Title
Create new category
Edit page index title
Edit category
Edit link
Security Checklist
MetaDefender Storage Security offers a checklist of the most common security practices, which if forgotten or misconfigured, can lead to huge security risks.
Note: For now, this feature is only available for Amazon S3 storage units.
| Title | Description | Importance | Notes | ||
|---|---|---|---|---|---|
| 1 | HTTPS (TLS) to access bucket data | Use HTTPS (TLS) to help prevent potential attackers from eavesdropping on or manipulating network traffic using person-in-the-middle or similar attacks. | Critical | ||
| 2 | Authenticated access to buckets | Your buckets should not be publicly available on the internet. They should be accessible only with authentication otherwise your organization is exposed to data leaks or potential cost increases. | Critical | ||
| 3 | Least privilege access principle | Securely control individual and group access to your AWS resources by making sure that used keys only have the required access level. | Major | This check is done at the bucket level. This means that the folder location configured in MetaDefender Storage Security might be compliant, but the check will fail because the bucket contains policies that allow a wildcard identity such as Principal "*" (which effectively means 'anyone') or allows a wildcard action "*" (which effectively allows the user to perform any action in the Amazon S3 bucket). | |
| 4 | Bucket versioning | Versioning is a means of keeping multiple variants of an object in the same bucket. Enable versioning to preserve, retrieve, and restore every version of every object stored in your Amazon S3 bucket. With versioning, you can easily recover from both unintended user actions and application failures. | Major | ||
| 5 | Bucket access logging | Enable access logging to help identify security issues. | Major | ||
| 6 | Server-side encryption | Request Amazon S3 to encrypt the objects in your bucket before saving on disks in its data centers, and then, decrypt them when you download the objects. Server-side encryption can help reduce risk to your data by encrypting the data with a key that is stored in a different mechanism than the mechanism that stores the data itself. | Major | ||
| 7 | Cross-region data replication | Although Amazon S3 stores your data across multiple geographically diverse Availability Zones by default, compliance requirements might dictate that you store data at even greater distances. Enable cross-region replication (CRR) to replicate data between distant AWS Regions to help satisfy these requirements. CRR enables automatic, asynchronous copying of objects across buckets in different AWS Regions. | Minor | This check will fail when there are replication-rule filters based on object tags, because some of the objects that are not tagged won't be copied across the destination bucket. | |
| 8 | S3 object locking | S3 Object Lock enables you to store objects using a "Write Once Read Many" (WORM) model. Enable S3 Object Lock to help prevent accidental or inappropriate deletion of data. | Minor | In order to enable both Cross-Region data replication and Object lock on a bucket, you will need to contact AWS support. More details here. |
Verify Security Checklist
- Add an Amazon S3 storage unit as described in Add An Amazon S3 Storage
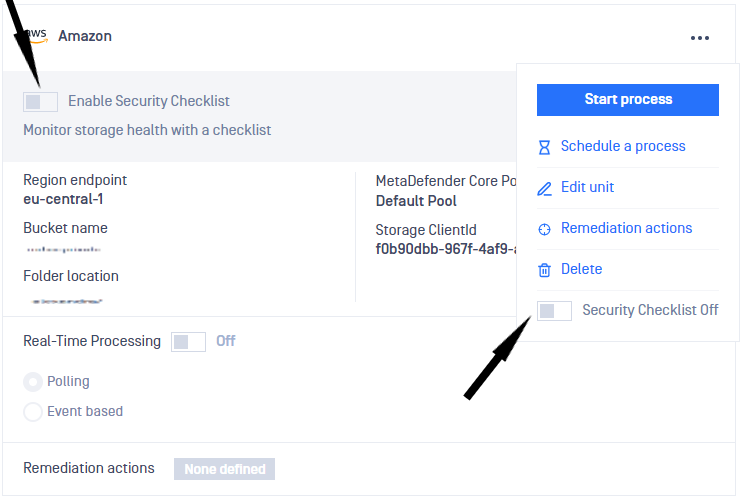
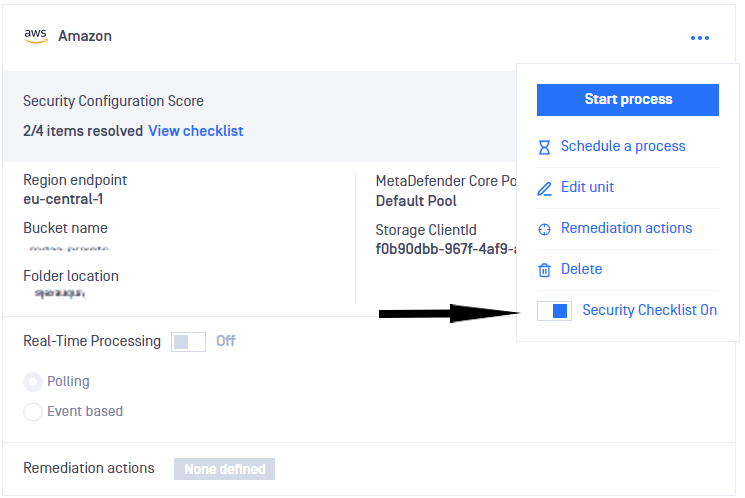
- The security checklist can be enabled either from the storage card, or from the actions dropdown by switching the toggle
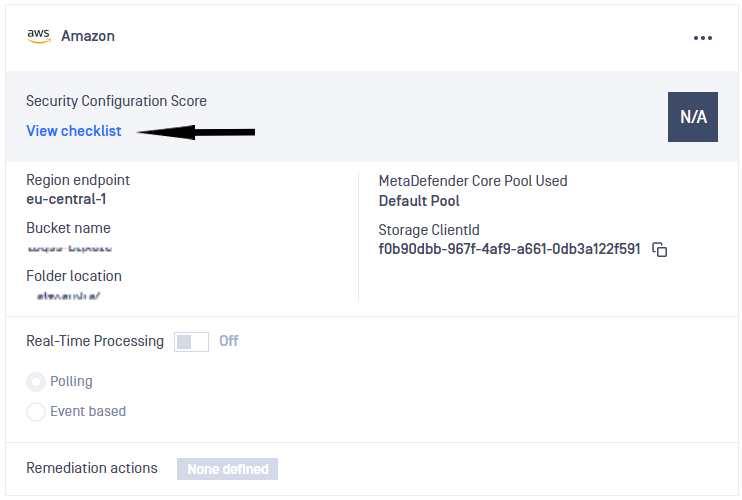
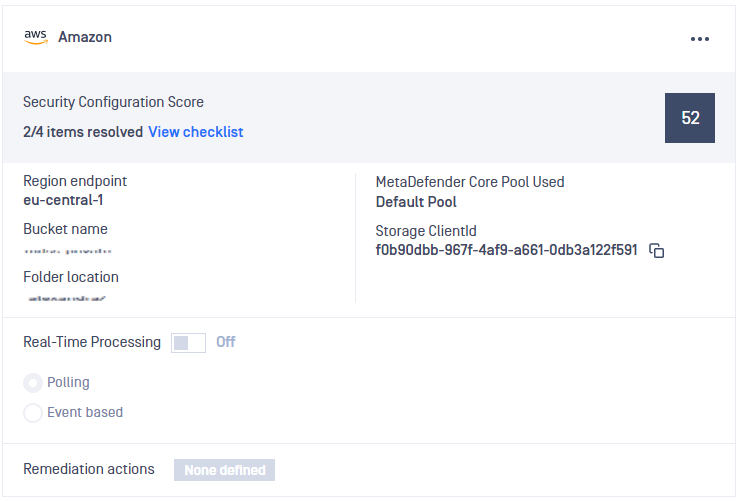
- Click View checklist to inspect the security checklist
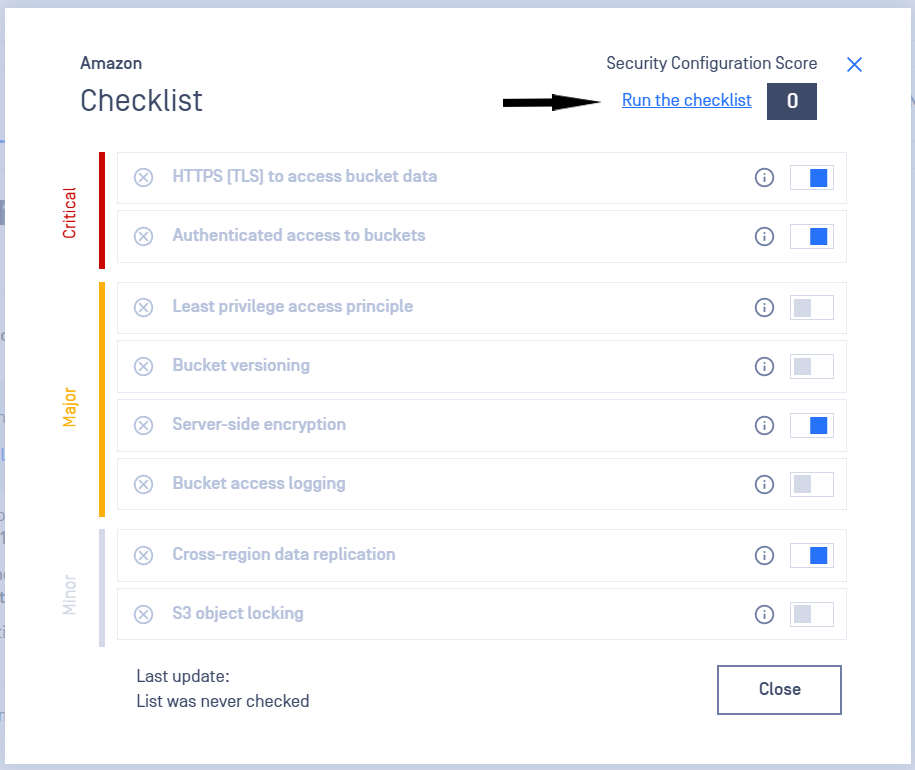
- A modal opens that presents the available security checks
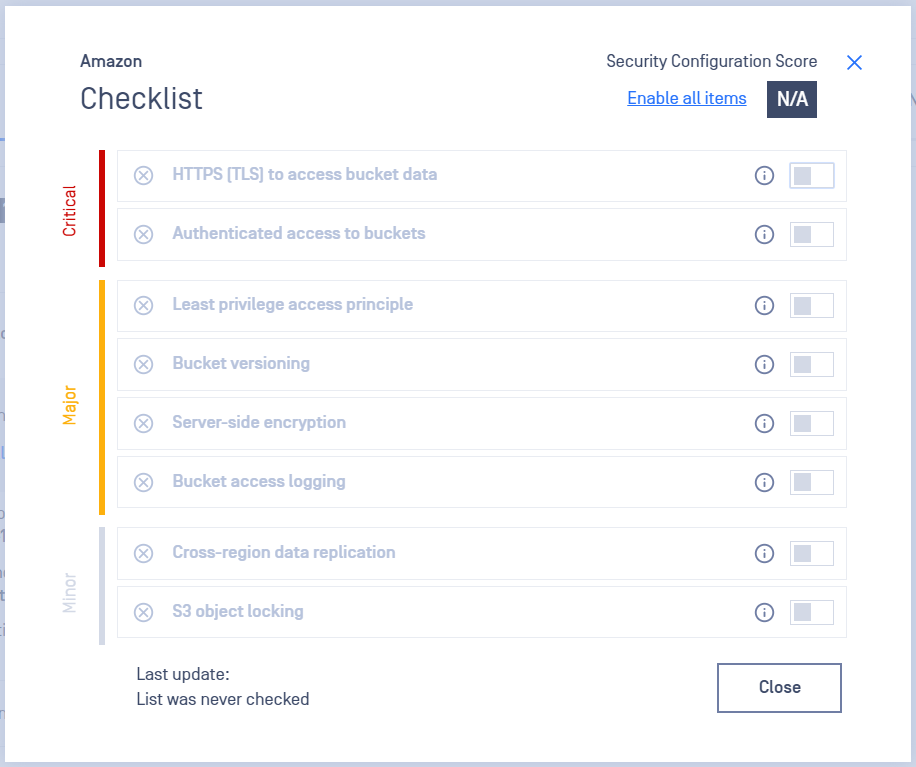
- Enable security checks by switching the toggle
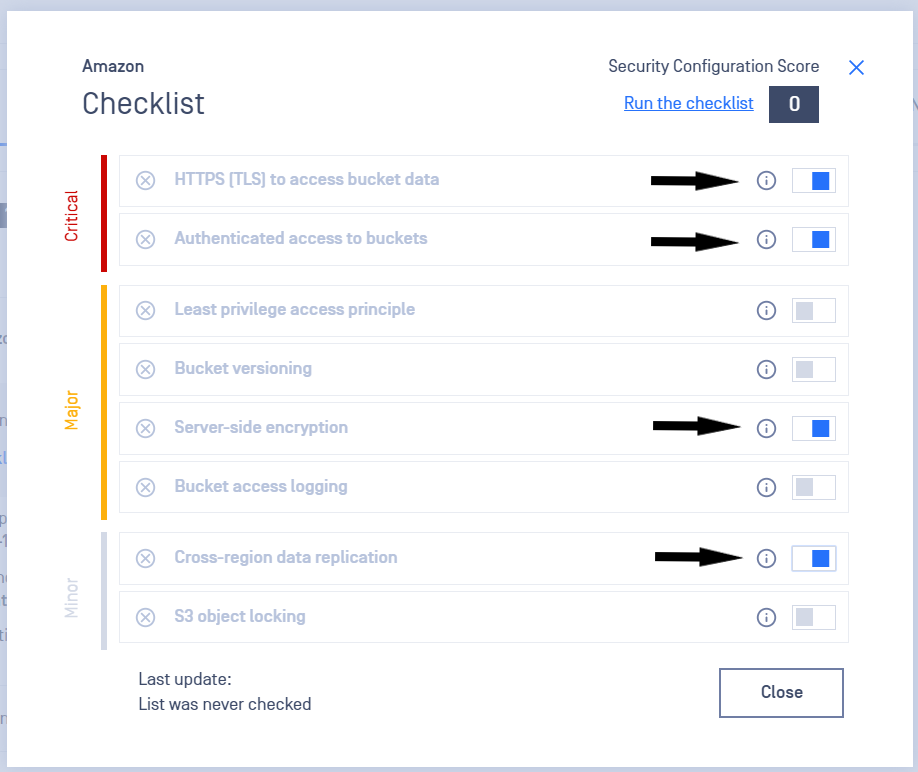
- Click Run the checklist to verify enabled checks
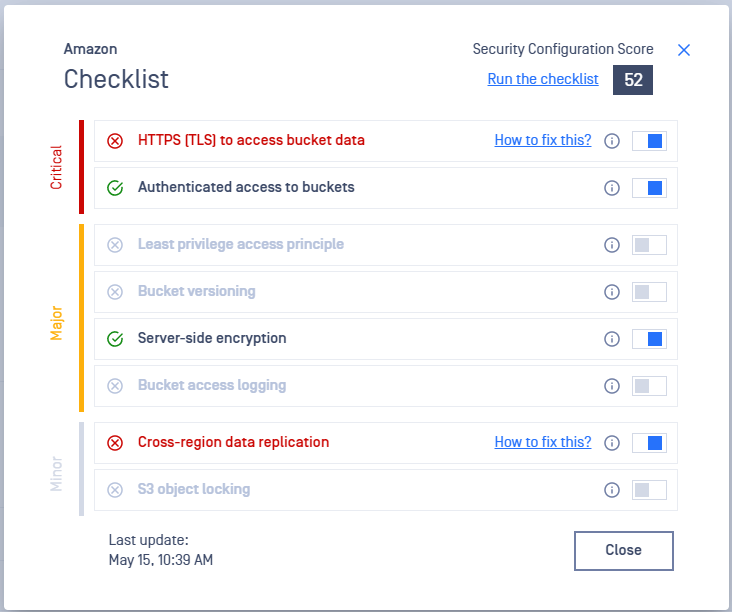
- A process will start that verifies all the enabled items, computes a score and sets a last update time
- Failed items will show in red and a How to fix link will be available
- Passed items will show in dark grey and the score will be updated accordingly
- Review the security checklist status in a glance by checking the storage card
- The security checklist can be disabled from the actions dropdown, by switching the toggle
How is the score computed?
Each type of check is worth a different number of points, such that, when all enabled and resolved, the total would be 100.
| Type of check | Points per item |
|---|---|
| Critical | 15 |
| Major | 12.5 |
| Minor | 10 |
The final score is a combination of the number of enabled and resolved security checks for each type.
| Variable name | Meaning |
|---|---|
| CR | Number of critical items that are resolved |
| MR | Number of major items that are resolved |
| mR | Number of minor items that are resolved |
| CE | Number of critical items that are enabled |
| ME | Number of major items that are enabled |
| mE | Number of minor items that are enabled |
The score is computed as follows: score = (CR * 15 + MR * 12.5 + mR * 10) / (CE * 15 + ME * 12.5 + mE * 10) * 100
We encourage you to verify the security checklist on demand as often as needed.
In order to run the checklist the following AWS policies are needed:
s3:GetBucketPublicAccessBlocks3:GetBucketObjectLockConfigurations3:GetEncryptionConfigurations3:GetBucketLoggings3:ListBuckets3:GetBucketVersionings3:GetBucketAcls3:GetBucketPolicys3:GetReplicationConfiguration
If any policies are missing, some checks might be unsuccessful.