Title
Create new category
Edit page index title
Edit category
Edit link
MFT to MFT
This feature makes it possible to transfer files between different networks using a secure and controlled connection. When enabled, all file and folder operations will be sent from the source MFT to the destination MFT server. Based on the following transfer policies, file operation rules can be specified:
- All files
- Only allowed files
- Only supervisor approved files (only when Supervisor approval feature is enabled)
Supported operations
MetaDefender Managed File Transfer versions should be identical on source and destination server.
The supported file and folder actions can be seen in the table below:
| Operation | File | Folder |
|---|---|---|
| Upload (Create) | ||
| Share | ||
| Move | ||
| Rename | ||
| Delete |
The supported account operations:
| Operation |
|---|
| Guest account creation |
| Guest account update |
| Guest account delete |
While 'Aggregate all file/folder actions' option is disabled make sure the creator user exists on the destination Managed File Transfer.
Guest accounts created while 'Aggregate all file/folder actions' option is enabled will appear on the destination Managed File Transfer as owned by the user who created the API key
Configuration
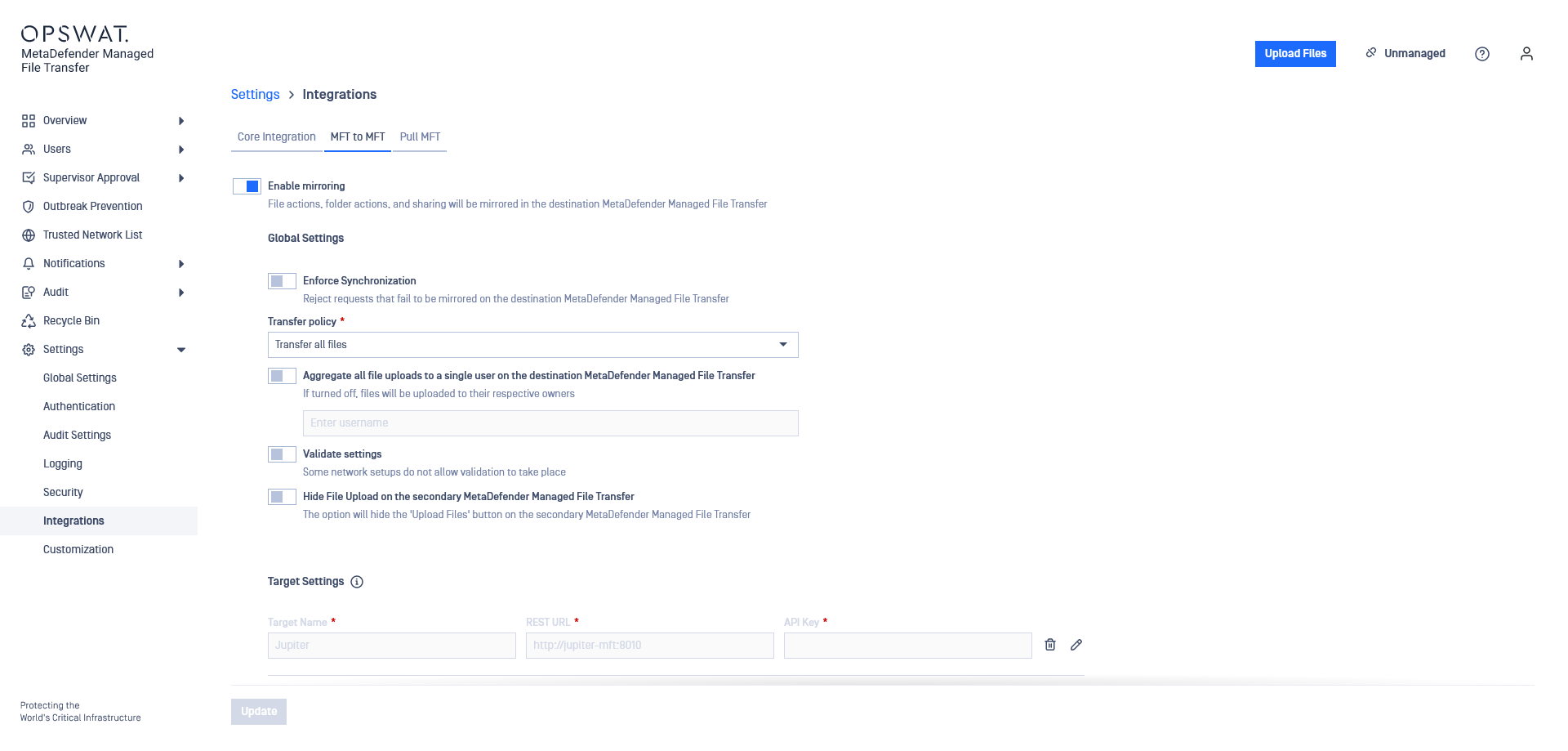
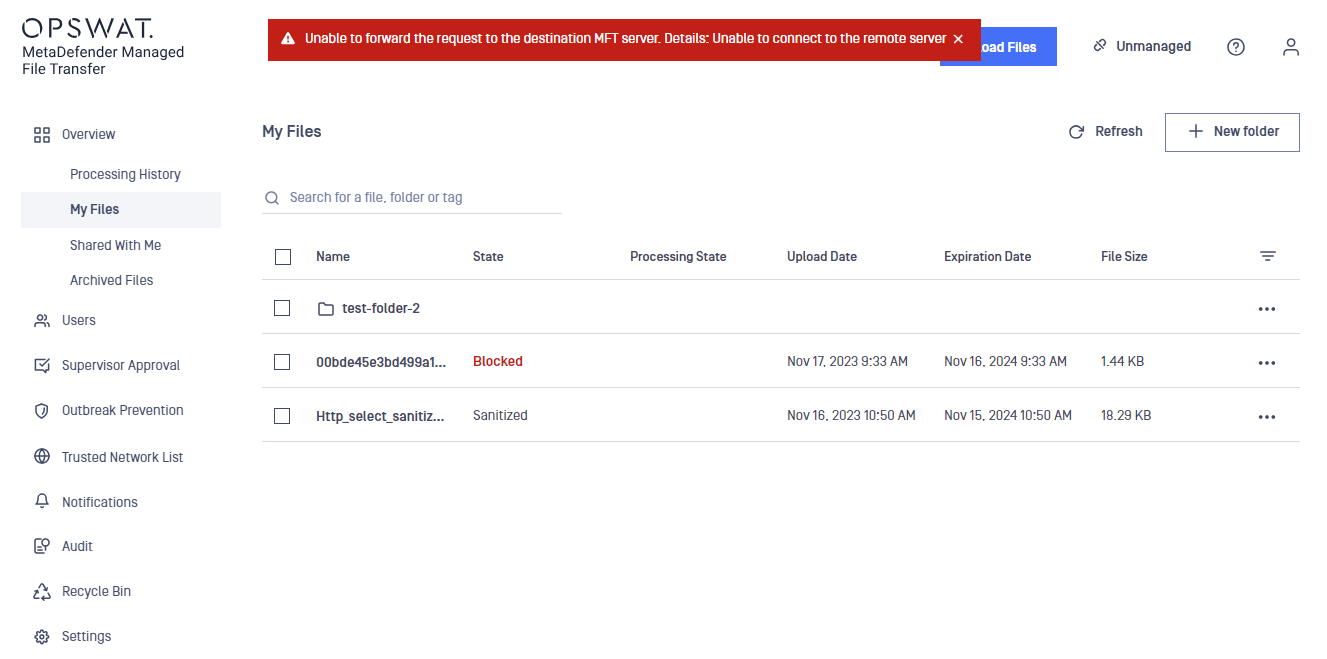
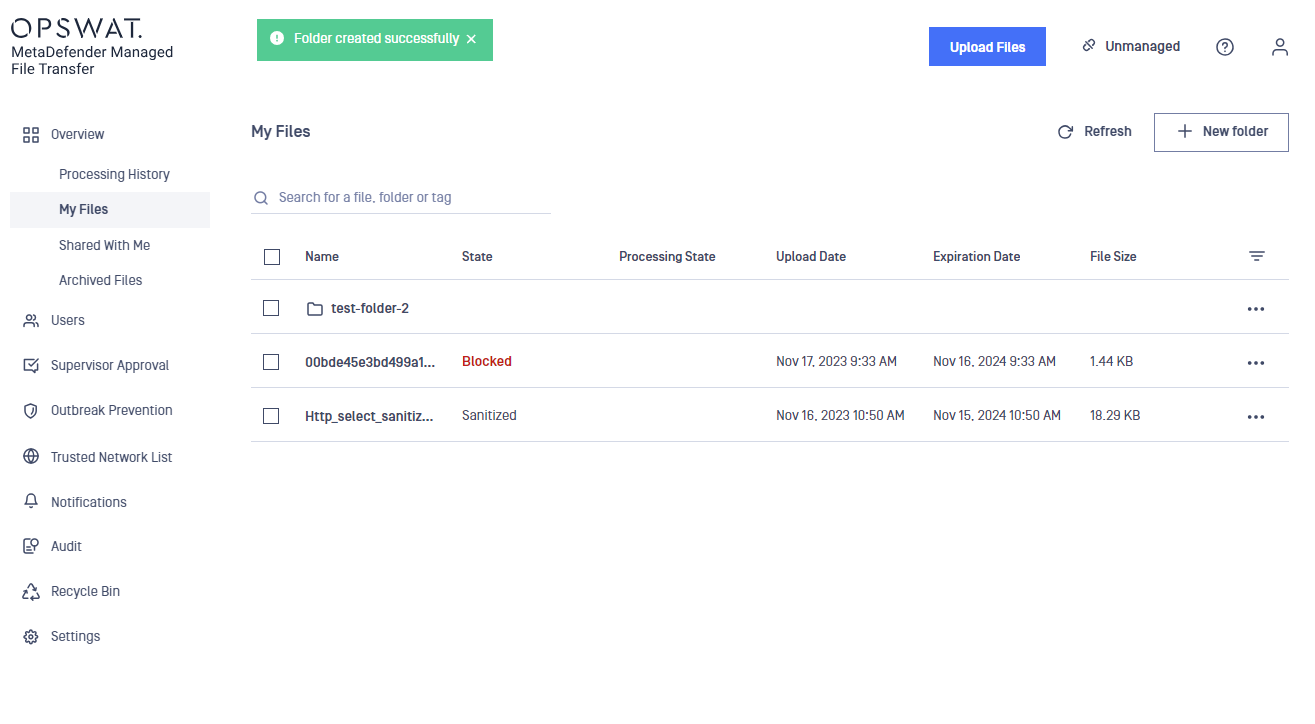
The functionality can be configured by navigating to the Settings page and then select MFT to MFT
MD MFT fully supports bidirectional integration, enabling seamless communication between Managed File Transfer systems in both ways.
By default the feature is disabled. In order to enable the feature and proceed to configuration, the user must switch on "Enable mirroring".
In order to connect with an upstream Managed File Transfer instance, the following steps must be performed:
- Provide the REST URL of the upstream Managed File Transfer instance. The URL must have the following format <schema>://<address>:<port>/[vault_rest].
It is important to provide the absolute URL and path to the destination Managed File Transfer's REST service (i.e. //).
- Log in with an administrator account on the second Managed File Transfer and generate an API key. The generated API key will be used to authorize requests from the source Managed File Transfer.
- Enforce Synchronization: by default this option is disabled, turn on if you want to show bad requests when there is any desynchronization between the two Managed File Transfers
Transfer policy configuration specifies which files should be transferred:
- Transfer all files
- Transfer only allowed files
- Transfer only supervisor approved files (only if Supervisor approval feature is enabled):
- A file is considered supervised if:
- the file is approved by the required supervisors
- the file is revoked by a supervisor
- the file is revoked by an administrator
- Files that have been blocked by MetaDefender Core can be supervised only if they receive an administrator approval
- All files in a group transfer must be supervised before the request can be forwarded to the upstream Managed File Transfer instance. This includes files stored in the recycle bin.
- A file is considered supervised if:
Administrators can now revoke blocked files, regardless of ownership.
Prior to version 3.1.0, there was no way to signal if an administrator had inspected a blocked file. An administrator could only approve a blocked file, thus making it available to supervisors.
The Supervisor Approval feature must be enabled, in order for the Transfer only supervisor approved files policy to work as expected.
If the feature is turned off, the following validation error will be displayed, and the update button will be disabled.
Future file uploads will not be transferred to the destination Managed File Transfer until either of the following steps is made:
- supervisor approval is enabled
- other transfer policy is selected
(Optional) Aggregate all file/folder actions to a single user. All forwarded actions will be interpreted as if the impersonated user requested them. For example, files will be uploaded to the impersonated user's account regardless of the user who initiated the actions on the source Managed File Transfer.
The impersonated user must exist on both Managed File Transfer instances. This implies that both instances must integrate with the same Active Directory or have the same local accounts created. If the impersonated user does not exist then all requests will be done on behalf of the user which generated the API key.
Guest accounts created with impersonation will be owned by the impersonated user, or the API key owner in case the impersonated user doesn't exist on the destination Managed File Transfer.
Guest welcome notifications (if configured for the destination Managed File Transfer) however will be sent to the email address of the guest account and the creator on the first Managed File Transfer.
- (Optional) Validate settings - If enabled, an initial connection test is performed to ensure that the settings are valid. If disabled, no attempt is made to validate the configuration. This can be useful when responses from the other network are not allowed.
In the case, a data diode is deployed between the two Managed File Transfer servers it may be impossible to receive a response from the second Managed File Transfer. The validation feature will have to be manually turned off in order for the setup to work.
- (Optional) Hide file upload on the secondary Managed File Transfer - If enabled, the file upload button within the destination Managed File Transfer becomes hidden. This action effectively removes the option for users to upload files through the destination Managed File Transfer's interface.
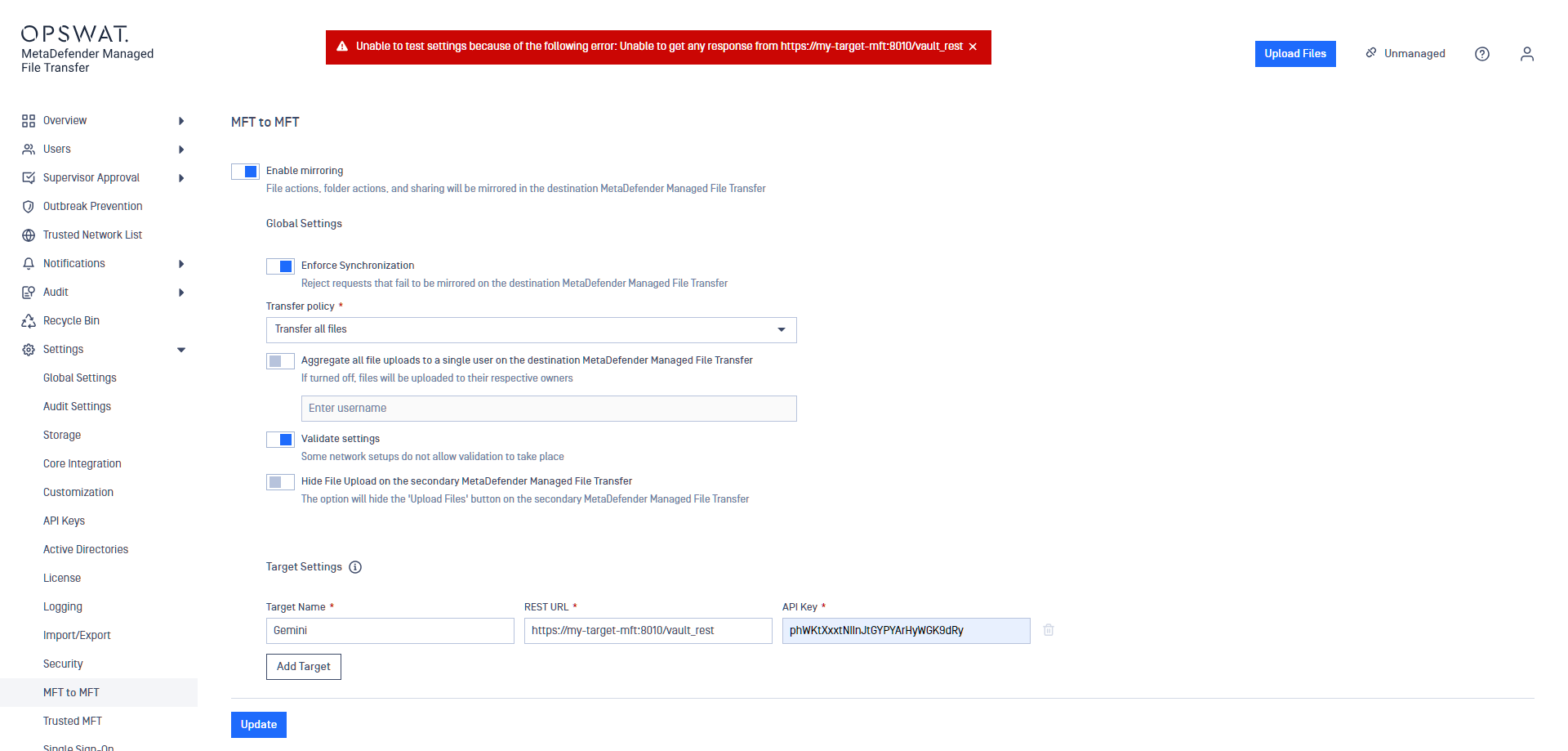
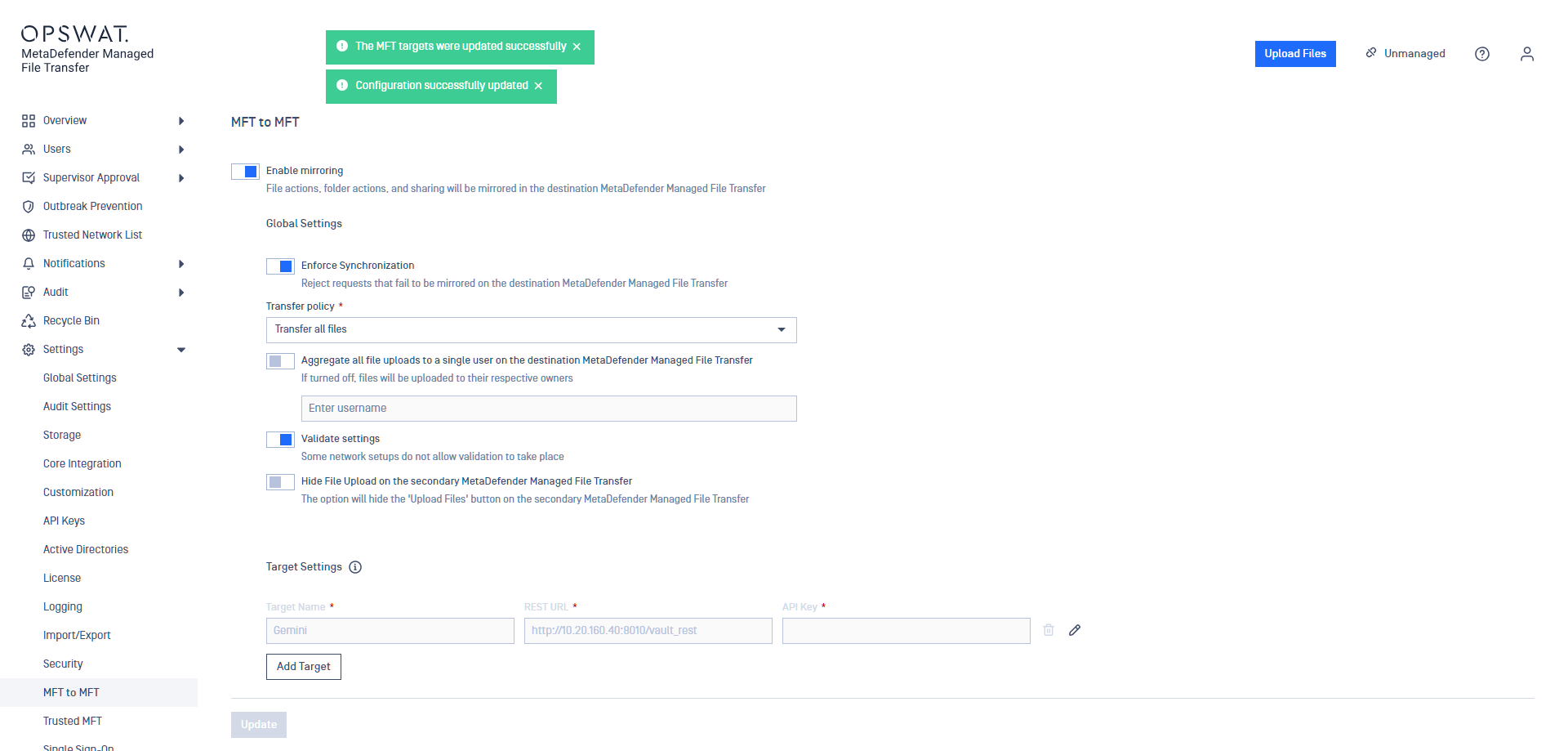
Multi-MFT
With adding multiple targets a multi-MFT solution can be configured.
From v3.6.2 all kind of users operations are forwarded except External Users.
Guest account related operations are forwarded to the specified targets.
All other account related operations are broadcasted to all targets.
If this mode is enabled, when creating a guest, then multiple targets can be specified. The guest account will be created on all targets.
When editing a guest, the targets can be modified. Already uploaded files will be synchronized to newly added target(s).
"Hide File Upload..." setting is not supported in this scenario.
In case "Enforce Synchronization" is enabled an operation will only fail if it fails to be completed on all target.
Detailed information about Guest user management in this case can be found in the End-User Guide.