Title
Create new category
Edit page index title
Edit category
Edit link
How do I retrieve the MetaDefender logs?
This article applies to all OCM v7.5.0+ releases deployed on Windows or Linux systems, and all MetaDefender Endpoint releases deployed on Windows, macOS, Linux, iOS and Android systems.
When troubleshooting an issue on a device, OPSWAT Support will usually request that the user send us the OPSWAT Client logs from their machine.
There are two ways to retrieve the Client logs:
- OPTION 1: Collect the logs directly from the Client device.
- OPTION 2: Retrieve the logs remotely. This method:
- requires that the user have administrator privileges on the associated OPSWAT Central Management account
- requires that the device be connected to the OPSWAT Central Management server
- is only applicable to Windows/macOS persistent Client.
OPTION 1: Collect the logs directly from the Endpoint device
Automatic Collection
This option is only available for Windows and macOS persistent OPSWAT Client.
Windows (Persistent Client)
- Download OPSWAT’s Log Collector tool, Here.
- Run the downloaded file.
- The zipped log file, which may be very large, will automatically be placed on your desktop, to be forwarded to the OPSWAT team.
macOS (Persistent Client)
- Download OPSWAT’s Log Collector tool, Here.
- Run the downloaded file.
- The zipped log file, which may be very large, will automatically be placed on your desktop, to be forwarded to the OPSWAT team.
Manual Collection
Windows (Persistent Client)
- Go to the relevant location/s below to collect the required log/s:
Client logs:
- Type %ProgramData% into the path bar and hit Enter.
- Then add \OPSWAT\Gears\logs\ to complete the path.
Crash dumps:
- Type %ProgramData% into the path bar and hit Enter.
- Then add \OPSWAT\Gears\logs\reports to complete the path.
SDK logs:
- Type %ProgramData% into the path bar and hit Enter.
- Then add \OPSWAT\Gears\sdk to complete the path.
OPG (verification file) logs:
- Type %HOMEPATH% into the path bar and hit Enter.
- Then add _ _\Appdata\Local\OPSWAT\Gears\Logs to complete the path.
- Copy the required logs, to be compressed (if necessary) and forwarded to the OPSWAT team.
Windows (On-Demand Client)
- Go to the relevant location/s below to collect the required log/s:
Client logs:
- Go to the folder where the MetaDefender Endpoint executable file is stored.
- Then locate the file named gears-ondemand.log
Crash dumps:
- Type %HOMEPATH% into the path bar and hit Enter.
- Then add \AppData\Local\CrashDump to complete the path.
If on-demand Client is triggered by third-party vendors, go to the relevant location/s below to collect the required log/s:
Pulse Secure Host Checker:
- Type %AppData% into the path bar and hit Enter.
- Then add \Pulse Secure\Host Checker\policy_XXX to complete the path. (so, for example: C:\Users\bob\AppData\Roaming\Pulse Secure\Host Checker\policy_1)
VMWare Horizon Client:
- Depending on which Horizon Client version you run, both the on-demand MetaDefender Endpoint executable file and the log file can be found in one of the locations below:
- C:\Users<username>\AppData\Local\VMware Horizon View Client\Code Cache<uuid>\
- C:\Program Files (x86)\VMWare\VMware Horizon View Client\Code Cache<uuid>\
- Depending on which Horizon Client version you run, both the on-demand MetaDefender Endpoint executable file and the log file can be found in one of the locations below:
- Copy the required log/s, to be compressed (if necessary) and forwarded to the OPSWAT team.
macOS (Persistent Client)
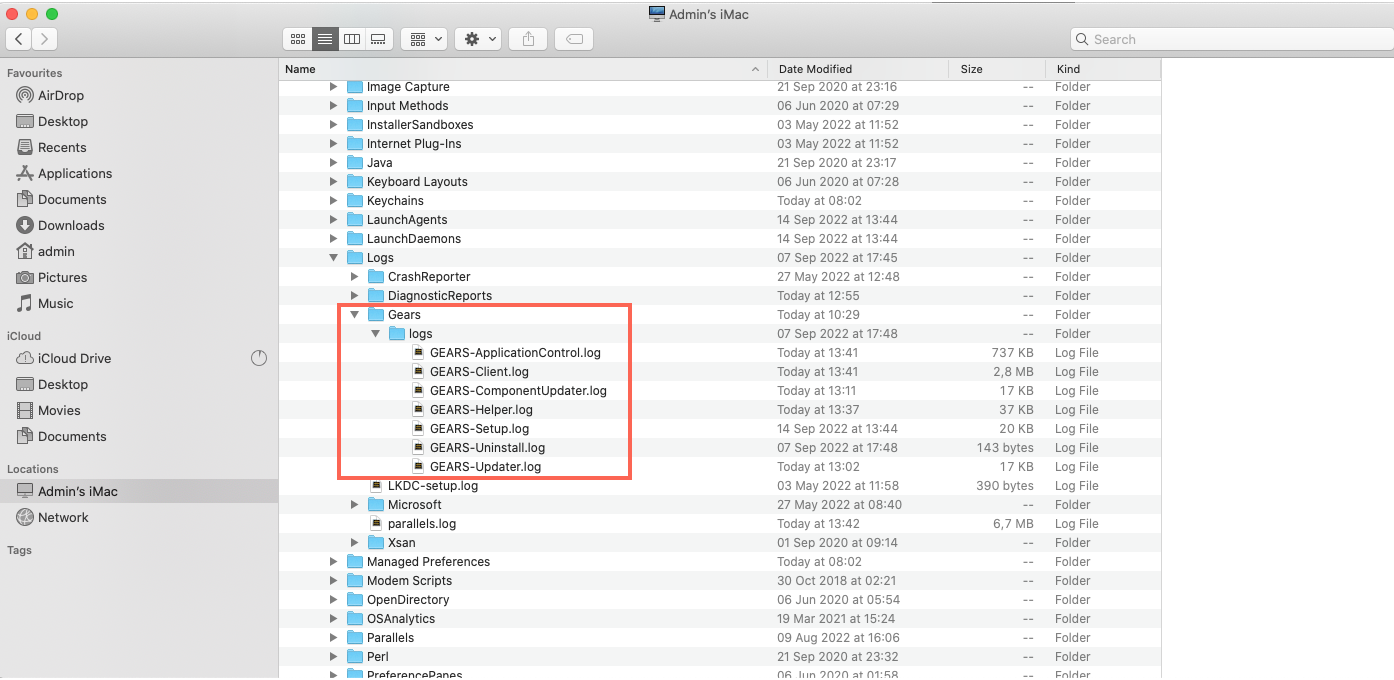
- Open Finder and go to /Library/Logs/Gears/logs, as illustrated in the screenshot below.