Overview MetaDefender Managed File Transfer Release Notes
Getting Started
Deployment & Usage
Support
Configuration
v3.5.0
Search this version
Configuration
Configuration
Title
Message
Create new category
What is the title of your new category?
Edit page index title
What is the title of the page index?
Edit category
What is the new title of your category?
Edit link
What is the new title and URL of your link?
Integrate with Okta
Summarize Page
Copy Markdown
Open in ChatGPT
Open in Claude
Connect to Cursor
Connect to VS Code
Below you can find a step by step tutorial on how to integrate Okta IdP with MetaDefender Managed File Transfer using the OpenID Connect protocol.
- Sign into Okta and navigate to admin dashboard
- Go to Applications and select Create App Integration

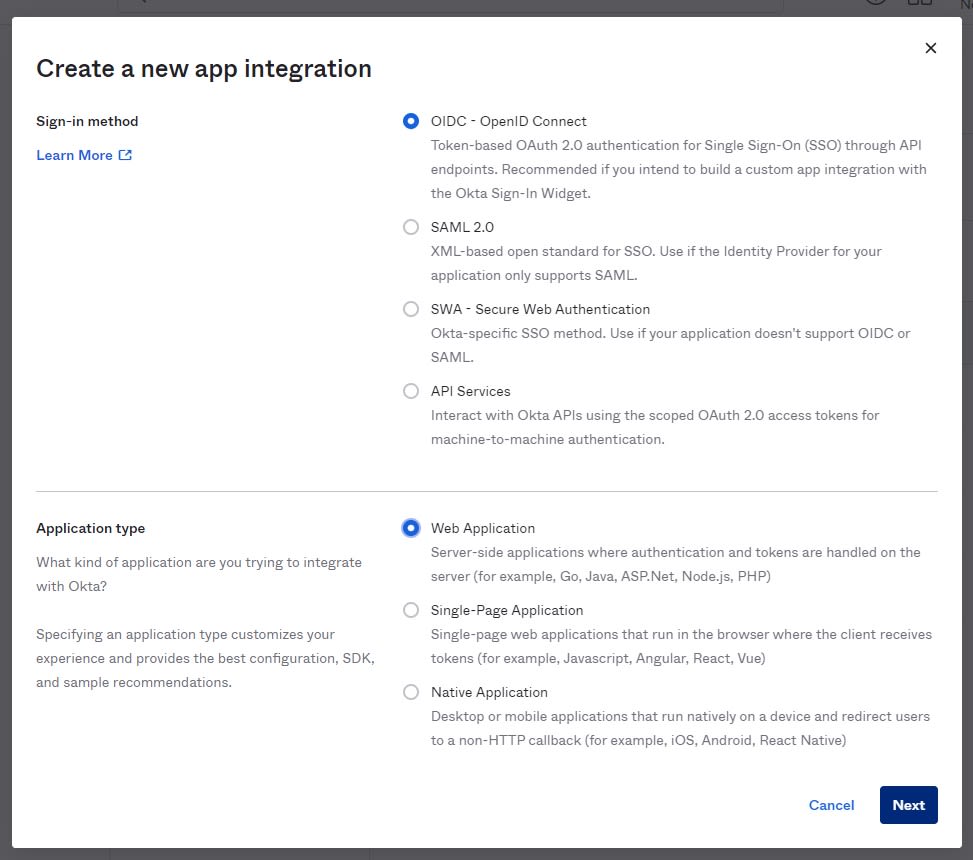
- Choose OIDC, Web application and click Next
- Let’s configure the application settings. Give the application a name like for example “Managed File Transfer App”.
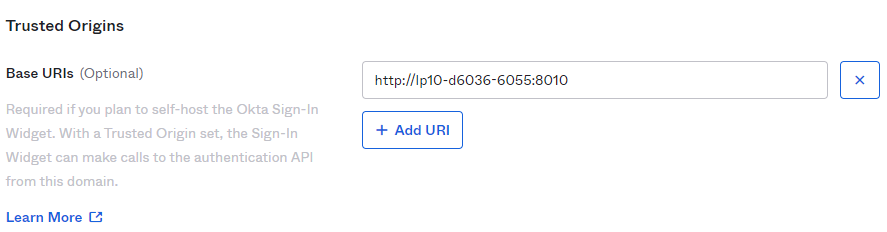
- Base URI should point to the location of the Managed File Transfer machine
- To find the Login redirect URI
- Go to MetaDefender Managed File Transfer web console and navigate to Settings → Single Sign-On
- Turn on Enable Single Sign-On
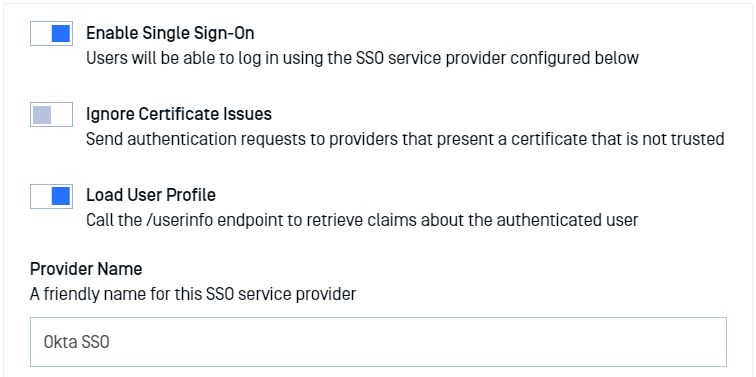
- Don’t turn on Ignore Certificate Issues as Okta will provide a trusted certificate
-
Turn on Load User Profile such that MetaDefender Managed File Transfer can acquire the following claims
- name
- preferred_username
- given_name
- family_name
- Authority should point to your Okta Org. URL. You can find this URL in the Okta dashboard
- IP Address or Domain should point to the location of your Managed File Transfer instance. Once you fill this information, Managed File Transfer will automatically generate the Redirect URI
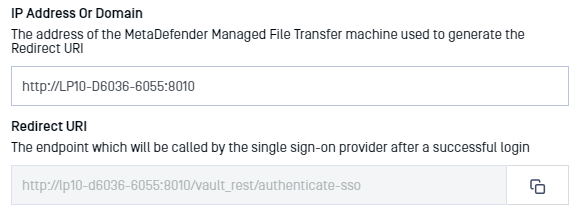
- Copy the Redirect URI and go back to the Okta Application Settings and paste it (step 6)
- You should now have a configuration similar to this:
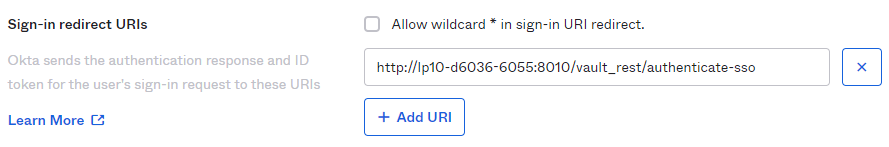
- Logout redirects URIs do not need to be configured as Managed File Transfer doesn’t support single log out for the moment.
- You can configure Group assignments as desired
- Grant type allowed: please make sure that Authorization Code is checked
- Click Done to finish the process of creating an OKTA app.
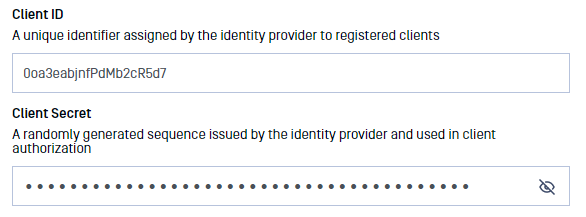
- You will be redirected to the app that you just created. On the General tab, scroll down to the Client Credentials section
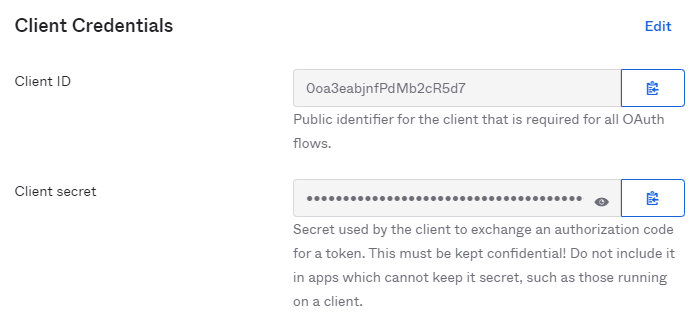
- Copy the Client ID and Client secret so we can enter them in MetaDefender Managed File Transfer SSO configuration.
- Administrator Emails: if some of the Okta users should have administrative rights in Managed File Transfer, please enter a list of emails in this field. MetaDefender Managed File Transfer will compare the email of users that login from Okta against the provided list to determine if a user should be an administrator
- You don’t need to specify additional integration scopes
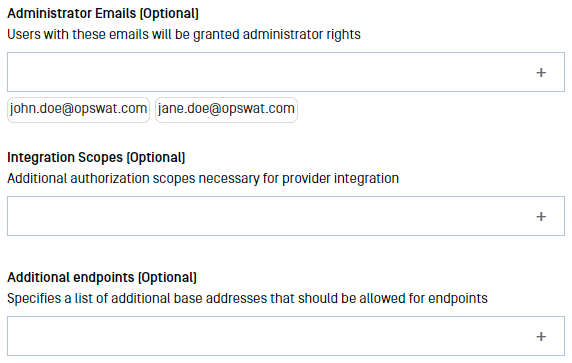
- If everything is ready, click Update.
Testing the integration
To test the integration:
- Log out of MetaDefender Managed File Transfer
- You will notice that there is a new Sign In with SSO button on the login page
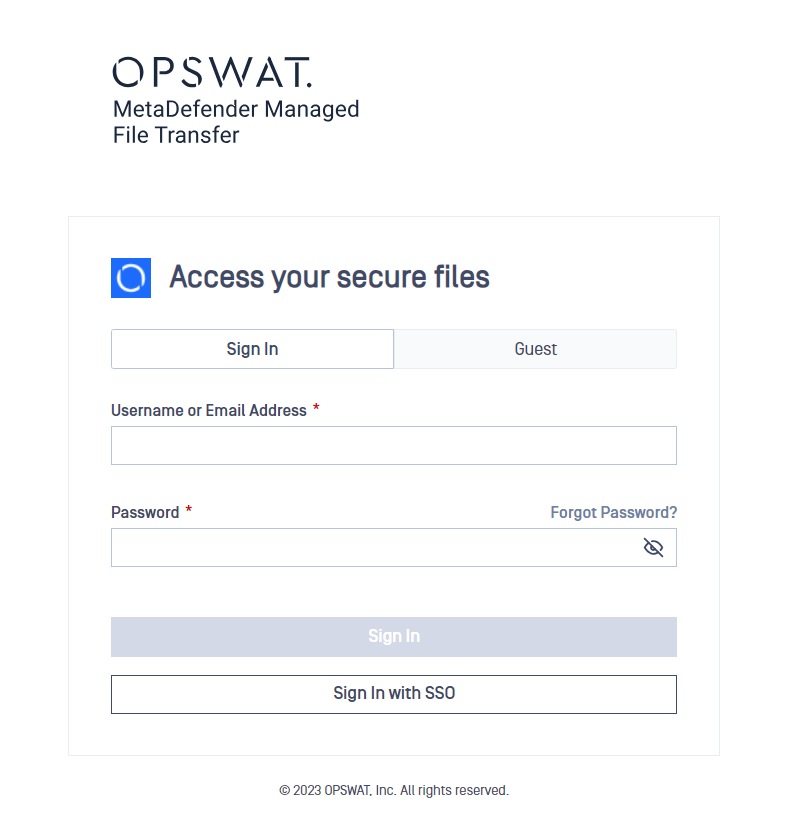
- Click Sign In with SSO. You should be redirected to Okta to login. Once logged in, you will be redirected back to MetaDefender Managed File Transfer and automatically logged in.
VariableType to search · ESC to discard
GlossaryType to search · ESC to discard
InsertType to search · ESC to discard
No matches
Last updated on
Was this page helpful?
Next to read:
Integrate with Active Directory Federation Servicesnull
Discard Changes
Do you want to discard your current changes and overwrite with the template?
Archive Synced Block
Message
Create new Template
What is this template's title?
Delete Template
Message