Title
Create new category
Edit page index title
Edit category
Edit link
Release Notes
| Version | 5.13.0 |
|---|---|
| Release date | 11 March 2026 |
| Scope | Focused on new functionalities, enhancements and bug fixes |
Before upgrading MetaDefender ICAP Server to v5.10.0 or newer from v5.6.0 or earlier, make sure you review the Release Notes and the following Documentation:
New Features, Improvements and Enhancements
| Details | |
|---|---|
| Improve capability in handling ICAP messages |
|
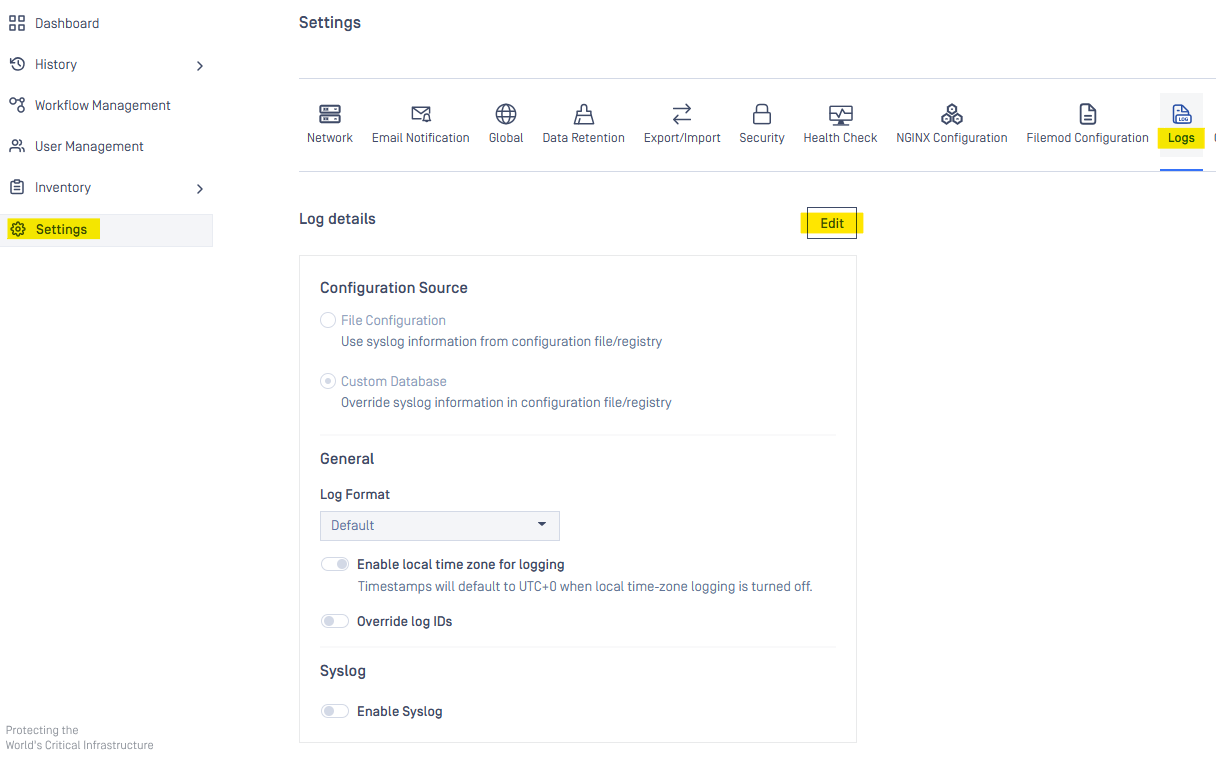
| Support Advanced Log Configurations on Web Console | Starting with MetaDefender ICAP version 5.13.0, the following advanced log configurations including local time zone, Common Event Format, product logs and syslog settings are supported This UI configuration is also support for CM10 integration
|
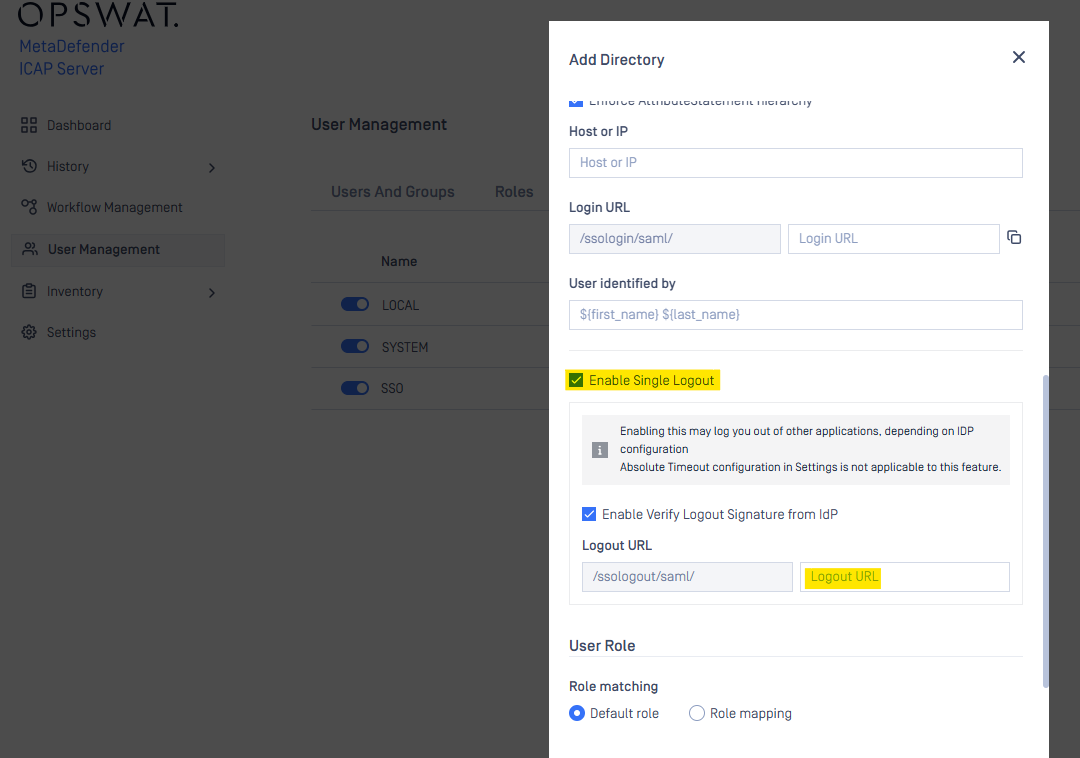
| Enhanced authentication experience | Implemented Single Logout (SLO) support within Single Sign-On (SAML), allowing users to securely end all active sessions across connected applications with a single action, improving both security and convenience refer to Enable Single Logout
|
| Security Enhancements | Upgraded third-party libraries for improved security:
Applied additional security hardening measures across the product to prevent vulnerabilities and strengthen overall protection. |
| Usability Improvements | New Configuration Option:
More detail, refer to Configuration file |
Bug Fixes
| Details | |
|---|---|
| Fixed timeout when exporting processing history | Resolved a timeout error that occurred during export of large processing histories |
| Fixed crash when deleting a support package via the UI | Fixed an edge case where deleting a support package via the UI could cause the service to crash |
| Minor Fixes | Resolved various UI cosmetic issues and minor fixes |
Known Limitations
| Details | |
|---|---|
| Proxy Configuration | Currently, HTTPS proxy configuration is not supported. |
| SAML Directory (SSO Integration) Limitations | In v5.5.0, users cannot create a new SAML directory via the web UI.
|
| Stability Issues on Red Hat/CentOS (Kernel Version 372) | MetaDefender ICAP Server v5.1.0 or newer may encounter stability issues on Red Hat/CentOS systems running kernel version 372. Solution: Upgrade to kernel version 425, where Red Hat has resolved this issue. |
| MetaDefender ICAP Server's NGINX Web Server Fails to Start with Weak Cipher Suites for HTTPS | From v5.1.0, OpenSSL 1.x has been replaced with OpenSSL 3.x — across the product and its dependencies — to enhance security and address vulnerabilities. As part of this upgrade, NGINX's OpenSSL 3.x in MetaDefender ICAP Server now enforces stricter cipher policies and rejects all weak cipher suites. The web server now only accepts "HIGH" encryption cipher suites https://www.openssl.org/docs/man1.1.1/man1/ciphers.html (MD5 and SHA1 hashing based are also not accepted). As a result, if you have already configured MetaDefender ICAP Server for HTTPS using a weak SSL cipher with your certificate, the server will not start due to the enforced security policies in NGINX's OpenSSL 3.x. |
| no_proxy Configuration | Starting with MetaDefender ICAP Server v5.1.0, the no_proxy setting must support CIDR for IP addresses.
For more details, see No Proxy configuration. |
| TLS Connectivity to MetaDefender Core on Debian | On Debian OS, MetaDefender ICAP Server v5.1.0 requires the two following commands to enable TLS communication with MetaDefender Core:
Resolution: Upgrade to MetaDefender ICAP Server v5.1.1, where the issue is resolved. |
| TLS 1.3 Not Supported on Windows Server 2012 | TLS 1.3 is not supported on Windows Server 2012 due to limitations with Schannel SSP. Reference |