Title
Create new category
Edit page index title
Edit category
Edit link
Deploy using Azure VMs
The deployment options vary depending on what are the number of instances where MetaDefender Storage Security will be installed.
Options:
- Single Instance deployment of MetaDefender Core and MetaDefender Storage Security
- Multi-Instance with Autoscaling for MetaDefender Core and single instance of MetaDefender Storage Security.
OPSWAT provides a terraform project to deploy MetaDefender Storage Security and MetaDefender Core in different instances using Azure services.
MetaDefender Storage Security running in VMs only supports single instance as the 3rd party tools cannot be all exported with Azure services. However, in case of using VMs separately for these 3rd party tools then MDSS can be replicated multiple times.
Prerequisites and Requirements
Azure knowledge: This guide assumes familiarity with Azure Services
Azure account: needs permission to create Azure Services listed in Recommended Architecture for Azure
Tools installation: Terraform
Single Instance Deployment
For a single deployment of MetaDefender Core in Azure you can use this example to test this deployment type, besides the MetaDefender VM instance, additional resources are being generated and set up.
Deploy using Terraform
OPSWAT provides a terraform project to create the infrastructure needed to deploy the Architecture Examples in CSPs
- Locally clone the metadefender-csp repository and go to Azure/single-vm-deployment
xxxxxxxxxxgit clone git@github.com:OPSWAT/metadefender-csp.gitcd Azure/single-vm-deploymentModify terraform.tfvars with the desired options
- LICENSE__KEY_CORE_ required if wanted to have the MetaDefender Core instance activated automatically
- APIKEY_GENERATION=true to have the apikey generated by terraform
- There is one general section and one section for each product that is supported using this Terraform project
xxxxxxxxxx# General variables RG_NAME = "metadefender" # Prefix to add to all the resourcesMD_REGION = "eastus" # Region for all the resourcesMD_VNET_CIDR = "192.168.0.0/16" # VPC CIDR where to create the MetaDefender productsPUBLIC_ENVIRONMENT = trueAPIKEY_GENERATION = trueIMPORT_RG = falseVM_PWD = "<SET_UP_VM_PWD>" # MetaDefender Core variables DEPLOY_CORE = trueCORE_INSTANCE_TYPE = "Standard_D8s_v5" # Instance type for MetaDefender CoreLICENSE_KEY_CORE = ""OFFER_PRODUCT_CORE = "opswat-mdcore-linux" # Windows opswat-mdcore-windowsSKU_CORE = "opswat-mdcore-linux" # Windows opswat-mdcore-windows # MetaDefender Storage Security variables DEPLOY_MDSS = true # true to deploy MetaDefender Storage Security together with CoreMDSS_INSTANCE_TYPE = "Standard_D8s_v5" # Instance type for MetaDefender Storage SecurityOFFER_PRODUCT_MDSS = "opswat-mdss-ubuntu"SKU_MDSS = "opswatmdssubuntu"DEPLOY_MDSS_COSMOSDB = false- Run terraform init and apply. Check the resource to be created, after that enter "y"
xxxxxxxxxxterraform initterraform applyDeploy using Azure portal
For having MetaDefender Core in a Single Azure VM as showed in Single Azure VM Architecture it is needed to follow the next steps
1. Create Resource Group
- Go to you Azure account and create a new resource group (we will refer to it as "metadefender-rg")
2. Create Azure VM
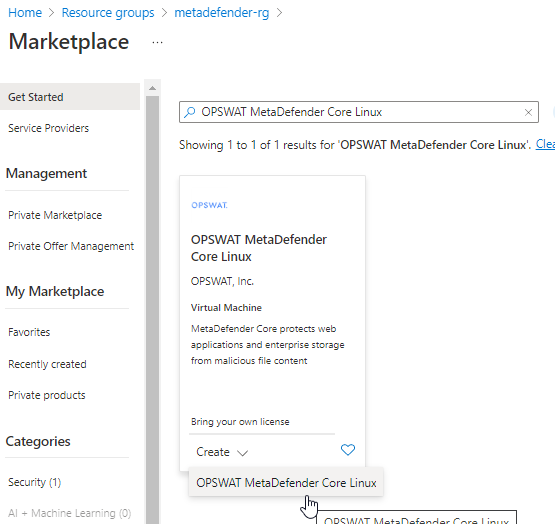
- Inside the resource group click on create resource and search for "OPSWAT MetaDefender Core Linux"
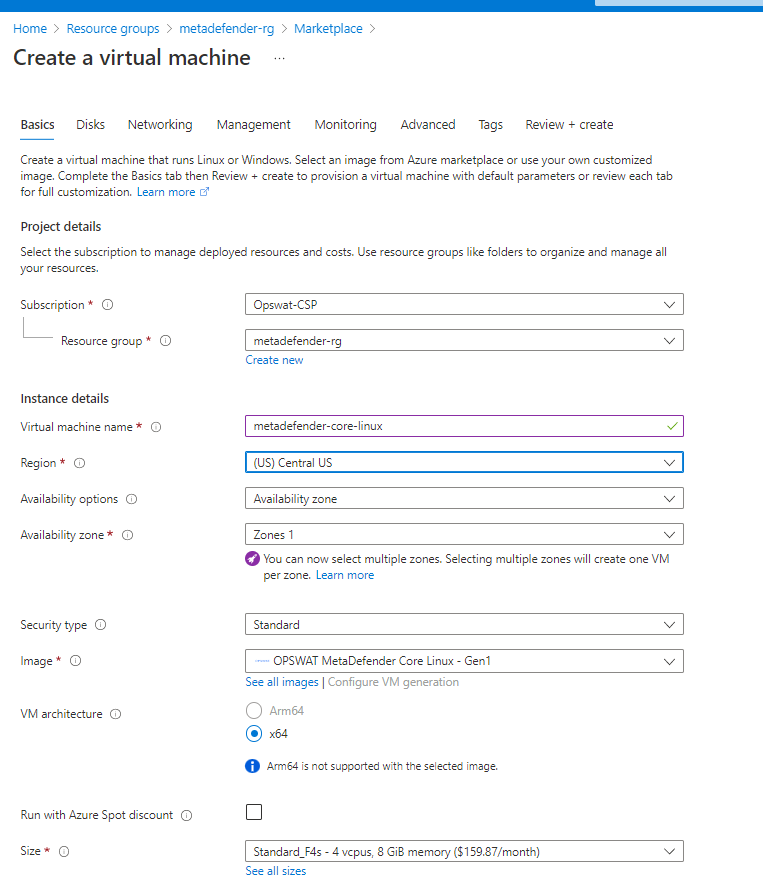
- Input the vm name and select the size based on General System Requirements
- Under Administrator Account section select the desired way to access to the VM. For this guideline we will generate a public key to access to it
3. Storage Configuration
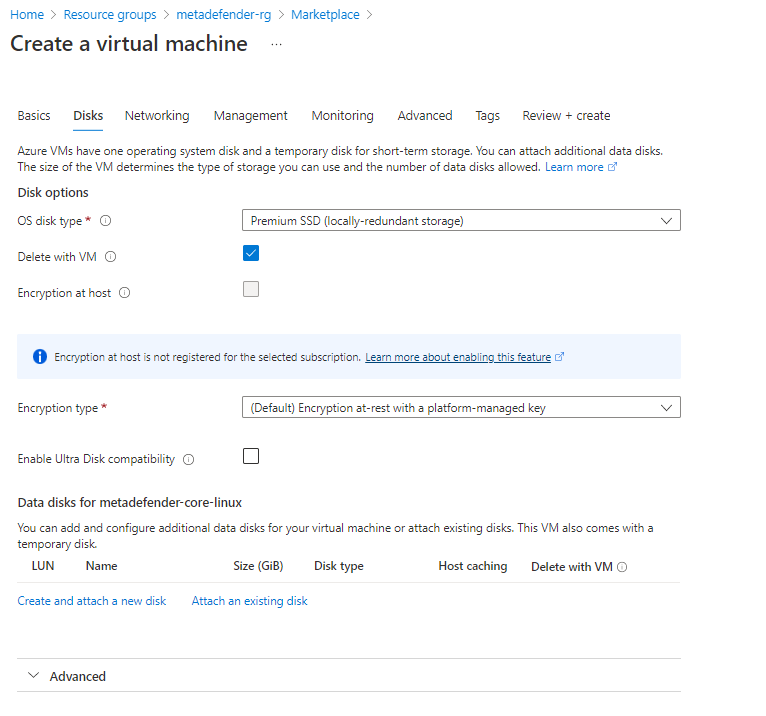
Storage step can be skipped.
In general there's no need for additional storage by MetaDefender. However, there are 2 situations where additional local storage might be required:
- MetaDefender will process large files or a high volume of files which submitted in MetaDefender's queue will need over 10GB files storage
- MetaDefender is configured to store files in the Quarantine section which will eventually fill the entire root volume.
In case quarantining the files in the MetaDefender instance or analyzing high volumes of files is a requirement, please consider adding an additional Azure Managed Disk
- Premium SSD is recommended for having the best performance
4. Network Configuration
- Change public IP to None in case you do not want to access from internet.
- Select the Virtual network and Subnet in case you already have them created, if not leave it to create them
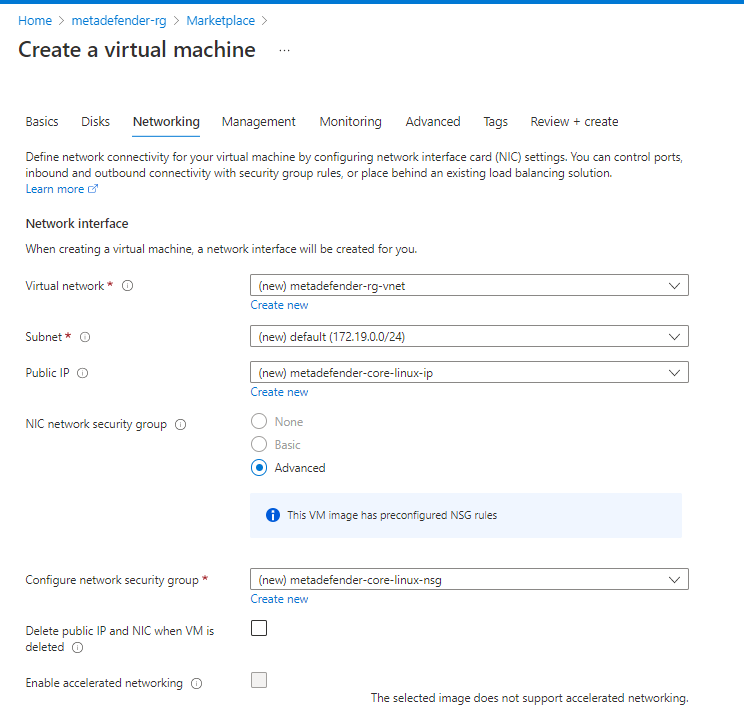
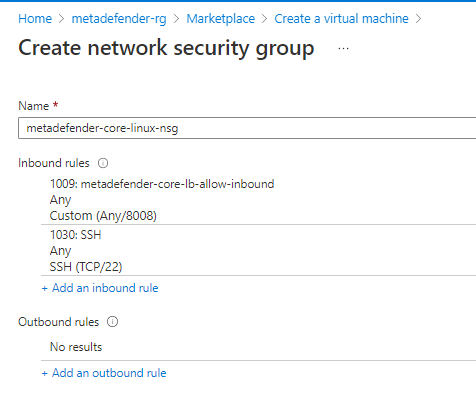
- Create Security Group adding rules for 8008 and SSH
- Under Load Balancing section as it is a single vm it is not really needed but it can be used to set up a health check using the /readyz endpoint
5. Review & Create the VM
- Under Management, Monitoring, Advanced and Tags there are not any configuration different from the default ones that are needed to be selected. So customize it as it is needed for each use case.
- After creating it will show you a window to download the private key to access to the VM in case that option was selected for accessing
##