Operating
3.5.1
Search this version
Operating
Operating
Title
Message
Create new category
What is the title of your new category?
Edit page index title
What is the title of the page index?
Edit category
What is the new title of your category?
Edit link
What is the new title and URL of your link?
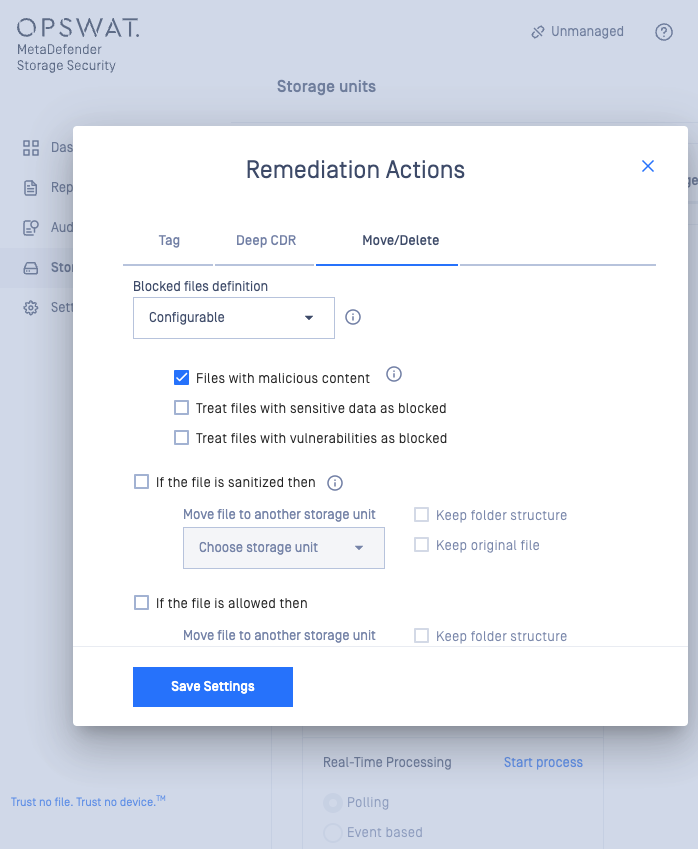
Remediation Actions
Copy Markdown
Open in ChatGPT
Open in Claude
Configuring Remediation Actions for Storage Units in MetaDefender Storage Security
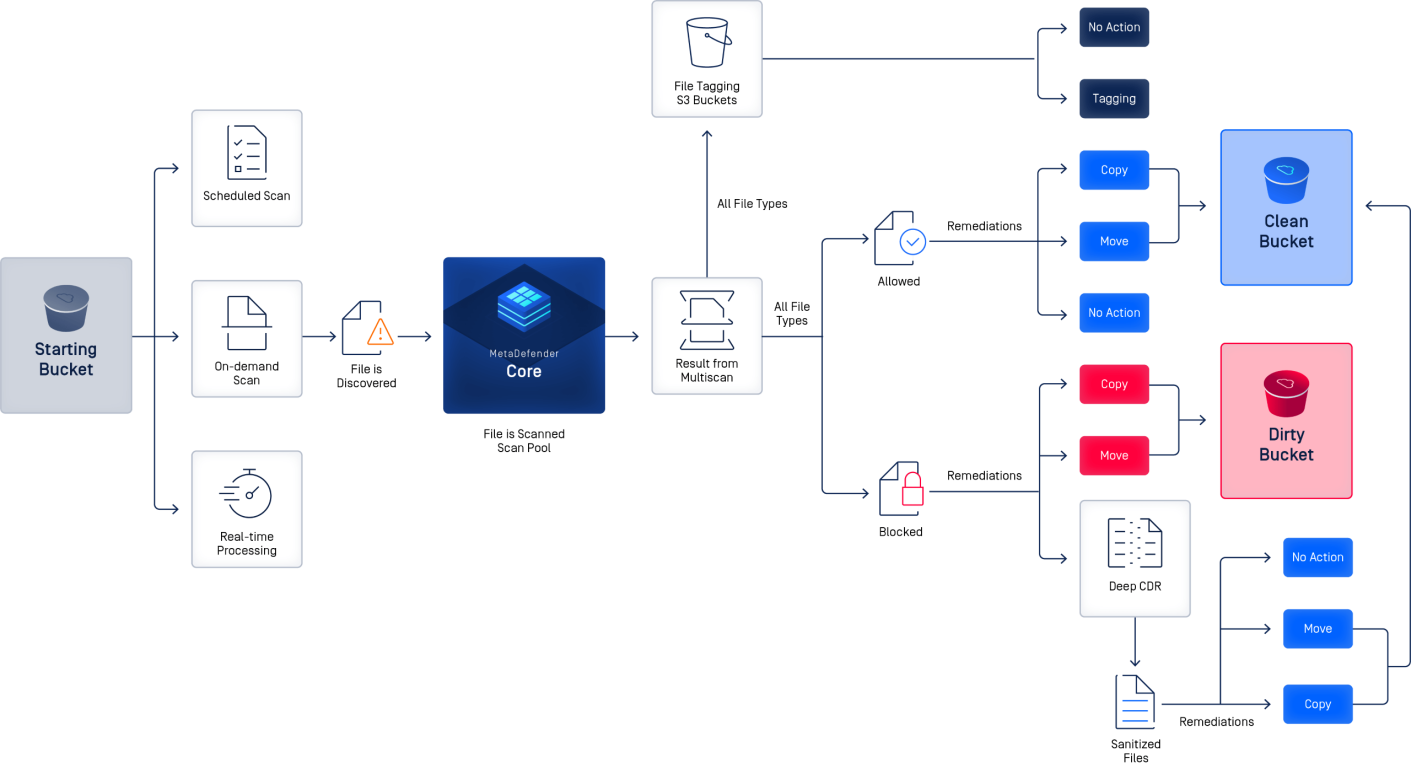
This section outlines how to configure remediation actions for your Storage Units (in this example for Amazon S3) within MetaDefender Storage Security, a step that allows users to automate responses to threats detected by multiscanning.
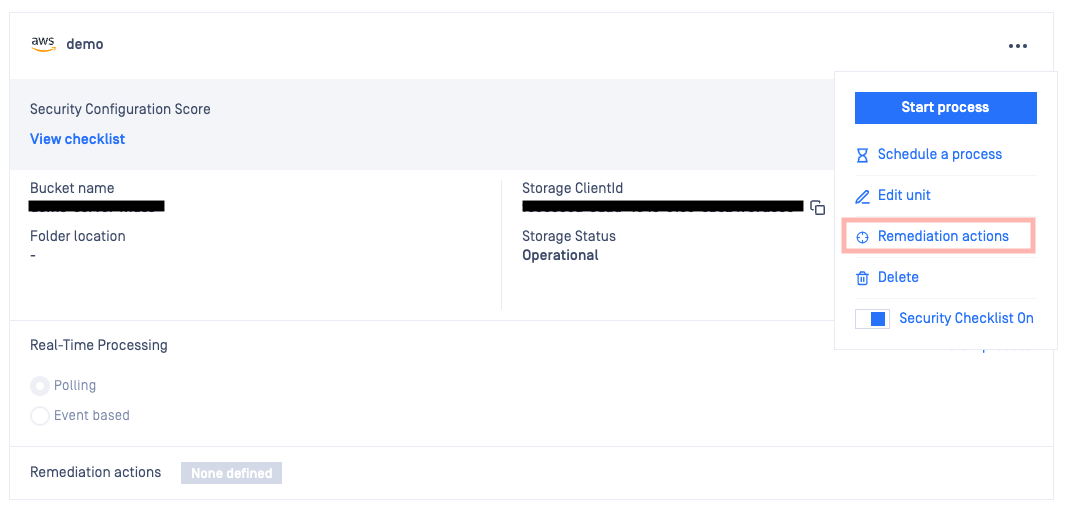
How to access Remediation Actions
- Navigate to the desired Storage Unit tile, this tile provides an overview of your storage unit's configuration and status.
- Locate the "Remediation actions" option, this is found within the tile, represented by a More options icon
Configuration Options
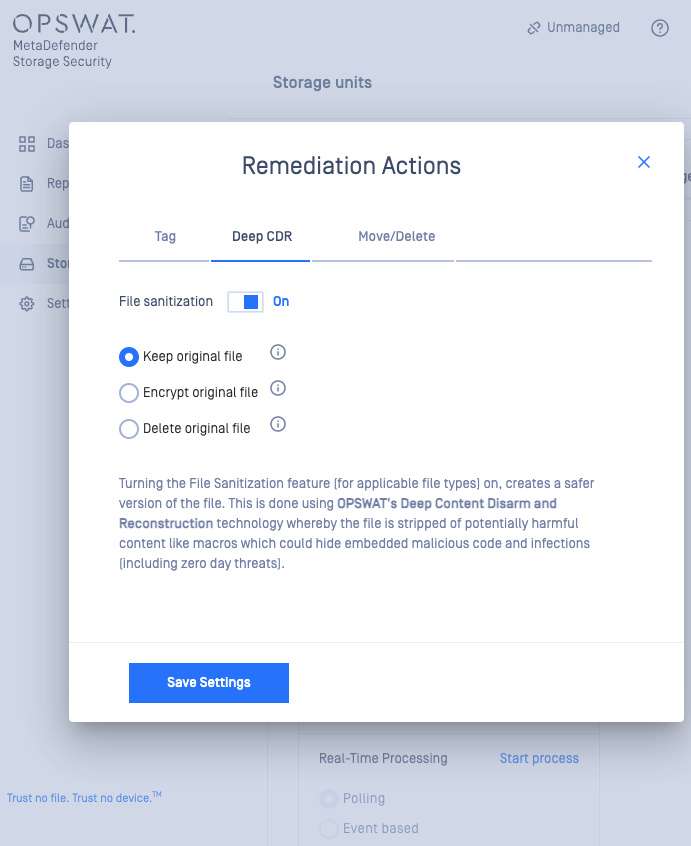
Once you've accessed the "Remediation actions" settings, you can define how MetaDefender Storage Security should handle files based on their scan results. The following options for Remediation Actions are available:
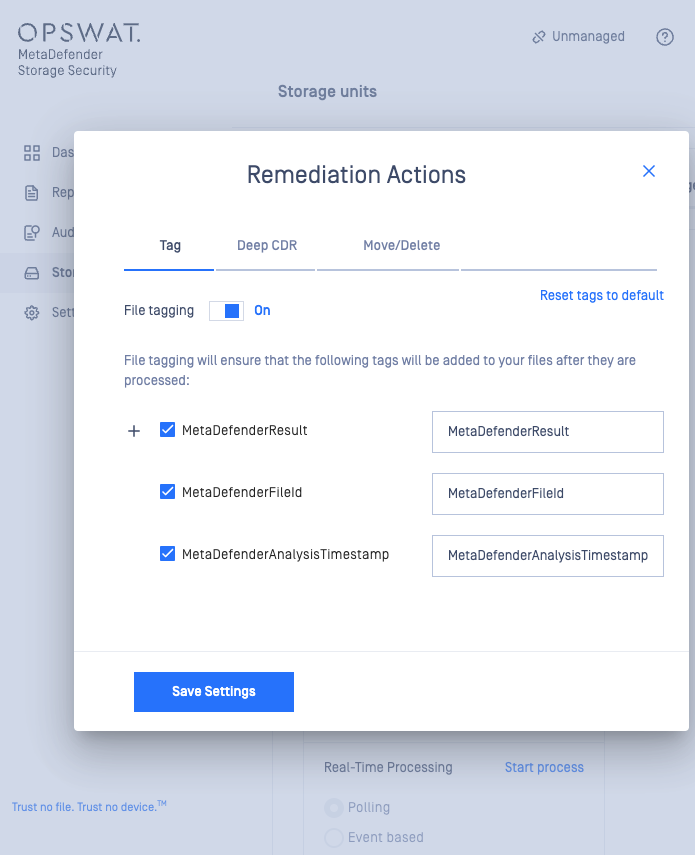
- Tagging helps with organization and further automated actions for the storage unit and applies specific tags to files based on their scan results.
- Move allows users to transfer files to a different bucket based on the scan outcome (e.g., move infected files to a quarantine bucket).
- Copy creates a copy of the file in another location while retaining the original and commonly used for archiving or further analysis.
- Delete permanently removes the file from the storage unit and needs to be used with caution, especially for critical data.
Configuring Actions Based on Scan Results
Users can configure different actions for each possible scan result:
- Clean : the files that are identified as safe, users might choose to take no action or move them to a designated "clean" bucket.
- Infected : these are the files containing malware and users should consider moving them to a quarantine bucket or deleting them entirely.
- Suspicious : the files that appear to have potentially harmful characteristics, users might opt to move them to a separate location for further analysis or delete them (depending on their tolerance risk level).
- Sanitized : the files that have been processed to remove potentially harmful content, users can can choose to move them to a "sanitized" bucket or leave them in their original location.
Important Considerations
- Make sure that the destination buckets for moved or copied files are properly configured and accessible within your environment (in this case Amazon S3)
- Carefully consider your organization's risk tolerance when configuring deletion actions. Implement safeguards like versioning or backups to prevent accidental data loss.
- Develop a clear tagging strategy to facilitate efficient file management and consistency.
- Regularly review and update your remediation actions and tagging configurations to align with your organizational evolving security needs and policies.
Tagging Options
Users can enable file tagging and select specific tags to be added to their files:
- MetaDefenderResult: This tag will indicate the outcome of the scan (e.g., clean, infected, suspicious).
- MetaDefenderFileId: This tag provides a unique identifier for each scanned file.
- MetaDefenderAnalysisTimestamp: This tag records the time of the file analysis.
Type to search, ESC to discard
Type to search, ESC to discard
Type to search, ESC to discard
Last updated on
Was this page helpful?
null
Discard Changes
Do you want to discard your current changes and overwrite with the template?
Archive Synced Block
Message
Create new Template
What is this template's title?
Delete Template
Message