Secure Access Solution
10.6.2605
Search this version
Secure Access Solution
Secure Access Solution
SAML Single Sign On based
3rd Party Integration
Title
Message
Create new category
What is the title of your new category?
Edit page index title
What is the title of the page index?
Edit category
What is the new title of your category?
Edit link
What is the new title and URL of your link?
Okta with Github
Summarize Page
Copy Markdown
Open in ChatGPT
Open in Claude
My OPSWAT Central Management can be easily integrated with an Okta & Github to ensure that a device is compliant with the organization's security policy before it is granted access to Github. This ensures that the user is not only authenticated by Okta, but also a device the user uses to access SaaS applications tested for risks and vulnerabilities such as infections or outdated operating systems, BEFORE it accesses an organization's cloud services.
Follow below steps to integrate My OPSWAT Central Management with your Okta & Github.
Step 1. Create Application On Okta
- Login to Okta Admin Dashboard
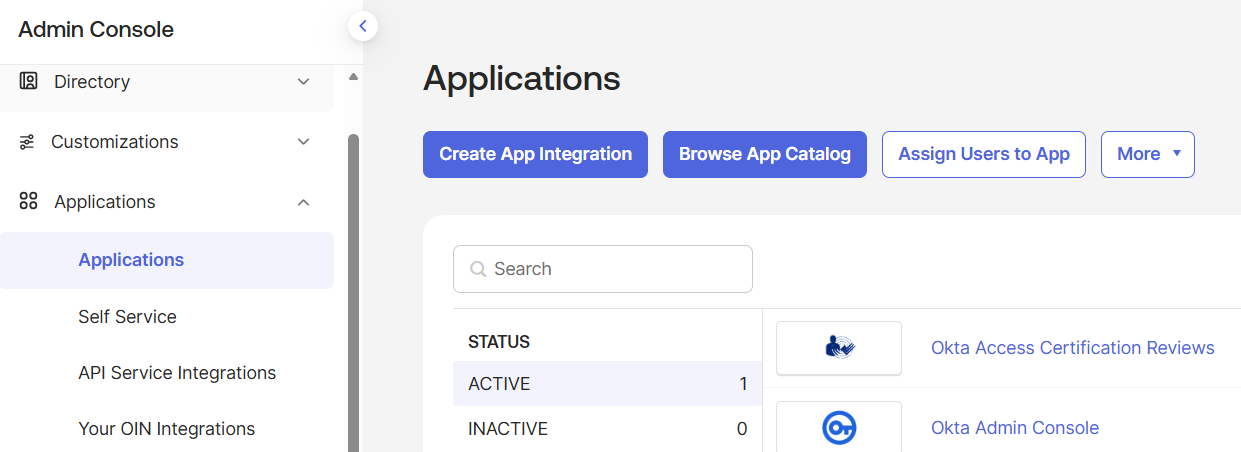
- Navigate to Applications -> Applications then click on Create App Integration
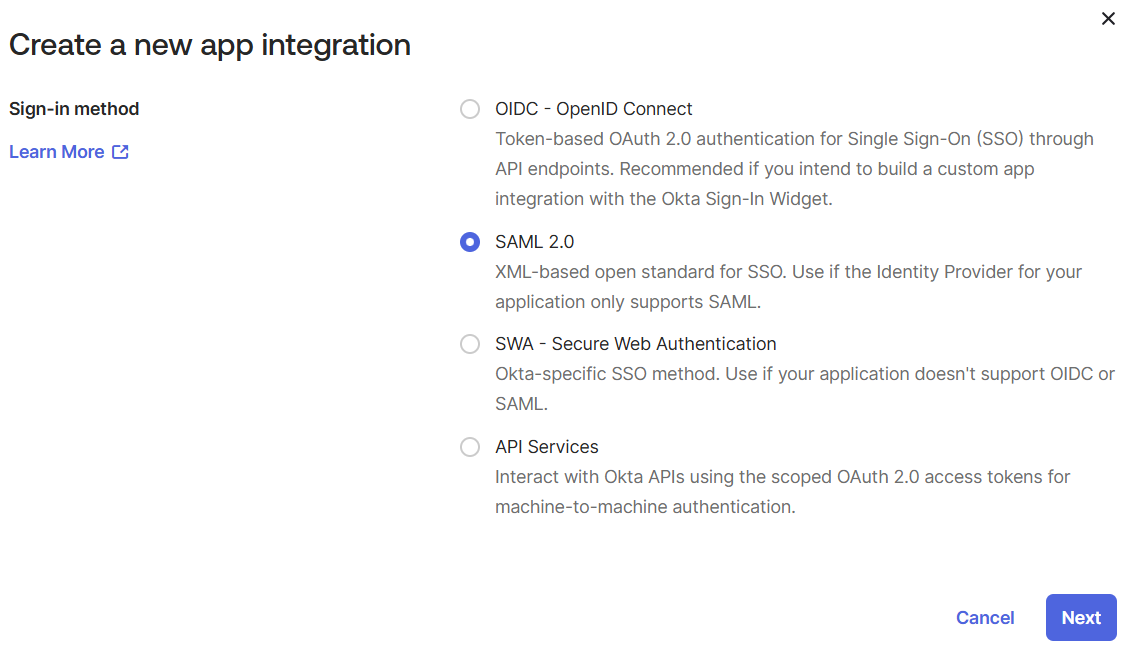
- Choose SAML 2.0 and click Next
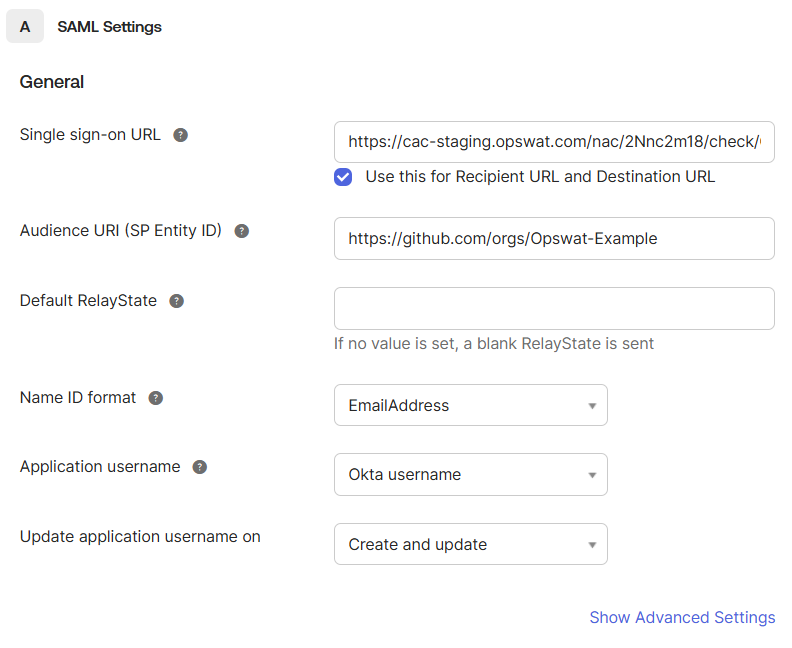
- At the SAML Settings step, fill with below information:
- Single sign-on URL: fill with a placeholder, like http://localhost
- Audience URI (SP Entity ID): fill with format https://github.com/orgs/<your organization>
- Name ID format: EmailAddress
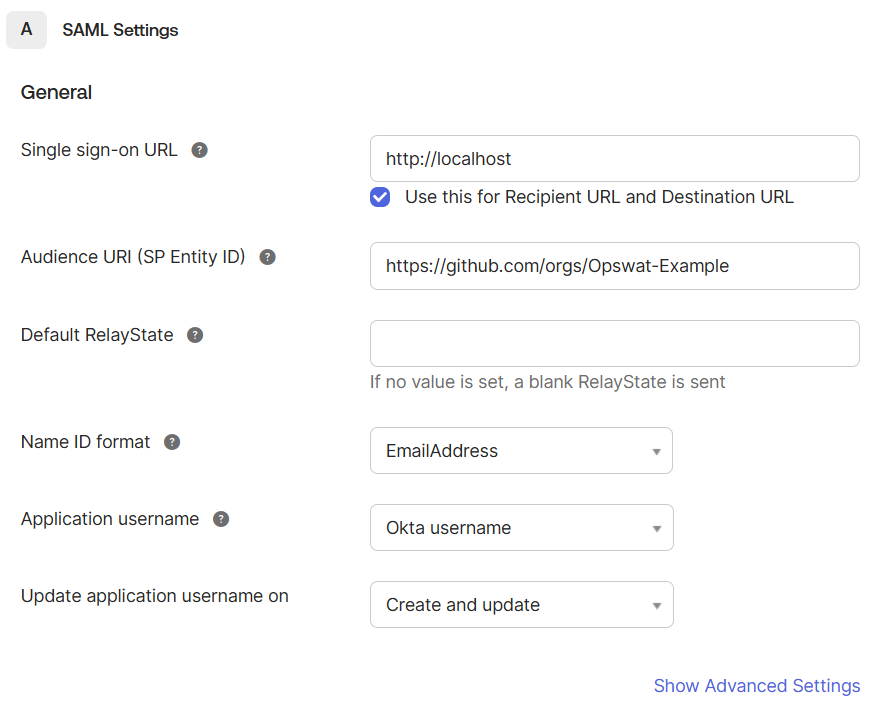
- Click Next then click Finish
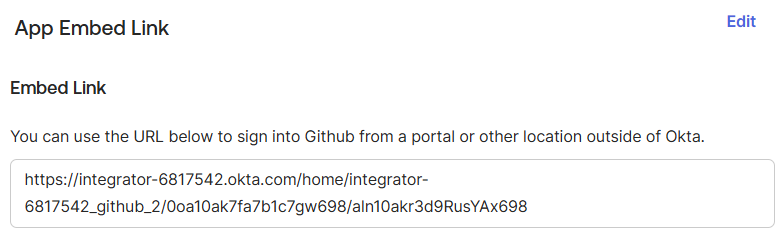
- Navigate to the Github application and click on General tab, then copy Embed Link
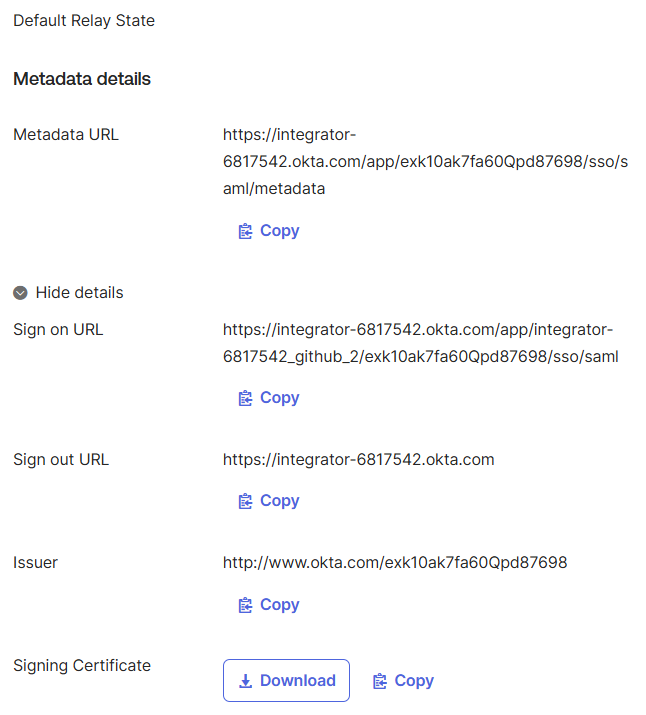
- Click on Sign On tab
- Copy Sign on URL
- Copy Issuer
- Download Signing Certificate
Step 2. Add application and configure Access Rules on My OPSWAT Central Management
- Log in to the My OPSWAT Central Management console.
- Navigate to Secure Access > Protected Apps.
- Check "Enable Secure Access".
- Click SAVE.
- Click Add Protected Application then choose IDP METHOD option.
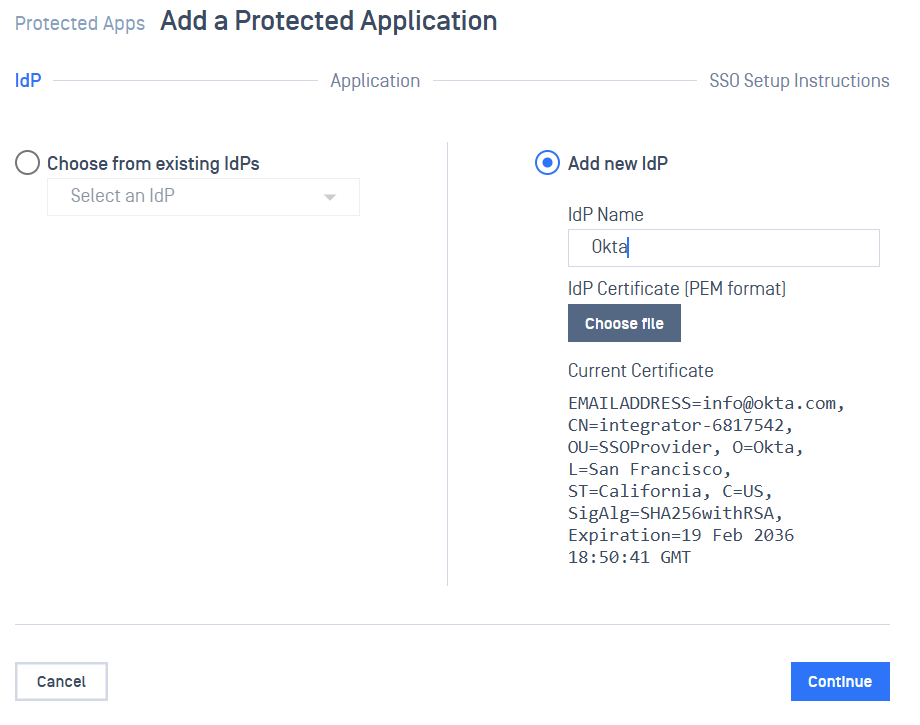
- Choose option Add new IDP , enter the name, and upload the certificate got in step 1.10. Then click Continue
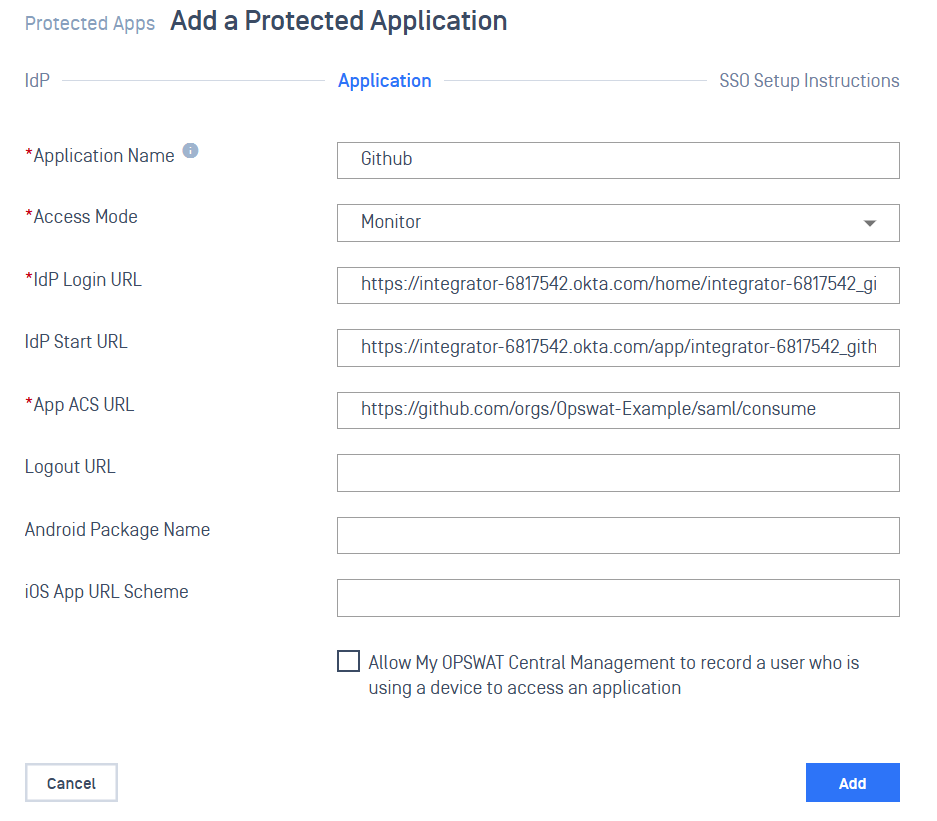
- Enter the required fields
- Application: application name, for example: Github
- IdP Login URL: fill in the link that you have from Step 1.6
- IdP Start URL: fill with the link that you have from Step 1.8
- App ACS URL: is the Gihub single sign-on post back URL of your organization's Github, format is https://github.com/orgs/<your organization name>/saml/consume
- Access Mode: pick an access mode you prefer. See details on the access modes at Step 2. Add protected applications with IdP Method
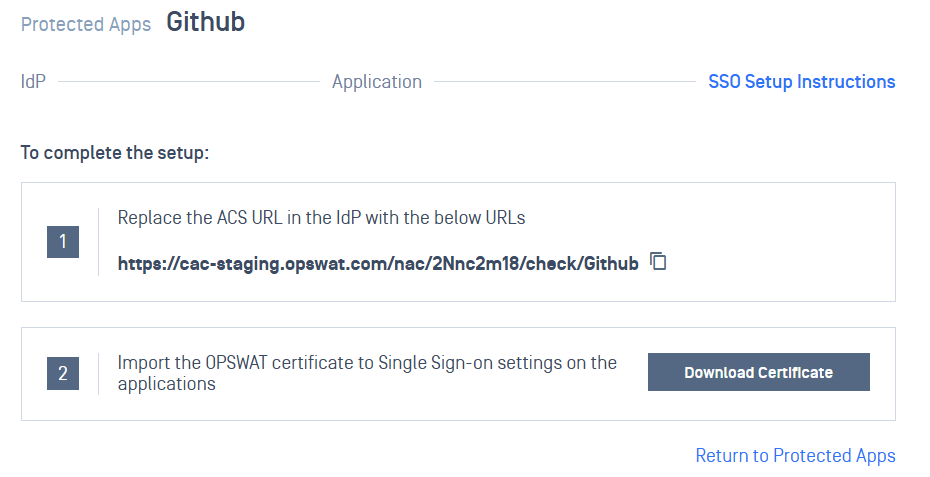
- After saving successfully, a SSO setup instruction will be shown, copy the ACS URL My OPSWAT Central Management generated there and download the OPSWAT Certificate. Note that this information can be found in the protected app's details later.
Step 3. Update Okta Application
- Navigate to the application created in Step 1
- Click on General tab, click Edit button under SAML Settings section
- Click Next to go to SAML Settings section and fill the Single sign-on URL with the ACS URL from Step 2.8. Then click Next and Finish
Step 4. Configure SSO On Github
- Login to your Github account and navigate to Settings -> Security -> Authentication security
- Click Enable SAML authentication and fill the required fields:
- Sign on URL: fill with the ACS URL from Step 2.8
- Issuer: fill with the Issuer from Step 1.9
- Public certificate: open the certificate file from Step 2.8 and copy the content then paste to the public certificate box
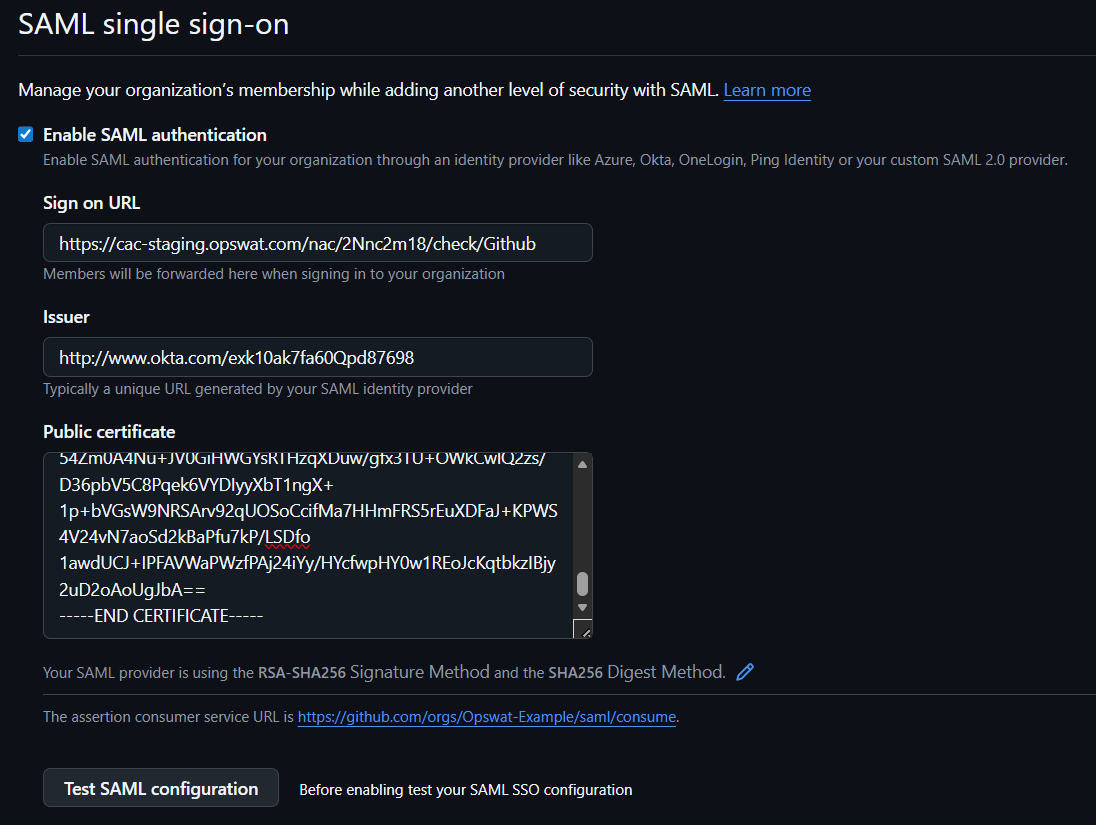
- Click Test SAML Configuration. If the test is successful, click Save to complete the setup.
Type to search, ESC to discard
Type to search, ESC to discard
Type to search, ESC to discard
Last updated on
Was this page helpful?
Next to read:
How It Worksnull
Discard Changes
Do you want to discard your current changes and overwrite with the template?
Archive Synced Block
Message
Create new Template
What is this template's title?
Delete Template
Message