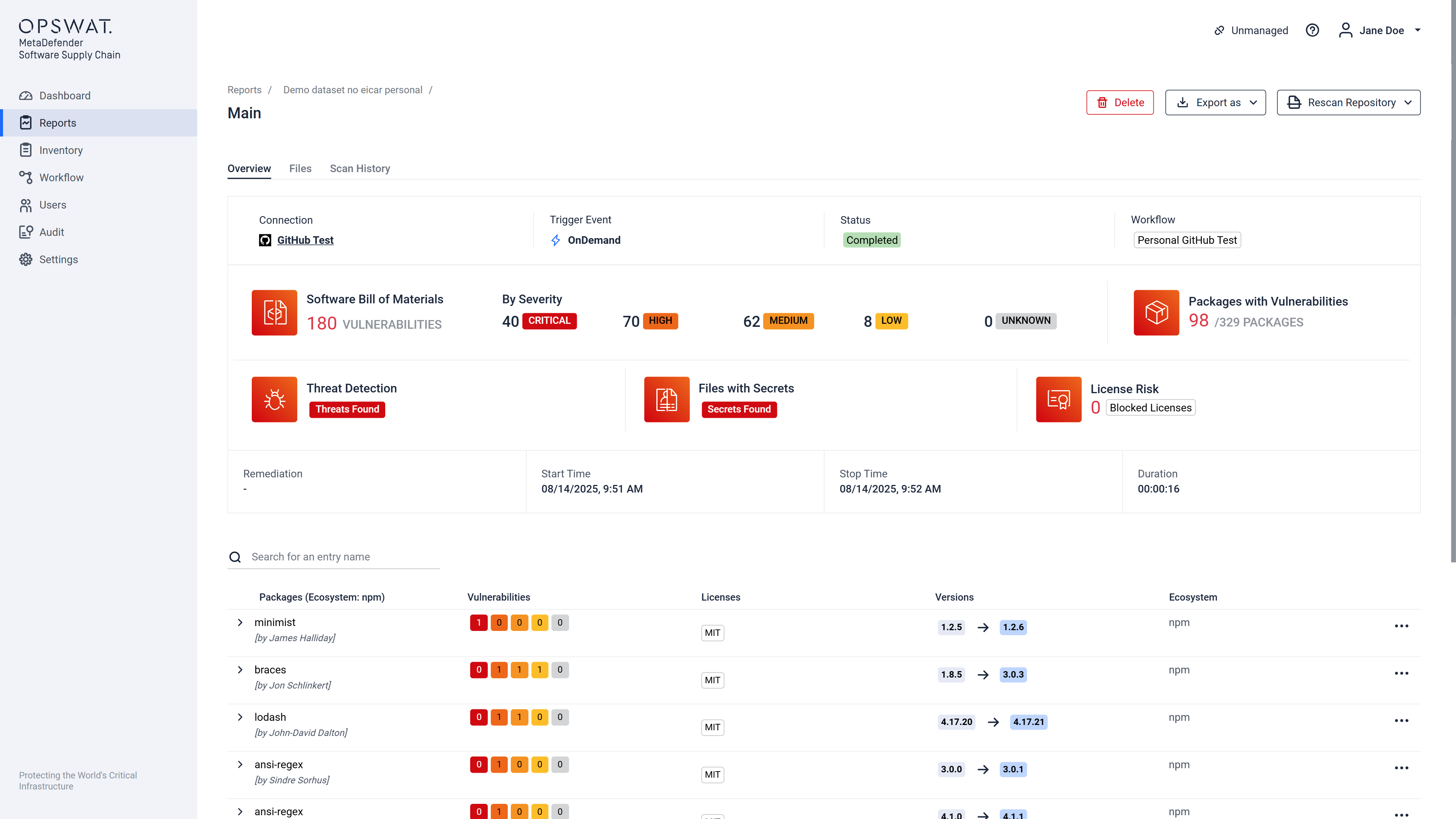
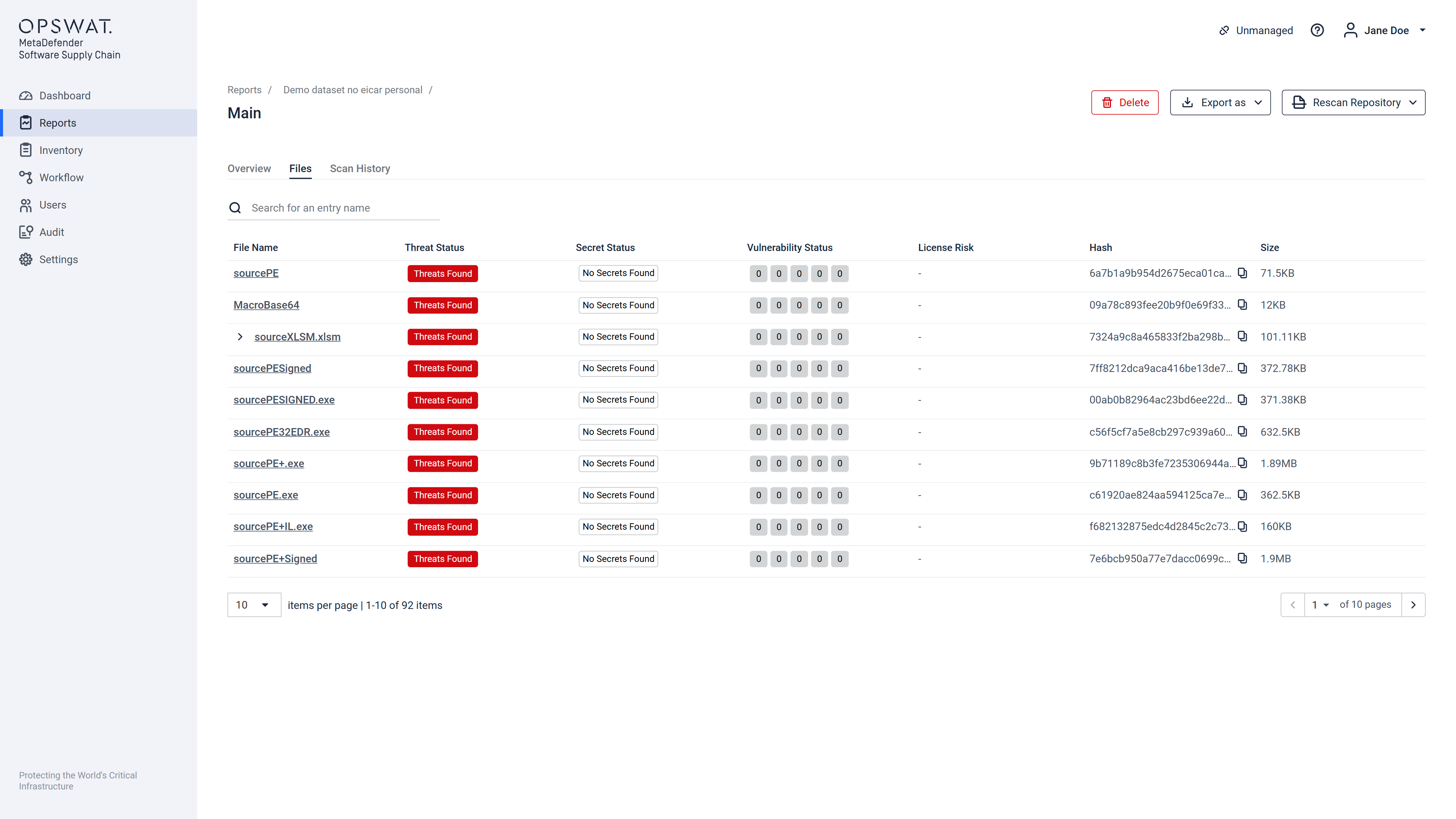
You can also dive deeper by clicking the expand caret on each file and you will see a tree view with more information regarding the issues. Or by clicking on a file which will open a view that displays more information about Threats, Secrets and Extracted Files (for archives).
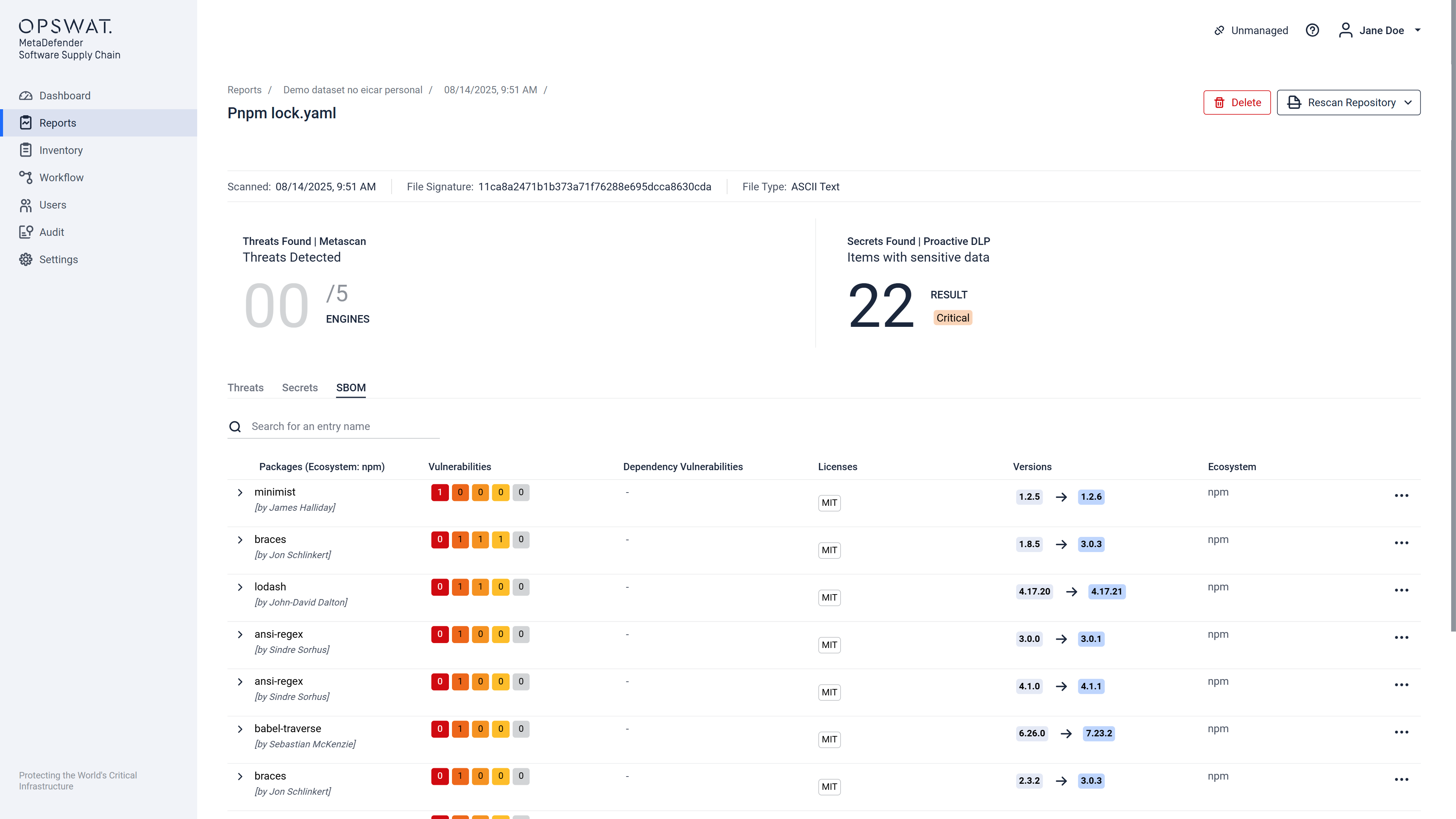
Software Bill of Materials(SBOM) analyzes the third-party packages in source code and containers, identifies known vulnerabilities, then generates inventories of these software components. With SBOM, users can scan track dependencies in large codebases to understand the risks associated with open-source software (OSS) and secure their applications.
Our current SBOM (Software Bill of Materials) implementation provides detailed information at the archive level, but there are limitations when it comes to nested archives. The behavior can be summarized as follows:
- For individual files outside of archives, the SBOM will display the appropriate information.
- For archives, the SBOM will sum up all relevant details (e.g., vulnerabilities, licenses) from the files contained within it, including nested archives.
- However, any nested archives (e.g., a zip file within another zip file) will not display their own SBOM details when inspected individually. Instead:
- The top-level archive will include the aggregated SBOM information from all its contents, including nested archives.
- Any nested archive files will have an empty SBOM when viewed directly.
- However, any nested archives (e.g., a zip file within another zip file) will not display their own SBOM details when inspected individually. Instead:
This behavior ensures that the SBOM at the topmost archive level provides a complete view of all vulnerabilities and license risks contained within its structure. However, direct SBOM visibility for deeply nested archives is not available.