Title
Create new category
Edit page index title
Edit category
Edit link
Network Security
ARP Protection
[Network Security > DoS/DDoS]
This page allows administrators to secure the OT network against ARP spoofing (ARP poisoning) and Man-in-the-Middle (MitM) attacks. By strictly managing how Address Resolution Protocol (ARP) packets are handled, the IFW ensures that malicious devices cannot hijack traffic intended for legitimate PLCs or SCADA servers. It's only supported for Transparent Mode.__
Settings
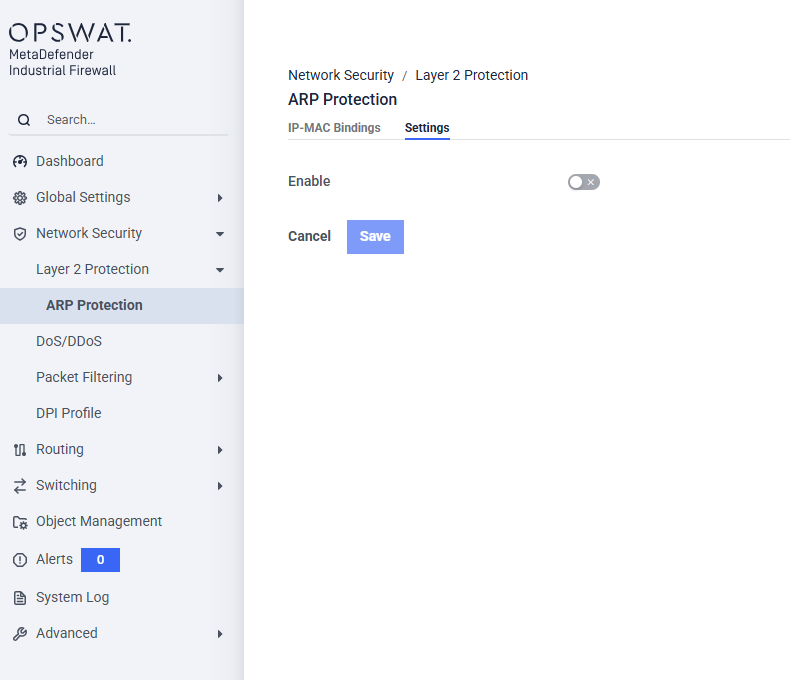
Enable ARP Protection (Toggle): When enabled, the firewall inspects ARP packets passing through its interfaces and validates them against the configured rules
IP-MAC Bindings
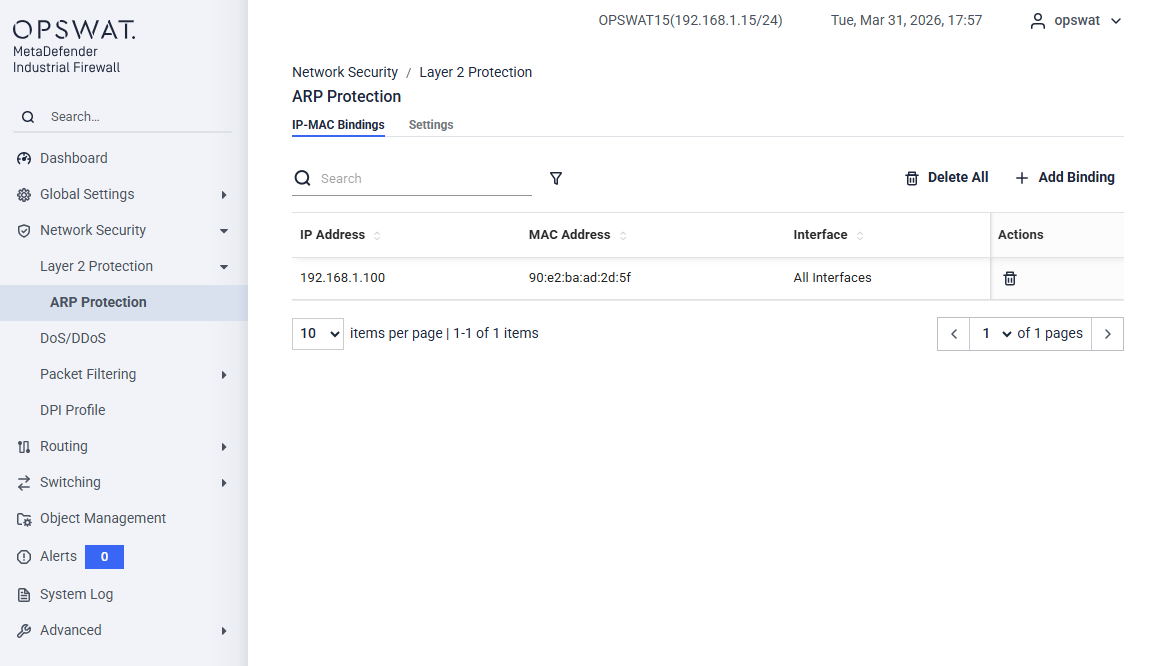
This page allows you to manually configure and manage static relationships between IP addresses and physical MAC addresses. We use these trusted mappings to validate ARP traffic and block ARP spoofing attempts.
Management Controls
- Add Binding: Click this button to create a new static IP-to-MAC address binding.
- Delete All: Delete all rules
- Search...: Enter an IP address, MAC address, or text description into this field to quickly filter and locate specific bindings within the table.
Binding Table
The table displays all configured static ARP bindings with the following details:
- IP Address: The configured IPv4 address of the trusted endpoint on the network.
- MAC Address: The physical hardware address associated with the specified IP address.
- Interface: Specific network interface to which this binding is applied.
- Action: Click the respective icons in this column to delete an individual binding entry.
Dos/DDos
[Network Security > DoS/DDoS]
A DoS/DDoS attack is a type of cyberattack designed to disrupt and render services or devices unusable. In this dialog, you can configure various filters to help protect both the device itself and other network devices from DoS attacks.
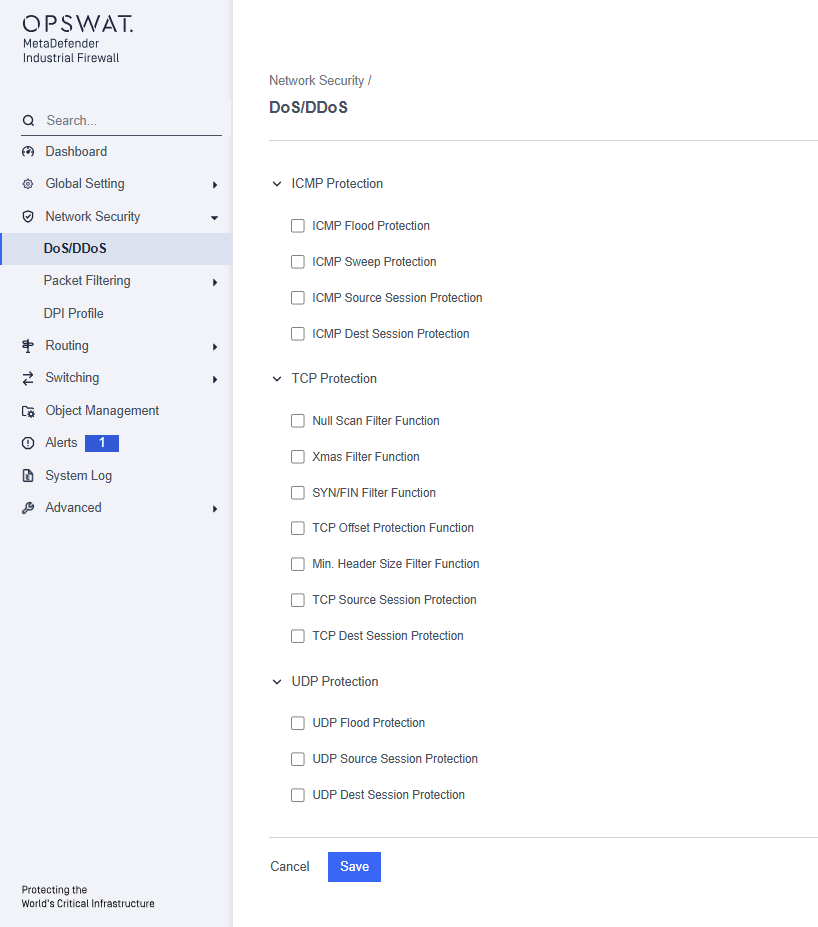
ICMP Protection:
- ICMP Flood Protection: Prevent overwhelming the network with a high volume of ICMP packets.
- ICMP Sweep Protection: Detect and block attempts to map out active devices on a network by sending ICMP requests to multiple IP addresses.
- ICMP Source Session Protection: Limit the number of ICMP requests from a single source
- ICMP Dest Session Protection: Limit the number of ICMP requests directed at a single destination
TCP Protection:
- Null Scan Filter Function: Blocks null scan attacks by filtering packets with no flags set.
- Xmas Filter Function: Prevents Xmas scan attacks by blocking packets with FIN, URG, and PSH flags set.
- SYN/FIN Filter Function: Detects and blocks SYN/FIN scan attacks.
- TCP Offset Protection Function: Ensures TCP packets have valid offsets to prevent manipulation.
- Min. Header Size Filter Function: Blocks packets below the minimum TCP header size to prevent attacks with malformed packets.
- TCP Source Session Protection: Limits the number of concurrent TCP connections from a single source IP address.
- TCP Dest Session Protection: Limits the number of concurrent TCP connections to a single destination IP address.
UDP Protection:
- UDP Flood Protection: Detects and blocks excessive UDP packets sent to a network.
- UDP Source Session Protection: Limits the number of concurrent UDP connections from a single source IP address.
- UDP Dest Session Protection: Limits the number of concurrent UDP connections to a single destination IP address.
Routing Mode
[Network Security > Packet Filtering > Routing Mode]
In this menu, you can configure the settings for the Routing Mode packet filter. This packet filter contains rules that the device sequentially applies to the data stream on its router interfaces. The Routing Mode packet filter performs stateful evaluation of the data stream, selectively filtering out undesired data packets.
When a data packet meets the criteria of one or more rules, the device executes the action specified by the first matching rule and disregards any subsequent rules. If no rules match the data packet, the device applies the default rule, which is set to “Block” by default. You can modify this default rule in the Configuration > Setting > Policy.
Firewall Rules
[Network Security > DoS/DDoS > Routing Mode > Firewall Rules]
This page allows you to create a new firewall rule to control traffic that is being routed between different network interfaces. In Routing Mode, the firewall acts as a gateway or router, making security decisions as traffic passes from one network segment to another. Each interface must have its own IP address.
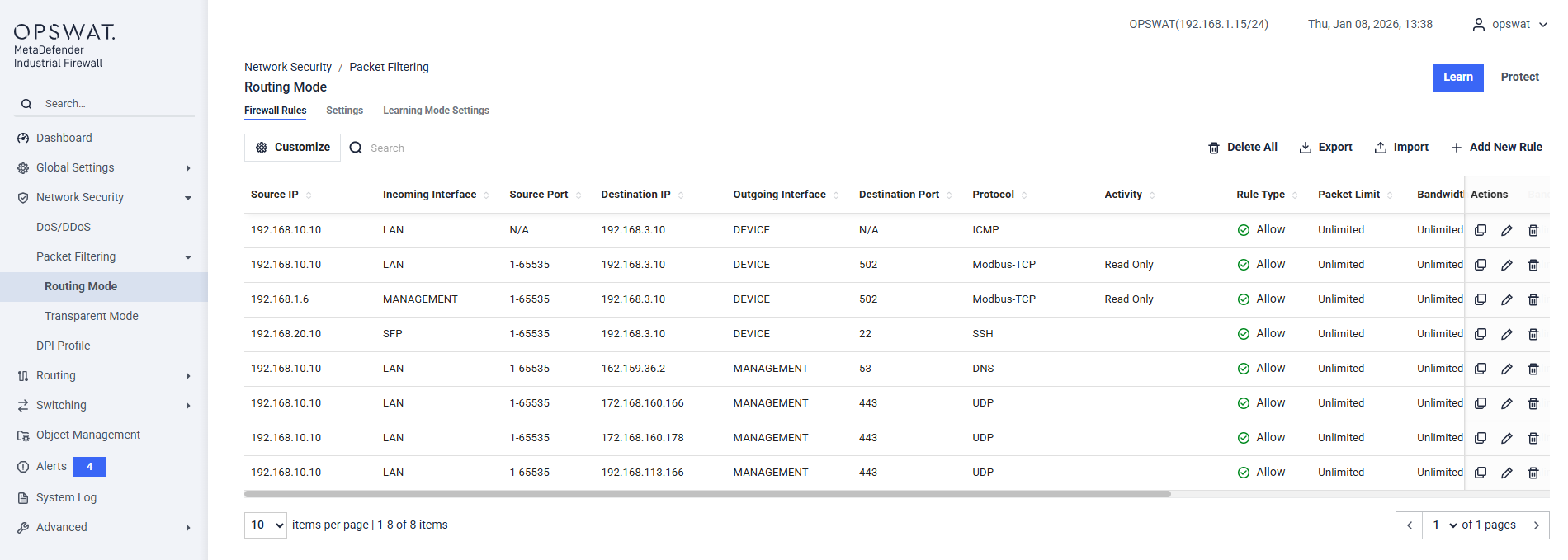
Customize: Opens the column customization panel, where you can select which columns are displayed and adjust their order.
Filter:
- Protocol: Select the protocol to apply filtering rules
- Protected IPs: Specify the IP addresses configured in the Alert settings.
Search: Perform a quick search by IP address, port, or protocol name.
Action:
- Clear All: Remove all existing rules.
- Import: Import the rules from a file.
- Export: Export the current rule to a file.
Add New Rule:
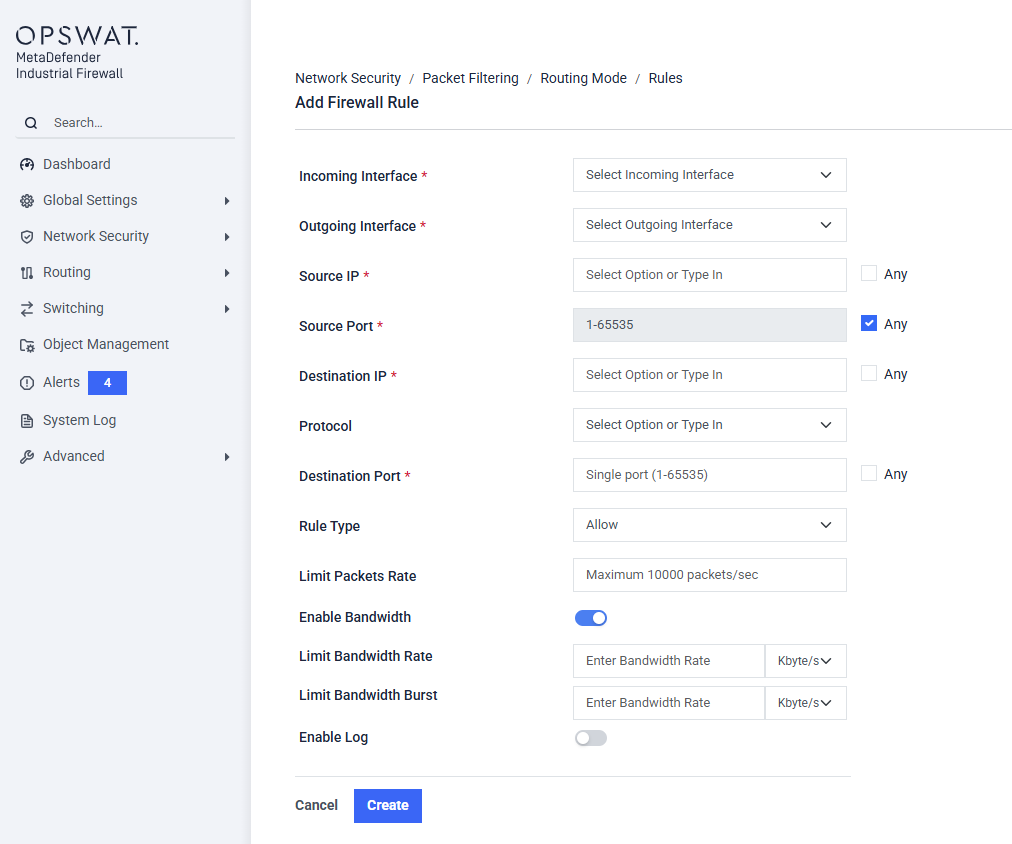
Incoming Interface: Select the interface where the traffic will enter the firewall (e.g.,
DEVICE).Outgoing Interface: Select the interface where the traffic will exit the firewall after being inspected (e.g.,
LAN).Source IP: Specify the IP address of the device initiating the communication.
- Check the Any box to have this rule apply to traffic from any source IP address.
Source Port: Specify the TCP or UDP port number the source device is using.
- Check the Any box to have this rule apply to any source port. This is the most common setting.
Destination IP: Specify the IP address of the device receiving the communication.
- Check the Any box to have this rule apply to traffic going to any destination IP address.
Protocol: Select the network protocol for this rule from the dropdown menu. The available protocols depend on your license.
Rule Type: Choose the action the firewall will take when traffic matches this rule.
- Allow: Permits the traffic to pass.
- Block: Drops the traffic and prevents it from reaching its destination.
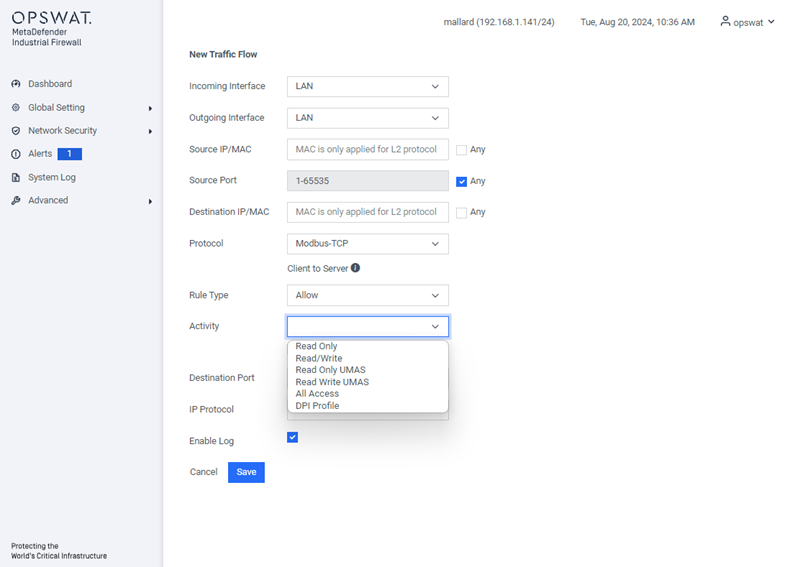
Activity: For supported industrial protocols, you can select a specific activity to control. This allows for granular control based on Deep Packet Inspection (DPI).
Destination Port Specify the TCP or UDP port number the destination device is listening on. This is often determined by the selected protocol (e.g., port 502 for Modbus/TCP).
- Check the Any box to have this rule apply to any destination port.
Concurrent TCP Connections: Enter a number to limit the number of simultaneous TCP connections allowed for this specific traffic flow.
Limit Packets Rate: Enter a number to control the maximum rate of packets per second allowed for this traffic flow. This can help prevent network flooding.
Limit Bandwidth: Check this box to enable and specify a bandwidth limit for this traffic flow.
Enable Log: Check this box to have the firewall create a log entry in the System Log every time this rule is matched.
Settings
[Network Security > Packet Filtering > Routing Mode > Settings]
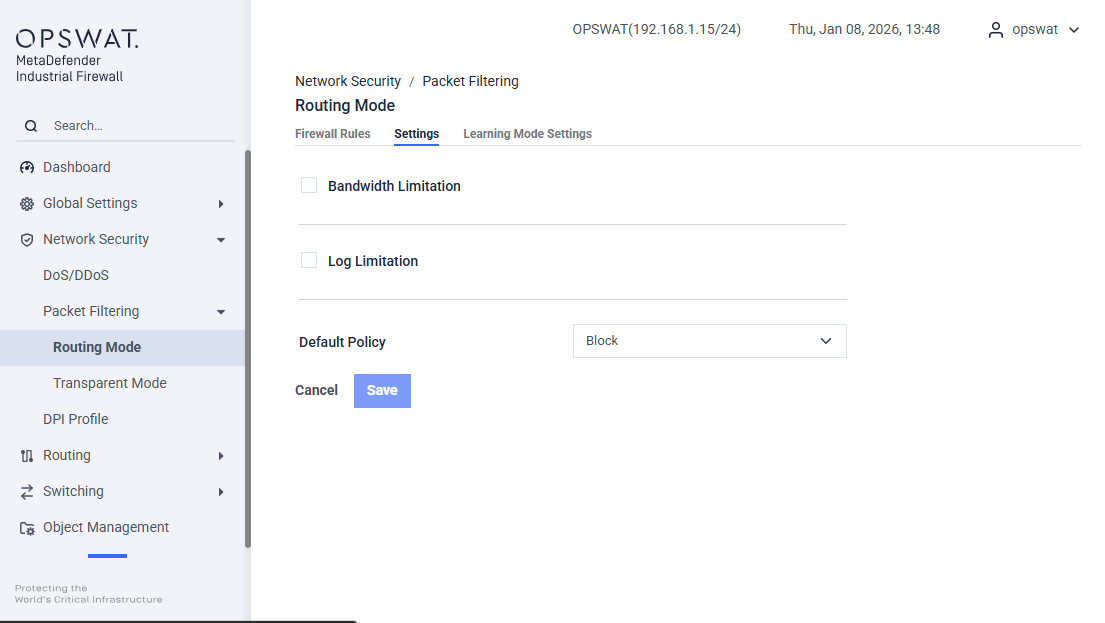
Bandwidth Limitation: Limit the maximum bandwidth in Routing mode.
Log Limitation: Restrict the logging of each firewall rule based on the specified rate limit and burst limit.
Default Policy: The default policy for routing mode is set to “Block.” This can be changed to “Allow” if needed.
Learning Mode Settings
[Network Security > Packet Filtering > Routing Mode > Learning Mode Settings]
The Learning Mode is a powerful feature that uses Deep Packet Inspection (DPI) to analyze the specific actions within industrial protocols. It automatically determines the operational behavior of your network traffic (e.g., distinguishing between "Read" and "Write" commands). This analysis allows the firewall to suggest highly accurate, granular firewall rules, dramatically speeding up the policy creation process.
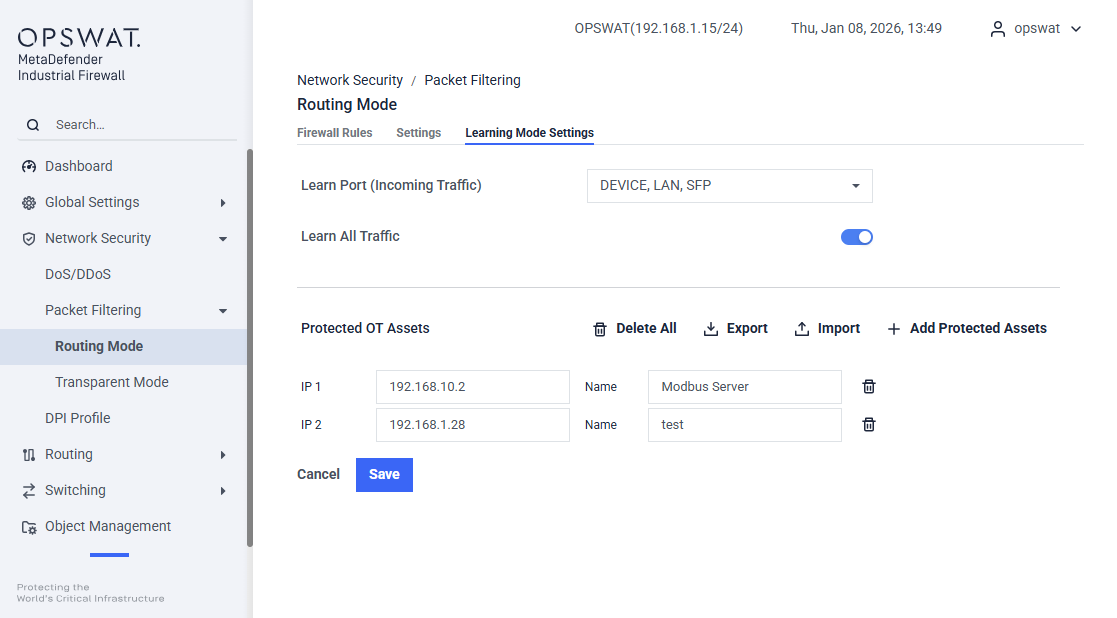
Learn Port (Incoming Traffic): This setting specifies which physical interface(s) the firewall will monitor for traffic. Select the port where the traffic you want to learn is entering the firewall.
Learn All Traffic: Controls the scope of the analysis.
- Enabled: Analyzes all TCP/UDP traffic on the selected Learn Port, including DPI for supported protocols.
- Disabled: Only analyzes traffic destined for the IPs listed in Protected OT Assets.
Protected OT Assets: Define your critical assets here. This list is used for:
- Focused Learning: To analyze traffic for only these specific assets when Learn All Traffic is disabled.
- Alert: To generate specific alerts when traffic to these assets is blocked.
Transparent Mode
This mode is used when configuring the LAN and DEVICE interfaces to operate in Transparent Mode.
Page Layout
- Firewall Rules : Manage traffic control rules
- Settings: Configure general Transparent Mode settings
- Learning Mode Settings: Configure traffic learning behavior
Firewall Rules
[Network Security > Packet Filtering >Transparent Mode > Firewall Rules]
Rule Type Tabs
- Ethernet Rules: Layer‑2 filtering (MAC‑based traffic). Ethernet Rules are used only when the “Block All L2 Protocols” feature is enabled.
- IP Rules: Layer‑3/4 filtering (IP, port, protocol)
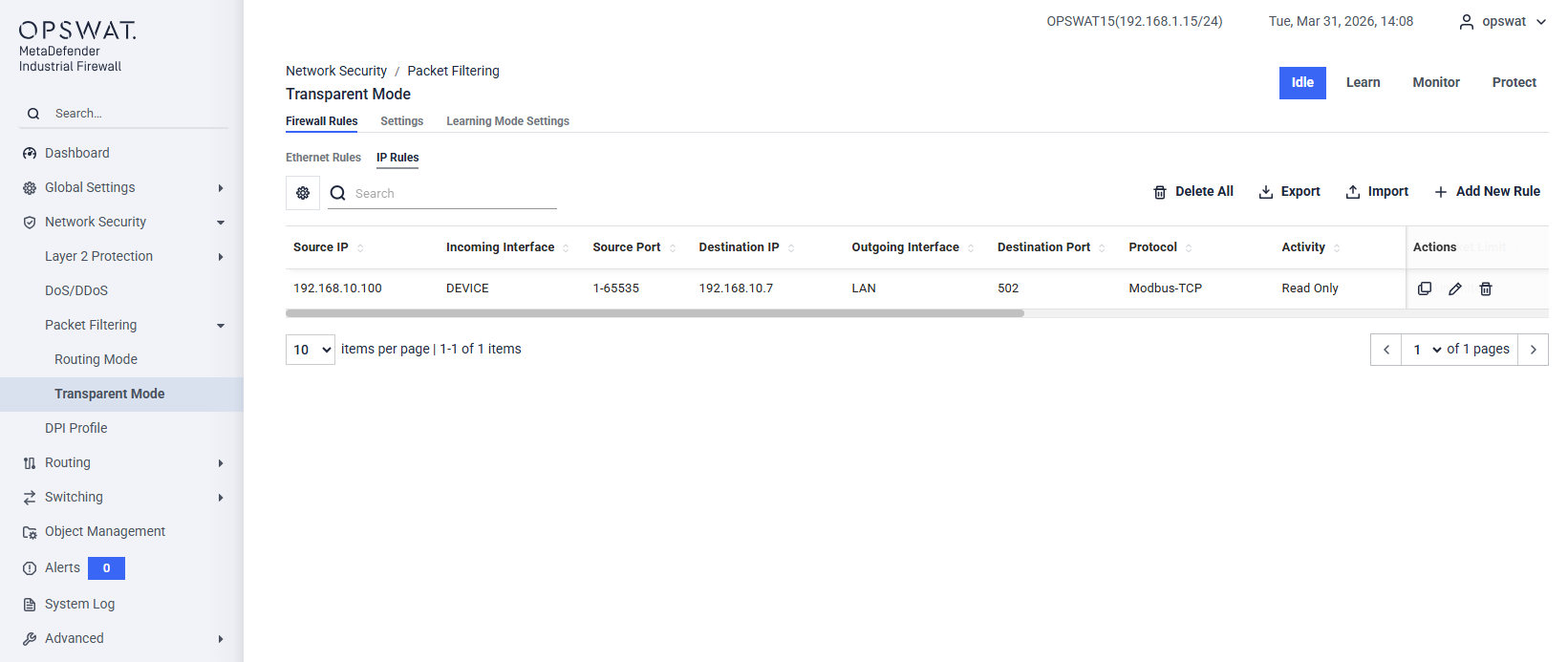
Filter:
- Protocol: Select the protocol to apply filtering rules.
- Protected IPs: Specify the IP addresses configured in the Alert settings.
Search: Perform a quick search by IP address, port, or protocol name.
Action:
- Clear All: Remove all existing rules.
- Import: Import the rules from a file.
- Export: Export the current rule to a file.
IP Rules:
Add New Rule:
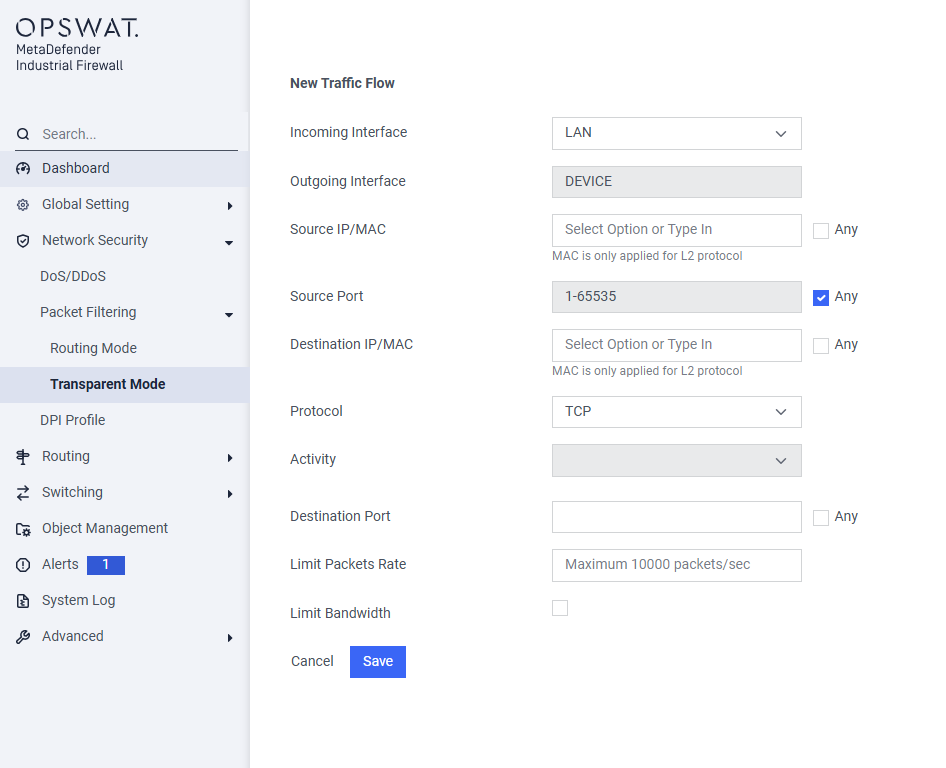
Incoming Interface: Select the interface where the traffic will enter the firewall.
Outgoing Interface: Select the interface where the traffic will exit the firewall after being inspected.
Source IP/MAC: Specify the address of the device initiating the communication.
- For Layer 3 traffic (like TCP/UDP), enter the IP address.
- For Layer 2 protocols (like GOOSE or SV), enter the MAC address.
- Check the Any box to have this rule apply to traffic from any source.
Source Port: Specify the TCP or UDP port number the source device is using.
- Check the Any box to have this rule apply to any source port. This is the most common setting.
Destination IP/MAC: Specify the address of the device receiving the communication.
- For Layer 3 traffic, enter the destination IP address.
- For Layer 2 protocols, enter the destination MAC address.
- Check the Any box to have this rule apply to traffic going to any destination.
Protocol: Select the network protocol for this rule from the dropdown menu (e.g.,
TCP,UDP,Modbus/TCP,GOOSE). The available protocols depend on your license.Activity: For supported industrial protocols, you can select a specific activity to control. This allows for granular control based on Deep Packet Inspection (DPI).
Destination Port: Specify the TCP or UDP port number the destination device is listening on. This is often determined by the selected protocol (e.g., port 502 for Modbus/TCP).
- Check the Any box to have this rule apply to any destination port.
Limit Packets Rate: (Optional) Enter a number to control the maximum rate of packets per second allowed for this traffic flow. This can help prevent network flooding.
Limit Bandwidth: (Optional) Check this box to enable and specify a bandwidth limit for this traffic flow.
Ethernet Rules:
Add New Rule:
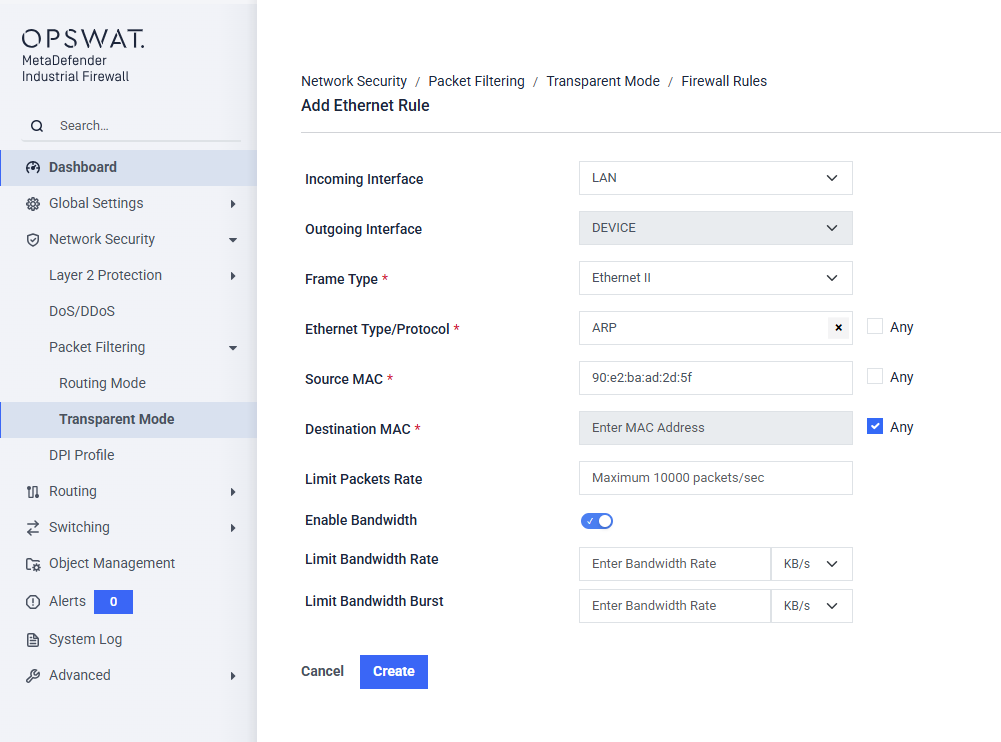
- Incoming Interface: Select the interface where the traffic will enter the firewall.
- Outgoing Interface: Select the interface where the traffic will exit the firewall after being inspected.
- Frame Type: Select the Ethernet frame format. Ethernet II is the most common frame type used in modern networks.
- Ethernet Type/Protocol: Select or type in the Ethernet protocol to match (e.g.,
ARP,GOOSE,SV,EtherCAT). - Source MAC: Enter the MAC address of the source device. Example:
80:e2:ba:ad:2d:5f - Destination MAC: Enter the MAC address of the destination device.
- Limit Packets Rate: (Optional) Enter a number to control the maximum rate of packets per second allowed for this traffic flow. This can help prevent network flooding.
- Limit Bandwidth: (Optional) Check this box to enable and specify a bandwidth limit for this traffic flow.
Settings
[Network Security > Packet Filtering >Transparent Mode > Settings]
This page allows administrators to configure global logging and Layer 2 protocol handling when the firewall is operating as a transparent bridge.__
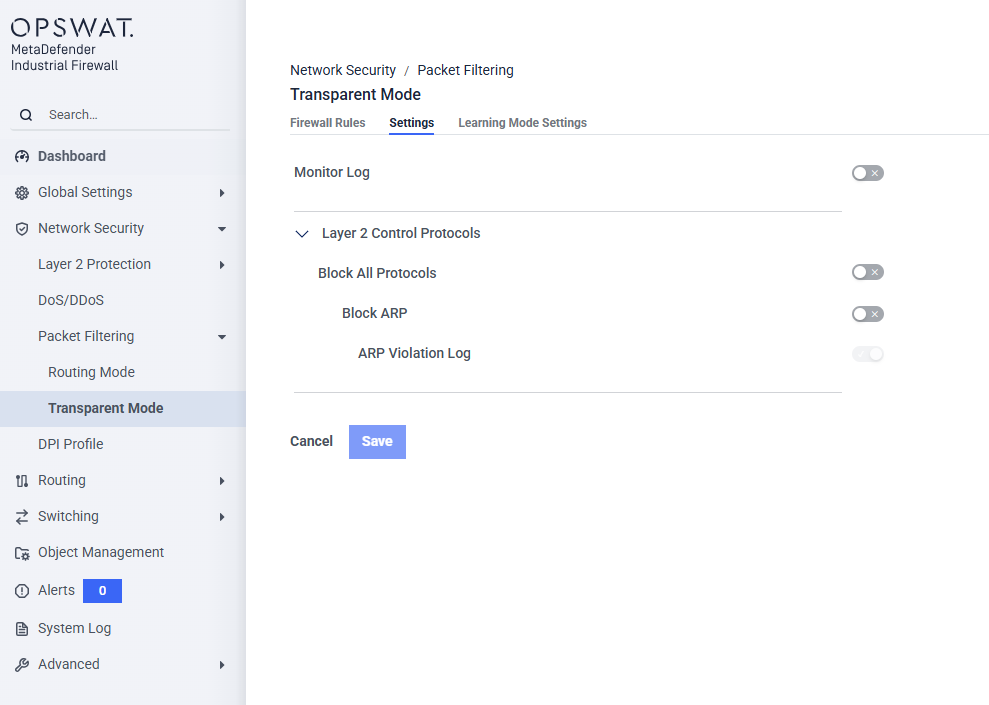
Monitor Log (Toggle): Enable this switch to globally log traffic events that hit the Transparent Mode interface. This is useful for auditing and troubleshooting traffic flows passing through the bridge without necessarily blocking them.
Layer 2 Control Protocols: This collapsible section controls how the firewall handles low-level Ethernet frame traffic (Layer 2)
- ** Block All Protocols (Toggle): Enable this switch to strictly drop all Layer 2 control protocols from traversing the transparent bridge.
- *
- ** Block ARP (Toggle): Enable this switch to specifically block Address Resolution Protocol (ARP) broadcasts across the bridge.
- *
- ARP Violation Log (Toggle): This toggle becomes active only when Block ARP is enabled. Turn this on to generate a system log entry every time an ARP packet is detected and dropped by the firewall.
Enabling Block All Protocols will enforce a highly restrictive baseline for Layer 2 communications. Ensure your network does not rely on these protocols for spanning tree, discovery, or low-level operational status before enabling.
Blocking ARP is a defense mechanism against ARP spoofing/poisoning attacks, but it will disrupt normal local network communication unless we have explicitly ARP rules at Ethernet Rules page.
Learning Mode Settings
[Network Security > Packet Filtering > Transparent Mode > Learning Mode Settings]
In Transparent Mode, Learning Mode analyzes Layer 2 and Layer 3 traffic to automatically generate firewall rules. It discovers general TCP/UDP and Layer 2 (e.g., GOOSE, SV) traffic flows, and for supported industrial protocols, also uses Deep Packet Inspection (DPI) to identify specific activities (e.g., Read vs. Write).__
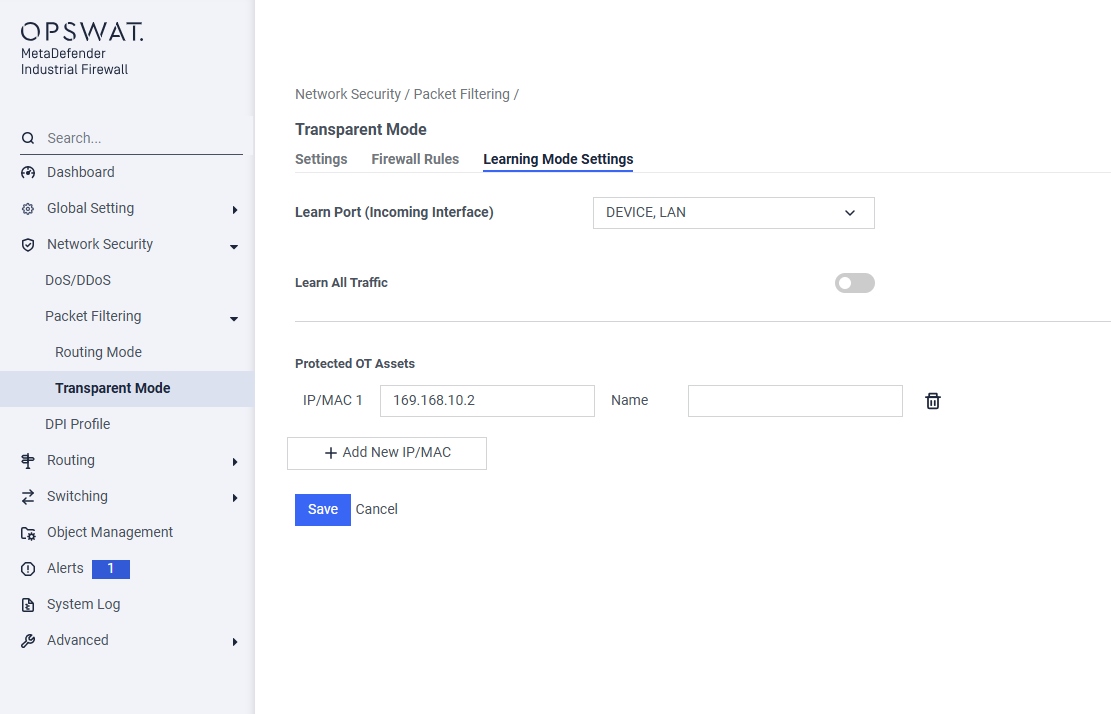
Learn Port (Incoming Traffic): Select the interface(s) (LAN or/and DEVICE) where the firewall will monitor traffic for analysis. In Transparent Mode, learning is only available on these two ports.
Learn All Traffic: Controls the scope of the analysis.
- Enabled: Analyzes all traffic on the selected Learn Port, including TCP/UDP (Layer 3) and MAC-based protocols like GOOSE or SV (Layer 2).
- Disabled: Only analyzes traffic destined for the IP or MAC addresses listed in Protected OT Assets.
Protected OT Assets: Define your critical assets here. This list is used for:
- Focused Learning: To analyze traffic for only these specific assets when Learn All Traffic is disabled.
- Alert: To generate specific alerts when traffic to these assets is blocked.
Configure Modbus Registers
You can configure a new or existing traffic flow to specific MODBUS registers and generate policies that only allow the specific learned registers or register ranges.
For a new traffic flow, click Add New Rule button:
- Protocol: MODBUS
- Activity: Read Only or Read/Write
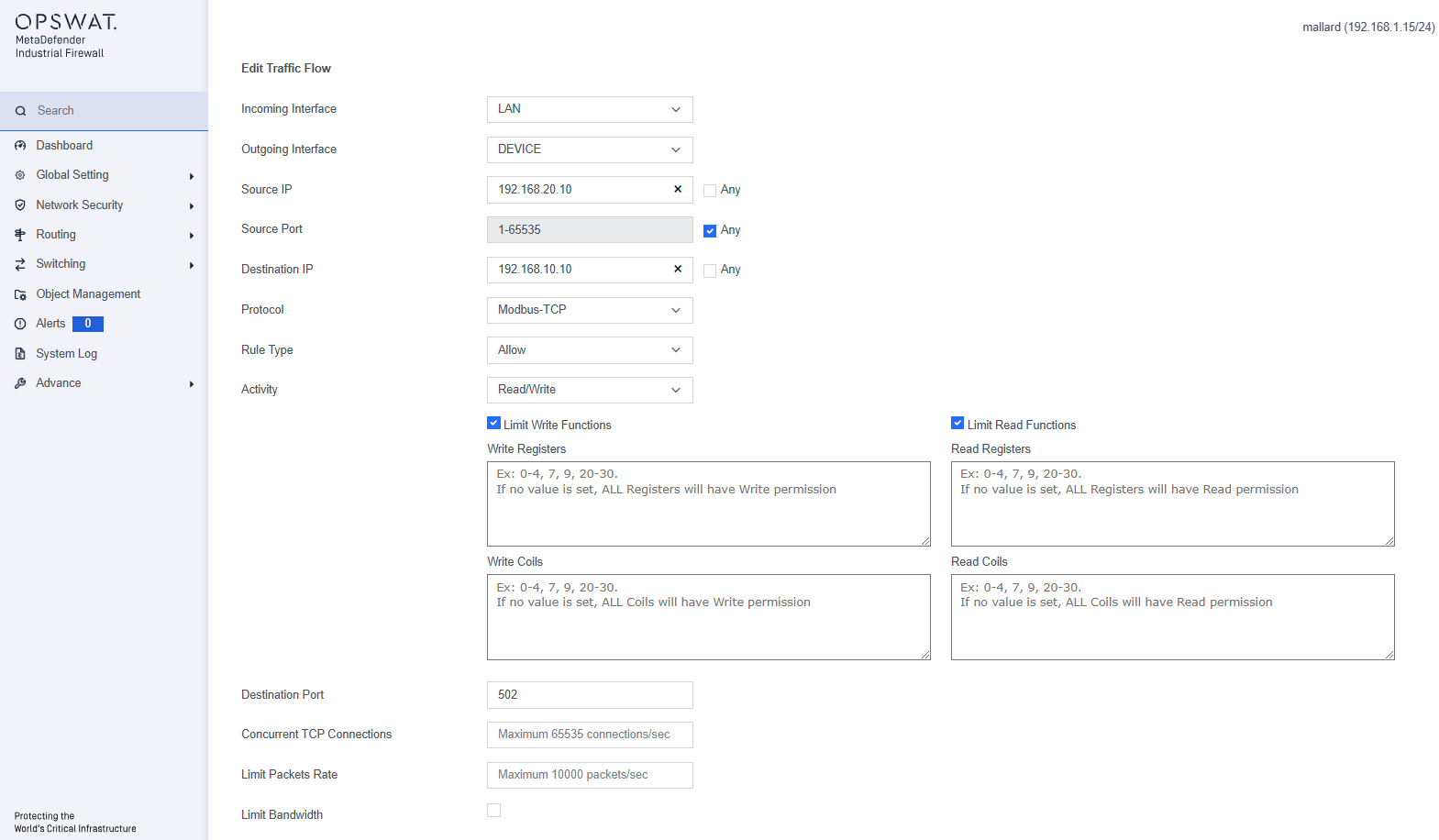
Additional boxes display to configure the MODBUS registers:
- Limit Read Functions Registers: Click to read only specified registers. You must click this box to display the Read Registers box.
- Write Registers: MODBUS registers that the policy will restrict writes to. Specify the registers as a comma-delimited list of individual values or ranges (e.g., 1,2,3,6-10).
- Read Registers: MODBUS registers that the policy will restrict reads to. Specify the registers as a comma-delimited list of individual values or ranges.
DPI Profile
[Network Security > DPI Profile]
The DPI (Deep Packet Inspection) function allows you to monitor and filter data packets, helping to protect your network from undesirable content such as spam or viruses. It inspects data packets for unwanted characteristics and protocol violations by examining both the header and the payload.
In this page, you can create the DPI profile. The device will block any data packets that do not match with the specified profiles.
The menu contains the following protocols:
- BN3500
- DNP3
- EtherNet/IP
- Modbus/TCP
- MQTT
- PROFINET-PTCP
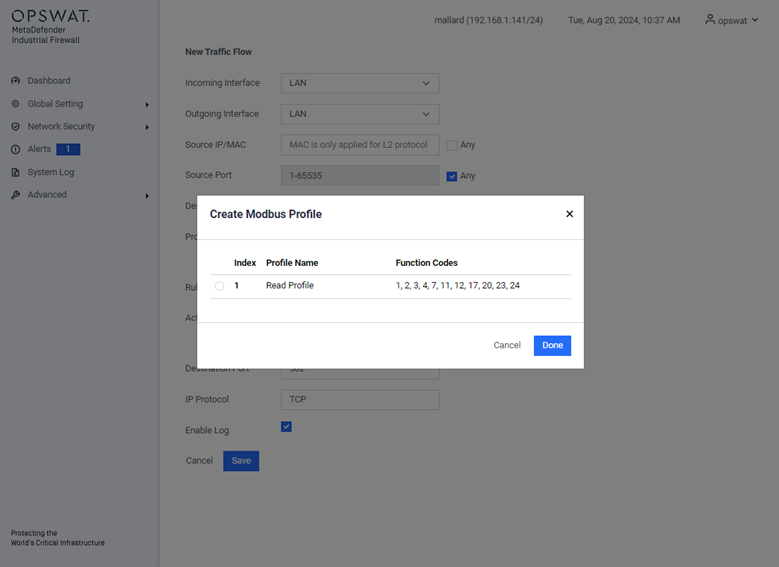
Example Creating Modbus Profile
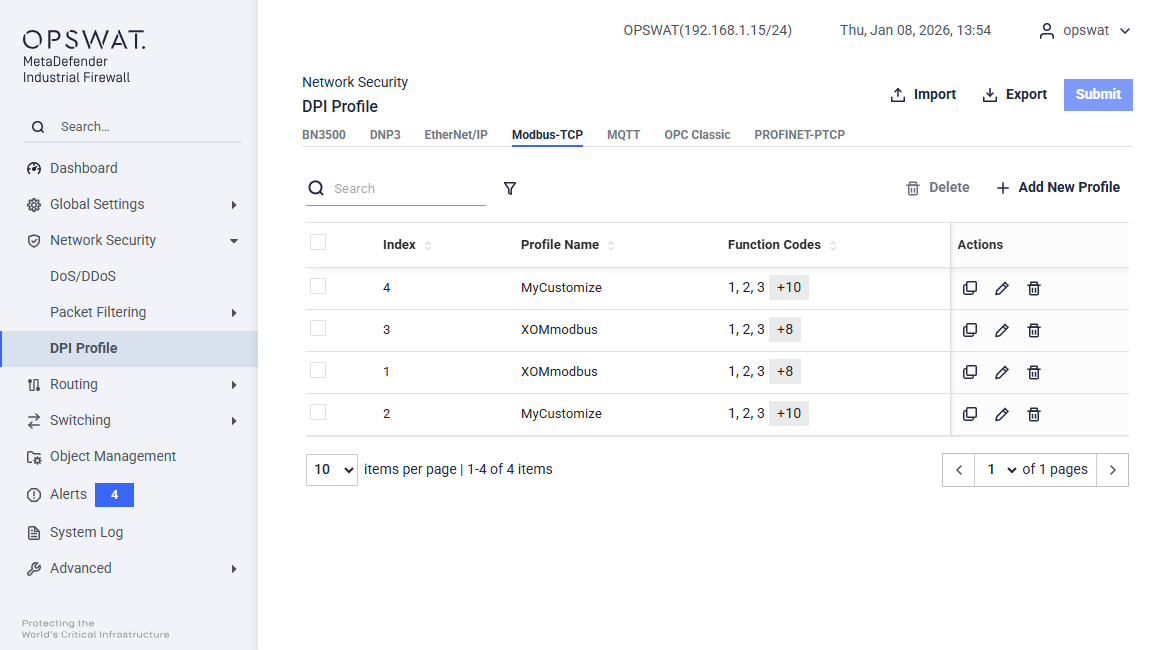
This page allows you to define Modbus TCP-specific profiles. These profiles specify function codes and register or coil addresses. The function codes in the Modbus TCP protocol determine the purpose of the data transfer. The device will block any data packets that violate the specified profiles. If an error is detected, the device can terminate the data connection upon user request. To assist you in defining function codes, predefined function code lists and a function code generator are provided.
- Add New Profile: Create a new profile.
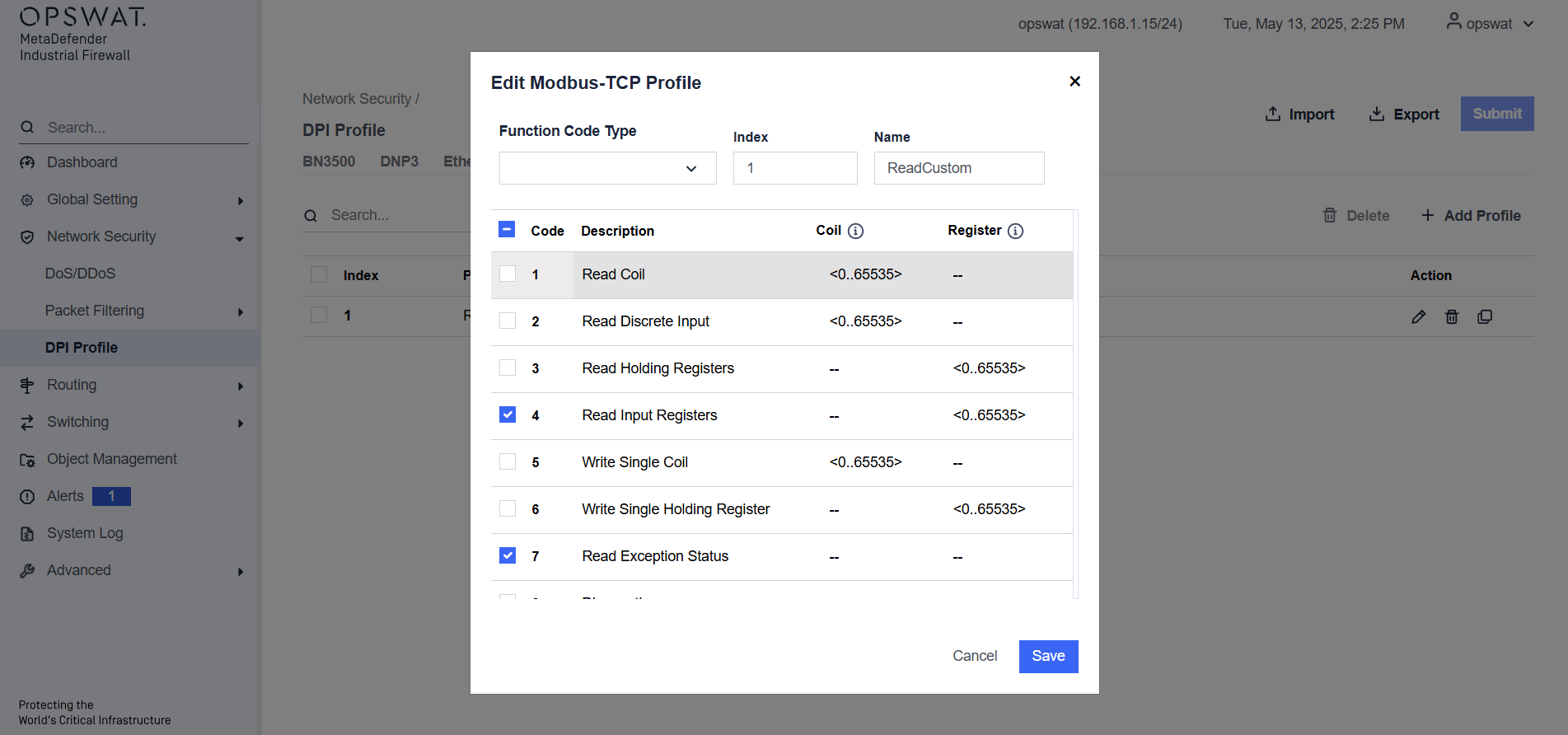
Action:
- Modify the selected profile.
- Remove the profile.
- Duplicate the profile.
Submit: Click this button to save all changes to the profiles.
After creating a profile, it will be available for selection when adding a new rule. You can select the DPI Profile, where the newly created profile will be displayed for use.