Security
Quick Overview
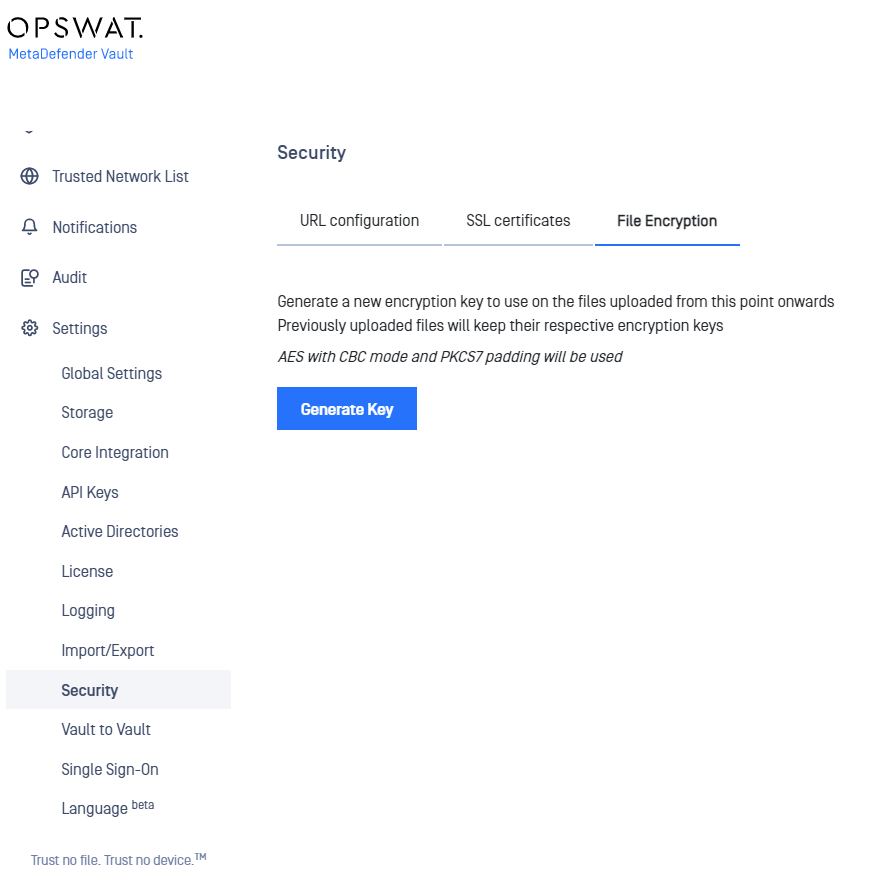
Starting with v2.0.6, there is a new settings page that allows users to configure all security aspects of the product.
The old procedure is still supported and details can be found here.
Step by step guide for enabling HTTPS
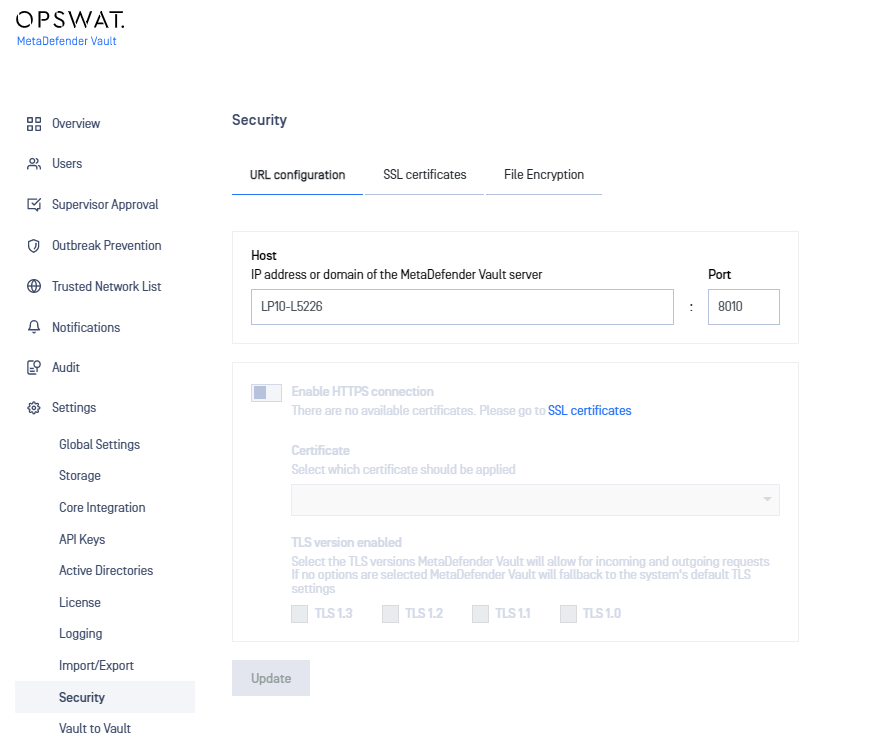
- Navigate to Settings → Security.
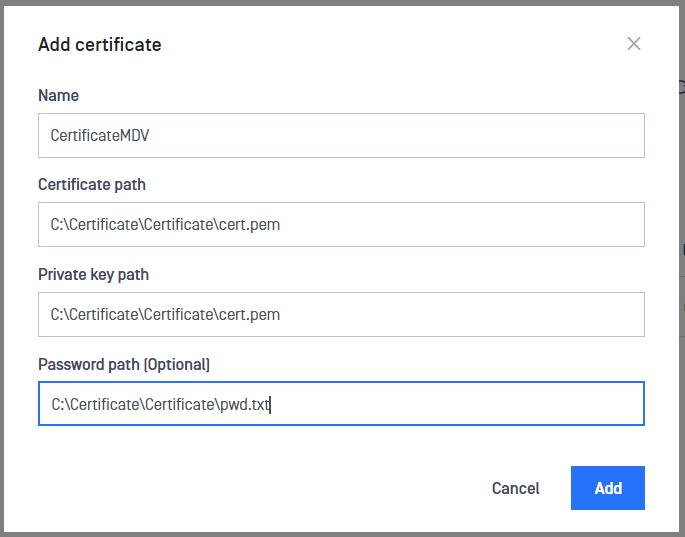
- It is necessary to create an SSL/TLS certificate before activating HTTPS so please navigate to the Manage Certificates tab and click ADD CERTIFICATE. A panel will open to the side prompting for the required input. Fill out the required fields and click ADD. Note: Please refer to Information regarding certificates in order to obtain a certificate and certificate key.
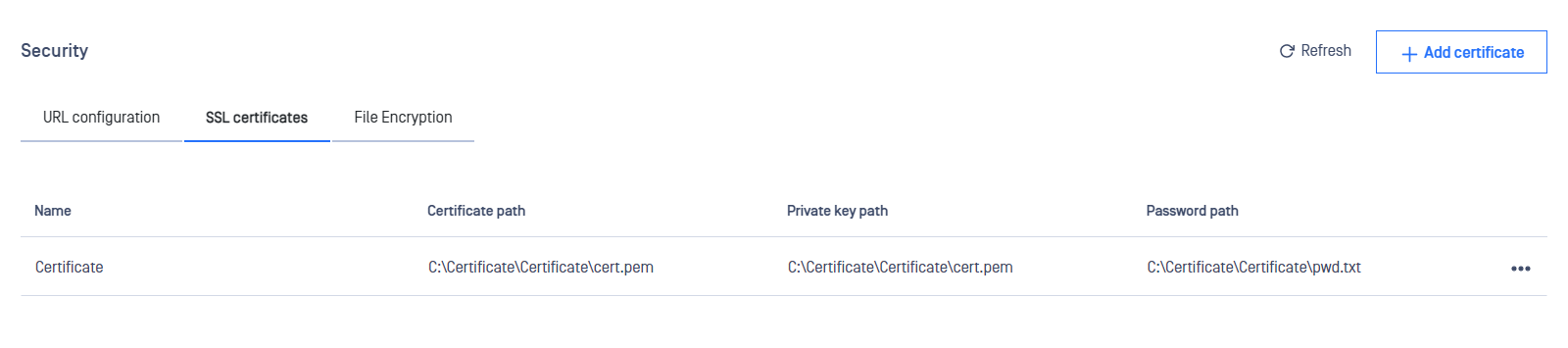
- The newly created certificate should now appear in the available certificates list.
- Navigate back to the Configure tab and observe that it is now possible to enable HTTPS.
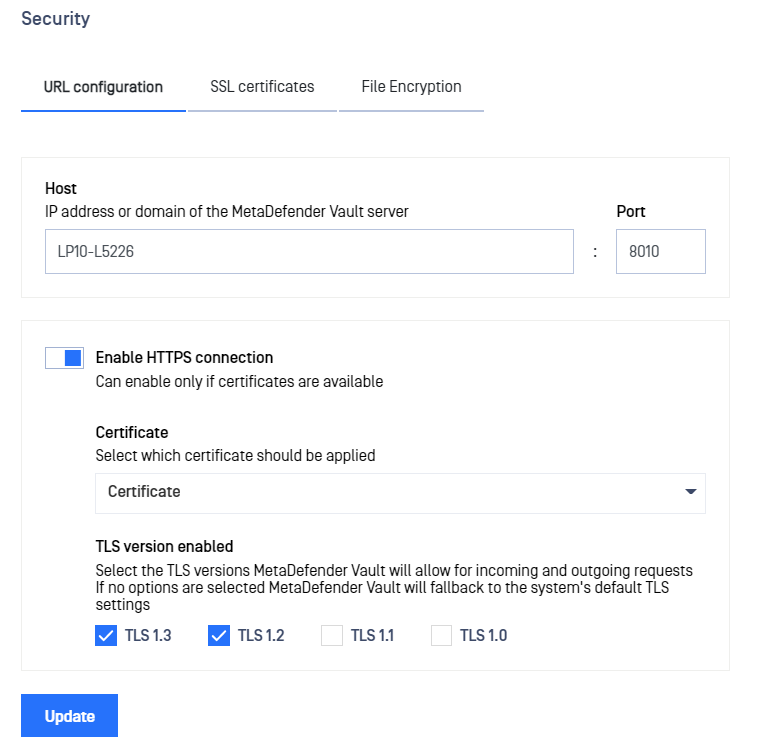
- Fill in the desired settings in the configuration window. Note that you can find more information about each field below.
The table below describes in detail each setting:
| Name | Description |
|---|---|
| Host | DNS name or IP Address of the machine running the MetaDefender Vault server. A DNS name will cause the server to listen on all network interfaces. An IP address will bind the server to that particular value. Note: this value is also used to generate links in email notifications. |
| Port | The port used to listen for connections. |
| Certificate | Name of the certificate created on step 2. |
| TLS version | TLS protocol version to use. By default TLSv1.2 and TLSv1.3 will be enabled if the operating system allows it. Connections with clients, that do not support at least one of the configured TLS versions, will fail |
- Click UPDATE and wait to be redirected to the new URL.
Enforcing TLS version
If you're upgrading from a previous version or deliberately leave all TLS options unchecked that will instruct Vault to default to the following:
- for outbound connections (i.e requests made by Vault) will use the operating system default TLS protocol
- for inbound web requests Vault's web server (NGINX) will default to TLS v1.2 or TLS v1.3
If you wish to enforce a particular TLS version please select only that option.
Key rotation
By default the product uses a randomly generated cryptographic key to encrypt uploaded files.
In order to generate a new cryptographic key please follow these steps:
- Navigate to Settings → Security → File Encryption.
- Click on the Generate Key button.
- A window will appear asking the client to confirm the action.
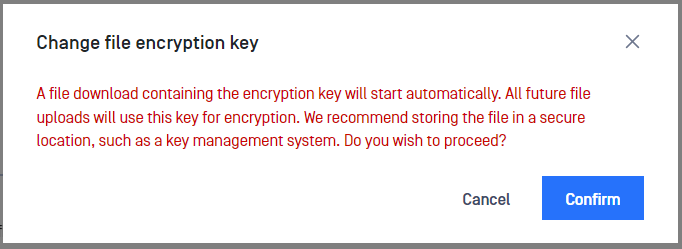
- Selecting Cancel will abort the request and no new key will be generated. Selecting Confirm will lead to step 5.
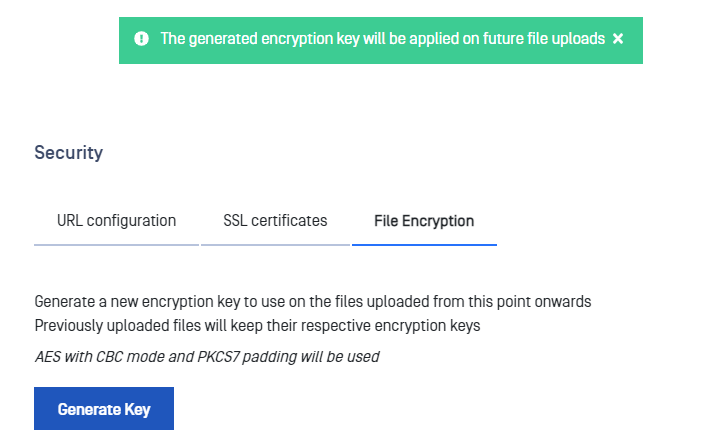
- The new cryptographic key has been generated.
- User agent will prompt the client to store the newly generated key in a file. If the client dismisses this step by mistake, he/she must generate a new encryption key. The previous key will be removed automatically by the system.
The system uses the AES algorithm with CBC mode and PKCS7 padding to generate cryptographic keys. Newly created cryptographic keys are stored in the database as UTF8-encoded hexadecimal characters.
Once a new encryption key is generated, all subsequent file uploads will use the newly created key for encryption. Files that were uploaded prior to the creation of the new key will remain encrypted with the old encryption keys.
Note: It is not possible to manually retire previous encryption keys. The system will automatically remove obsolete keys when all files encrypted with those keys are deleted.
Example
- File1 and File2 are encrypted with key A.
- User generates key B => key A becomes obsolete.
- User uploads File3.
- File3 is encrypted with key B.
- System does a cleanup check and sees that key A is obsolete but it is still used to encrypt files File1 and File2 so the key is not removed.
- User generates key C => key B becomes obsolete like key A.
- User deletes files File1 and File3.
- System does a cleanup check and erases key B (obsolete + no encrypted files). Key A still has one file (File2) encrypted with it so is left alone. Key C has no files encrypted with it but is the active key so it is left alone.

